In today's highly interconnected world, Secure Shell (SSH) access has emerged as an indispensable tool for managing and securing IoT devices remotely. As the Internet of Things continues to expand at an unprecedented rate, understanding how to effectively utilize SSH is essential for maintaining secure communication channels. This article will explore the intricacies of SSH access for IoT devices, equipping you with the knowledge and tools necessary to enhance your network's security and efficiency.
SSH, or Secure Shell, plays a pivotal role in enabling secure remote access within the IoT ecosystem. With billions of devices now connected globally, ensuring secure communication is no longer optional—it’s a necessity. Whether you're a developer, a network administrator, or simply a tech enthusiast, mastering SSH access can empower you to manage IoT devices more effectively while safeguarding sensitive data.
This guide aims to provide a detailed exploration of SSH access in the context of IoT devices. By examining its technical aspects, best practices, and potential challenges, you'll gain the expertise needed to implement secure solutions. Let's delve into the specifics and uncover how SSH can transform your approach to IoT management.
Read also:Park Bo Gum And Kim Yoo Jung Relationship
Table of Contents
- Understanding SSH Access
- The Expanding IoT Landscape
- Key Benefits of SSH for IoT Devices
- Critical Security Considerations for SSH in IoT
- Configuring SSH Access for IoT Devices
- Best Practices for Secure SSH Access
- Resolving Common SSH Connection Issues
- Common Attacks Targeting SSH and IoT
- Emerging Trends in SSH and IoT Security
- Conclusion and Next Steps
Understanding SSH Access
Secure Shell (SSH) is a cryptographic protocol designed to establish secure communication channels between devices over potentially unsecured networks. For IoT devices, SSH access provides a dependable method for remote management, secure data transfer, and reliable command execution. This section will introduce the fundamental principles of SSH and its significance in the context of IoT ecosystems.
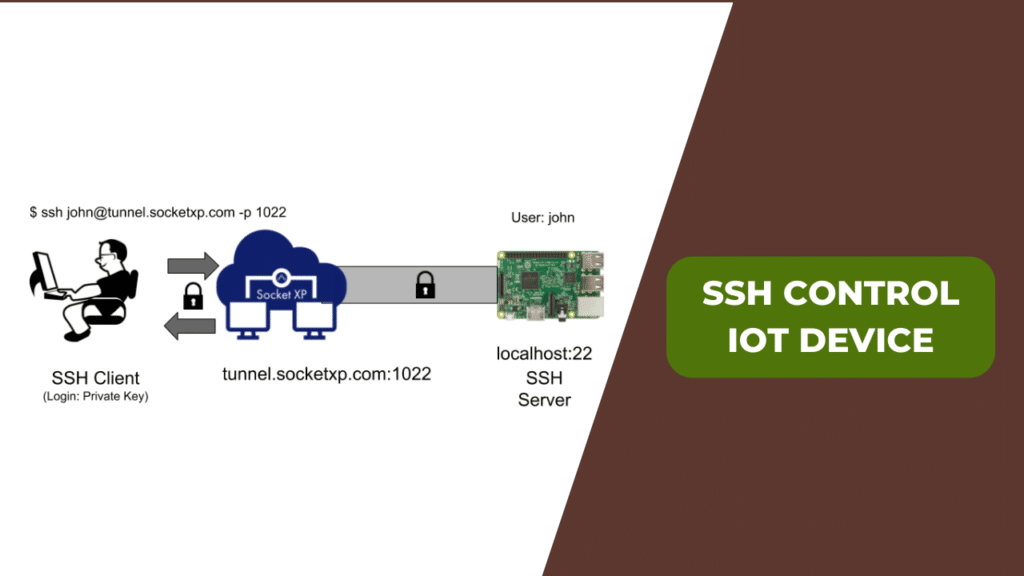
How SSH Works
SSH operates by establishing an encrypted connection between a client device and a server. This ensures that all data transmitted between devices remains confidential and protected from unauthorized access or tampering. Within the IoT framework, SSH allows administrators to securely connect to remote devices, execute commands, and transfer files without compromising system integrity.
