In today's rapidly advancing technological landscape, establishing secure connections for remote IoT devices using AWS and Raspberry Pi has become a fundamental necessity for both businesses and developers. As the number of connected devices continues to grow, ensuring secure communication is no longer optional—it's essential. This article delves into the critical steps and best practices for securely connecting remote IoT devices within an AWS Virtual Private Cloud (VPC) using Raspberry Pi as the hardware foundation.
The Internet of Things (IoT) is revolutionizing industries by enabling smart devices to communicate and share data efficiently. However, with this increased connectivity comes the challenge of maintaining strong security protocols. Establishing secure remote connections for IoT devices, especially through cloud services like AWS, demands a strategic approach to protect sensitive information and ensure reliable performance.
This comprehensive guide will walk you through the process of setting up a secure connection between your IoT devices and AWS VPC using Raspberry Pi. Whether you're a developer, an IT professional, or a hobbyist, this article provides actionable insights and practical tips to help you implement a secure IoT infrastructure effectively.
Read also:Yang Yang Wife
Table of Contents
- Introduction
- Overview of IoT and Its Challenges
- Understanding AWS VPC
- Role of Raspberry Pi in IoT
- Steps to Securely Connect IoT Devices
- Importance of Encryption
- Network Security Best Practices
- Monitoring and Managing IoT Devices
- Troubleshooting Common Issues
- Future Trends in IoT Security
- Conclusion
Introduction
The Internet of Things (IoT) has transformed the way we interact with technology, enabling a wide range of devices to communicate and share data seamlessly. However, as the number of connected devices increases, ensuring their security becomes a top priority. Securely connecting remote IoT devices within an AWS Virtual Private Cloud (VPC) using Raspberry Pi offers a scalable and cost-effective solution. This setup empowers businesses to monitor and manage IoT devices from a centralized location while maintaining robust security protocols.
This article aims to provide a detailed and practical guide to setting up a secure IoT infrastructure. By the end of this guide, you will have a thorough understanding of the tools, techniques, and best practices necessary to establish a secure connection between your IoT devices and AWS VPC, ensuring the reliability and security of your IoT ecosystem.
Overview of IoT and Its Challenges
What is IoT?
The Internet of Things (IoT) refers to a network of physical devices equipped with sensors, software, and connectivity features that allow them to exchange data. These devices range from smart home appliances to industrial machinery, all designed to enhance efficiency, automation, and convenience. The integration of IoT into various industries has revolutionized operations, offering unprecedented levels of connectivity and data-driven insights.
Key Challenges in IoT Security
While IoT brings numerous benefits, it also introduces significant security challenges. Some of the primary concerns include:
- Data Privacy: Safeguarding sensitive information transmitted between devices is a critical challenge in IoT ecosystems.
- Device Authentication: Ensuring that only authorized devices can access the network is essential to prevent unauthorized access and potential breaches.
- Network Vulnerabilities: Mitigating risks associated with unauthorized access to the network is crucial for maintaining the integrity of IoT systems.
To address these challenges effectively, a multi-layered security approach is necessary. This includes implementing encryption, authentication protocols, and robust network security measures to protect IoT devices and data.
Understanding AWS VPC
What is AWS VPC?
AWS Virtual Private Cloud (VPC) is a logically isolated section of the AWS Cloud where you can launch AWS resources within a virtual network that you define. This allows you to have complete control over your network environment, including IP address ranges, subnets, security groups, and routing tables. AWS VPC provides a secure and customizable environment for deploying and managing IoT devices.
Read also:Understanding The Concept Of Masa 49 And Its Cultural Significance
Benefits of Using AWS VPC for IoT
Using AWS VPC for IoT offers several advantages that contribute to a secure and efficient infrastructure:
- Enhanced Security: Isolate your IoT devices from the public internet to minimize exposure to external threats.
- Scalability: Easily scale your IoT infrastructure to accommodate growing demands without compromising performance or security.
- Customization: Tailor your network settings to meet specific requirements, ensuring optimal performance and security for your IoT ecosystem.
By leveraging AWS VPC, you can create a secure, reliable, and scalable environment for your IoT devices, enabling seamless integration and management.
Role of Raspberry Pi in IoT
What is Raspberry Pi?
Raspberry Pi is a small, affordable computer designed for a wide range of applications, including IoT projects. Its compact size, low power consumption, and versatility make it an ideal platform for deploying IoT devices. Raspberry Pi serves as a powerful and cost-effective solution for connecting and managing IoT devices, enabling developers and hobbyists to build innovative solutions.
Why Use Raspberry Pi for IoT?
