In today's world of interconnected devices, ensuring robust security for IoT systems has become a top priority. As the Internet of Things (IoT) expands rapidly, securing communication between devices is essential to safeguard networks from cyber threats. Secure Shell (SSH) offers a powerful solution by providing encryption and authentication mechanisms to protect IoT ecosystems.
The proliferation of IoT devices has brought about immense opportunities for innovation and convenience. However, this growth also increases the risk of cyberattacks. Implementing SSH protocols for IoT devices plays a crucial role in mitigating these risks by encrypting data transmissions and ensuring secure access. This article delves into the importance of SSH in IoT environments and explores how it can enhance the security of your smart devices.
Regardless of whether you're a tech enthusiast, a business owner, or an IT professional, understanding SSH IoT device security is vital. In this detailed guide, we will examine the fundamentals of SSH, its applications in IoT, and the best practices for implementing secure protocols. Let's explore this essential topic!
Read also:Brian Musso Net Worth
Table of Contents
- Understanding SSH
- SSH in IoT Systems
- The Importance of SSH in IoT
- How SSH Operates
- Advantages of SSH for IoT Devices
- Common SSH IoT Device Attacks
- Securing SSH Connections
- Best Practices for SSH IoT Security
- Tools for Managing SSH IoT Security
- The Future of SSH in IoT
Understanding SSH
SSH, or Secure Shell, is a cryptographic network protocol designed to secure data communication, facilitate remote command execution, and enable file transfers over unsecured networks. First introduced in 1995 by Tatu Ylönen, SSH has become a cornerstone of modern cybersecurity. It operates on port 22 by default and establishes a secure channel between two devices, ensuring confidentiality, integrity, and authentication.
SSH is widely utilized across various industries, including IT, telecommunications, and finance, to safeguard sensitive information. Its advanced encryption algorithms and key exchange mechanisms make it an ideal choice for securing IoT devices. By leveraging SSH, organizations can effectively protect their networks from unauthorized access and potential data breaches.
Key Features of SSH
SSH offers several critical features that make it indispensable for securing IoT devices:
- Encryption: SSH encrypts all data transmissions, ensuring that sensitive information remains confidential during transfer.
- Authentication: SSH supports multiple authentication methods, including passwords, public keys, and certificates, to verify the identity of users and devices.
- Integrity: SSH ensures data integrity by detecting and preventing tampering during transmission, safeguarding the authenticity of the information exchanged.
SSH in IoT Systems
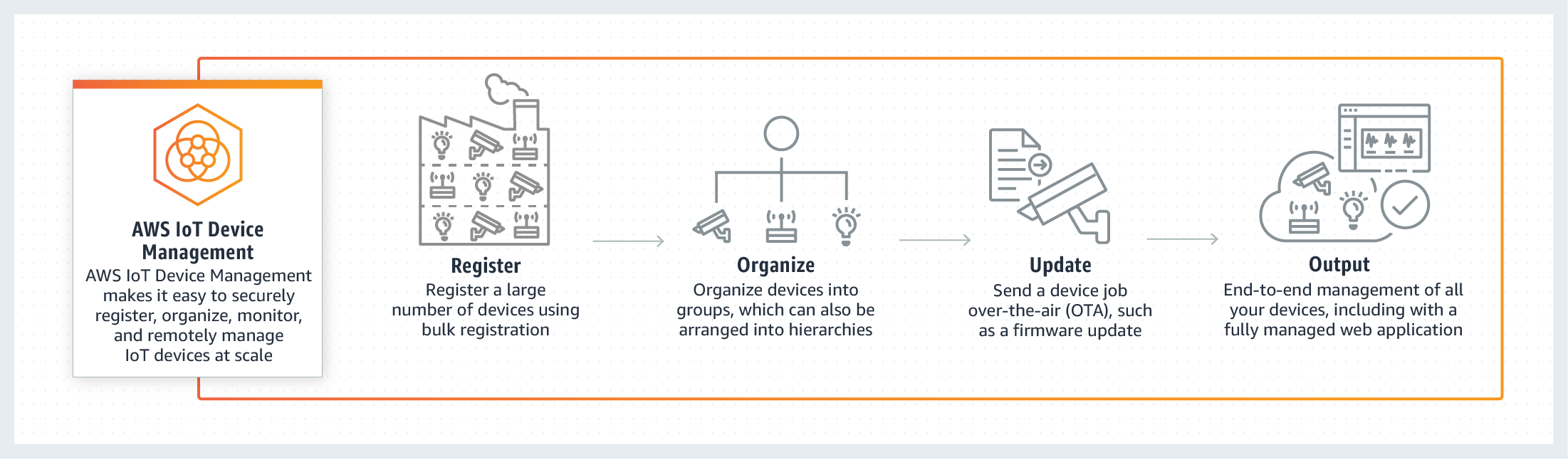
The integration of SSH into IoT ecosystems has transformed the way smart devices communicate and interact. As IoT devices become increasingly interconnected, the demand for secure communication protocols has grown exponentially. SSH implementations in IoT provide a reliable solution for protecting data transmissions and ensuring secure access to devices.
