Transform your home network into a powerful tool for secure browsing and remote access by setting up a Raspberry Pi SSH proxy. Whether you're a tech enthusiast or a professional seeking to enhance your cybersecurity measures, this guide will walk you through every step of creating and managing an SSH proxy using Raspberry Pi. From understanding the basics to advanced configurations, this article will equip you with the knowledge to fully utilize your Raspberry Pi's capabilities.
A Raspberry Pi SSH proxy is more than just a buzzword in the tech community—it’s a practical solution for safeguarding your online activities. By tunneling your internet traffic through an encrypted SSH connection, you can bypass geographical restrictions, protect your privacy, and access your home network from anywhere in the world. This guide will delve into the technical details while ensuring the content remains accessible to both beginners and advanced users.
In today's increasingly digital world, cybersecurity is more critical than ever. Setting up a Raspberry Pi SSH proxy is one of the simplest yet most effective ways to secure your online presence. Whether you're a student, a remote worker, or a hobbyist, this guide will provide you with the tools and insights to get started with your Raspberry Pi SSH proxy setup.
Read also:Luke Wilson
Table of Contents
- What is an SSH Proxy?
- Raspberry Pi: An Overview
- Benefits of Using Raspberry Pi SSH Proxy
- Setting Up Raspberry Pi SSH Proxy
- Configuration Steps
- Security Considerations
- Troubleshooting Common Issues
- Advanced Features and Customizations
- Performance Optimization
- Conclusion
Understanding SSH Proxy: A Secure Gateway for Your Internet Traffic
An SSH proxy, often referred to as an SSH tunnel, is a method of securely forwarding network traffic through an encrypted Secure Shell (SSH) connection. This technique allows you to bypass firewalls, mask your IP address, and encrypt your data, making it an indispensable tool for privacy-conscious users. When paired with Raspberry Pi, this compact yet powerful device can serve as a dedicated server for hosting your SSH proxy, providing a reliable and cost-effective solution for enhanced online security.
How Does an SSH Proxy Work?
When you establish an SSH proxy, your internet traffic is routed through the SSH connection, effectively hiding your real IP address. This ensures that your online activities remain private and secure, shielding your data from unauthorized access. The Raspberry Pi, with its low power consumption and compact design, is the perfect platform for hosting such a setup, making it an ideal choice for both personal and professional use.
Key Features of SSH Proxy:
- Encrypted data transfer to protect sensitive information
- IP address masking for enhanced anonymity
- Bypassing geographical restrictions to access restricted content
- Secure remote access to your home network from anywhere in the world
Raspberry Pi: The Ideal Platform for Hosting an SSH Proxy
Raspberry Pi is a series of single-board computers developed by the Raspberry Pi Foundation. Renowned for its affordability and versatility, Raspberry Pi has become a favorite among hobbyists, educators, and professionals alike. Its robust hardware and extensive software support make it the perfect device for hosting an SSH proxy, offering a seamless and efficient solution for secure internet browsing.
Why Choose Raspberry Pi for SSH Proxy?
Raspberry Pi stands out as an excellent choice for setting up an SSH proxy due to several key advantages:
- Low power consumption, ensuring minimal energy usage even during prolonged operation
- Compact size, making it easy to integrate into any home or office setup
- Highly customizable, allowing users to tailor the setup to their specific needs
- Support for a wide range of operating systems, providing flexibility in software selection
Raspberry Pi's ability to run lightweight Linux distributions enables it to handle resource-intensive services like SSH proxies without compromising performance, making it a reliable and efficient choice for secure internet browsing.
Read also:Is Park Bo Gum Married
Key Benefits of Implementing a Raspberry Pi SSH Proxy
Setting up a Raspberry Pi SSH proxy offers numerous advantages that cater to both personal and professional needs. Below are some of the key benefits you can expect:
Enhanced Security for Your Online Activities
By encrypting your internet traffic, an SSH proxy ensures that your data remains secure from potential threats. This is especially beneficial when connecting to public Wi-Fi networks or accessing sensitive information remotely, providing an additional layer of protection against unauthorized access.
Geographical Flexibility for Unrestricted Access
With an SSH proxy, you can bypass geographical restrictions imposed by websites or streaming services. This allows you to access content that may not be available in your region, giving you the freedom to explore the internet without limitations.
A Cost-Effective Alternative to Commercial Proxy Services
Raspberry Pi offers a budget-friendly alternative to commercial proxy services. By leveraging open-source software and affordable hardware, you can set up a reliable SSH proxy without incurring high costs, making it an attractive option for individuals and small businesses alike.
