In today's rapidly advancing IoT (Internet of Things) landscape, establishing secure connections between remote devices and centralized servers is a crucial challenge for both businesses and developers. As the number of connected devices grows, ensuring robust data security and network architecture becomes paramount. This article explores the detailed process of securely connecting a remote IoT Virtual Private Cloud (VPC) using a Raspberry Pi and an AWS (Amazon Web Services) server. By the conclusion of this guide, you will possess a thorough understanding of the necessary steps and tools to implement this solution effectively.
In the era of IoT, industries have been transformed by enabling seamless communication between devices. However, with such connectivity comes the responsibility of maintaining security. AWS and Raspberry Pi provide an economical and scalable solution for constructing secure IoT systems. From configuring a VPC to setting up firewalls and encryption protocols, this article offers comprehensive, step-by-step instructions to help you fortify your IoT infrastructure.
Regardless of whether you're an experienced developer or new to IoT, this guide is crafted to equip you with the knowledge and tools required to establish a secure connection between your IoT devices and an AWS server. Let's explore the details and discover how to leverage Raspberry Pi and AWS to create a secure, scalable, and efficient IoT network.
Read also:Granblue Fantasy Relink Cross Platform
Table of Contents
- Understanding IoT and VPC
- Exploring Raspberry Pi
- Setting Up AWS Server
- Configuring VPC
- Methods for Secure Connections
- Encryption Techniques
- Firewall and Security Groups
- Monitoring and Logging
- Best Practices for Security
- Troubleshooting Common Issues
Understanding IoT and VPC
The Internet of Things (IoT) refers to the network of physical objects that communicate and exchange data via the internet. A Virtual Private Cloud (VPC) is an isolated segment within the AWS cloud where you can deploy AWS resources in a virtual network defined by you. By integrating IoT with VPC, you create a secure and scalable environment for managing IoT devices.
VPC offers several advantages, including:
- Enhanced security through private IP addresses and controlled access.
- Customizable network topology tailored to your specific needs.
- Seamless integration with other AWS services for streamlined operations.
Securing your IoT VPC requires configuring network settings, implementing encryption protocols, and monitoring traffic to ensure data integrity and privacy.
Why Choose AWS for IoT?
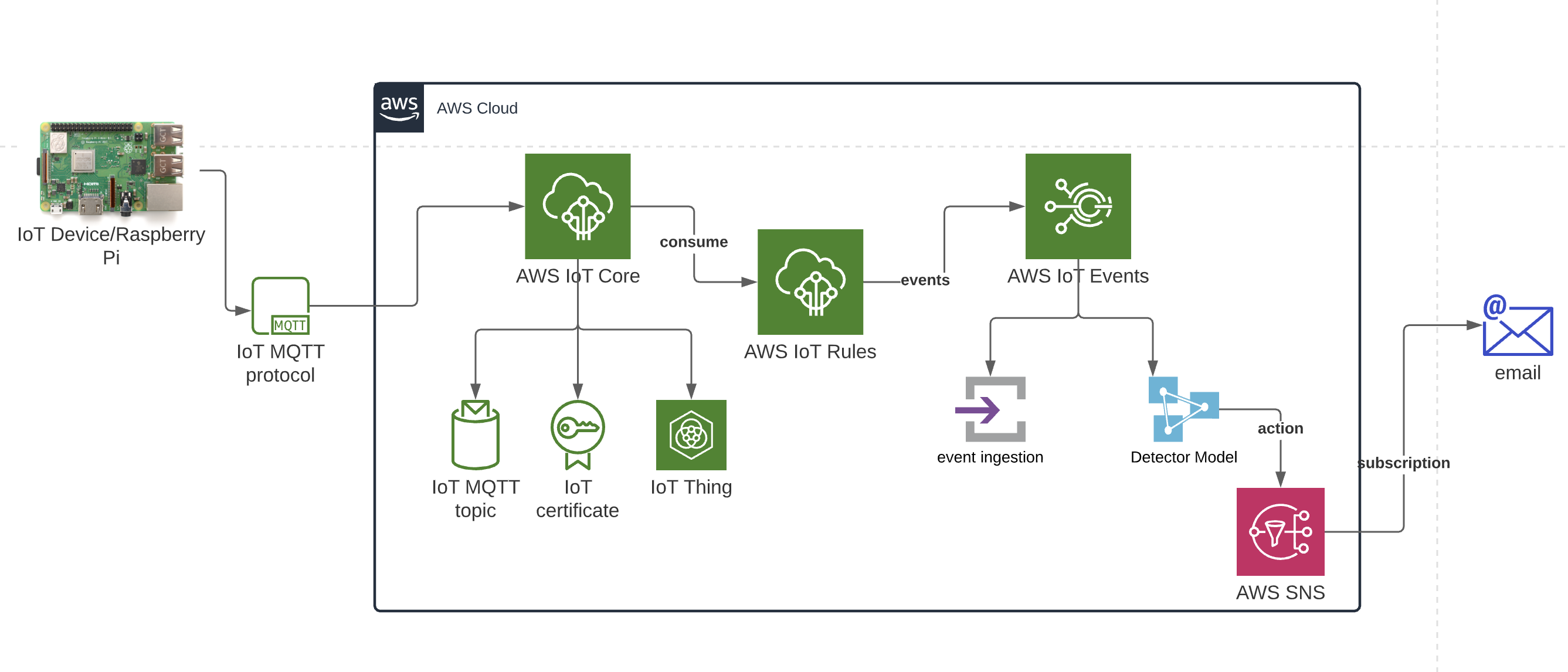
AWS provides a comprehensive suite of services designed specifically for IoT applications. These include AWS IoT Core, AWS Lambda, and AWS CloudWatch, which collectively form a robust platform for managing and securing IoT devices.