In an IoT environment, SSH can secure communication between various components, such as sensors, actuators, gateways, and cloud platforms. By encrypting data transmissions and authenticating devices, SSH helps prevent unauthorized access and potential cyberattacks, ensuring the integrity and privacy of the data exchanged.
Applications of SSH in IoT
SSH implementations in IoT have diverse applications across various industries:
Read also:Miranda Richardson
- Smart Homes: SSH secures communication between smart appliances, lighting systems, and security cameras, enhancing the overall safety and functionality of home automation systems.
- Industrial Automation: SSH protects data transmissions in manufacturing plants and industrial control systems, ensuring seamless and secure operations in critical environments.
- Healthcare: SSH ensures secure communication between medical devices and healthcare platforms, safeguarding sensitive patient data and enabling reliable remote monitoring.
The Importance of SSH in IoT
IoT devices are often deployed in unsecured environments, making them highly vulnerable to cyberattacks. SSH IoT device security addresses this vulnerability by providing a robust framework for protecting data transmissions and ensuring secure access to devices. By implementing SSH, organizations can significantly reduce the risk of unauthorized access and potential data breaches.
According to a report by Gartner, the number of IoT devices is projected to reach 25 billion by 2025. With this rapid growth, the need for secure communication protocols like SSH becomes increasingly critical. Organizations must prioritize SSH IoT device security to protect their networks and sensitive information from emerging cyber threats.
How SSH Operates
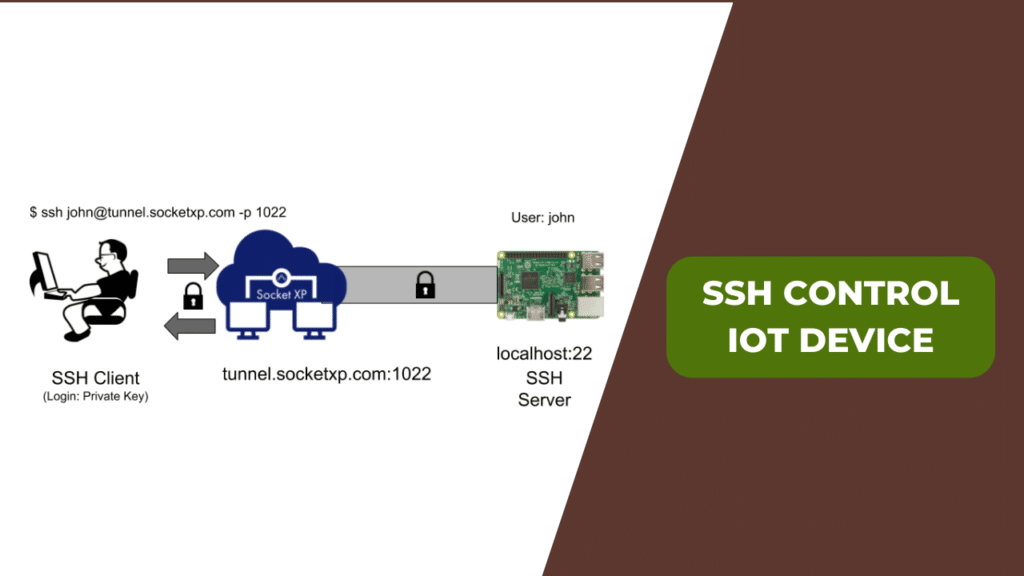
SSH operates on a client-server model, where a client initiates a connection with a server using a secure channel. The process involves several key steps, including key exchange, authentication, and encryption. During the key exchange phase, SSH employs algorithms like Diffie-Hellman to establish a shared secret between the client and server. This shared secret is then used to encrypt data transmissions and ensure secure communication.
Authentication in SSH can be performed using various methods, including passwords, public keys, and certificates. Public key authentication is widely regarded as the most secure method, as it eliminates the need for password-based authentication and reduces the risk of brute-force attacks, thereby enhancing the overall security of the system.
Advantages of SSH for IoT Devices
Implementing SSH IoT device security offers numerous benefits for both organizations and individuals:
- Enhanced Security: SSH encrypts data transmissions and ensures secure access to devices, significantly reducing the risk of unauthorized access and potential data breaches.
- Improved Performance: SSH compresses data transmissions, leading to faster communication and reduced bandwidth usage, which is particularly beneficial in resource-constrained IoT environments.
- Scalability: SSH can be easily scaled to accommodate growing IoT ecosystems, ensuring secure communication across multiple devices and networks, regardless of their size or complexity.
Common SSH IoT Device Attacks
Despite its robust security features, SSH IoT device implementations are not immune to cyberattacks. Common attack vectors include brute-force attacks, man-in-the-middle (MITM) attacks, and keylogging. To mitigate these risks, organizations must implement strong security measures and adhere to best practices.
