Enabling IoT devices to function securely behind firewalls is a growing challenge for organizations worldwide. As the Internet of Things continues to expand, ensuring both secure and efficient access to devices within firewalled networks is vital for maintaining robust security and functionality. In this article, we’ll delve into the best practices, tools, and advanced techniques for achieving seamless connectivity without compromising security.
In today’s interconnected world, IoT devices are increasingly prevalent across industries, ranging from smart homes to industrial automation. Managing their access behind firewalls is no longer optional but essential. Organizations must balance accessibility with security to ensure these devices operate optimally while remaining protected from potential cyber threats. This guide aims to provide an in-depth exploration of the challenges and solutions involved in securely accessing IoT devices behind firewalls.
This article is designed to offer a detailed roadmap for accessing IoT devices behind firewalls. From foundational principles to advanced configurations, readers will gain a comprehensive understanding of the subject. Let’s explore further.
Read also:Honeytoon Teach Me First Free Your Ultimate Guide To Learning Korean With Fun And Interactive Comics
Contents Overview
- Understanding IoT and Firewalls
- Key Challenges in Accessing IoT Devices Behind Firewalls
- Strategies for Secure IoT Device Access
- Prioritizing Security Considerations
- Essential Tools for Managing IoT Devices
- Adopting Best Practices for IoT Connectivity
- Designing Networks for IoT Devices
- Emerging Trends in IoT and Firewall Management
- Case Study: Successful Implementation
- Final Thoughts
Understanding IoT and Firewalls
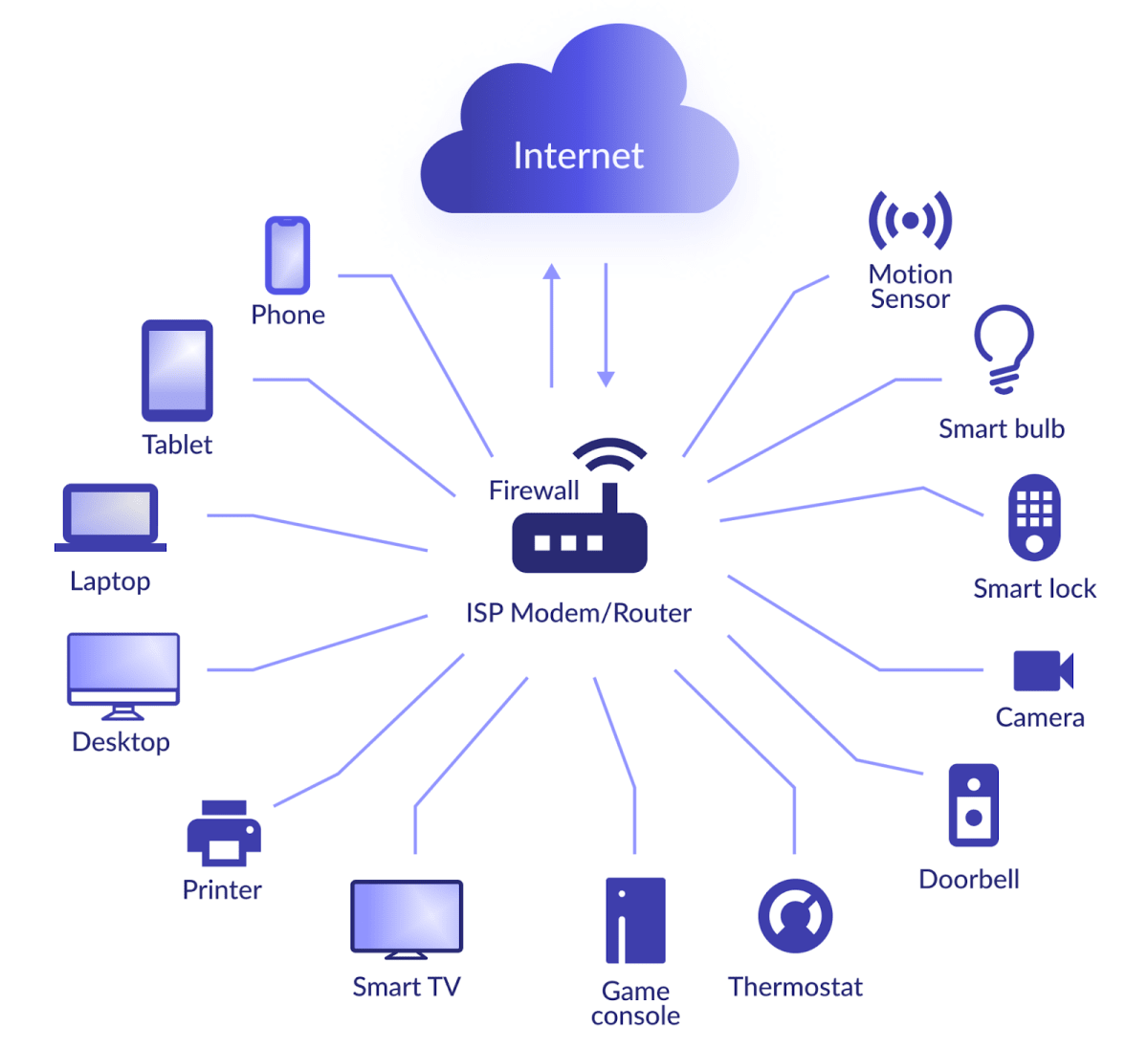
The Internet of Things has transformed how devices interact with each other and the internet, creating a connected ecosystem that drives innovation. However, as IoT devices become integral to corporate networks, the importance of robust security measures cannot be overstated. Firewalls play a pivotal role in safeguarding these networks from unauthorized access and potential cyber threats.
Accessing IoT devices behind firewalls requires meticulous planning and execution. Firewalls are engineered to block unauthorized traffic, which can inadvertently restrict access to IoT devices. This article will examine the intricacies of this challenge and provide actionable solutions to address it effectively.
Understanding the dynamic relationship between IoT devices and firewalls is the cornerstone of ensuring secure and reliable connectivity. By exploring how firewalls function and their interaction with IoT devices, organizations can implement strategies that enhance both security and functionality.
Key Challenges in Accessing IoT Devices Behind Firewalls
