In today's increasingly interconnected world, AWS IoT remote access has emerged as a transformative solution for businesses aiming to manage devices and data seamlessly. This technology empowers users to connect, monitor, and control IoT devices from anywhere globally, ensuring smooth operations and delivering real-time insights. In this article, we will delve into the concept of AWS IoT remote access, exploring its benefits, implementation strategies, and much more.
AWS IoT remote access is more than just a buzzword in the tech industry; it signifies a significant shift in how organizations engage with their IoT ecosystems. By harnessing the capabilities of cloud computing and advanced networking protocols, AWS enables businesses to establish secure and scalable connections to their devices remotely. This capability is essential for industries ranging from manufacturing to healthcare, where real-time data access can be a game-changer.
In the subsequent sections, we will examine the various dimensions of AWS IoT remote access, including its architecture, security measures, and practical applications. Whether you're a developer, a business leader, or someone curious about IoT technologies, this guide will equip you with the knowledge to fully leverage the potential of AWS IoT remote access.
Read also:Nikki Catsouras Photos Body A Comprehensive Examination Of The Controversy Facts And Impact
Table of Contents
- Exploring AWS IoT Remote Access
- Understanding the Architecture
- Ensuring Robust Security
- Key Benefits
- Implementation Process
- Real-World Applications
- Addressing Challenges
- Optimizing System Performance
- Future Trends
- Conclusion and Next Steps
Exploring AWS IoT Remote Access
AWS IoT remote access is a service designed to allow users to connect and manage IoT devices remotely via the cloud. This technology empowers businesses to interact with their devices globally, ensuring seamless operations and real-time data access. Built on the robust infrastructure of AWS, the service offers scalability, reliability, and security.
How It Works
The process begins by connecting devices to the AWS IoT Core, which serves as a central hub for communication. Through this hub, users can issue commands, receive data, and perform updates from remote locations. The service supports a wide array of protocols, including MQTT, HTTP, and WebSockets, ensuring compatibility with various devices and applications.
Key Features
- Secure communication between devices
- Scalable infrastructure for growing needs
- Real-time data streaming for instant insights
- Comprehensive device fleet management
Understanding the Architecture
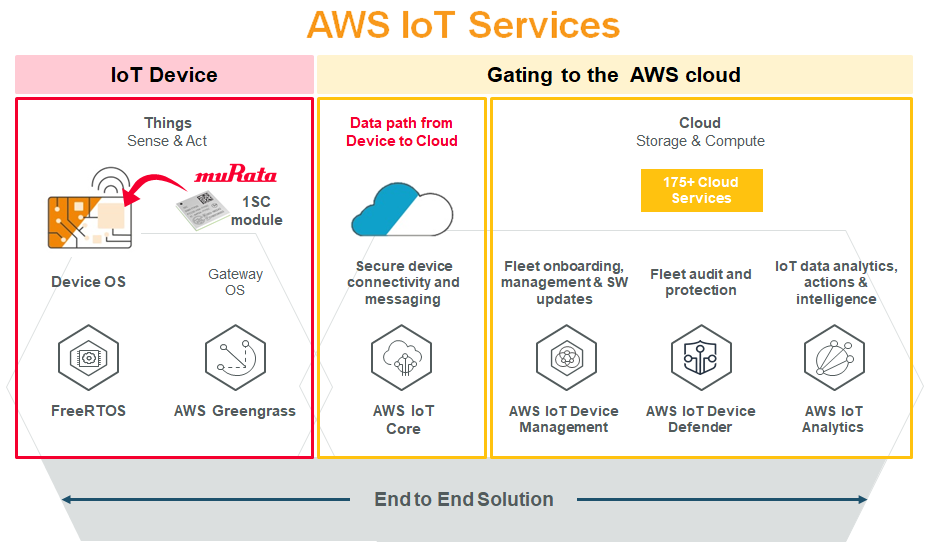
The architecture of AWS IoT remote access is meticulously designed to ensure efficient and secure communication between devices and the cloud. It comprises several components, each playing a critical role in the overall system.
