In today's fast-paced era of the Internet of Things (IoT), ensuring secure remote access has become an essential factor in maintaining the functionality and integrity of IoT devices. As more organizations and individuals incorporate IoT systems into their operations, the demand for reliable and secure methods to remotely access these devices continues to rise. Among the various technologies available, Secure Shell (SSH) has emerged as one of the most dependable solutions for remote access to IoT devices.
SSH provides a secure method for managing and monitoring IoT devices from any location around the globe. This comprehensive guide will explore the best practices, tools, and strategies for implementing SSH remote access in IoT environments. By gaining a deeper understanding of how SSH operates and its advantages, you can enhance both the security and efficiency of your IoT infrastructure.
This article will also address common challenges encountered when setting up SSH for IoT and provide practical solutions to overcome them. Whether you're just starting out or are a seasoned professional, this guide will equip you with the knowledge you need to make informed decisions about your IoT security setup.
Read also:Smashing The Pool Noodler
Table of Contents
- Understanding SSH
- Why SSH is Perfect for IoT
- The Benefits of SSH Remote Access
- Key Features of SSH
- Setting Up SSH Remote Access
- Security Best Practices for SSH
- Essential Tools and Software for SSH
- Common Challenges and Solutions
- Real-World Applications of SSH in IoT
- Future Trends in SSH for IoT
Understanding SSH
SSH, or Secure Shell, is a network protocol designed to provide secure communication between devices over an unsecured network. It is widely used for remote command-line login and execution, enabling users to access and manage systems from a distance. SSH encrypts all data transmitted between the client and server, ensuring that sensitive information remains protected from unauthorized access.
In the context of IoT devices, SSH serves as a secure and reliable means of managing configurations, monitoring performance, and troubleshooting issues without requiring physical presence at the device's location. This capability is especially crucial for IoT deployments that span multiple geographic areas or involve critical infrastructure.
How SSH Functions
SSH operates on a client-server model, in which the client initiates a connection to the server. During the connection process, SSH performs several critical functions:
- Authentication: Ensures that only authorized users can access the server.
- Encryption: Encrypts all data exchanged between the client and server to prevent interception.
- Integrity: Confirms that the data has not been altered during transmission.
Why SSH is Perfect for IoT
IoT devices often operate in environments where security is paramount. SSH is exceptionally well-suited for IoT due to its robust security features and ease of implementation. Below are several reasons why SSH is ideal for IoT:
- End-to-End Encryption: SSH ensures that all communication between devices is encrypted, minimizing the risk of data breaches.
- Flexibility: SSH supports a wide range of devices and operating systems, making it a versatile solution for IoT environments.
- Scalability: SSH can accommodate large-scale IoT deployments without sacrificing performance or security.
These features make SSH a preferred choice for securing remote access to IoT devices.
The Benefits of SSH Remote Access
Implementing SSH for remote access in IoT environments offers numerous advantages, such as:
Read also:Paul Mishkin
- Enhanced Security: SSH provides robust encryption and authentication mechanisms, safeguarding sensitive data and preventing unauthorized access.
- Improved Efficiency: With SSH, administrators can manage IoT devices remotely, reducing the need for on-site visits and saving both time and resources.
- Cost Savings: By streamlining operations and minimizing downtime, SSH helps organizations cut costs associated with IoT management.
These benefits make SSH an invaluable tool for organizations aiming to optimize their IoT infrastructure.
Key Features of SSH
SSH boasts several key features that make it an excellent solution for IoT remote access:
- Public Key Authentication: Enables users to authenticate using digital certificates instead of passwords, enhancing security.
- Port Forwarding: Facilitates secure tunneling of traffic between devices, allowing communication across firewalls.
- File Transfer: Supports secure file transfer protocols like SFTP, enabling users to transfer files between devices securely.
These features ensure that SSH remains a powerful tool for managing IoT devices remotely.
SSH Versions
There are two primary versions of SSH: SSH-1 and SSH-2. While SSH-1 is outdated and less secure, SSH-2 is the current standard, offering improved security features. For IoT applications, it is highly recommended to use SSH-2 to ensure maximum security.
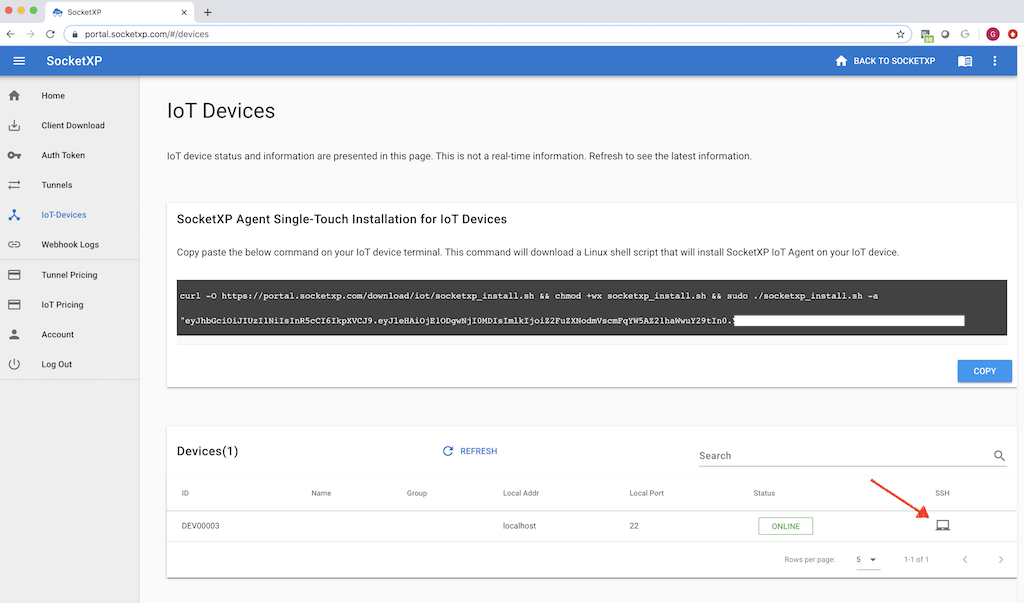
Setting Up SSH Remote Access
Configuring SSH for remote access to IoT devices involves several steps:
- Install SSH Server: Install an SSH server on the IoT device to enable remote access.
