Establishing a secure VNC server on your Raspberry Pi 3 is crucial to safeguard your device from unauthorized access and cyber threats. As Raspberry Pi continues to gain popularity across various projects, the importance of robust security measures cannot be overstated. A VNC (Virtual Network Computing) server allows you to remotely access and control your Raspberry Pi, but without proper security configurations, your device could be vulnerable to hackers and malicious actors.
In this guide, we will delve into the essential steps and best practices to secure your Raspberry Pi 3 VNC server. From setting up firewalls and enabling encryption protocols to adopting strong authentication methods, you'll learn how to protect your device while maintaining seamless remote access. Whether you're a beginner or an experienced user, this article will equip you with actionable insights to enhance the security of your Raspberry Pi.
By the conclusion of this guide, you'll have a thorough understanding of the risks associated with unsecured VNC servers and how to mitigate them effectively. Let’s get started!
Read also:Jason Momoa Height
Table of Contents
- Introduction to Securing Your RPi3 VNC Server
- Understanding the Potential Risks of an Insecure VNC Server
- Installing and Configuring a VNC Server on RPi3
- Implementing Encryption for VNC Connections
- Configuring Firewall Settings for Enhanced Protection
- Adopting Strong Passwords and Authentication Methods
- Ensuring Your RPi3 Remains Up to Date
- Fortifying Your Network Environment
- Monitoring Your RPi3 for Suspicious Activity
- Exploring Alternative Remote Access Solutions
- Conclusion and Final Thoughts
Introduction to Securing Your RPi3 VNC Server
Why Security is Essential for Your RPi3 VNC Server
Raspberry Pi 3 is a versatile and powerful single-board computer used in a wide array of applications, from home automation systems to IoT projects. When you set up a VNC server on your RPi3, it creates a potential entry point for cybercriminals if left unsecured. Implementing robust security measures is vital to protect sensitive data and ensure the integrity of your device.
