As the Internet of Things (IoT) continues to expand, ensuring secure connections between remote devices has become a top priority for both individuals and businesses. Whether you're a tech enthusiast or a professional developer, understanding how to establish a secure peer-to-peer (P2P) connection between IoT devices, such as a Raspberry Pi, is essential. This guide delves into the process of setting up secure connections, exploring free software options, and ensuring seamless compatibility with Windows systems—all without any cost.
In today's highly interconnected world, IoT devices have revolutionized the way we live and work, enhancing productivity and convenience in countless ways. However, this increased connectivity also brings significant risks, including unauthorized access and data breaches. Securing your IoT network isn't just an option—it's a necessity. This article will walk you through the steps to securely connect remote IoT devices using P2P technology, focusing on Raspberry Pi and Windows systems.
Whether you're building a home automation system, setting up remote monitoring solutions, or experimenting with IoT projects, this guide will provide you with the knowledge and tools needed to ensure your setup is secure, efficient, and cost-effective. Let's explore how to achieve this seamlessly and without additional expenses.
Read also:Kai Ryssdal Wife
Table of Contents
- Introduction to IoT
- Raspberry Pi Overview
- Basics of Secure Connections
- Understanding P2P Technology
- Setting Up Remote IoT Connections
- Ensuring Windows Compatibility
- Free Software Options for Download
- Security Best Practices
- Troubleshooting Tips
- Conclusion
Introduction to IoT
The Internet of Things (IoT) represents a network of interconnected devices capable of exchanging data and performing tasks autonomously. These devices range from smart home appliances and wearable tech to industrial sensors, all designed to improve efficiency and convenience. A critical aspect of maintaining the integrity and functionality of such systems is ensuring secure connections between remote IoT devices.
IoT devices often rely on wireless communication protocols, making them vulnerable to various cyber threats. As a result, ensuring secure communication between devices, particularly in remote setups, is essential to protect sensitive data and prevent unauthorized access.
Why Security is Vital in IoT
- IoT devices often handle sensitive information, including personal data and operational metrics.
- Unsecured connections can lead to data breaches, system compromises, and even financial losses.
- Implementing robust security measures is crucial for safeguarding both individual users and businesses.
Raspberry Pi Overview
Raspberry Pi is a highly versatile single-board computer widely used in IoT projects due to its affordability, flexibility, and open-source nature. It serves as an excellent platform for developers and hobbyists alike, enabling them to create innovative solutions. By leveraging Raspberry Pi's capabilities, users can establish secure peer-to-peer connections between remote IoT devices.
Raspberry Pi supports a variety of operating systems, programming languages, and communication protocols, making it adaptable to diverse applications. Its compatibility with Windows systems ensures seamless integration into existing infrastructures, further enhancing its appeal.
Key Features of Raspberry Pi
- Compact size with low power consumption, making it ideal for portable and low-energy projects.
- Support for multiple interfaces, including Wi-Fi, Bluetooth, and Ethernet, enabling versatile connectivity options.
- Compatibility with a wide range of sensors and peripherals, allowing users to expand functionality as needed.
Basics of Secure Connections
Establishing a secure connection involves implementing encryption, authentication, and authorization mechanisms. These elements ensure that only authorized devices can access the network and that data transmitted between devices remains confidential and protected from unauthorized interception.
When setting up secure connections for remote IoT devices, such as Raspberry Pi, using protocols like SSH (Secure Shell) and SSL/TLS (Secure Sockets Layer/Transport Layer Security) is highly recommended. These protocols provide robust encryption and authentication capabilities, significantly reducing the risk of unauthorized access.
Read also:Park Bo Gum And Kim Yoo Jung Relationship
Popular Encryption Protocols
- SSH: Ideal for secure remote access and command execution, ensuring that communication between devices is encrypted and secure.
- SSL/TLS: Ensures secure data transmission over the internet, protecting sensitive information from eavesdropping and tampering.
Understanding P2P Technology
Peer-to-peer (P2P) technology allows devices to communicate directly without relying on centralized servers. This decentralized approach offers numerous advantages, such as reduced latency and improved efficiency, making it particularly well-suited for IoT applications. By leveraging P2P technology, users can enable seamless data exchange between remote IoT devices, even in challenging network environments.
Implementing P2P connections requires careful planning, including considerations for network topology, security measures, and software compatibility. By adopting P2P technology, users can create resilient, scalable, and secure IoT systems capable of meeting the demands of modern applications.
Advantages of P2P Technology
- Reduced dependency on centralized servers, minimizing single points of failure and improving reliability.
- Improved data transfer speeds and reliability, ensuring faster and more efficient communication between devices.
- Enhanced security through direct device communication, reducing the risk of unauthorized access and data breaches.
Setting Up Remote IoT Connections
Setting up a remote IoT connection involves several key steps, including configuring the Raspberry Pi, establishing a secure network, and ensuring compatibility with Windows systems. Below is a detailed step-by-step guide to help you achieve this:
Step 1: Configure Raspberry Pi
- Install the latest version of Raspberry Pi OS on your device, ensuring it is fully updated and optimized for your project.
