Secure Shell (SSH) web access for IoT devices has emerged as a transformative solution for both tech enthusiasts and professionals in today's rapidly evolving digital landscape. As the Internet of Things (IoT) continues to expand, ensuring secure and efficient remote access to these devices has become more critical than ever. This article delves into the top SSH web access solutions for IoT devices, providing comprehensive insights into their features, advantages, and security considerations.
In the modern interconnected world, IoT devices are becoming increasingly ubiquitous, from smart thermostats in homes to sophisticated industrial sensors. These devices require secure and reliable remote access to function optimally. SSH web access offers a robust framework for managing and interacting with these devices securely, streamlining the process and enhancing efficiency.
Whether you're a network administrator, a developer, or an IoT enthusiast, understanding the best SSH web access options available can empower you to make informed decisions. This article explores various tools, solutions, and best practices, ensuring your IoT devices remain secure and accessible while meeting your specific needs.
Read also:Diesel Dave Net Worth
Understanding SSH Web Access for IoT Devices
SSH (Secure Shell) is a cryptographic network protocol designed to facilitate secure communication between devices over potentially unsecured networks. When integrated with web-based interfaces, SSH web access enables users to manage IoT devices remotely using standard web browsers. This eliminates the need for specialized software, making device management more accessible and straightforward.
For IoT devices, SSH web access offers numerous advantages, including:
- Enhanced Security: Utilizes encryption protocols to protect sensitive data during transmission.
- Convenient Accessibility: Provides seamless remote access through web browsers, ensuring flexibility and convenience.
- Scalability: Supports the management of multiple devices, making it ideal for large-scale deployments.
- Reduced Dependency on Physical Access: Minimizes the need for physical interaction with devices, saving time and resources.
As IoT deployments grow in complexity, SSH web access solutions have become indispensable tools for maintaining device security and functionality, ensuring optimal performance across diverse environments.
The Importance of SSH Web Access for IoT Devices
IoT devices often operate in varied environments, ranging from smart homes to large-scale industrial facilities. Ensuring secure and reliable access to these devices is essential for maintaining their performance and security. SSH web access addresses these concerns by offering:
Advanced Security Protocols
SSH employs robust encryption protocols, such as AES and RSA, to safeguard data transmitted between devices. This ensures that sensitive information remains secure, even when accessed over public networks, protecting against unauthorized access and potential threats.
Efficient Remote Management
With SSH web access, users can manage IoT devices from anywhere in the world using a standard web browser. This eliminates the need for proprietary software, simplifies device management, and enhances operational efficiency, allowing users to perform tasks effortlessly without the constraints of location.
Read also:Peter Stormare In Prison Break
Scalability for Large-Scale Deployments
SSH web access solutions are designed to handle large-scale IoT deployments, making them ideal for businesses and industries with numerous connected devices. Whether managing a few devices or thousands, these solutions provide the scalability needed to accommodate growing demands while maintaining security and performance.
Key Features of Top SSH Web Access Solutions
When evaluating SSH web access solutions for IoT devices, several key features should be considered to ensure optimal performance and security:
1. Robust Authentication Mechanisms
Premier SSH web access solutions incorporate advanced authentication mechanisms, such as two-factor authentication (2FA) and public key authentication, ensuring only authorized users can access devices. These features enhance security and minimize the risk of unauthorized access.
2. Cutting-Edge Encryption Standards
Encryption is a cornerstone of SSH web access, and solutions should support modern encryption standards, such as AES-256, to safeguard data during transmission. This ensures that sensitive information remains protected, even in the face of evolving cyber threats.
3. Intuitive User Interfaces
Web-based interfaces should be user-friendly and intuitive, allowing users to navigate and perform tasks efficiently without requiring extensive training. A well-designed interface enhances usability and improves overall user experience.