VNC servers enable remote access to your Raspberry Pi’s graphical interface, allowing you to control it from another computer or device. While this feature is incredibly useful, it also introduces risks such as unauthorized access, data breaches, and malware infections. By implementing the appropriate security protocols, you can minimize these risks and safely enjoy the benefits of remote access.
Understanding the Potential Risks of an Insecure VNC Server
Common Threats to Your RPi3 VNC Server
An insecure VNC server can expose your Raspberry Pi to several types of threats:
- Brute Force Attacks: Hackers can attempt to guess your password by trying multiple combinations until they succeed, gaining unauthorized access to your device.
- Man-in-the-Middle Attacks: Without encryption, attackers can intercept and manipulate your VNC traffic, potentially gaining access to sensitive information.
- Malware Injection: Unauthorized access can lead to the installation of malicious software on your device, compromising its functionality and security.
- Data Theft: Sensitive information stored on your Raspberry Pi can be stolen if the VNC server is compromised, leading to potential privacy violations and financial losses.
These risks underscore the necessity of securing your VNC server to protect your device and data from malicious actors. By addressing these vulnerabilities, you can significantly enhance the security of your Raspberry Pi.
Installing and Configuring a VNC Server on RPi3
Step-by-Step Guide to Setting Up Your VNC Server
Before diving into advanced security measures, let’s first walk through the process of setting up a VNC server on your Raspberry Pi 3:
- Begin by updating your Raspberry Pi's operating system using the command:
sudo apt update && sudo apt upgrade. - Install the VNC server by running the command:
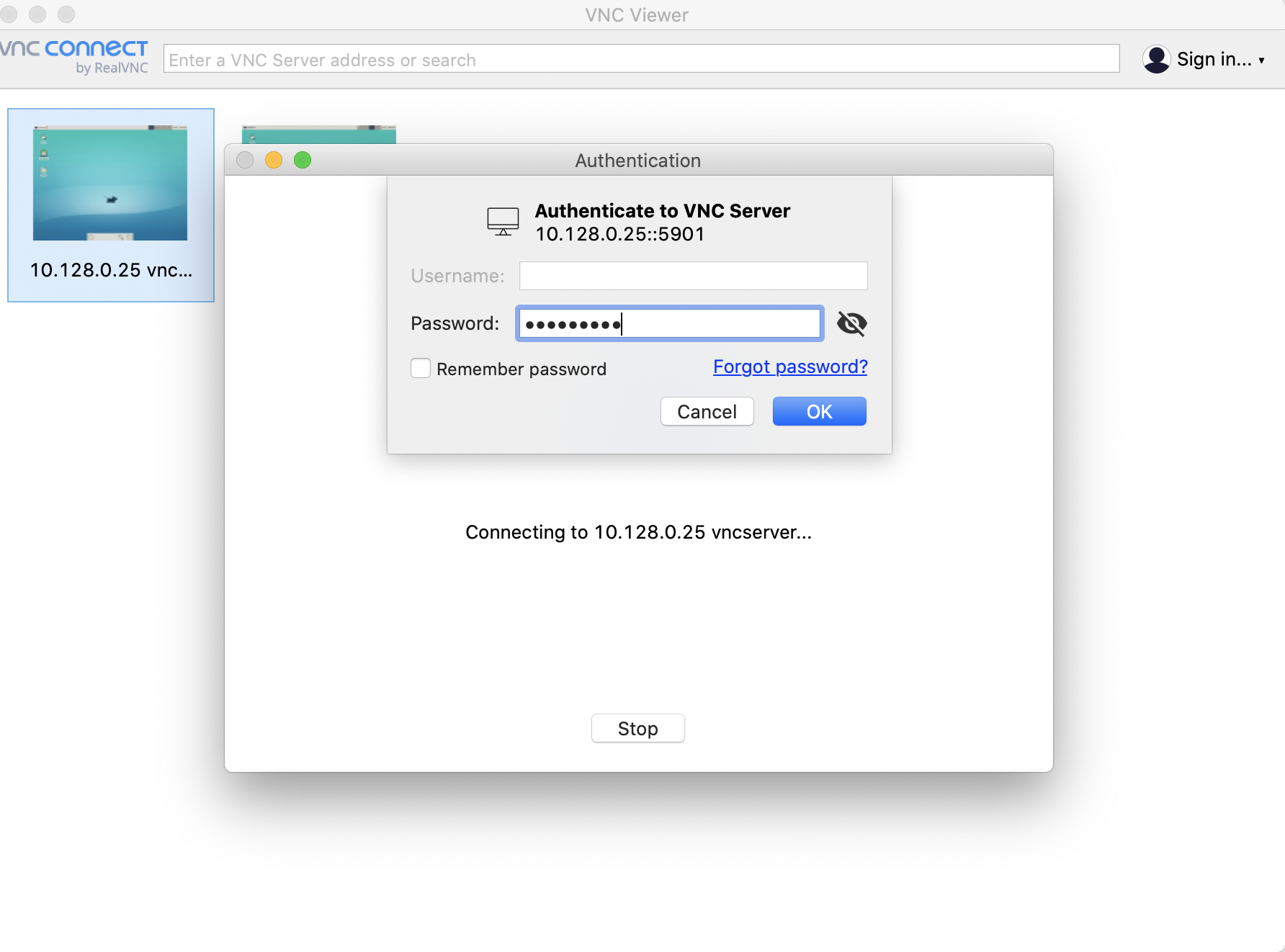
sudo apt install realvnc-vnc-server realvnc-vnc-viewer. - Enable VNC through the Raspberry Pi Configuration tool or by using the command:
sudo raspi-config. - Set a secure password for your VNC server by navigating to the VNC options in the Raspberry Pi Configuration menu.
Once your VNC server is installed and configured, you can proceed to enhance its security with additional measures.