Core Components
- AWS IoT Core: Acts as the central hub for device communication.
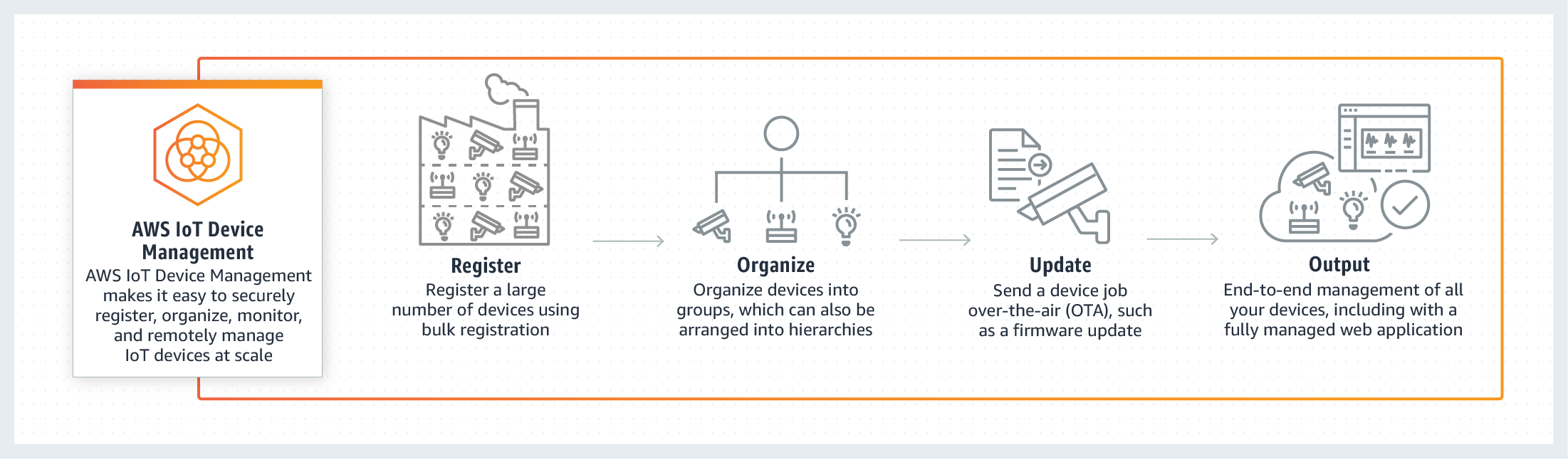
- AWS IoT Device Management: Provides tools for managing device fleets.
- AWS IoT Rules Engine: Processes and routes device data to other AWS services.
Data Flow
Data flows through the system in a structured and secure manner, starting from the device, passing through the AWS IoT Core, and then being routed to the appropriate AWS services for further processing. This ensures that data is handled efficiently and securely at every stage.
Ensuring Robust Security
Security is a top priority in AWS IoT remote access. The service employs a multi-layered approach to safeguard devices and data, incorporating encryption, authentication, and authorization mechanisms.
Encryption
All data transmitted between devices and the cloud is encrypted using industry-standard protocols, ensuring that sensitive information remains secure during transit. This encryption process protects data from unauthorized access and cyber threats.
Read also:Hank Kunneman Age
Authentication and Authorization
Devices must authenticate themselves before connecting to the AWS IoT Core. Additionally, strict authorization policies are in place to ensure that only authorized users and devices can access specific resources. This dual-layer security ensures maximum protection.
Key Benefits
Implementing AWS IoT remote access offers numerous advantages for businesses, including increased efficiency, enhanced security, and improved scalability.
Increased Efficiency
By enabling remote access to devices, businesses can significantly reduce the need for on-site maintenance, saving valuable time and resources. This allows teams to focus on more strategic initiatives, driving innovation and growth.
Enhanced Security
The robust security measures ensure that devices and data are protected from unauthorized access and cyber threats. Businesses can operate with confidence, knowing that their IoT ecosystem is secure.