Key Features of SSH
- Encryption: Protects sensitive information from unauthorized interception.
- Authentication: Ensures that only authorized users can access the system, enhancing overall security.
- Integrity: Verifies that data has not been altered during transmission, maintaining its accuracy and reliability.
The Expanding IoT Landscape
The Internet of Things (IoT) has revolutionized industries by fostering seamless connectivity among devices. From smart homes and wearable technology to industrial automation and healthcare systems, IoT devices are reshaping how we interact with technology on a daily basis. However, this rapid expansion introduces unique challenges, particularly concerning security and efficient management.
Growth Statistics
According to recent reports by Statista, the global number of IoT devices is projected to surpass 25.44 billion by 2030. This exponential growth underscores the critical need for robust security measures, such as SSH access, to safeguard these devices against potential threats and vulnerabilities.
Key Benefits of SSH for IoT Devices
Integrating SSH access into your IoT infrastructure offers a multitude of advantages. Below are some of the most significant benefits:
Enhanced Security
SSH provides end-to-end encryption, ensuring that sensitive data transmitted between IoT devices remains secure. This feature is especially vital for applications involving personal or financial information, where data protection is paramount.
Read also:Wes Bentley
Efficient Remote Management
With SSH, administrators can manage IoT devices remotely, eliminating the need for physical access. This capability not only enhances operational efficiency but also reduces downtime, enabling swift troubleshooting and updates.
Secure File Transfer
SSH supports secure file transfer through protocols like SFTP (Secure File Transfer Protocol). This functionality is invaluable for tasks such as firmware updates, log file transfers, and data synchronization across IoT networks, ensuring that all data exchanges remain secure and reliable.
Critical Security Considerations for SSH in IoT
While SSH offers robust security features, improper implementation can expose IoT devices to vulnerabilities. Below are some essential security considerations to keep in mind:
Strong Authentication Mechanisms
Utilizing strong passwords or public key authentication is crucial to preventing unauthorized access. Avoid using default credentials and regularly update authentication methods to enhance security. Additionally, consider implementing multi-factor authentication for an added layer of protection.
Regular Updates and Maintenance
Ensuring that SSH software and firmware are consistently updated is vital for addressing known vulnerabilities. Manufacturers and developers should prioritize security patches to protect IoT devices from emerging threats and maintain system integrity.
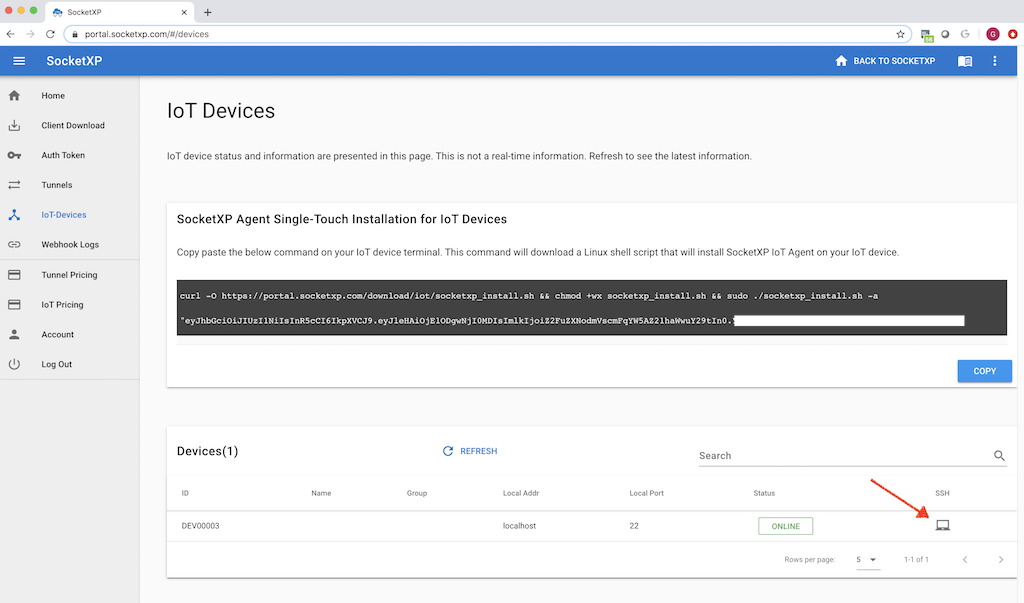
Configuring SSH Access for IoT Devices
Setting up SSH access for IoT devices involves several steps. This section will guide you through the process, ensuring a secure and efficient configuration:
Step-by-Step Guide
- Install an SSH Server: Begin by installing an SSH server on your IoT device. Popular options include OpenSSH and Dropbear, both of which offer reliable and secure solutions.
