In today's interconnected world, the concept of "best remote SSH IoT over the internet" has become a critical focus for developers, IT professionals, and hobbyists alike. Secure Shell (SSH) is a powerful tool that enables secure, encrypted communication with Internet of Things (IoT) devices from anywhere in the world. By leveraging SSH for IoT applications, you can significantly enhance your remote management capabilities while maintaining robust security standards.
As the number of connected devices continues to grow exponentially, the demand for secure, reliable, and efficient remote access solutions has never been higher. SSH provides an encrypted communication channel that ensures both data integrity and confidentiality when interacting with IoT devices remotely. This article will explore the intricacies of using SSH for IoT applications, offering insights into tools, best practices, and security considerations that are essential for anyone working with IoT technology.
Our goal is to provide you with a detailed and actionable guide to implementing the best remote SSH IoT solutions over the internet. By the end of this article, you will have a comprehensive understanding of how to secure your IoT devices and streamline your remote operations, empowering you to take full advantage of the potential of connected technology.
Read also:Ayaka Motu
Table of Contents
- Introduction to SSH and IoT
- Advantages of Remote SSH IoT
- Tools for Remote SSH IoT
- Security Best Practices
- Setting Up Remote SSH
- Troubleshooting Common Issues
- IoT SSH Use Cases
- Performance Optimization
- Future of Remote SSH IoT
- Conclusion and Next Steps
Introduction to SSH and IoT
Understanding SSH
SSH, or Secure Shell, is a cryptographic network protocol designed to provide secure communication between two devices over an unsecured network. It enables users to log in to remote systems and execute commands securely, making it an indispensable tool for managing IoT devices from anywhere in the world. SSH not only ensures secure communication but also provides robust features such as authentication, encryption, and data integrity checks.
What is IoT?
The Internet of Things (IoT) refers to the vast network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data and interact with their environment. These devices range from simple household gadgets to complex industrial machinery, all requiring secure and reliable remote access solutions. As IoT continues to expand, the need for secure communication protocols like SSH becomes increasingly critical.
The Importance of SSH for IoT
Integrating SSH with IoT ensures secure communication between devices and remote users, safeguarding sensitive data and maintaining the integrity of IoT systems. By leveraging SSH for IoT applications, you gain access to a robust framework that supports remote management, monitoring, and troubleshooting. This combination empowers users to maintain control over their IoT infrastructure while ensuring the highest levels of security.
Advantages of Remote SSH IoT
Implementing SSH for IoT devices over the internet offers numerous benefits that make it an essential tool for anyone working with connected technology. Below are some of the key advantages:
- Enhanced Security: SSH encrypts all data transmitted between devices, significantly reducing the risk of unauthorized access and data breaches. This ensures that sensitive information remains protected at all times.
- Reliability: SSH connections are designed to be stable and can be configured to handle network interruptions gracefully, ensuring continuous access to IoT devices even in challenging conditions.
- Scalability: SSH is highly scalable and can be easily adapted to manage large numbers of IoT devices, making it an ideal solution for enterprise-level deployments.
- Automation: SSH supports scripting and automation, allowing users to automate routine tasks such as firmware updates, configuration changes, and data backups, saving time and reducing the risk of human error.