Read also:Brian Musso Net Worth
Implementing Encryption for VNC Connections
The Importance of Encryption in Securing Your VNC Server
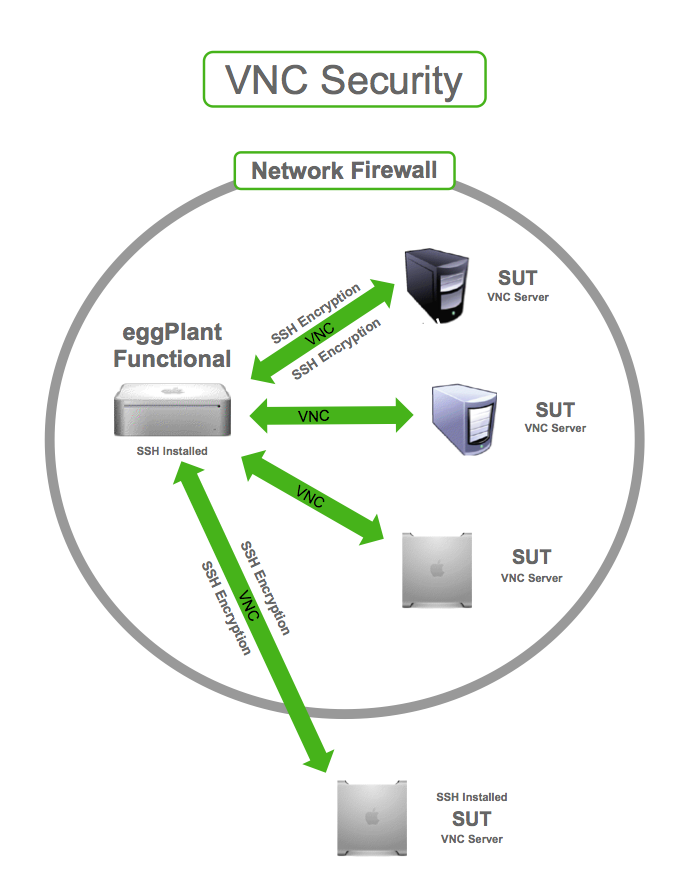
Encryption is a critical component in ensuring that your VNC traffic is securely transmitted between your Raspberry Pi and the client device. Without encryption, your data can be intercepted and read by attackers. To enable encryption for your VNC connections:
- Use VNC Connect, which supports AES encryption by default, to secure your communications.
- Configure your VNC server to require encrypted connections in the settings menu, ensuring that all traffic is protected.
- Consider using an SSH tunnel to further secure your VNC traffic, adding an additional layer of protection against potential threats.
By implementing encryption, you can significantly reduce the risk of man-in-the-middle attacks and data interception, enhancing the overall security of your VNC server.
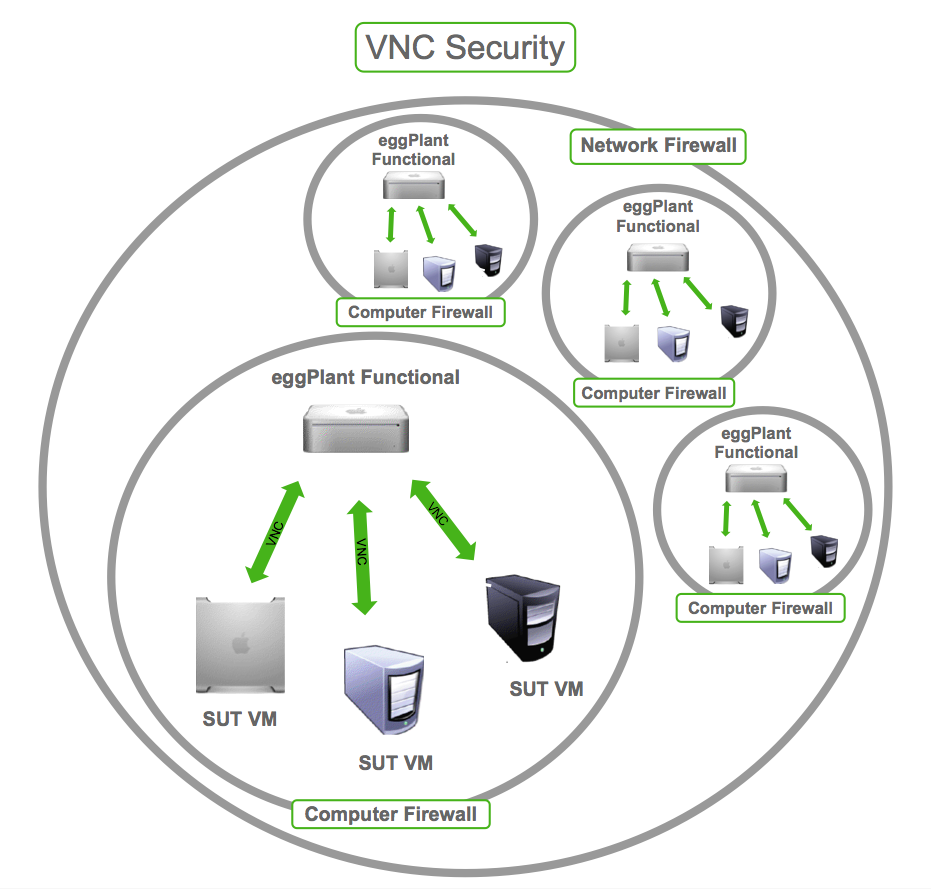
Configuring Firewall Settings for Enhanced Protection
Using UFW to Safeguard Your RPi3
A firewall acts as a protective barrier between your Raspberry Pi and the outside world, allowing only authorized traffic to pass through. To configure a firewall on your RPi3:
- Install UFW (Uncomplicated Firewall) using the command:
sudo apt install ufw. - Allow VNC traffic by running the command:
sudo ufw allow 5900(or the port number your VNC server is using). - Enable the firewall with the command:
sudo ufw enable.