- Enable SSH for secure remote access, allowing you to manage the device remotely with encrypted communication.
- Configure network settings to connect to your Wi-Fi or Ethernet network, ensuring stable and reliable connectivity.
Step 2: Establish Secure Network
- Implement encryption protocols such as SSH and SSL/TLS to secure data transmission between devices.
- Set up firewalls and intrusion detection systems to enhance overall network security and protect against potential threats.
Step 3: Ensure Windows Compatibility
- Download and install necessary drivers and software on your Windows system to facilitate seamless communication with your IoT devices.
- Test the connection thoroughly to ensure all devices are properly configured and functioning as expected.
Ensuring Windows Compatibility
Ensuring compatibility with Windows systems is essential for users who wish to integrate their IoT projects into existing infrastructures. Fortunately, several free software options are available to facilitate this process, enabling secure and efficient communication between devices.
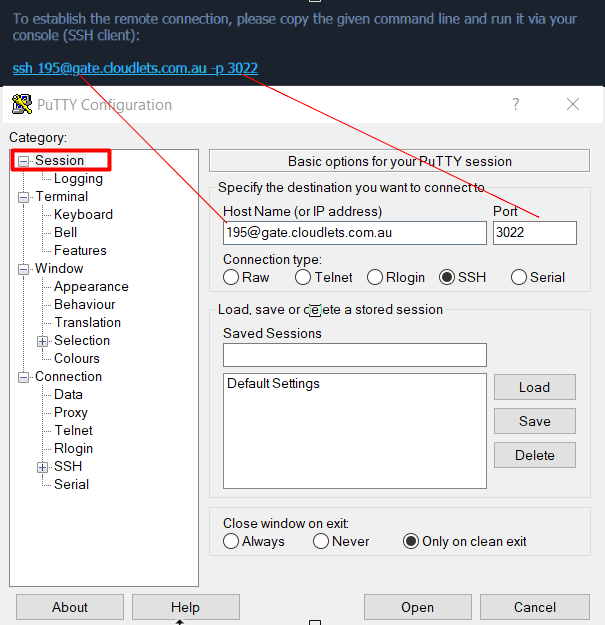
Popular tools such as PuTTY (for SSH) and FileZilla (for file transfer) can be downloaded and used without incurring any costs. These tools provide essential functionalities for managing remote IoT devices from a Windows machine, simplifying the setup process and enhancing usability.
Recommended Tools
- PuTTY: A free SSH client that enables secure remote access to your IoT devices.
- FileZilla: A free FTP client that allows you to transfer files between devices with ease and security.
Free Software Options for Download
Several free software options are available for securely connecting IoT devices, providing essential functionalities for establishing secure connections, managing devices, and ensuring compatibility with Windows systems. These tools are invaluable for anyone looking to create a robust and secure IoT setup.
Some of the most popular options include:
- Raspberry Pi Imager: A tool for installing Raspberry Pi OS on your device, ensuring a smooth and hassle-free setup process.
- OpenSSH: A powerful tool for secure remote access and command execution, protecting your devices from unauthorized access.
- WireGuard: A modern and efficient VPN solution that provides secure and reliable connections between devices.
Where to Download
- Raspberry Pi Imager: Raspberry Pi Official Website
- OpenSSH: OpenSSH Official Website
- WireGuard: WireGuard Official Website
Security Best Practices
Implementing security best practices is essential for maintaining the integrity and security of your IoT network. Below are some key recommendations to help you protect your devices and data:
- Regularly update firmware and software to patch vulnerabilities and ensure your devices are protected against the latest threats.
- Use strong, unique passwords and enable two-factor authentication wherever possible to enhance security and reduce the risk of unauthorized access.
- Monitor network activity closely and implement intrusion detection systems to identify and respond to potential threats promptly.
By following these best practices, you can significantly reduce the risk of cyberattacks and ensure the security and reliability of your IoT setup.
Troubleshooting Tips
Even with careful planning and execution, issues may arise during the setup process. Below are some common troubleshooting tips to help you resolve connectivity problems and ensure smooth operation of your IoT system:
- Ensure all devices are properly configured and connected to the network, verifying settings such as IP addresses and network credentials.
- Check firewall settings to ensure they do not block necessary ports, preventing communication between devices.
- Refer to official documentation and community forums for additional support and guidance, leveraging the collective knowledge of the IoT community.
By addressing these issues promptly and systematically, you can resolve connectivity problems and ensure your IoT system operates seamlessly and efficiently.
Conclusion
In conclusion, establishing secure connections for remote IoT devices, such as Raspberry Pi, and ensuring compatibility with Windows systems is an achievable goal with the right tools and knowledge. By following the steps outlined in this guide, you can create a secure, efficient, and cost-effective IoT setup that integrates seamlessly with your existing infrastructure.
We encourage you to share your experiences and insights in the comments section below, helping others learn from your successes and challenges. Additionally, feel free to explore other articles on our website for more information on IoT, Raspberry Pi, and related topics. Together, let's build a safer, more connected, and more innovative world!