In today’s hyper-connected digital landscape, ensuring the secure integration of IoT devices within firewall-protected networks has become a cornerstone of modern cybersecurity. As the proliferation of IoT devices continues to surge, safeguarding their communication with external systems while maintaining robust security protocols is more critical than ever. This article explores cutting-edge strategies, essential tools, and practical techniques to establish secure connections for IoT devices behind firewalls, empowering you to protect your network while fully leveraging the transformative potential of IoT technology.
The Internet of Things (IoT) has redefined how we interact with technology, significantly enhancing efficiency and convenience in both personal and professional settings. However, integrating these devices into existing networks, particularly those safeguarded by firewalls, demands a meticulous approach to ensure data integrity and security. Without proper planning, the vulnerabilities inherent in IoT devices can expose networks to cyber threats.
This guide offers in-depth insights into the process of securely connecting IoT devices behind firewalls. By adhering to the principles outlined here, you can fortify your network infrastructure while fully capitalizing on the advantages of IoT. Let’s delve deeper into the strategies that will safeguard your IoT ecosystem.
Read also:Abruzzi Prison Break
Table of Contents
- Understanding IoT Devices and Firewalls
- The Importance of Firewalls in IoT Security
- Establishing Secure Bi-Directional Communication
- Best Practices for Securing IoT Connections
- Leveraging Tools and Technologies for IoT Connectivity
- The Role of Network Segmentation in IoT Security
- Implementing Robust Data Encryption for IoT Devices
- Configuring Firewalls for Enhanced IoT Security
- Addressing Common Challenges in IoT Firewall Integration
- Conclusion and Future Considerations
Understanding IoT Devices and Firewalls
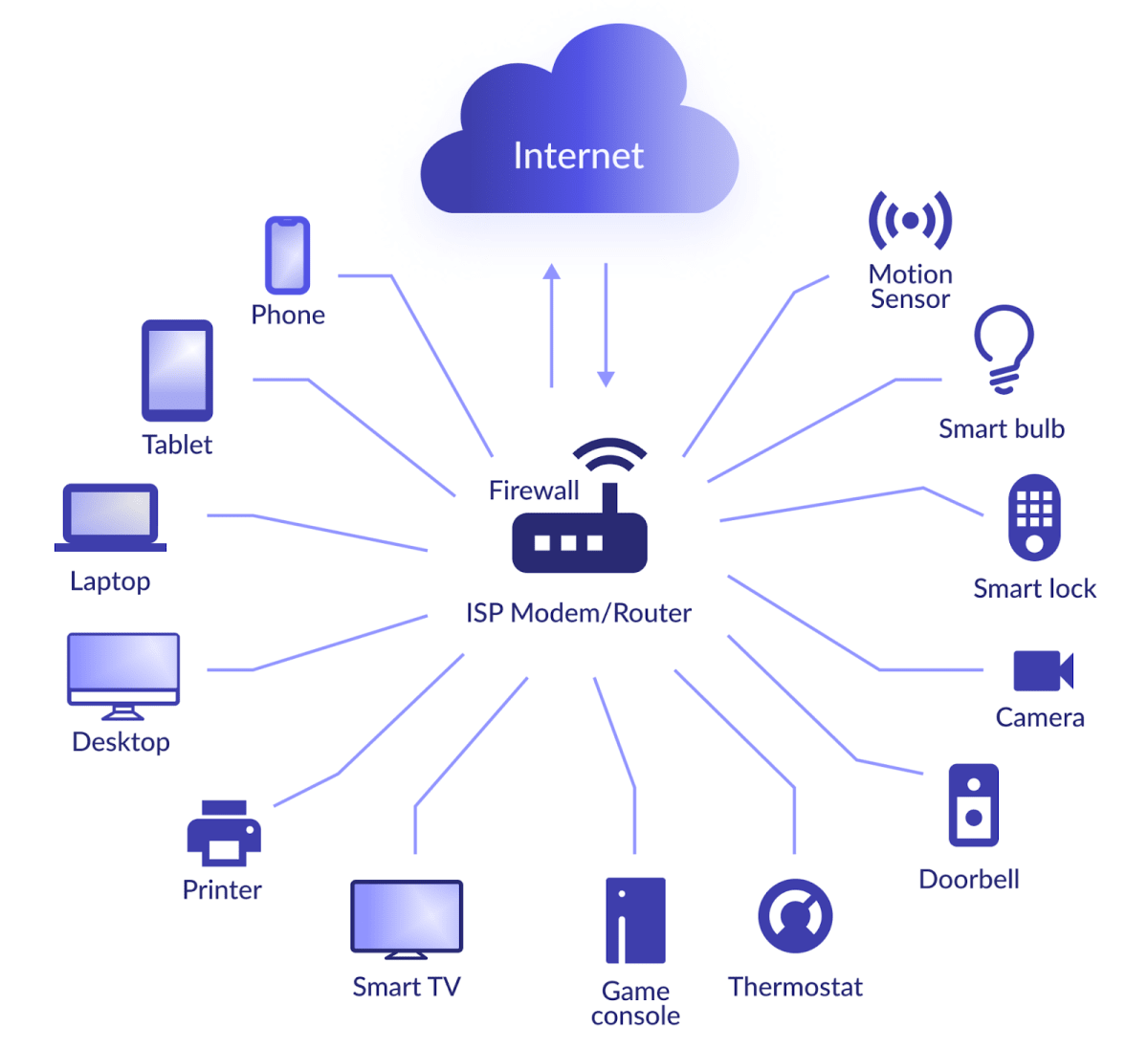
IoT devices are revolutionizing industries by enabling smart homes, advanced industrial automation, and cutting-edge healthcare solutions. However, as these devices increasingly rely on internet connectivity, they become susceptible to cyber threats. Firewalls play a pivotal role in protecting networks by meticulously filtering incoming and outgoing traffic according to predefined security rules.
Integrating IoT devices behind a firewall requires balancing accessibility with security. Properly configured firewalls ensure that IoT devices remain protected while maintaining seamless communication with external systems, thereby preserving the integrity of your network.
