Are you searching for a dependable method to secure remote access to your Raspberry Pi? As the Raspberry Pi continues to grow in popularity, so does the necessity for robust security measures to ensure safe remote connections. Whether you're a hobbyist, a professional developer, or an IT enthusiast, understanding how to secure your Raspberry Pi is essential for safeguarding your data and maintaining privacy.
The Raspberry Pi has become a versatile device for countless projects, from automating your home to managing servers. However, with its increasing capabilities comes the responsibility to secure your device against unauthorized access, especially when controlling it remotely. In this guide, we will explore the best practices, tools, and techniques for achieving secure remote access for your Raspberry Pi.
By the end of this article, you will have a thorough understanding of how to set up and maintain secure connections to your Raspberry Pi. Whether you're new to the platform or an experienced user, this article will provide valuable insights to enhance your knowledge and skills. Let’s get started!
Read also:Brad Paisley Wife And Kids A Closer Look At The Country Stars Family Life
Contents Overview
- Understanding Raspberry Pi Secure Remote Access
- Why Secure Remote Access is Vital
- SSH for Secure Remote Connections
- Enhancing Security with a VPN
- Setting Up SSH on Raspberry Pi
- Optimizing SSH for Maximum Security
- Exploring Alternative Secure Remote Access Methods
- Best Practices for Raspberry Pi Security
- Troubleshooting Common Issues
- Conclusion
Understanding Raspberry Pi Secure Remote Access
The Raspberry Pi has transformed the world of electronics and computing with its affordability and power. Its adaptability makes it perfect for various applications, from home automation systems to media centers and even web servers. As more users rely on the Raspberry Pi for remote tasks, the importance of secure remote access becomes increasingly significant.
Secure remote access ensures that only authorized individuals can connect to your Raspberry Pi, protecting sensitive data and preventing unauthorized access. This section will introduce the basics of remote access and emphasize why security should be a top priority for Raspberry Pi users.
Why Security is Essential for Remote Connections
When you remotely connect to your Raspberry Pi, you expose it to potential risks such as hacking, malware infections, and unauthorized access. Without appropriate security measures, your device could become vulnerable to cybercriminals. By implementing secure remote access protocols, you can protect your Raspberry Pi and ensure its safety.
Why Secure Remote Access is Vital
In today's interconnected world, securing your devices is not just a convenience but a necessity. Secure remote access for your Raspberry Pi is critical for protecting your data and maintaining privacy. This section will examine the potential risks associated with unsecured remote access and why prioritizing security is essential.
Common Threats to Raspberry Pi Security
Here are some common threats that could compromise your Raspberry Pi if left unprotected:
- Brute Force Attacks: Hackers use automated tools to guess passwords and gain unauthorized access.
- Malware Infections: Malicious software can infiltrate your Raspberry Pi, affecting its performance and security.
- Data Breaches: Sensitive information stored on your Raspberry Pi could be exposed if not adequately secured.
SSH for Secure Remote Connections
Secure Shell (SSH) is one of the most reliable and secure methods for remote access. It provides encrypted communication between your Raspberry Pi and your device, ensuring that your data remains safe during transmission. This section will explore the benefits of SSH and how it functions.
Read also:Miranda Richardson
Advantages of Using SSH
Here are some key advantages of using SSH for Raspberry Pi secure remote access:
- Encryption: SSH encrypts all data transmitted between your Raspberry Pi and your device, preventing unauthorized interception.
- Authentication: SSH employs robust authentication methods to verify the identity of users and devices.
- Flexibility: SSH supports a wide array of commands and protocols, making it adaptable for various applications.
Enhancing Security with a VPN
Beyond SSH, using a Virtual Private Network (VPN) can significantly enhance the security of your Raspberry Pi remote access. A VPN creates a secure tunnel between your device and the internet, shielding your connection from potential threats. This section will explain how a VPN works and why it is beneficial for Raspberry Pi users.
How a VPN Enhances Security
A VPN offers several security benefits for Raspberry Pi users:
- Data Encryption: All data transmitted through a VPN is encrypted, ensuring privacy and security.
- Anonymous Browsing: A VPN masks your IP address, making it challenging for hackers to track your online activities.
- Protection Against Public Wi-Fi Risks: Using a VPN on public Wi-Fi networks protects your Raspberry Pi from potential threats.
Setting Up SSH on Raspberry Pi
Configuring SSH on your Raspberry Pi is a straightforward process that requires minimal technical expertise. This section will guide you step-by-step through the setup process, ensuring you can establish a secure connection to your device.
Step-by-Step Guide to Enabling SSH
Update your Raspberry Pi operating system using the command:
sudo apt update && sudo apt upgrade.Enable SSH by running the command:
sudo raspi-configand selecting the SSH option.Restart your Raspberry Pi to apply the changes:
sudo reboot.
Optimizing SSH for Maximum Security
After enabling SSH, it's crucial to configure it properly to maximize security. This section will provide tips and best practices for securing your SSH connection.
Best Practices for Securing SSH
- Change Default SSH Port: Modify the default SSH port (22) to a non-standard port to reduce the risk of brute force attacks.
- Disable Root Login: Prevent direct root access to your Raspberry Pi by disabling root login in the SSH configuration file.
- Use Strong Passwords: Implement strong, complex passwords to enhance the security of your SSH connection.