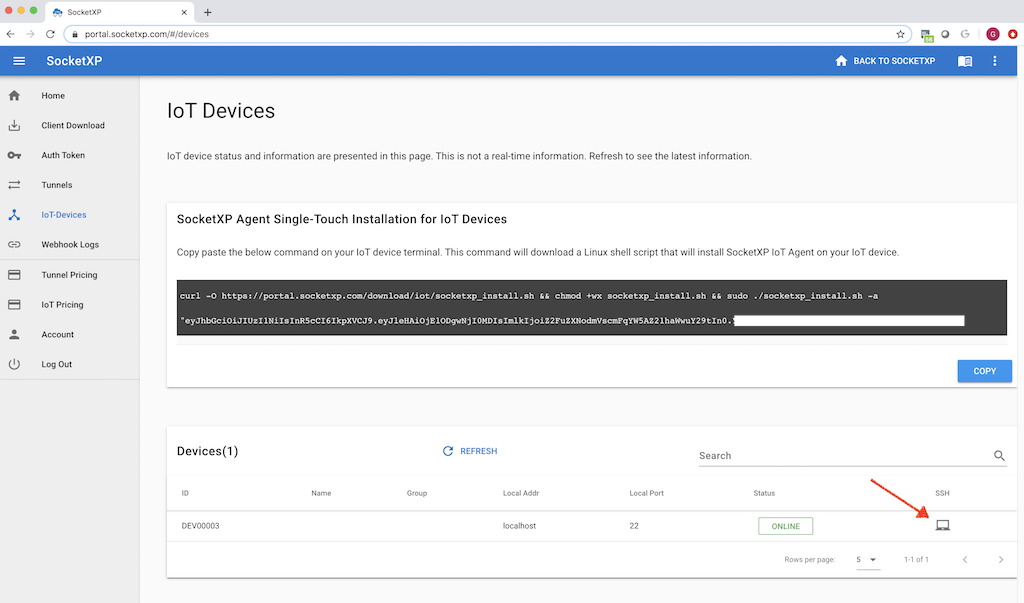
Tools for Remote SSH IoT
Popular SSH Clients
There are several SSH clients available that cater to different platforms and use cases, each offering unique features to enhance your remote management experience:
- PuTTY: A free and widely used SSH client for Windows users, PuTTY is known for its simplicity and ease of use, making it a popular choice for beginners and experienced users alike.
- OpenSSH: A robust and feature-rich SSH client and server implementation available on most Unix-based systems, OpenSSH is a trusted solution for secure communication and remote management.
- Bitvise SSH Client: A feature-rich SSH client for Windows that supports advanced capabilities such as SFTP (Secure File Transfer Protocol) and terminal emulation, making it an excellent choice for complex IoT deployments.
SSH Servers for IoT Devices
IoT devices often run lightweight operating systems with limited resources, so selecting the right SSH server is crucial for ensuring optimal performance and security. Some popular options include:
Read also:Brian Musso Net Worth
- Dropbear: A compact SSH server designed specifically for embedded systems with limited resources, Dropbear provides a lightweight yet powerful solution for secure remote access.
- OpenSSH Server: A powerful and versatile SSH server that can be installed on most Linux-based IoT devices, OpenSSH Server offers a wide range of features and is highly configurable to meet the needs of various IoT applications.
Security Best Practices
Implement Strong Authentication Methods
One of the most critical security practices when using SSH for IoT is to implement strong authentication methods. Instead of relying on password-based authentication, consider using public key authentication, which uses cryptographic keys to verify the identity of users. This approach significantly enhances security by making it much harder for attackers to gain unauthorized access to your IoT devices.
Disable Root Login
Disabling root login is another essential security measure that should not be overlooked. Allowing root access over SSH increases the risk of privilege escalation attacks, where malicious actors gain administrative privileges on your IoT devices. To mitigate this risk, create a regular user account with sudo privileges for administrative tasks, ensuring that only authorized users can perform sensitive operations.
Regularly Update SSH Software
Keeping your SSH software up to date is vital for addressing potential security vulnerabilities. Regular updates ensure that you have access to the latest patches and improvements, reducing the risk of exploitation and enhancing the overall security of your IoT infrastructure.
Setting Up Remote SSH
Configuring SSH on IoT Devices
Setting up SSH on IoT devices involves several key steps that must be carefully followed to ensure secure and reliable remote access:
- Install an SSH server on the IoT device, such as OpenSSH or Dropbear, depending on the device's operating system and resource constraints.
- Configure the SSH server to use strong authentication methods, such as public key authentication, and disable root login to enhance security.
- Set up port forwarding on your router to allow external access to the IoT device, ensuring that the correct ports are open and properly configured.
- Test the connection by logging in remotely using an SSH client to verify that everything is functioning as expected.