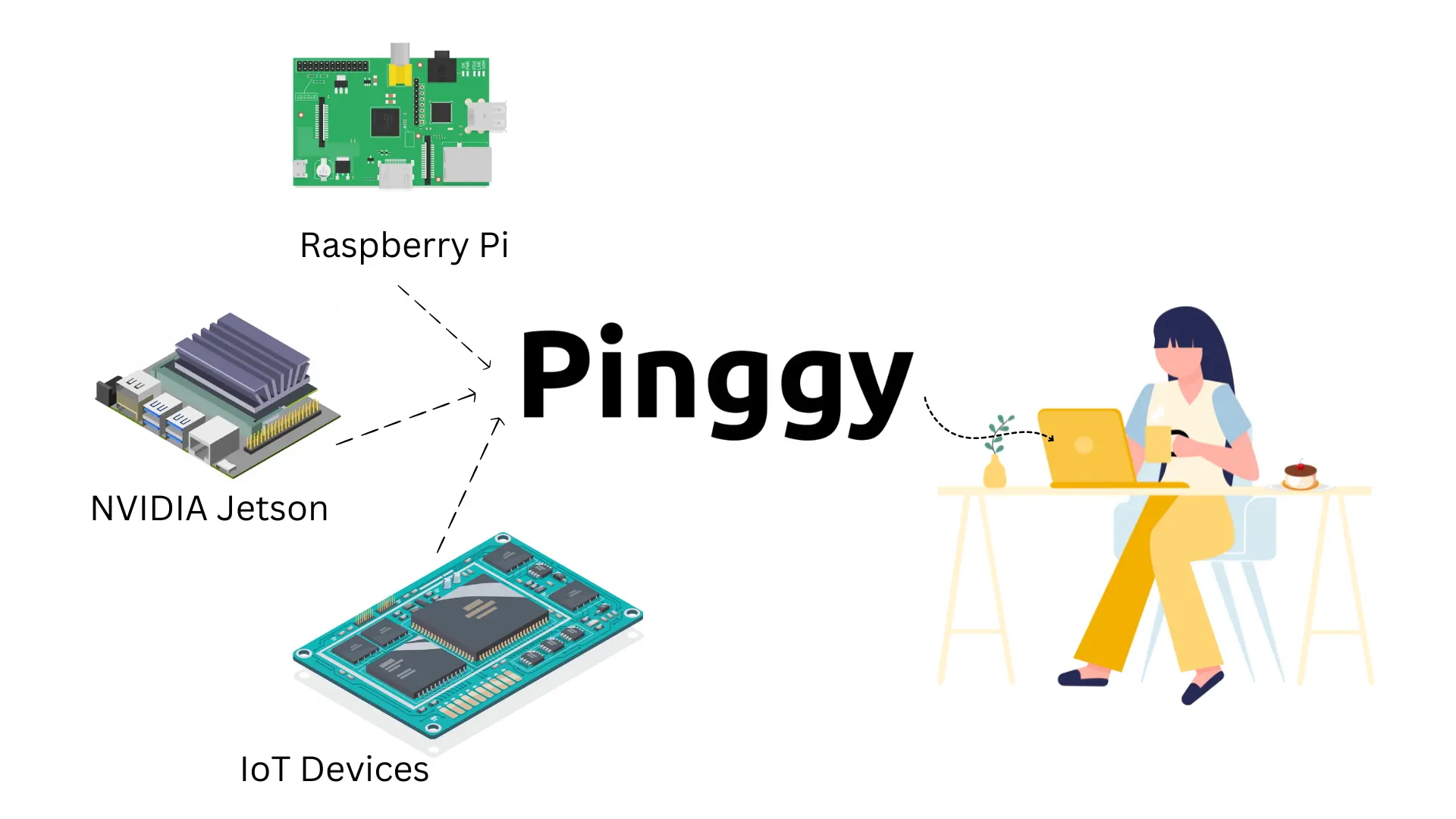
4. Compatibility with Diverse IoT Devices
The best SSH web access solutions should support a wide range of IoT devices, including those running on different operating systems and hardware platforms. This ensures seamless integration and management across diverse device ecosystems.
Top SSH Web Access Solutions for IoT Devices
Several SSH web access solutions stand out for their reliability, security, and ease of use. Below are some of the top options available:
1. WebSSH: A Versatile Open-Source Solution
WebSSH is a popular open-source solution that enables users to access SSH servers through web browsers. It supports modern encryption protocols and offers extensive customization options, making it suitable for both small-scale and enterprise-level IoT deployments. Its flexibility and adaptability make it a preferred choice for many users.
2. Termius: A Feature-Rich SSH Client
Termius is a powerful SSH client that provides web-based access to IoT devices. It supports multiple authentication methods, including SSH keys and 2FA, and features a user-friendly interface for managing devices. Its comprehensive feature set and ease of use make it an excellent choice for professionals and enthusiasts alike.
3. CloudShell: A Cloud-Based SSH Web Access Solution
CloudShell is a cloud-based SSH web access solution that enables secure remote access to IoT devices. It offers advanced security features, such as role-based access control, and integrates seamlessly with popular cloud platforms like AWS and Azure. Its scalability and cloud compatibility make it ideal for large-scale deployments.