Exploring Raspberry Pi
The Raspberry Pi is a compact computer that has become immensely popular among developers and hobbyists. Its versatility allows it to run various operating systems and applications, making it an excellent choice for IoT projects.
Key features of the Raspberry Pi include:
Read also:Brian Musso Net Worth
- Affordable and energy-efficient design.
- Support for multiple programming languages and development environments.
- Compatibility with a broad range of sensors and actuators.
When combined with AWS, the Raspberry Pi becomes a powerful tool for building secure IoT solutions.
Setting Up Raspberry Pi for IoT
Before connecting your Raspberry Pi to an AWS server, proper configuration is essential. This involves installing an operating system, setting up network settings, and configuring security protocols to ensure a secure and efficient connection.
Setting Up AWS Server
Configuring an AWS server for IoT involves several steps, including launching an EC2 instance, configuring security groups, and installing necessary software. AWS provides extensive documentation and tools to simplify this process.
Steps to set up an AWS server:
- Create an AWS account if you haven't already.
- Launch an EC2 instance with the appropriate AMI (Amazon Machine Image).
- Configure security groups to control inbound and outbound traffic.
- Install and configure necessary software, such as MQTT brokers or database servers.
Choosing the Right EC2 Instance
Selecting the appropriate EC2 instance type is vital for ensuring optimal performance and cost-efficiency. Consider factors such as CPU power, memory, and storage requirements when making your choice.
Configuring VPC
Setting up a VPC entails defining subnets, route tables, and network access control lists (ACLs). Proper VPC configuration ensures that your IoT devices can communicate securely with the AWS server.
Key considerations for VPC configuration:
- Create subnets for different types of devices or applications.
- Set up route tables to manage traffic flow within the VPC.
- Implement network ACLs to add an additional layer of security.
Subnet Configuration
Subnets allow you to divide your VPC into smaller networks, each with its own IP address range. This enhances security and simplifies network management, making it easier to organize and secure your IoT devices.
Methods for Secure Connections
Securing the connection between your IoT devices and the AWS server requires implementing various protocols and technologies. Common methods include:
- TLS (Transport Layer Security) for encrypting data in transit.
- SSH (Secure Shell) for secure remote access.
- MQTT (Message Queuing Telemetry Transport) for lightweight communication.
Implementing TLS
TLS is a widely adopted protocol for securing data transmission over the internet. By implementing TLS, you can ensure that data exchanged between your IoT devices and the AWS server remains encrypted and protected from unauthorized access.
Encryption Techniques
Encryption is fundamental to securing IoT systems. It involves converting plaintext data into ciphertext to prevent unauthorized access. Common encryption techniques include AES (Advanced Encryption Standard) and RSA (Rivest-Shamir-Adleman).
Key points to consider when implementing encryption:
- Select the most suitable encryption algorithm based on your security requirements.
- Securely store encryption keys using AWS Key Management Service (KMS).
- Regularly update encryption keys to reduce the risk of compromise.
Key Management
Effective key management is essential for maintaining the security of your IoT system. AWS KMS provides a secure and scalable solution for managing encryption keys, ensuring their protection and accessibility.
Firewall and Security Groups
Firewalls and security groups are essential components of a secure IoT infrastructure. They control access to your AWS resources and help prevent unauthorized access.
Best practices for configuring firewalls and security groups:
- Define rules to permit only necessary traffic.
- Regularly review and update rules to reflect changes in your network environment.
- Monitor traffic logs to detect and respond to potential threats promptly.
Monitoring Security Groups
Regularly monitoring security groups ensures that your IoT system remains secure. AWS CloudWatch provides tools for monitoring and analyzing security group activity, helping you identify and address potential vulnerabilities.
Monitoring and Logging
Monitoring and logging are indispensable for maintaining the security and performance of your IoT system. AWS CloudWatch and AWS CloudTrail offer comprehensive tools for monitoring and logging AWS resources.
Key benefits of monitoring and logging:
- Identify and respond to potential security threats in real-time.
- Gain insights into system performance and usage patterns.
- Comply with regulatory requirements by maintaining detailed logs.
Using AWS CloudWatch
AWS CloudWatch is a powerful tool for monitoring and logging AWS resources. It provides detailed metrics and logs that can help you identify and address issues before they impact your system, ensuring continuous operation and security.
Best Practices for Security
Implementing best practices for security is critical for protecting your IoT system from potential threats. Some key best practices include:
- Regularly update software and firmware to patch vulnerabilities.
- Utilize strong authentication mechanisms, such as multi-factor authentication (MFA).
- Restrict access to sensitive data and resources to authorized personnel only.
Regular Security Audits
Conducting regular security audits ensures that your IoT system remains secure. This involves reviewing security configurations, testing for vulnerabilities, and implementing necessary updates and improvements to maintain a robust security posture.
Troubleshooting Common Issues
Even with the strongest security measures, issues can arise. Common problems include connectivity issues, configuration errors, and security breaches. Effective troubleshooting requires a systematic approach and access to relevant tools and resources.
Tips for troubleshooting:
- Verify network settings and ensure proper configuration.
- Review logs for error messages and other signs of issues.
- Refer to AWS documentation and support resources for guidance.
Using AWS Support
AWS offers a variety of support options, including online documentation, forums, and paid support plans. Leveraging these resources can help you resolve issues quickly and efficiently, ensuring minimal downtime and maximum security.
Conclusion
Securing a remote IoT VPC using a Raspberry Pi and AWS server involves several critical steps, from setting up the infrastructure to implementing encryption protocols and monitoring security. By following the guidelines outlined in this article, you can build a secure, scalable, and efficient IoT system.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and cloud computing. Together, let's create a safer and more connected world!