Secure remote management of IoT devices using SSH has become indispensable in the modern technological landscape. As the Internet of Things continues to expand, understanding how to establish and maintain remote SSH connections is vital for developers, engineers, and tech enthusiasts. This comprehensive guide delves into the realm of remote SSH for IoT, covering foundational principles, advanced techniques, and practical applications.
In today’s hyper-connected world, IoT devices are increasingly prevalent, ranging from smart home systems to sophisticated industrial automation platforms. However, effectively managing these devices remotely can be challenging without the right tools and expertise. Remote SSH provides a secure and reliable means of accessing IoT devices over the internet, ensuring data integrity, privacy, and seamless operation.
This article aims to explore remote SSH for IoT devices in detail, focusing on practical applications, security considerations, and industry best practices. Whether you’re just starting out or are an experienced professional, this guide equips you with the knowledge to harness the full potential of remote SSH for IoT devices.
Read also:Diesel Dave Net Worth
Table of Contents
- Understanding Remote SSH for IoT
- Benefits of Remote SSH for IoT
- Setting Up a Remote SSH Connection
- Enhancing Security for Remote SSH
- Advanced Techniques for Remote SSH IoT
- Troubleshooting Common Remote SSH Issues
- Real-World Applications of Remote SSH IoT
- Tools and Software for Remote SSH IoT
- Best Practices for Remote SSH IoT
- Future Trends in Remote SSH IoT
Understanding Remote SSH for IoT
Remote SSH for IoT involves securely connecting to IoT devices over the internet using the SSH (Secure Shell) protocol. SSH is a robust framework that ensures encrypted communication and secure authentication, making it a preferred choice for remote device management across various industries.
SSH, as a network protocol, facilitates secure communication between devices, enabling users to execute commands, transfer files, and monitor device performance without compromising sensitive data. With the rapid growth of IoT, the demand for secure remote access solutions has surged. Understanding the fundamentals of remote SSH for IoT is essential for anyone working with connected devices, whether personally or professionally.
Benefits of Remote SSH for IoT
There are numerous advantages to using remote SSH for IoT:
- Enhanced Security: SSH encrypts all data transmitted between devices, safeguarding against unauthorized access and eavesdropping.
- Reliability: SSH connections are stable and resilient to network disruptions, ensuring consistent performance even in challenging conditions.
- Flexibility: SSH supports a wide array of commands and operations, making it adaptable to various IoT applications and scenarios.
- Scalability: SSH can manage multiple devices and connections simultaneously, accommodating large-scale IoT deployments with ease.
By leveraging SSH for remote IoT management, organizations can improve operational efficiency while maintaining stringent security standards.
Setting Up a Remote SSH Connection
Step 1: Install SSH Client and Server
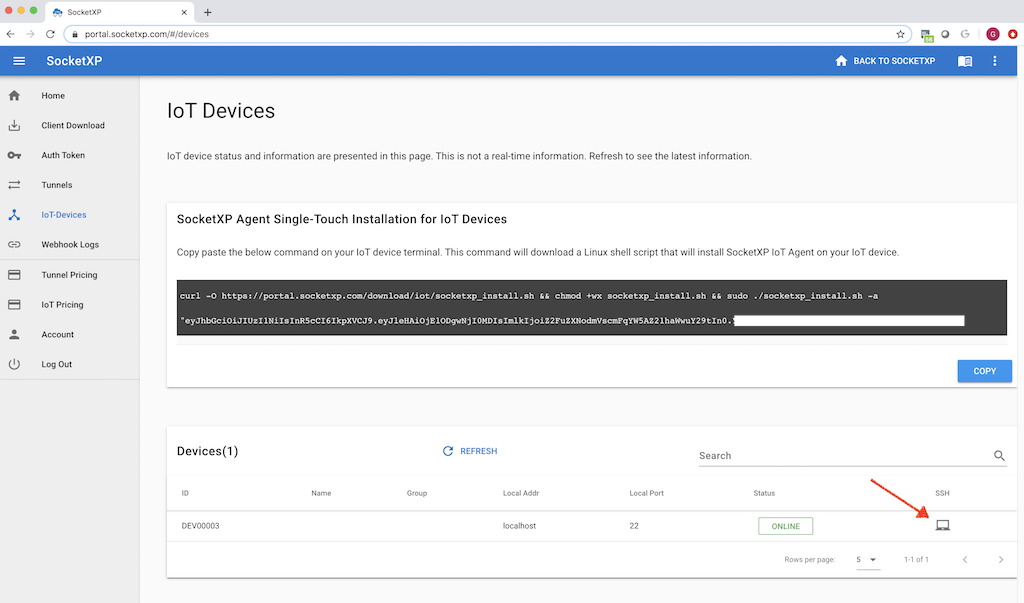
To establish a remote SSH connection, you need to install an SSH client on your local machine and an SSH server on the IoT device. Popular SSH clients include PuTTY (for Windows) and OpenSSH (for Linux and macOS). Ensure that both the client and server are properly configured to facilitate seamless communication.
Step 2: Configure Firewall Settings
It is crucial to configure your firewall to allow incoming SSH connections on port 22 (or a custom port if specified). This step ensures that remote access to your IoT device is enabled without compromising network security.
Read also:Song Hye Kyo And Lee Min Ho Drama Name The Ultimate Exploration Of Their Iconic Collaboration
Step 3: Generate SSH Keys
Using SSH keys instead of passwords enhances security and simplifies the authentication process. Generate a public-private key pair and add the public key to the authorized_keys file on the IoT device to enable key-based authentication.