Raspberry Pi offers several compelling advantages for IoT projects:
- Cost-Effective: Its affordable pricing makes it accessible for both individual enthusiasts and businesses, reducing the barriers to entry for IoT development.
- Flexible: Raspberry Pi supports a wide range of sensors, peripherals, and connectivity options, making it adaptable to various IoT applications.
- Community Support: A large and active community provides extensive resources, tutorials, and support, empowering users to overcome challenges and enhance their projects.
With Raspberry Pi, you can build powerful IoT solutions that seamlessly integrate with cloud services like AWS, enabling advanced functionality and scalability.
Steps to Securely Connect IoT Devices
Setting Up AWS VPC
To establish a secure connection for IoT devices, the first step is to set up an AWS VPC. This involves creating a virtual network with subnets, route tables, and security groups. Follow these steps to configure your AWS VPC:
- Create a new VPC in the AWS Management Console, defining the IP address range and other network parameters.
- Define subnets for public and private access to ensure proper segmentation of your IoT devices.
- Set up security groups to control inbound and outbound traffic, ensuring only authorized communication is allowed.
Configuring Raspberry Pi
After setting up your AWS VPC, the next step is to configure your Raspberry Pi to connect to the AWS environment. This includes:
- Installing necessary software and libraries to enable communication with AWS services.
- Configuring network settings to ensure proper connectivity to the VPC.
- Implementing authentication protocols, such as certificate-based authentication, to secure communication between devices.
By following these steps, you can establish a secure and reliable connection between your IoT devices and AWS VPC, ensuring the integrity and performance of your IoT infrastructure.
Importance of Encryption
Why Encryption Matters
Encryption plays a vital role in IoT security by ensuring that data transmitted between devices remains confidential and protected from unauthorized access. Implementing encryption protocols, such as TLS (Transport Layer Security), can significantly enhance the security of your IoT infrastructure, safeguarding sensitive information and maintaining data integrity.
Implementing Encryption in IoT
To implement encryption effectively in your IoT setup, consider the following strategies:
- Use strong encryption algorithms for data transmission to protect against interception and unauthorized access.
- Implement certificate-based authentication for devices to verify their identity and ensure secure communication.
- Regularly update encryption keys and certificates to prevent vulnerabilities and maintain the highest level of security.
Prioritizing encryption is essential for protecting sensitive data and maintaining the trustworthiness of your IoT network.
Network Security Best Practices
Securing Your IoT Network
Network security is a critical component of protecting IoT devices from unauthorized access and cyber threats. To enhance the security of your IoT network, consider the following best practices:
- Use Firewalls: Deploy firewalls to control and monitor network traffic, blocking unauthorized access and potential threats.
- Implement Intrusion Detection Systems (IDS): Utilize intrusion detection systems to monitor for suspicious activity and alert administrators of potential security breaches.
- Regularly Update Firmware and Software: Keep firmware and software up to date to address vulnerabilities and ensure the latest security features are in place.
Managing Access Control