Improved Scalability
The scalable infrastructure of AWS allows businesses to easily expand their IoT ecosystems as needed, accommodating growth without compromising performance. This flexibility ensures that businesses can adapt to changing demands seamlessly.
Implementation Process
Implementing AWS IoT remote access involves several key steps, from setting up the infrastructure to configuring devices and testing the system.
Step 1: Set Up AWS IoT Core
Begin by setting up the AWS IoT Core in your AWS account. This involves configuring settings such as regions, protocols, and security policies. Proper configuration ensures a solid foundation for your IoT ecosystem.
Step 2: Configure Devices
Once the core is set up, configure your devices to connect to it. This includes installing necessary software and setting up authentication credentials. Proper device configuration is crucial for seamless communication.
Step 3: Test the System
Thoroughly test the system to ensure that devices can connect and communicate with the cloud as expected. Address any issues that arise during testing before deploying the system fully. Testing ensures reliability and performance.
Real-World Applications
AWS IoT remote access has a wide range of applications across various industries. Some common use cases include:
Remote Monitoring in Healthcare
Hospitals and healthcare providers use AWS IoT remote access to monitor medical devices and patient data in real-time. This improves patient care, enhances operational efficiency, and ensures timely interventions.
Smart Manufacturing
Manufacturing companies leverage the technology to monitor production lines and equipment remotely. This enables predictive maintenance, reduces downtime, and optimizes production processes.
Smart Cities
Cities use AWS IoT remote access to manage infrastructure such as traffic lights, streetlights, and waste management systems. This enhances urban living conditions, improves resource management, and promotes sustainability.
Addressing Challenges
While AWS IoT remote access offers many benefits, businesses may face challenges during implementation. These include issues related to connectivity, security, and scalability.
Connectivity Issues
Ensure that devices have a stable internet connection to maintain communication with the AWS IoT Core. Use redundant connections and failover mechanisms to mitigate potential disruptions, ensuring uninterrupted operations.
Security Concerns
Regularly update security policies and protocols to protect against emerging threats. Conduct regular security audits to identify and address vulnerabilities, maintaining a secure IoT ecosystem.
Optimizing System Performance
To maximize the benefits of AWS IoT remote access, it's important to optimize performance through various strategies. These include monitoring system performance, optimizing data usage, and leveraging advanced analytics.
Monitoring Performance
Use AWS CloudWatch and other monitoring tools to track system performance and identify potential bottlenecks or issues. Proactive monitoring ensures that the system operates efficiently and reliably.
Optimizing Data Usage
Implement data compression and filtering techniques to reduce the amount of data transmitted between devices and the cloud. This improves efficiency, reduces costs, and enhances overall system performance.
Future Trends
The future of AWS IoT remote access is bright, with advancements in technology driving new possibilities. Some trends to watch include the integration of AI and machine learning, the expansion of 5G networks, and the development of more advanced security measures.
AI and Machine Learning
AI and machine learning will play a pivotal role in enhancing the capabilities of AWS IoT remote access, enabling more intelligent and autonomous systems. These technologies will drive innovation and improve decision-making processes.
5G Networks
The rollout of 5G networks will provide faster and more reliable connectivity, further improving the performance of IoT systems. This will enable businesses to leverage IoT technologies more effectively, unlocking new opportunities for growth and innovation.
Conclusion and Next Steps
In conclusion, AWS IoT remote access is a powerful solution for businesses aiming to manage IoT devices remotely. With its robust architecture, advanced security features, and wide range of applications, it offers numerous benefits for organizations across various industries.
To take advantage of this technology, consider implementing it in your business operations. Begin by setting up the infrastructure, configuring devices, and testing the system thoroughly. As you move forward, stay updated on the latest trends and advancements in the field to ensure that your IoT ecosystem remains cutting-edge.
We invite you to share your thoughts and experiences with AWS IoT remote access in the comments below. Additionally, feel free to explore other articles on our site for more insights into IoT technologies and their applications.