- Configure Firewall Settings: Adjust your firewall settings to allow SSH traffic on the designated port (default is 22). Ensure that these settings are configured securely to prevent unauthorized access.
- Set Up Authentication: Implement public key authentication for enhanced security. This method eliminates the need for password-based access, reducing the risk of brute force attacks.
- Test the Connection: Verify that SSH access is functioning correctly by connecting to the device from a remote client. This step ensures that all configurations are properly implemented and operational.
Best Practices for Secure SSH Access
Adopting best practices is essential for maintaining secure SSH access in IoT environments. Below are some recommendations to help you optimize security:
Restrict Access to Trusted Sources
Limit SSH access to trusted IP addresses or specific networks to minimize the risk of unauthorized access. This approach significantly enhances security by reducing the potential attack surface.
Monitor SSH Activity
Implement logging and monitoring tools to track SSH activity and detect any suspicious behavior. Regularly reviewing logs can help identify potential security breaches and allow for timely responses.
Use Non-Standard Ports
Consider using non-standard ports for SSH to deter automated attacks and reduce the likelihood of brute force attempts. While this measure alone does not guarantee complete security, it adds an additional layer of protection.
Resolving Common SSH Connection Issues
Even with proper configuration, SSH connections can encounter issues. Below are some common problems and their solutions:
Connection Refused
If you receive a "connection refused" error, verify that the SSH server is running and that the firewall allows traffic on the specified port. Double-check your configuration settings to ensure that all components are correctly aligned.
Authentication Failure
Ensure that your credentials are accurate and that public key authentication is properly configured. Additionally, review file permissions and ownership settings to confirm that they align with SSH requirements.
Common Attacks Targeting SSH and IoT
SSH access in IoT environments is vulnerable to various types of attacks. Understanding these threats is crucial for implementing effective countermeasures:
Brute Force Attacks
Attackers may attempt to guess passwords through brute force methods. Enforcing strong password policies, enabling two-factor authentication, and utilizing rate-limiting techniques can significantly mitigate this risk.
Man-in-the-Middle Attacks
These attacks involve intercepting and altering communication between devices. Using SSH ensures that all data remains encrypted, reducing the likelihood of successful interception and maintaining the integrity of the communication channel.
Emerging Trends in SSH and IoT Security
As technology continues to evolve, new trends in SSH and IoT security are emerging. Below are some anticipated developments:
Quantum Computing and Cryptography
Quantum computing presents both challenges and opportunities for cryptographic systems. Researchers are actively exploring post-quantum algorithms to ensure the long-term security of SSH and IoT systems, safeguarding against potential future threats.
AI-Driven Security Solutions
Artificial intelligence is being increasingly integrated into security systems to detect and respond to threats in real time. This advancement promises to enhance the protection of SSH-enabled IoT devices, providing more proactive and dynamic security measures.
Conclusion and Next Steps
SSH access for IoT devices is a powerful tool for secure remote management and communication. By understanding its benefits, implementing best practices, and addressing potential challenges, you can effectively safeguard your IoT ecosystem. We encourage you to share your insights, ask questions, or explore related topics in our other articles. Together, we can foster a safer and more connected technological landscape.
Thank you for reading! If you found this article helpful, please consider subscribing to our newsletter or leaving a comment below. Your feedback is invaluable in helping us improve and expand our content to better serve your needs.