One of the primary obstacles in accessing IoT devices behind firewalls is balancing security with accessibility. Firewalls are designed to block traffic that doesn’t meet predefined criteria, which can sometimes hinder the communication between IoT devices and external systems.
Additional challenges include:
- Complex Network Configurations: Many organizations operate with intricate network setups that complicate firewall configurations for IoT devices.
- Device Compatibility Issues: Not all IoT devices are compatible with advanced firewall settings, leading to potential connectivity hurdles.
- Security Risks: Creating exceptions in firewalls or opening ports can expose networks to vulnerabilities, making security a critical concern.
Tackling these challenges demands a blend of technical expertise, strategic planning, and the integration of appropriate tools and technologies.
Read also:Jeff Carriveau
Strategies for Secure IoT Device Access
Port Forwarding
Port forwarding is a widely adopted technique for accessing IoT devices behind firewalls. This method involves directing incoming traffic from a specific port on the firewall to a designated device on the internal network, enabling secure communication.
When utilizing port forwarding, consider the following:
- Select port numbers that are less likely to be targeted by attackers to reduce security risks.
- Configure the firewall to permit only essential traffic through the specified port, enhancing security.
- Regularly monitor and update port forwarding rules to ensure ongoing protection against evolving threats.
Reverse Proxy
A reverse proxy acts as a mediator between external clients and internal IoT devices, offering a layer of security by masking the actual IP addresses of the devices. This approach mitigates potential security risks and enhances network efficiency.
Advantages of employing a reverse proxy include:
- Enhanced security through abstraction of device IP addresses, reducing the risk of unauthorized access.
- Improved load balancing and performance optimization, ensuring smooth operations.
- Centralized management of access control and authentication, simplifying network administration.
Leveraging Virtual Private Networks (VPNs)
A Virtual Private Network (VPN) establishes a secure tunnel between external clients and internal networks, enabling encrypted communication with IoT devices behind firewalls. This method offers robust protection against potential cyber threats.
Benefits of using a VPN include:
- Strong encryption protocols that safeguard sensitive data during transmission.
- Scalability for accommodating multiple users and devices, ensuring flexibility.
- Reduced risk of unauthorized access through public networks, enhancing overall security.
Prioritizing Security Considerations
When accessing IoT devices behind firewalls, security must remain a top priority. Implementing comprehensive security measures is essential to protect sensitive information and prevent potential breaches.
