As technology advances, the Internet of Things (IoT) has become a cornerstone of modern innovation. One of the most effective tools for securely managing IoT devices remotely is Secure Shell (SSH). This comprehensive SSH IoT remotely tutorial will guide you through the essential and advanced concepts of leveraging SSH to manage IoT devices effectively.
In today's digital landscape, remote management of IoT devices is not just a convenience—it's a necessity. Whether you're a developer, hobbyist, or an enterprise seeking to optimize operations, understanding how SSH integrates with IoT can significantly enhance your capabilities. This tutorial is designed to take you from foundational knowledge to advanced practices, equipping you with the skills to manage IoT devices securely and efficiently.
By the conclusion of this SSH IoT remotely tutorial, you'll be proficient in setting up and managing IoT devices using SSH, ensuring both data integrity and device security. Let's delve into the world of IoT management through SSH and unlock its full potential.
Read also:Scott Wapner Family
Table of Contents
- Exploring SSH and IoT
- Understanding SSH Fundamentals
- What is IoT and Why Choose SSH?
- Configuring SSH for IoT Devices
- Ensuring Secure SSH IoT Connections
- Automating IoT Tasks with SSH
- Resolving Common SSH IoT Challenges
- Essential Tools and Software for SSH IoT
- Best Practices for SSH IoT Management
- The Evolving Role of SSH in IoT
Exploring SSH and IoT
SSH (Secure Shell) is a cryptographic network protocol that facilitates secure communication over unsecured networks. It is widely utilized for remote administration and file transfer. IoT (Internet of Things) refers to the interconnected network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data seamlessly.
When combined, SSH and IoT form a powerful alliance for managing devices remotely. This SSH IoT remotely tutorial will delve into the complexities of this integration, empowering you to manage your devices securely and efficiently.
Understanding SSH Fundamentals
How SSH Operates
SSH functions on a client-server model, where a client connects to a server using encryption to secure the connection. The protocol ensures authentication and data integrity, making it indispensable for IoT device management.
Key characteristics of SSH include:
- Encryption of data during transmission to safeguard sensitive information.
- Authentication through public and private keys for enhanced security.
- Support for multiple authentication methods, including password and key-based authentication, offering flexibility and robustness.
What is IoT and Why Choose SSH?
The Significance of IoT
IoT has transformed industries by enabling smart devices to communicate and share data effortlessly. From smart homes to industrial automation, IoT applications are vast and varied, driving innovation across sectors.
Using SSH for IoT device management provides numerous benefits:
Read also:Is Park Bo Gum Married
- Heightened security through encrypted connections, protecting devices and data from unauthorized access.
- Reliable remote access and control, allowing seamless management of IoT devices regardless of location.
- Easy integration with existing infrastructure, ensuring compatibility and scalability.
Configuring SSH for IoT Devices
Prerequisites for Setup
Prior to configuring SSH for IoT, ensure you have the following:
- An IoT device with SSH support, ensuring compatibility with the protocol.
- A stable internet connection to maintain uninterrupted communication.
- A client device (computer, smartphone) with SSH client software installed, facilitating remote access.
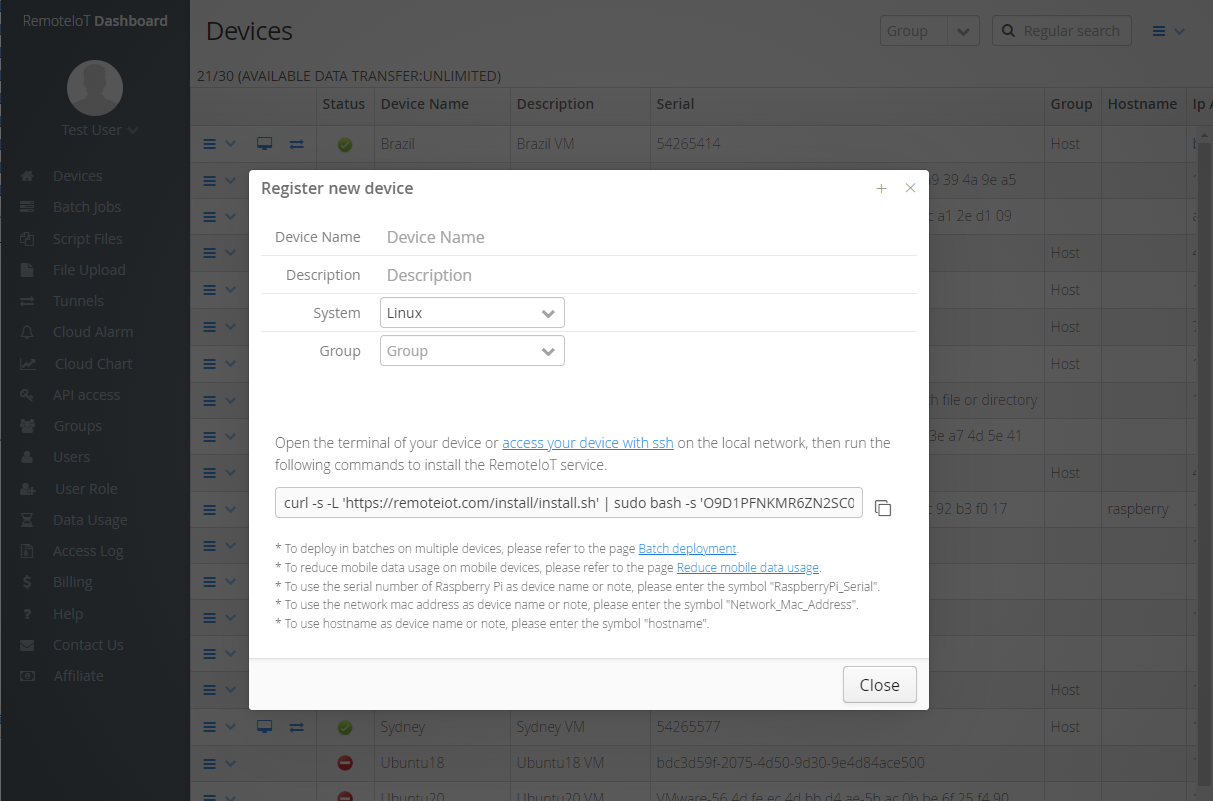
Once you meet the prerequisites, follow these steps to configure SSH:
- Install an SSH server on your IoT device, enabling it to accept remote connections.