Access control is another crucial aspect of network security. By implementing role-based access control (RBAC), you can ensure that only authorized personnel have access to sensitive systems and data. This helps minimize the risk of unauthorized access and maintains the integrity of your IoT infrastructure.
Monitoring and Managing IoT Devices
Importance of Monitoring
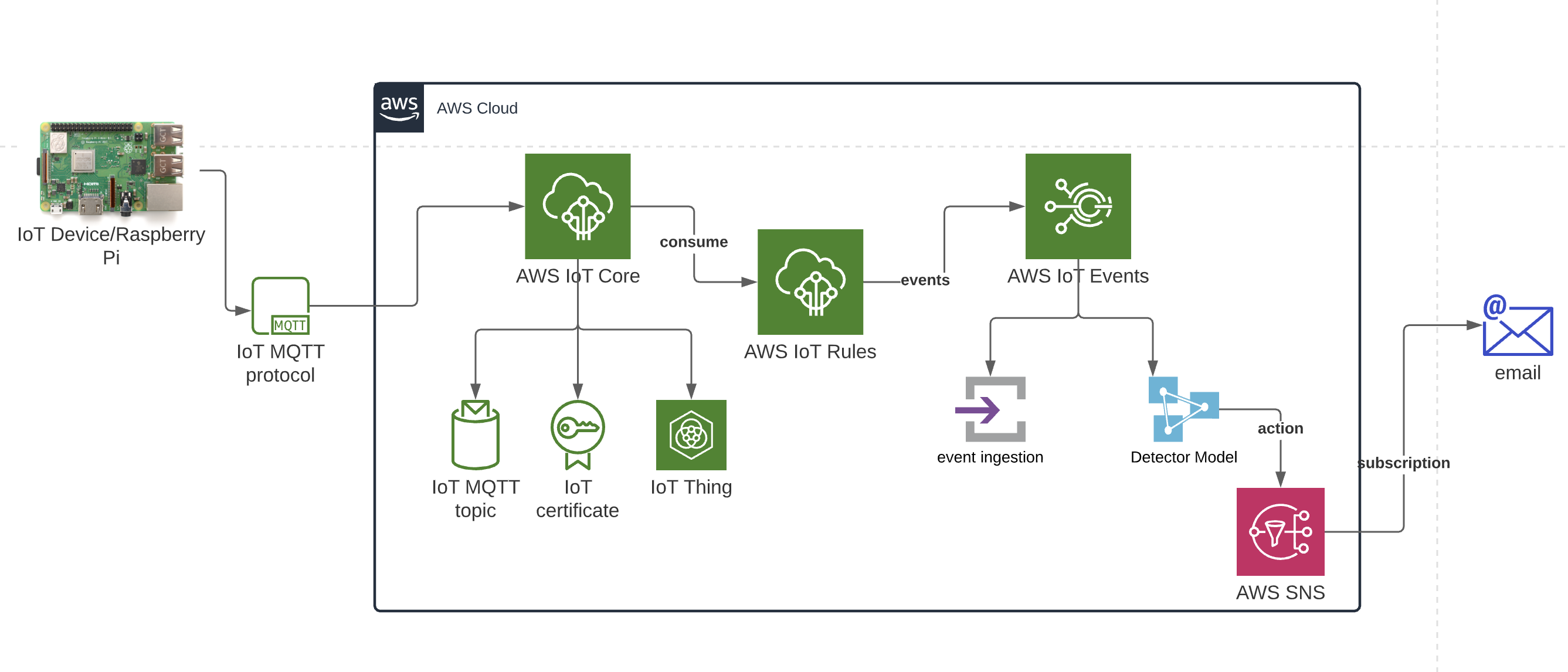
Monitoring your IoT devices is essential for maintaining their performance and security. Tools like AWS IoT Core provide powerful monitoring capabilities, allowing you to track device activity, receive alerts for anomalies, and respond promptly to potential issues. Regular monitoring ensures that your IoT devices operate efficiently and securely.
Managing IoT Devices
Effectively managing your IoT devices involves several key strategies:
- Centralized Management Platforms: Use centralized platforms for device monitoring, updates, and configuration management to streamline operations and improve efficiency.
- Automated Processes: Implement automated processes for firmware updates and maintenance tasks to reduce manual intervention and minimize downtime.
- Regular Log Reviews: Regularly review logs and analytics to identify potential issues, optimize performance, and enhance security.
By actively monitoring and managing your IoT devices, you can ensure their optimal performance and security, addressing potential issues before they escalate.
Troubleshooting Common Issues
Common IoT Challenges
Even with careful planning and implementation, IoT setups can encounter various challenges. Some common issues include:
- Network Connectivity Problems: Ensuring stable and reliable network connections is critical for IoT devices to function effectively.
- Device Authentication Failures: Authentication issues can disrupt communication and compromise security, requiring prompt resolution.
- Data Transmission Errors: Errors during data transmission can lead to incomplete or inaccurate information, affecting the overall performance of IoT systems.
Resolving IoT Issues
To address these challenges effectively, follow these troubleshooting steps:
- Verify network settings and ensure proper configuration to resolve connectivity issues.
- Check device certificates and authentication credentials to resolve authentication failures.
- Review logs for detailed error messages and take corrective action to resolve data transmission errors.
By addressing these issues promptly and systematically, you can minimize downtime and maintain the reliability of your IoT infrastructure.
Future Trends in IoT Security
Emerging Technologies
The future of IoT security is shaped by emerging technologies that promise to enhance security and efficiency. Some of these technologies include:
- Blockchain: Blockchain technology can provide secure and transparent data transactions, enhancing trust and reliability in IoT ecosystems.
- Artificial Intelligence: AI-powered systems can detect and respond to potential threats proactively, offering predictive threat detection and mitigation capabilities.
- Quantum Computing: Quantum computing advancements could revolutionize encryption techniques, offering advanced security measures to protect sensitive data.
Adapting to New Challenges
As IoT continues to evolve, staying ahead of emerging security challenges will require a proactive and adaptive approach. By embracing new technologies and continuously refining security practices, you can ensure the long-term success and security of your IoT projects.
Conclusion
Establishing secure connections for remote IoT devices within an AWS VPC using Raspberry Pi is a critical step in building a robust and scalable IoT infrastructure. By following the steps and best practices outlined in