Some critical security considerations include:
- Implementing robust authentication mechanisms, such as multi-factor authentication (MFA), to verify user identities.
- Regularly updating firmware and software for both IoT devices and firewalls to address vulnerabilities and enhance performance.
- Monitoring network activity continuously to detect any signs of unauthorized access or suspicious behavior.
By adhering to these security best practices, organizations can ensure that their IoT devices remain secure while maintaining accessibility when necessary.
Essential Tools for Managing IoT Devices
Various tools are available to facilitate the effective management of IoT devices behind firewalls. These tools simplify configuration, enhance security, and improve overall network management.
Some notable tools include:
- Firewall Management Software: Solutions like pfSense and Cisco ASA offer advanced features for configuring and managing firewalls, ensuring optimal performance.
- IoT Device Management Platforms: Platforms such as AWS IoT and Microsoft Azure IoT Hub provide comprehensive solutions for securely managing IoT devices at scale.
- Network Monitoring Tools: Tools like Nagios and Zabbix help monitor network activity and detect potential security threats in real-time.
Selecting the appropriate tools depends on the specific needs and requirements of the organization. It’s crucial to evaluate each tool’s features and capabilities before making an informed decision.
Adopting Best Practices for IoT Connectivity
Implementing best practices is essential for ensuring secure and efficient access to IoT devices behind firewalls. These practices help minimize risks and optimize device performance.
- Regular Audits: Conduct periodic audits of firewall configurations and IoT device settings to identify and address potential vulnerabilities.
- Network Segmentation: Use network segmentation to isolate IoT devices from other parts of the network, reducing the risk of unauthorized access.
- Documentation: Maintain detailed documentation of all configurations and changes to facilitate troubleshooting and ensure continuity.
By following these best practices, organizations can enhance the security and efficiency of their IoT device management processes.
Designing Networks for IoT Devices
Creating a network that effectively accommodates IoT devices behind firewalls requires careful consideration of various factors. A well-designed network can enhance security, improve performance, and simplify management.
Key elements of a secure network design include:
- Strategic Firewall Placement: Position firewalls in locations that maximize protection for sensitive areas of the network.
- Device Grouping: Group similar IoT devices together to streamline configuration and management processes.
- Access Control Lists (ACLs): Implement ACLs to restrict access to specific devices and services, enhancing security and control.
By incorporating these elements into network design, organizations can create a secure and efficient environment for their IoT devices.
Emerging Trends in IoT and Firewall Management
The landscape of IoT and firewall management continues to evolve, driven by advancements in technology and changing security requirements. Some emerging trends include:
- AI-Powered Security: Artificial intelligence and machine learning are being leveraged to enhance threat detection and response capabilities, providing proactive protection.
- Zero Trust Architecture: This security model assumes that no device or user can be trusted by default, requiring strict verification for all access attempts to minimize risks.
- 5G Connectivity: The advent of 5G networks is set to revolutionize IoT device communication, enabling faster, more reliable connections that support advanced applications.
Staying informed about these trends is crucial for organizations aiming to remain competitive in the rapidly evolving field of IoT and firewall management.
Case Study: Successful Implementation
A leading manufacturing company encountered challenges in accessing IoT devices behind firewalls in their production facilities. By integrating port forwarding, reverse proxy, and VPN technologies, they achieved secure and reliable connectivity, overcoming the obstacles they faced.
Key insights from this case study include:
- Adopting a multi-layered approach to address different aspects of the challenge, ensuring comprehensive solutions.
- Regularly reviewing and updating configurations to adapt to evolving requirements, maintaining optimal performance.
- Engaging with industry experts to ensure effective implementation, leveraging specialized knowledge and experience.
This real-world example highlights the effectiveness of combining multiple strategies to overcome the complexities of accessing IoT devices behind firewalls.
Final Thoughts
Accessing IoT devices behind firewalls is a complex but achievable task when approached with the right strategies and tools. By understanding the challenges, implementing best practices, and utilizing available technologies, organizations can ensure secure and efficient connectivity for their IoT devices.
We encourage readers to explore the methods and tools discussed in this article and apply them to their specific scenarios. Feel free to share your thoughts, ask questions, or provide feedback in the comments section below. Additionally, don’t hesitate to share this article with others who may find it valuable. For more insights into IoT and network security, explore our other resources available on the site.