In our increasingly connected world, the ability to remotely access IoT devices via SSH has become indispensable for businesses and individuals. Whether you're overseeing smart home systems, industrial machinery, or cloud-based infrastructures, Secure Shell (SSH) access delivers unmatched control and adaptability. As IoT devices continue to multiply, understanding how to securely connect to them from any location is essential for unlocking their full potential.
SSH offers a robust solution for the remote management and monitoring of IoT devices. This technology facilitates user interaction with IoT devices through encrypted connections, ensuring data integrity and safeguarding sensitive information. In this article, we will delve into the complexities of SSH IoT access, its advantages, and the best practices for implementation.
By the end of this guide, you will possess a thorough understanding of how SSH empowers secure global management of IoT devices. We will also address potential challenges and offer practical solutions to help you effectively integrate this technology into your projects.
Read also:Does Jonny Lee Miller Have Tattoos
Table of Contents
- What is SSH and Its Role in IoT?
- Benefits of Using SSH for IoT Device Access
- Security Considerations for SSH IoT Connections
- The Setup Process for SSH IoT Device Access
- Best Practices for Managing SSH IoT Connections
- Common Issues and Troubleshooting Tips
- Scaling SSH IoT Access for Enterprise Use
- Future Trends in SSH IoT Device Management
- SSH vs Other Remote Access Protocols
- Conclusion and Next Steps
What is SSH and Its Role in IoT?
Understanding the SSH Protocol
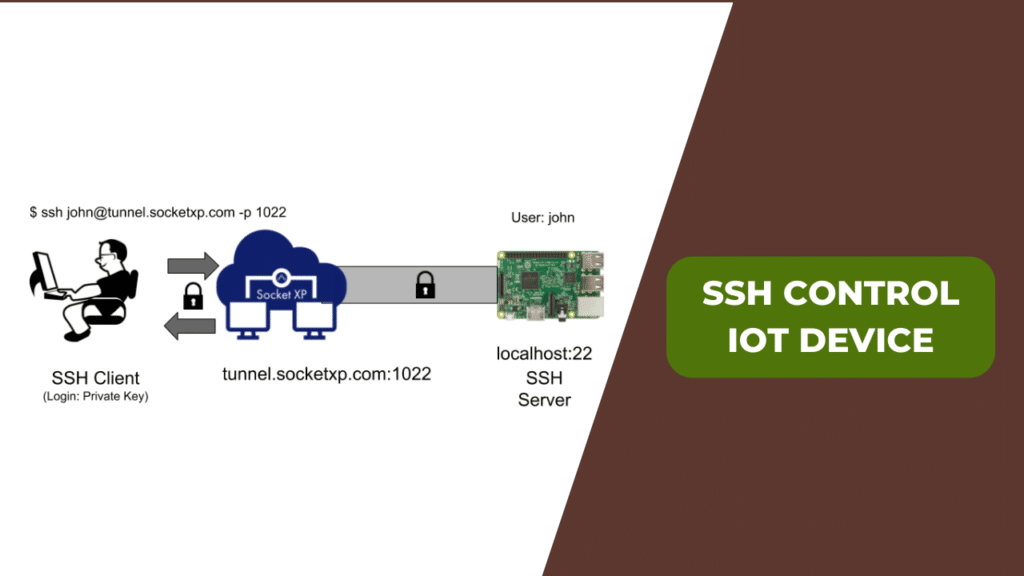
Secure Shell (SSH) is a cryptographic network protocol designed to facilitate secure data communication over unsecured networks. It establishes a secure channel for accessing remote devices, transferring files, and executing commands. SSH ensures data integrity, confidentiality, and authentication, making it a preferred choice for remotely managing IoT devices.
The Importance of SSH in IoT
In the IoT landscape, SSH plays a pivotal role in device management. It empowers administrators to access IoT devices from anywhere, conduct diagnostics, update firmware, and monitor system performance. With the exponential growth of connected devices, SSH provides a scalable and secure approach to remote management, addressing the complexities of modern IoT ecosystems.