4. SecureCRT: A Comprehensive SSH Client
SecureCRT is a robust SSH client that includes web-based access capabilities. It supports advanced encryption protocols and offers extensive customization options, making it a favorite among IT professionals. Its powerful features and reliability make it a top choice for managing IoT devices securely.
Best Practices for Implementing SSH Web Access
Implementing SSH web access for IoT devices requires careful planning and adherence to best practices to ensure a secure and effective deployment. Below are some recommendations:
1. Encourage Strong Passwords
Encourage users to create strong, unique passwords for SSH access. Avoid using default credentials and regularly update passwords to enhance security and minimize the risk of unauthorized access.
2. Enable Two-Factor Authentication
Two-factor authentication adds an extra layer of security by requiring users to provide two forms of identification before accessing IoT devices. This significantly reduces the risk of unauthorized access and enhances overall security.
3. Keep Software Up to Date
Regularly update SSH web access solutions and IoT devices with the latest software patches and security updates to protect against vulnerabilities and emerging threats. Staying current with updates ensures optimal performance and security.
4. Monitor Access Logs Regularly
Regularly review access logs to detect and respond to unauthorized access attempts promptly. Monitoring logs helps identify potential security breaches and ensures timely mitigation of risks.
Security Considerations for SSH Web Access
While SSH web access offers numerous benefits, it also introduces potential security risks. Below are some security considerations to keep in mind:
1. Protect Against Brute-Force Attacks
Implement rate-limiting and account lockout policies to prevent brute-force attacks on SSH credentials. These measures help safeguard against unauthorized access attempts and enhance overall security.
2. Secure Private Keys
Store SSH private keys in a secure location and limit access to authorized personnel only. Properly securing private keys is crucial to maintaining the integrity and security of SSH web access solutions.
3. Configure Firewall Rules
Configure firewall rules to restrict SSH access to trusted IP addresses and networks. This minimizes the risk of unauthorized access and ensures that only authorized users can connect to IoT devices.
Case Studies: Real-World Applications of SSH Web Access
Several organizations have successfully implemented SSH web access for their IoT deployments, demonstrating its practical benefits and versatility. Below are two case studies highlighting its real-world applications:
Case Study 1: Smart City Infrastructure
A major city deployed SSH web access to manage its network of IoT-enabled streetlights. This solution enabled maintenance teams to monitor and control the lights remotely, reducing response times, optimizing energy consumption, and significantly lowering operational costs. The implementation of SSH web access transformed the city's infrastructure management, enhancing efficiency and sustainability.
Case Study 2: Industrial Automation
An industrial manufacturing plant implemented SSH web access to manage its IoT sensors and machines. This enabled engineers to troubleshoot issues and optimize processes from anywhere in the world, improving productivity and reducing downtime. The integration of SSH web access streamlined operations and enhanced the plant's overall performance.
Future Trends in SSH Web Access for IoT Devices
The future of SSH web access for IoT devices looks promising, with several emerging trends set to shape the industry:
1. Integration with AI and Machine Learning
AI and machine learning technologies are being integrated into SSH web access solutions to enhance security, automation, and predictive capabilities. These advancements enable smarter decision-making and improve the overall efficiency of IoT device management.
2. Adoption of Quantum-Resistant Encryption
As quantum computing becomes more prevalent, SSH web access solutions are expected to adopt quantum-resistant encryption algorithms to safeguard against future threats. This ensures long-term security and protects sensitive data from evolving cyber risks.
3. Greater Emphasis on User Privacy
With growing concerns about data privacy, SSH web access solutions will prioritize user privacy and compliance with regulations such as GDPR and CCPA. This focus on privacy ensures that user data remains protected and compliant with global standards.
Conclusion
SSH web access has transformed the way IoT devices are managed and secured, offering secure, convenient, and scalable remote access. These solutions have become essential tools for modern-day technology professionals, enabling them to efficiently manage and protect their IoT deployments. To achieve the best results, it is crucial to select a solution that aligns with your specific needs and adheres to best practices for implementation and security.
We encourage you to explore the options discussed in this article and consider how SSH web access can enhance your IoT deployments. Feel free to leave a comment or share this article with others who may find it valuable. For more insights into IoT and related technologies, be sure to explore our other articles.
Table of Contents
- Understanding SSH Web Access for IoT Devices
- The Importance of SSH Web Access for IoT Devices
- Key Features of Top SSH Web Access Solutions
Top SSH Web Access Solutions for IoT Devices
- Best Practices for Implementing SSH Web Access
- Security Considerations for SSH Web Access
- Case Studies: Real-World Applications of SSH Web Access
- Future Trends in SSH Web Access for IoT Devices
- Conclusion