According to a study by Symantec, over 70% of IoT devices are vulnerable to cyberattacks due to weak security protocols. By implementing SSH IoT device security, organizations can significantly reduce the risk of unauthorized access and potential data breaches, ensuring the safety and integrity of their networks.
Types of SSH IoT Device Attacks
Here are some common SSH IoT device attacks:
- Brute-Force Attacks: Attackers attempt to guess passwords or private keys by systematically trying all possible combinations, exploiting weak or predictable credentials.
- Man-in-the-Middle (MITM) Attacks: Attackers intercept and alter data transmissions between devices, compromising the integrity of the communication and potentially accessing sensitive information.
- Keylogging: Attackers capture keystrokes to obtain sensitive information, such as passwords or private keys, enabling unauthorized access to devices and networks.
Securing SSH Connections
To ensure the security of SSH IoT device implementations, organizations must take proactive measures to protect their networks and devices. This includes configuring SSH settings, implementing strong authentication methods, and regularly updating software and firmware to address potential vulnerabilities.
An effective way to secure SSH connections is by disabling password-based authentication and enabling public key authentication. This eliminates the risk of brute-force attacks and ensures that only authorized users can access devices, enhancing the overall security of the system.
Best Practices for Securing SSH Connections
Here are some best practices for securing SSH IoT device implementations:
- Use Strong Passwords: Ensure that all passwords are complex and unique to reduce the risk of brute-force attacks, even when public key authentication is enabled.
- Enable Public Key Authentication: Disable password-based authentication and use public key authentication for added security, reducing the likelihood of unauthorized access.
- Regularly Update Software: Keep all software and firmware up to date to address potential vulnerabilities and security flaws, ensuring the system remains resilient against emerging threats.
Best Practices for SSH IoT Security
In addition to securing SSH connections, organizations must adhere to best practices for implementing SSH IoT device security. This includes monitoring network activity, configuring firewalls, and educating employees on cybersecurity awareness.
Monitoring network activity is essential for detecting potential threats and addressing security incidents promptly. By implementing intrusion detection systems (IDS) and intrusion prevention systems (IPS), organizations can proactively identify and mitigate potential cyberattacks, enhancing the overall security of their IoT ecosystems.
Steps to Implement Best Practices
Here are some steps to implement best practices for SSH IoT device security:
- Monitor Network Activity: Use IDS and IPS to detect and respond to potential threats in real-time, ensuring the system remains secure and operational.
- Configure Firewalls: Set up firewalls to control incoming and outgoing traffic and protect devices from unauthorized access, reducing the attack surface for potential threats.
- Educate Employees: Train employees on cybersecurity awareness and best practices to reduce the risk of human error, which is often a significant factor in security breaches.
Tools for Managing SSH IoT Security
Several tools and platforms are available to help organizations manage SSH IoT device security effectively. These tools offer features like automated key management, centralized logging, and real-time monitoring, making it easier to secure IoT ecosystems.
Popular tools for managing SSH IoT device security include OpenSSH, PuTTY, and SSH.com. These tools provide a range of features and functionalities to address the unique needs of different organizations and industries, ensuring comprehensive protection for IoT devices and networks.
Top Tools for SSH IoT Device Management
Here are some top tools for managing SSH IoT device security:
- OpenSSH: A widely used open-source SSH implementation that provides robust security features and functionalities, making it a reliable choice for securing IoT ecosystems.
- PuTTY: A popular SSH client for Windows that offers a user-friendly interface and advanced configuration options, enabling users to manage SSH connections effectively.
- SSH.com: A comprehensive SSH solution that includes features like key management, centralized logging, and real-time monitoring, offering organizations a holistic approach to IoT security.
The Future of SSH in IoT
As the IoT landscape continues to evolve, the role of SSH in securing IoT ecosystems will become increasingly important. Advances in technology, such as quantum computing and artificial intelligence, will introduce new challenges and opportunities for securing IoT devices and networks.
Organizations must stay informed about emerging trends and technologies to ensure the continued security of their IoT ecosystems. By embracing innovation and adhering to best practices, organizations can protect their networks and sensitive information from potential cyber threats, maintaining trust and reliability in an increasingly connected world.
Conclusion
In conclusion, SSH IoT device security is a critical component of modern cybersecurity practices. By encrypting data transmissions and ensuring secure access to devices, SSH provides a robust framework for protecting IoT ecosystems from potential cyber threats. Organizations must prioritize SSH IoT device security to safeguard their networks and sensitive information, ensuring the reliability and safety of their operations.
We encourage readers to implement the best practices outlined in this article and explore the tools and platforms available for managing SSH IoT device security. By taking proactive measures and staying informed about emerging trends, organizations can protect their IoT ecosystems and ensure the continued security of their networks.
Feel free to leave a comment or share this article with others who may benefit from the information provided. For more insights into cybersecurity and IoT, explore our other articles and resources on the site.