Configuring a firewall helps prevent unauthorized access and protects your device from potential attacks, ensuring that only legitimate traffic reaches your Raspberry Pi.
Adopting Strong Passwords and Authentication Methods
Best Practices for Enhancing Password Security
Using strong passwords is one of the simplest yet most effective ways to secure your RPi3 VNC server. Follow these best practices to enhance your password security:
- Create complex passwords that include a mix of uppercase and lowercase letters, numbers, and special characters to make them harder to guess.
- Avoid using easily guessable information such as birthdays, names, or common words that could be easily exploited by attackers.
- Enable two-factor authentication (2FA) if supported by your VNC server, adding an additional layer of protection against unauthorized access.
Strong passwords serve as the first line of defense against unauthorized access, ensuring that your device remains secure even if other security measures are compromised.
Ensuring Your RPi3 Remains Up to Date
The Importance of Regular Software and Firmware Updates
Regularly updating your Raspberry Pi's software and firmware is crucial for maintaining security. Updates often include patches for known vulnerabilities and improvements to existing features. To keep your RPi3 up to date:
- Run the command
sudo apt update && sudo apt upgradeperiodically to install the latest updates and security patches. - Check for firmware updates using the command:
sudo rpi-update, ensuring that your device is equipped with the latest security enhancements.
Staying current with updates ensures that your device is protected against the latest threats, reducing the risk of potential security breaches.
Fortifying Your Network Environment
Steps to Secure Your Local Network
Your Raspberry Pi's security is closely tied to the security of your local network. Here are some steps to secure your network environment:
- Change your router's default admin credentials to a strong password, reducing the risk of unauthorized access to your network settings.
- Enable WPA3 encryption for your Wi-Fi network if supported by your router, providing a higher level of security for wireless communications.
- Disable remote management features on your router unless absolutely necessary, minimizing the attack surface for potential intrusions.
A secure network environment plays a crucial role in protecting your Raspberry Pi from unauthorized access, ensuring that your device remains safe from external threats.
Monitoring Your RPi3 for Suspicious Activity
Tools to Help Detect and Respond to Potential Security Threats
Monitoring your Raspberry Pi for suspicious activity can help you detect and respond to potential security threats quickly. Consider using the following tools to enhance your monitoring capabilities:
- Fail2Ban: This tool automatically blocks IP addresses that exhibit malicious behavior, such as repeated failed login attempts, reducing the risk of brute force attacks.
- Logwatch: Analyzes system logs and sends you a detailed report of any unusual activity, enabling you to stay informed about the security status of your device.
By actively monitoring your device, you can proactively address potential security issues, ensuring that your Raspberry Pi remains secure at all times.
Exploring Alternative Remote Access Solutions
Other Options for Secure Remote Access
While VNC is a popular choice for remote access, there are other solutions you might consider depending on your specific needs and security requirements:
- SSH: Secure Shell provides a secure method for accessing your Raspberry Pi's command-line interface, offering robust encryption and authentication features.
- TeamViewer: Offers cross-platform remote access with built-in security features, making it a versatile option for managing your devices remotely.
- NoMachine: Provides high-performance remote access with strong encryption, ensuring secure and efficient connectivity for your Raspberry Pi.
Exploring alternative solutions can help you find the best fit for your specific requirements, enhancing both the functionality and security of your remote access setup.
Conclusion and Final Thoughts
Securing your Raspberry Pi 3 VNC server is essential for protecting your device and data from cyber threats. By following the steps outlined in this guide, you can significantly enhance the security of your VNC server and enjoy safe remote access to your Raspberry Pi. Remember to regularly update your software, use strong passwords, and monitor your device for any suspicious activity to maintain a secure environment.
We encourage you to take immediate action by implementing these security measures today. Share this article with others who may benefit from it, and feel free to leave a comment if you have any questions or additional tips. Together, we can create a safer digital environment for everyone.