- Configure the server settings, including port and authentication methods, to tailor the setup to your specific needs.
- Test the connection using an SSH client to ensure proper functionality and identify any issues.
Ensuring Secure SSH IoT Connections
Top Security Practices
Security is paramount when managing IoT devices remotely. Here are some strategies to fortify your SSH IoT connection:
- Utilize strong, unique passwords or key-based authentication to deter brute-force attacks and unauthorized access.
- Change the default SSH port to a non-standard port, reducing the risk of automated attacks targeting default settings.
- Enable firewall rules to restrict access, ensuring only authorized devices and users can connect.
- Regularly update your SSH server and client software to address vulnerabilities and enhance security.
Implementing these practices can significantly reduce the likelihood of unauthorized access to your IoT devices, safeguarding your network and data.
Automating IoT Tasks with SSH
Scripting for Streamlined Automation
SSH can be leveraged to automate repetitive tasks on IoT devices, enhancing efficiency and reducing manual intervention. By crafting scripts, you can perform tasks such as data collection, system monitoring, and device updates automatically.
Popular scripting languages for SSH automation include:
- Bash: A versatile scripting language well-suited for command-line tasks and automation.
- Python: A powerful and flexible language offering extensive libraries for IoT and automation tasks.
- Perl: A robust language known for its text-processing capabilities, ideal for complex automation scenarios.
These scripts can be scheduled to execute at specified intervals, ensuring your IoT devices remain updated and function optimally without requiring constant supervision.
Resolving Common SSH IoT Challenges
Identifying and Addressing Issues
Despite meticulous setup, challenges may arise when utilizing SSH for IoT. Here are some common problems and their solutions:
- Connection Refused: Verify that the SSH server is operational and the required port is open, ensuring the connection can be established.
- Authentication Failure: Double-check your credentials and confirm the correct keys are being utilized, resolving authentication-related issues.
- Timeout Errors: Ensure a stable internet connection and adjust timeout settings as needed to prevent premature disconnections.
Promptly addressing these issues ensures a dependable SSH IoT connection, minimizing disruptions and maintaining operational efficiency.
Essential Tools and Software for SSH IoT
Popular SSH Clients
A variety of tools and software are available to streamline SSH IoT management. Some of the most widely used options include:
- PuTTY: A free and open-source SSH client for Windows, offering a user-friendly interface and robust functionality.
- OpenSSH: A widely adopted SSH client and server for Unix-like operating systems, providing secure and reliable communication.
- Termius: A cross-platform SSH client with an intuitive interface, supporting seamless management across multiple devices.
Selecting the appropriate tool depends on your specific requirements and the operating system you are utilizing, ensuring optimal performance and ease of use.
Best Practices for SSH IoT Management
Optimizing Management Strategies
To efficiently manage IoT devices using SSH, consider the following best practices:
- Document your setup and configurations meticulously, providing a reliable reference for future modifications and troubleshooting.
- Monitor your devices regularly for any suspicious activity, promptly addressing potential security threats and ensuring ongoing integrity.
- Implement role-based access control to restrict unauthorized access, maintaining a secure and controlled environment.
- Backup your data routinely to prevent data loss in the event of unforeseen circumstances, ensuring business continuity and peace of mind.
By adhering to these practices, you can ensure the smooth and secure management of your IoT devices, optimizing their performance and reliability.
The Evolving Role of SSH in IoT
Emerging Trends and Innovations
As IoT continues to expand, the importance of SSH in managing these devices will only increase. Emerging trends such as quantum computing and AI-driven security will further elevate the capabilities of SSH in IoT, offering advanced protection and functionality.
Staying informed about the latest developments in SSH and IoT ensures you remain at the forefront of secure and efficient device management, adapting to evolving challenges and opportunities.
Conclusion
This SSH IoT remotely tutorial has provided an extensive overview of leveraging SSH to manage IoT devices. From grasping the fundamentals to implementing best practices, you are now well-equipped to handle your IoT devices securely and effectively.
We invite you to share your thoughts and experiences in the comments section below. Furthermore, explore our additional articles for deeper insights into IoT and related technologies. Together, let's drive the future of secure IoT management and innovation!