Why Choose SSH for IoT Device Access?
Adopting SSH for IoT device access offers numerous advantages, including enhanced security, flexibility, and operational efficiency. Below are some of the key benefits:
- Encryption: SSH encrypts all data exchanged between the client and server, safeguarding it from eavesdropping and unauthorized access.
- Authentication: SSH supports advanced authentication mechanisms, such as public-key cryptography, which bolster security and deter unauthorized intrusions.
- Platform Independence: SSH operates seamlessly across various platforms and operating systems, ensuring versatility in diverse IoT environments.
- Command Execution: Users can remotely execute commands, enabling efficient device management without the need for physical access.
Addressing Security Concerns in SSH IoT Connections
Key Security Challenges
Despite its robust security features, SSH is not immune to vulnerabilities. Common security challenges include brute-force attacks, weak passwords, and misconfigured SSH servers. To mitigate these risks, it is crucial to implement best practices and regularly update security protocols.
Enhancing SSH IoT Connection Security
Here are some actionable steps to fortify the security of SSH IoT connections:
- Employ strong, unique passwords for each device to prevent unauthorized access.
- Enable public-key authentication to replace less secure password-based logins.
- Disable root login to minimize the risk of unauthorized access.
- Regularly update SSH software to patch any identified security vulnerabilities.
Setting Up SSH for IoT Device Access
Comprehensive Step-by-Step Guide
Configuring SSH for IoT device access involves several critical steps:
Read also:Granblue Fantasy Relink Crossplay
- Install an SSH server on the IoT device to enable remote access capabilities.
- Customize the SSH server settings, including port numbers and authentication methods, to align with your specific requirements.
- Test the connection using an SSH client from a remote location to ensure proper functionality.
- Secure the connection by implementing firewall rules and access restrictions to protect against unauthorized access.
Essential Tools and Software
A variety of tools and software solutions can simplify the SSH setup process. Popular options include OpenSSH for server deployment and PuTTY for client-side access. These tools are widely adopted and come with extensive documentation to support seamless implementation.
Optimizing SSH IoT Connections
Maintaining Robust Security
To ensure the sustained security of SSH IoT connections, adhere to the following best practices:
- Regularly audit SSH server configurations and access logs to identify and address potential security breaches.
- Restrict access to trusted IP addresses or networks to minimize the risk of unauthorized intrusions.
- Monitor for suspicious login attempts and respond promptly to mitigate potential threats.
Improving Performance and Reliability
Efficient management of SSH IoT connections demands attention to performance optimization. Techniques such as data compression and bandwidth throttling can enhance connection speed and reliability, particularly in low-bandwidth environments.
Resolving Common Issues in SSH IoT Connections
Diagnosing Connection Problems
Common issues with SSH IoT connections include timeouts, authentication failures, and configuration errors. To diagnose these problems, consider the following:
- Confirm that the SSH server is operational and accessible from the intended network.
- Verify that the correct port number is being used to establish the connection.
- Review authentication credentials and permissions to ensure they are correctly configured.
Solving Connection Challenges
Once the issue is identified, apply the appropriate solutions. For instance, restart the SSH server if it is unresponsive, update authentication keys if necessary, or adjust firewall settings to permit SSH traffic.