Exploring the Functions of Firewalls
Firewalls serve as a protective barrier between trusted internal networks and untrusted external networks like the internet. They monitor and control network traffic based on a comprehensive set of security rules. These rules can be tailored to permit or restrict specific types of traffic, ensuring only authorized data passes through. By doing so, firewalls provide a critical layer of defense against cyber threats.
The Importance of Firewalls in IoT Security
IoT devices, often constrained by limited resources, frequently lack advanced security features, making them vulnerable to attacks such as Distributed Denial of Service (DDoS) and unauthorized access. Firewalls mitigate these risks by regulating access to IoT devices and shielding them from malicious traffic.
As highlighted in a Gartner report, the global IoT security market is projected to exceed $3.1 billion by 2023, underscoring the growing significance of securing IoT devices. In enterprise environments, where data breaches can result in substantial financial and reputational damage, firewalls are indispensable for safeguarding sensitive information.
Key Advantages of Firewalls for IoT Devices
- Prevent unauthorized access to IoT devices, reducing the risk of data breaches.
- Protect sensitive data exchanged between IoT devices and external networks.
- Filter out malicious traffic to minimize the likelihood of cyberattacks.
- Enhance network visibility and control over IoT device communication.
Establishing Secure Bi-Directional Communication
A significant challenge in connecting IoT devices behind a firewall is enabling secure bi-directional communication. IoT devices often need to transmit data to cloud servers and receive commands or updates from external sources. Configuring firewalls to facilitate this type of communication necessitates meticulous planning and execution.
Read also:Robert Benevides
To achieve secure bi-directional communication, techniques such as port forwarding, reverse proxies, or virtual private networks (VPNs) can be employed. These methods allow IoT devices to interact with external systems without compromising the security of the internal network.
Utilizing Port Forwarding for IoT Devices
Port forwarding involves directing incoming traffic from a specific port on the firewall to a designated IoT device within the network. This technique is widely used to enable remote access to IoT devices while ensuring firewall protection. Properly configured port forwarding enhances both security and functionality.