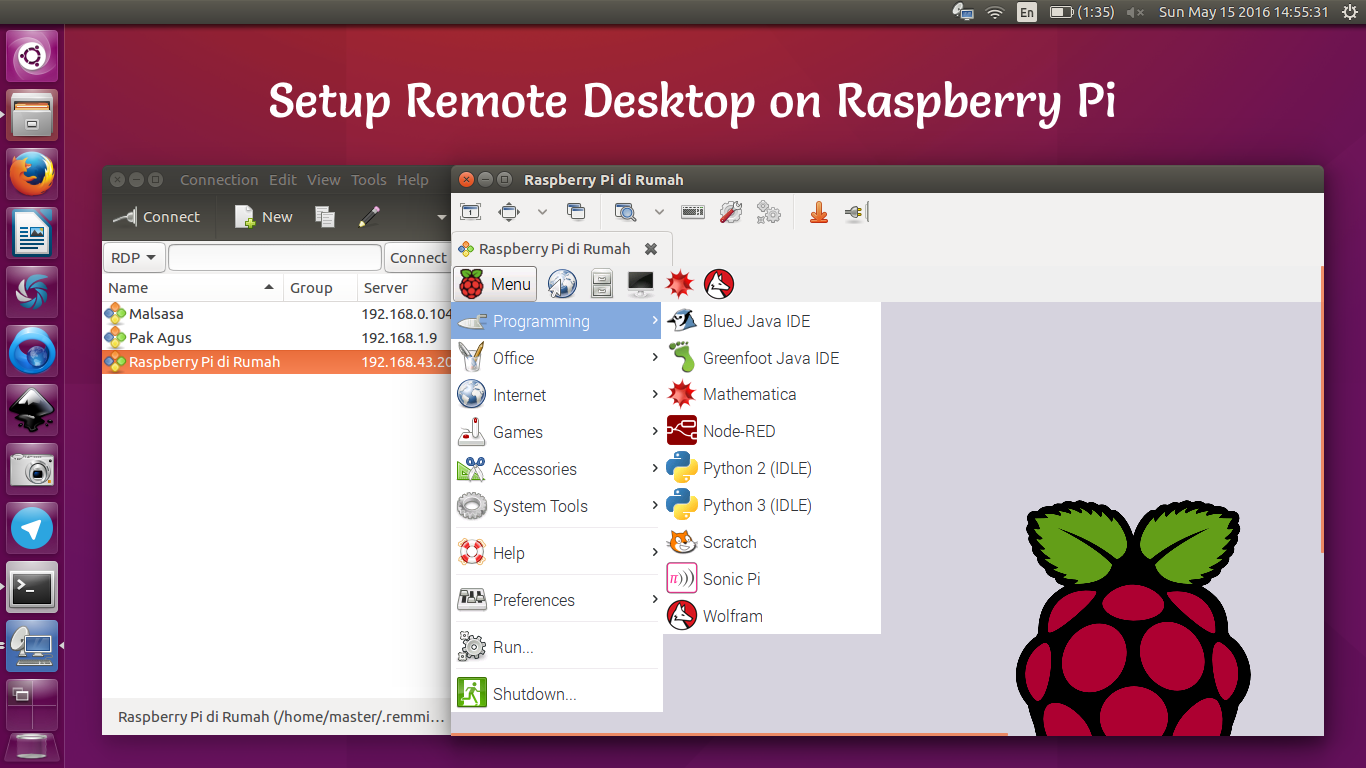
Exploring Alternative Secure Remote Access Methods
While SSH is the most widely used method for secure remote access, there are alternative solutions you can explore. This section will introduce some alternative tools and their benefits.
Discovering Other Remote Access Tools
Here are some alternative tools for Raspberry Pi secure remote access:
- TeamViewer: A user-friendly remote access tool that offers both free and paid versions.
- NoMachine: A fast and secure remote desktop solution that supports multiple platforms.
- VNC: A graphical remote access protocol that allows you to control your Raspberry Pi remotely.
Best Practices for Raspberry Pi Security
Adopting best practices is essential for maintaining the security of your Raspberry Pi. This section will provide actionable tips to ensure your remote access remains secure.
Tips for Securing Your Raspberry Pi
- Regularly Update Software: Keep your Raspberry Pi operating system and applications updated to patch security vulnerabilities.
- Enable Firewall: Use a firewall to restrict unauthorized access to your Raspberry Pi.
- Monitor Logs: Regularly check your system logs for any suspicious activity.
Troubleshooting Common Issues
Even with the best security measures in place, issues can arise. This section will address common problems related to Raspberry Pi secure remote access and provide solutions.
Solving Connection Problems
- Check Network Connectivity: Ensure that your Raspberry Pi is connected to the internet and the network is functioning properly.
- Verify SSH Configuration: Double-check your SSH settings to ensure they are correctly configured.
- Restart Services: Restart the SSH service or reboot your Raspberry Pi to resolve connectivity issues.
Conclusion
Secure remote access for your Raspberry Pi is a critical component of using this powerful device effectively. By implementing the best practices and tools discussed in this article, you can ensure your Raspberry Pi remains secure and protected against potential threats. Remember to regularly update your software, monitor your system logs, and follow security guidelines to maintain the integrity of your device.
We encourage you to share your thoughts and experiences in the comments section below. If you found this article helpful, consider sharing it with others who may benefit from it. For more informative content, explore our other articles and stay updated on the latest trends in technology.