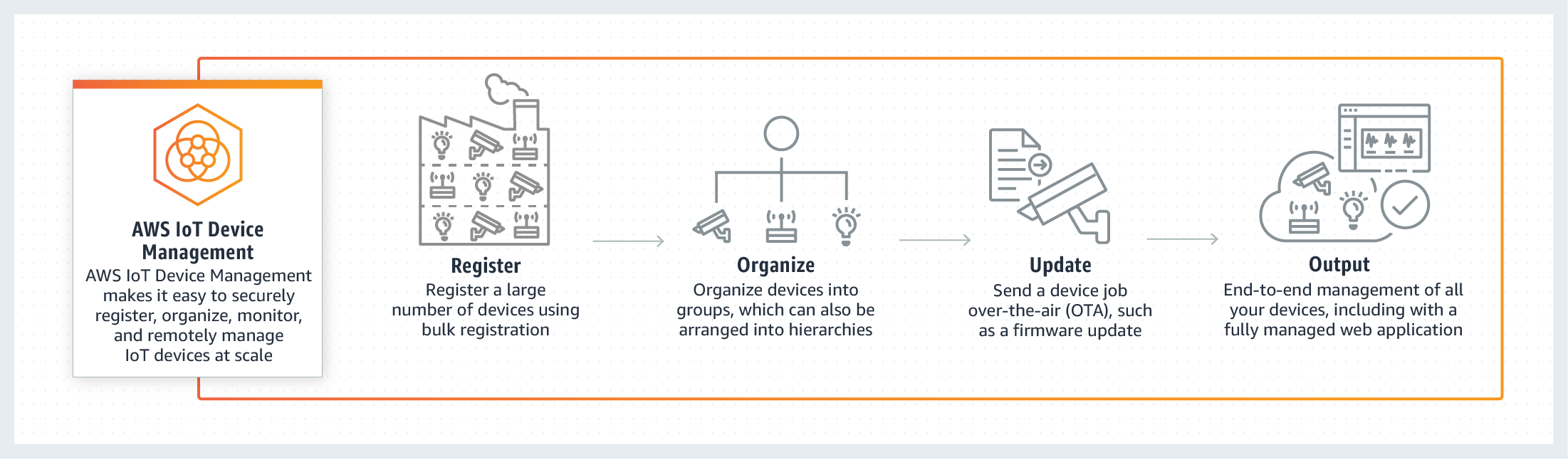
Scaling SSH IoT Access for Enterprise Deployments
Enterprise-Specific Requirements
For large-scale deployments, SSH IoT access must be both scalable and manageable. Enterprises require centralized management tools, advanced authentication systems, and comprehensive logging capabilities. Solutions like SSH key management platforms and network automation tools can help fulfill these needs.
Best Practices for Scaling SSH IoT Access
When scaling SSH IoT access, consider the following best practices:
- Implement role-based access control to efficiently manage user permissions and ensure security.
- Leverage automated deployment tools to simplify server configuration and streamline the setup process.
- Continuously monitor system performance and allocate resources as needed to maintain optimal functionality.
Exploring the Future of SSH IoT Device Management
Innovative Technologies Shaping the Future
The evolution of SSH IoT device management is driven by emerging technologies such as quantum computing, blockchain, and artificial intelligence. These advancements promise to enhance security, improve performance, and expand the range of functionalities available.
Adapting to Emerging Challenges
As IoT technology continues to advance, so must SSH protocols and practices. Staying informed about industry trends and adapting to new challenges will be vital for maintaining secure and effective SSH IoT connections.
Comparing SSH with Other Remote Access Protocols
An In-Depth Comparison
While SSH is a widely adopted choice for IoT device access, alternative protocols such as Telnet, FTP, and HTTPS also exist. However, SSH surpasses these options in terms of security and reliability. Below is a comparative analysis of key features:
| Protocol | Security | Performance | Usability |
|---|---|---|---|
| SSH | High | Good | Excellent |
| Telnet | Low | Good | Fair |
| FTP | Low | Good | Fair |
Conclusion and Next Steps
In summary, SSH IoT device access provides a secure, efficient, and scalable solution for managing connected devices globally. By comprehending its benefits, implementing best practices, and staying informed about emerging trends, you can harness the full potential of this technology in your projects.
We encourage readers to take proactive steps by exploring SSH implementation in their IoT ecosystems. Share your experiences or ask questions in the comments below. Additionally, consider subscribing to our newsletter for insightful content on IoT and related technologies. Together, let's unlock the true potential of secure IoT device management!
Data Source: SSH.com, NIST, ISO