Enhancing Security for Remote SSH
While SSH is inherently secure, additional measures can further protect your IoT devices:
- Use Strong Passwords: If passwords are used instead of keys, ensure they are complex, unique, and regularly updated.
- Enable Two-Factor Authentication (2FA): Add an extra layer of security by requiring a second form of verification during the login process.
- Disable Root Login: Restrict direct access to the root account to minimize the risk of unauthorized administrative access and potential system vulnerabilities.
- Regularly Update Software: Keep your SSH client and server software up to date to address potential vulnerabilities and maintain optimal performance.
Implementing these security practices will help safeguard your IoT devices from cyber threats and ensure long-term protection.
Advanced Techniques for Remote SSH IoT
Port Forwarding
Port forwarding allows you to access services running on your IoT device from a remote location. This technique is particularly useful for managing web servers, databases, and other applications, enabling efficient remote administration.
Tunneling
SSH tunneling creates a secure channel for transmitting data between devices, protecting sensitive information during transmission. This method is ideal for securing communication in environments where data privacy is paramount.
Automated Scripts
Developing automated scripts can streamline repetitive tasks, such as monitoring device status or updating firmware. These scripts can be executed remotely via SSH, saving time, reducing manual effort, and improving overall efficiency.
Troubleshooting Common Remote SSH Issues
Despite its reliability, SSH connections may encounter issues. Below are some common problems and their solutions:
- Connection Refused: Verify that the SSH server is running and the firewall allows incoming connections on the correct port. Double-check the IP address and port number for accuracy.
- Authentication Failed: Carefully review your SSH keys, passwords, and user permissions to ensure proper authentication. Check for typos or configuration errors.
- Timeout Errors: Ensure stable internet connectivity and optimize network settings for better performance. Adjust idle timeout settings to prevent disconnections during prolonged sessions.
Addressing these issues promptly will help maintain uninterrupted access to your IoT devices and ensure seamless remote management.
Real-World Applications of Remote SSH IoT
Remote SSH for IoT has numerous practical applications across various industries:
- Smart Agriculture: Farmers utilize IoT sensors and SSH connections to monitor soil moisture levels, automate irrigation systems, and optimize crop yield through data-driven insights.
- Industrial Automation: Manufacturers rely on SSH for remote control, maintenance, and troubleshooting of production equipment, ensuring efficient operations and minimizing downtime.
- Home Automation: Consumers leverage SSH to manage smart home devices, such as lighting, HVAC systems, and security cameras, enhancing convenience, energy efficiency, and safety.
These examples illustrate the versatility and value of remote SSH for IoT in addressing real-world challenges and driving innovation.
Tools and Software for Remote SSH IoT
Several tools and software can enhance your remote SSH IoT experience:
- OpenSSH: A widely-used open-source SSH implementation offering robust features, flexibility, and compatibility across multiple platforms.
- Bitvise SSH Client: A powerful SSH client for Windows, providing advanced security options, ease of use, and seamless integration with enterprise environments.
- Ansible: An automation platform that simplifies SSH-based tasks, such as configuration management, deployment, and orchestration, enabling efficient remote device management.
Exploring these tools can help you optimize your remote SSH IoT setup and achieve greater efficiency in managing connected devices.
Best Practices for Remote SSH IoT
To maximize the effectiveness of remote SSH for IoT, consider the following best practices:
- Document Configuration Settings: Maintain detailed records of your SSH setup, including server configurations, key pairs, and user permissions, for future reference and troubleshooting.
- Monitor Activity Logs: Regularly review logs to detect and respond to suspicious activities, ensuring timely identification and mitigation of potential security threats.
- Perform Regular Backups: Ensure that critical data, configurations, and system settings are backed up regularly to prevent data loss in the event of hardware failure or other unforeseen circumstances.
Adhering to these practices will contribute to a more secure, efficient, and reliable remote SSH IoT environment, fostering trust and confidence in your operations.
Future Trends in Remote SSH IoT
The future of remote SSH for IoT is promising, with emerging technologies shaping its evolution:
- Quantum Computing: Advances in quantum computing may lead to the development of new encryption methods, enhancing SSH security and addressing potential vulnerabilities in existing protocols.
- Edge Computing: Integrating edge computing with SSH can significantly reduce latency and improve processing capabilities for IoT devices, enabling real-time data analysis and decision-making.
- Artificial Intelligence: AI-driven automation can optimize SSH operations, reducing manual intervention, increasing efficiency, and enabling predictive maintenance for IoT devices.
Staying informed about these trends will empower you to adapt and thrive in the rapidly evolving landscape of remote SSH IoT, ensuring continued success and innovation.
Kesimpulan
In conclusion, remote SSH for IoT devices offers a secure, efficient, and scalable solution for managing connected devices remotely. By understanding the principles, techniques, and best practices outlined in this guide, you can unlock the full potential of SSH for IoT applications and drive meaningful innovation in your field.
We encourage you to share your thoughts, experiences, and insights in the comments section below. Additionally, feel free to explore other articles on our website for more in-depth knowledge about technology and IoT. Together, let’s embrace the future of remote connectivity and innovation!
References:
- OpenSSH Documentation: https://www.openssh.com/
- NIST Cybersecurity Framework: https://www.nist.gov/cyberframework
- IEEE IoT Journal: https://ieeexplore.ieee.org/xpl/RecentIssue.jsp?punumber=6488907