A Step-by-Step Guide to Setting Up Your Raspberry Pi SSH Proxy
Setting up a Raspberry Pi SSH proxy involves several steps, from preparing your hardware to configuring the software. Follow this comprehensive guide to ensure a smooth setup process:
Hardware Requirements for Your SSH Proxy Setup
Before you begin, ensure you have the following hardware components:
- Raspberry Pi (any model with SSH support)
- MicroSD card with Raspberry Pi OS installed
- Power supply compatible with your Raspberry Pi model
- Ethernet cable or Wi-Fi adapter for network connectivity
Software Setup for Your Raspberry Pi
Once your hardware is ready, proceed with the software installation:
- Download and install Raspberry Pi OS on your MicroSD card
- Enable SSH in the Raspberry Pi Configuration to allow remote access
- Set up a static IP address for your Raspberry Pi to ensure consistent network connectivity
Configuration Steps for Your Raspberry Pi SSH Proxy
Configuring your Raspberry Pi SSH proxy requires careful attention to detail. Follow these steps to ensure a successful setup:
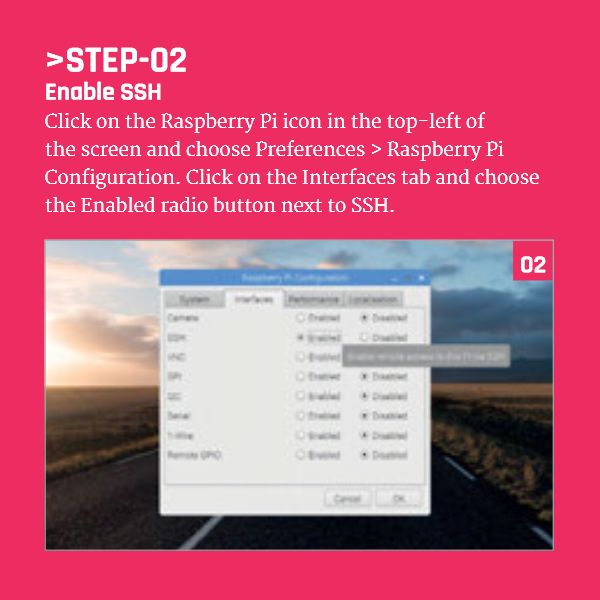
Step 1: Enable SSH on Your Raspberry Pi
To enable SSH on your Raspberry Pi, navigate to the Raspberry Pi Configuration menu and select the "Interfaces" tab. From there, enable SSH and apply the changes to activate the service.
Step 2: Install Required Packages for SSH
Open a terminal and run the following commands to install necessary packages:
sudo apt update
sudo apt install openssh-server
Step 3: Configure the SSH Tunnel
Set up the SSH tunnel by modifying the SSH configuration file. Use a text editor to edit the file located at /etc/ssh/sshd_config, ensuring that the necessary settings are properly configured for optimal performance.
Security Best Practices for Your Raspberry Pi SSH Proxy
While an SSH proxy enhances your security, it's essential to implement additional measures to protect your setup:
Use Strong Passwords for Enhanced Security
Ensure that all user accounts on your Raspberry Pi have strong, unique passwords to prevent unauthorized access. Consider enabling two-factor authentication for added security, providing an extra layer of protection against potential threats.
Regularly Update Your System for Optimal Security
Keep your Raspberry Pi OS and installed packages up to date to protect against vulnerabilities. Use the following commands to update your system:
sudo apt update
sudo apt upgrade
Troubleshooting Common Issues with Your Raspberry Pi SSH Proxy
Encountering issues during setup is not uncommon. Below are some common problems and their solutions:
SSH Connection Fails to Establish
If you're unable to establish an SSH connection, verify that SSH is enabled and check your network settings. Ensure that your Raspberry Pi's IP address is correct and accessible from your device, resolving any network-related issues that may arise.
Slow Performance of Your SSH Proxy
If your SSH proxy is running slowly, consider optimizing your network configuration or upgrading your hardware. A faster Ethernet connection or a more powerful Raspberry Pi model may significantly improve performance, ensuring a smoother browsing experience.
Exploring Advanced Features to Enhance Your Raspberry Pi SSH Proxy
Once your Raspberry Pi SSH proxy is up and running, you can explore advanced features to enhance its functionality:
Port Forwarding for Secure Service Access
Set up port forwarding to allow specific services to pass through your SSH proxy. This can be particularly useful for running web servers or accessing remote databases securely, expanding the capabilities of your setup.
Custom Scripts for Automation and Optimization
Create custom scripts to automate tasks such as monitoring bandwidth usage or logging connection attempts. These scripts can help you maintain and optimize your SSH proxy more effectively, ensuring it operates at peak performance.
Tips for Optimizing the Performance of Your Raspberry Pi SSH Proxy
Optimizing your Raspberry Pi SSH proxy can significantly improve its performance. Consider the following tips:
Choose a Lightweight Operating System
Opt for a lightweight Linux distribution designed for Raspberry Pi, such as Raspbian Lite, to reduce resource consumption and enhance system efficiency.
Monitor Resource Usage for Optimal Performance
Regularly monitor your Raspberry Pi's CPU and memory usage to identify potential bottlenecks. Use tools like htop or Glances to gain insights into system performance, enabling you to make informed decisions to optimize your setup.
Conclusion: Building a Safer and More Connected Digital World
Setting up a Raspberry Pi SSH proxy is a powerful way to enhance your cybersecurity and access the internet securely from anywhere. By following the steps outlined in this guide, you can create a reliable and efficient SSH proxy tailored to your needs. Remember to prioritize security and regularly update your system to protect against potential threats.
We encourage you to share your experiences and ask questions in the comments section below. Additionally, explore other articles on our site to discover more ways to leverage Raspberry Pi for your projects. Together, let's build a safer and more connected digital world!