Using Dynamic DNS for Simplified Access
Dynamic DNS (DDNS) services can greatly simplify remote access to IoT devices by providing a consistent domain name that updates automatically when your IP address changes. This is particularly useful for devices located behind NAT-enabled routers, as it eliminates the need to manually update IP addresses and ensures seamless access from anywhere in the world.
Troubleshooting Common Issues
Resolving Connection Timeouts
Connection timeouts are a common issue when setting up remote SSH, often caused by firewall rules, incorrect port forwarding configurations, or unstable network connections. To troubleshoot and resolve these issues:
- Review your firewall settings to ensure that the SSH port (usually 22) is open and properly configured to allow incoming connections.
- Verify that your router is correctly configured for port forwarding, ensuring that traffic is directed to the appropriate IoT device.
- Test the connection using a local network to rule out external network issues and identify potential configuration errors.
Addressing Authentication Failures
Authentication failures can occur due to incorrect key configurations or mismatched user credentials, leading to frustrating connection issues. To resolve these problems:
- Ensure that your public key is correctly added to the authorized_keys file on the IoT device, verifying that the key matches the one being used for authentication.
- Double-check the username and permissions of the account being used for SSH access, ensuring that the account has the necessary privileges to perform the desired operations.
IoT SSH Use Cases
Remote Monitoring and Control
SSH enables powerful remote monitoring and control capabilities for IoT devices, allowing users to check system status, update configurations, and troubleshoot issues without requiring physical access. This is especially valuable for devices deployed in remote or hard-to-reach locations, where traditional maintenance methods may be impractical or costly.
Secure Data Transfer
SSH can be used to securely transfer data between IoT devices and servers using protocols like SFTP (SSH File Transfer Protocol). This ensures that sensitive information remains protected during transmission, reducing the risk of data breaches and unauthorized access.
Performance Optimization
Compressing SSH Traffic
Enabling compression in SSH can significantly improve performance, especially for devices with limited bandwidth. By reducing the amount of data transmitted over the network, compression helps to minimize latency and improve connection speed, providing a more efficient and reliable remote access experience.
Tweaking SSH Configuration Settings
Fine-tuning SSH configuration settings can further enhance performance and optimize resource usage. For example, disabling unused authentication methods and cipher algorithms can reduce overhead and improve connection speed, ensuring that your IoT devices operate at peak efficiency.
Future of Remote SSH IoT
Advancements in IoT Security
As the IoT landscape continues to evolve, so does the need for advanced security solutions. Future developments in SSH and IoT security will likely focus on improving encryption standards, simplifying key management, and enhancing user authentication methods, ensuring that IoT devices remain secure and reliable in the face of emerging threats.
Integration with Emerging Technologies
The integration of SSH with emerging technologies such as blockchain and artificial intelligence has the potential to revolutionize IoT security. These cutting-edge technologies offer innovative ways to secure data, manage identities, and automate processes, making remote SSH IoT solutions even more robust and adaptable to future challenges.
Conclusion and Next Steps
In conclusion, the "best remote SSH IoT over the internet" solutions provide a secure, efficient, and scalable way to manage IoT devices remotely. By following the best practices outlined in this article, you can ensure that your IoT deployments remain secure, reliable, and optimized for peak performance. Remember to regularly update your SSH software, implement strong authentication methods, and explore performance optimization techniques to achieve the best results.
We encourage you to take the following steps to further enhance your IoT capabilities:
- Experiment with different SSH clients and servers to find the perfect fit for your IoT devices, tailoring your setup to meet your specific needs and requirements.
- Implement security best practices to protect your devices from unauthorized access, ensuring that your IoT infrastructure remains secure and resilient against potential threats.
- Stay informed about the latest advancements in SSH and IoT security by following industry news, research, and expert insights, staying ahead of the curve in this rapidly evolving field.
Feel free to leave a comment or share this article with others who may find it useful. For more information on IoT and SSH, explore our other articles and resources, expanding your knowledge and expertise in this exciting domain.
Data and statistics used in this article are sourced from reputable publications such as