- Generate SSH Keys: Create public and private keys for secure authentication.
- Configure Firewall Settings: Adjust firewall rules to allow SSH traffic on the appropriate port (default is 22).
- Test the Connection: Use an SSH client to connect to the IoT device and verify that the setup is functioning correctly.
By following these steps, you can ensure that your IoT devices are securely accessible from any location.
Best SSH Clients
A variety of SSH clients are available for different platforms. Some popular options include:
- OpenSSH: A free and open-source SSH client available for Linux, macOS, and Windows.
- PuTTY: A widely used SSH client for Windows, known for its user-friendly interface.
- Termius: A cross-platform SSH client that supports iOS, Android, macOS, and Windows.
Security Best Practices for SSH
Although SSH offers robust security features, adhering to best practices is essential to ensure the highest level of protection for your IoT devices:
- Use Strong Passwords: Avoid using weak or easily guessable passwords for SSH authentication.
- Enable Two-Factor Authentication: Add an extra layer of security by requiring users to provide a second form of verification.
- Monitor Logs: Regularly review SSH logs to detect and respond to suspicious activity.
Implementing these practices can significantly enhance the security of your SSH remote access setup.
SSH Security Risks
Despite its security features, SSH is not immune to potential risks. Some common vulnerabilities include:
- Brute Force Attacks: Attackers attempt to guess passwords through automated trials.
- Man-in-the-Middle Attacks: Attackers intercept and alter communication between the client and server.
- Configuration Errors: Improperly configured SSH settings can leave devices vulnerable to attacks.
Being aware of these risks and taking proactive measures can help mitigate potential threats.
Essential Tools and Software for SSH
Several tools and software solutions can enhance the SSH remote access experience for IoT devices:
- SSH Key Management Tools: Solutions like HashiCorp Vault and AWS Secrets Manager simplify the management of SSH keys.
- SSH Tunnel Managers: Tools like SSHuttle and Corkscrew facilitate secure tunneling of traffic between devices.
- IoT-Specific SSH Solutions: Platforms like Balena and Resin.io offer specialized SSH capabilities for IoT devices.
These tools can streamline the SSH setup and management process, ensuring a more efficient and secure experience.
Common Challenges and Solutions
Implementing SSH for IoT remote access can present several challenges. Below are some common issues and their solutions:
- Connection Issues: Ensure that firewall settings allow SSH traffic and that the correct port is open.
- Authentication Problems: Verify that SSH keys are correctly configured and that users have the necessary permissions.
- Performance Bottlenecks: Optimize SSH settings and use compression to improve performance on slower networks.
Addressing these challenges will help ensure a smooth and reliable SSH remote access experience.
Advanced Troubleshooting Tips
For more complex issues, consider the following troubleshooting tips:
- Check Logs: Review SSH server logs for detailed information about connection attempts and errors.
- Test Connectivity: Use tools like ping and traceroute to verify network connectivity between devices.
- Update Software: Ensure that all SSH-related software is up to date to benefit from the latest security patches.
Real-World Applications of SSH in IoT
SSH is utilized in a variety of real-world IoT applications, including:
- Smart Home Systems: SSH enables remote access to smart home devices for configuration and troubleshooting.
- Industrial Automation: SSH secures communication between industrial IoT devices in manufacturing environments.
- Healthcare Devices: SSH ensures the secure transmission of sensitive patient data in medical IoT applications.
These applications demonstrate the versatility and importance of SSH in the IoT landscape.
Case Studies
Several organizations have successfully implemented SSH for IoT remote access. For example:
- Company A: A leading manufacturer of smart home devices uses SSH to manage and monitor their products remotely, reducing customer support costs by 30%.
- Company B: A healthcare provider employs SSH to secure communication between IoT devices in their hospitals, ensuring compliance with HIPAA regulations.
Future Trends in SSH for IoT
As the IoT ecosystem continues to evolve, several trends are emerging in the realm of SSH remote access:
- Quantum-Resistant Encryption: Researchers are exploring new encryption methods that can withstand attacks from quantum computers.
- AI-Driven Security: Artificial intelligence is being used to enhance SSH security by detecting and responding to threats in real time.
- Edge Computing Integration: SSH is being integrated with edge computing technologies to improve performance and reduce latency in IoT applications.
These trends highlight the ongoing innovation in SSH technology and its potential to shape the future of IoT security.
Conclusion
In summary, SSH remote access provides a secure and efficient method for managing IoT devices from anywhere in the world. By understanding the key features, benefits, and best practices of SSH, organizations can ensure the security and reliability of their IoT infrastructure. We encourage you to implement SSH in your IoT setup and explore the tools and solutions available to enhance your experience.
Feel free to leave a comment or share this article with others who may find it useful. For more information on IoT security and related topics, explore our other articles on the site.