Best Practices for Securing IoT Connections
Implementing best practices is essential for ensuring secure connections between IoT devices and external networks. Below are some vital strategies to consider:
- Employ strong authentication mechanisms, such as two-factor authentication (2FA), to secure access to IoT devices.
- Regularly update firmware and software to address potential security vulnerabilities promptly.
- Monitor network activity for suspicious behavior and deploy intrusion detection systems (IDS) to enhance security.
- Limit access to IoT devices by implementing role-based access control (RBAC), ensuring only authorized users can interact with them.
Securing IoT Communication Protocols
IoT devices frequently utilize communication protocols such as MQTT, CoAP, and HTTP. Ensuring the security of these protocols is paramount for protecting data transmitted between devices and external systems. By encrypting communication channels and employing secure authentication methods, the risks of data interception and unauthorized access can be significantly mitigated.
Leveraging Tools and Technologies for IoT Connectivity
A variety of tools and technologies can facilitate the secure connection of IoT devices behind firewalls. These include:
- Firewall appliances specifically designed for IoT environments, offering advanced security features tailored to IoT needs.
- Cloud-based IoT platforms that provide built-in security features, simplifying the management and protection of IoT devices.
- Network monitoring tools that offer real-time visibility into IoT device activity, enabling proactive identification of potential threats.
- Encryption protocols such as TLS/SSL, which secure data in transit, ensuring the confidentiality and integrity of information exchanged.
IoT-Specific Firewalls
IoT-specific firewalls are engineered to address the unique security challenges associated with IoT devices. These firewalls feature advanced capabilities such as deep packet inspection, intrusion prevention, and device profiling, making them ideal for securing IoT networks. By deploying IoT-specific firewalls, organizations can enhance their network’s resilience against cyber threats.
The Role of Network Segmentation in IoT Security
Network segmentation involves partitioning a network into smaller, isolated segments to enhance security and optimize performance. By segmenting IoT devices into distinct subnets, the potential impact of a security breach can be minimized, and unauthorized access to critical systems can be prevented.
Segmentation can be achieved through techniques such as VLANs (Virtual Local Area Networks) or firewalls with advanced routing capabilities. This approach ensures that IoT devices are separated from other network resources, reducing the risk of lateral movement by attackers and enhancing overall network security.
Benefits of Network Segmentation
- Enhanced security by isolating IoT devices from critical systems, limiting the scope of potential breaches.
- Improved network performance by reducing traffic congestion and optimizing resource allocation.
- Simplified management of IoT devices and associated security policies, streamlining network administration.
Implementing Robust Data Encryption for IoT Devices
Data encryption is a foundational aspect of IoT security. By encrypting data transmitted between IoT devices and external systems, sensitive information can be safeguarded from unauthorized access and interception. Common encryption methods utilized in IoT environments include:
- TLS/SSL for securing communication channels, ensuring data privacy during transmission.
- AES (Advanced Encryption Standard) for encrypting data at rest, protecting stored information from unauthorized access.
- Elliptic Curve Cryptography (ECC) for lightweight encryption, ideal for resource-constrained IoT devices.
Implementing Encryption in IoT Networks
To effectively implement encryption in IoT networks, consider the following:
- Select encryption protocols compatible with the capabilities of IoT devices, ensuring seamless integration without compromising performance.
- Use strong encryption keys and rotate them regularly to prevent key compromise, maintaining the integrity of encrypted data.
- Ensure consistent application of encryption across all communication channels, eliminating potential vulnerabilities.
Configuring Firewalls for Enhanced IoT Security
Proper configuration of firewalls is crucial for securing IoT devices behind firewalls. Firewalls should be meticulously configured to permit only essential traffic to and from IoT devices while blocking all other traffic. This can be achieved by:
- Defining specific rules for IoT device communication, ensuring only authorized interactions are allowed.
- Using application control to restrict access to unauthorized applications, minimizing potential security risks.
- Implementing intrusion prevention systems (IPS) to detect and block malicious traffic, enhancing overall network security.
Advanced Firewall Features for IoT
Modern firewalls offer advanced features that significantly enhance IoT security, including:
- Deep packet inspection for analyzing traffic at the application layer, identifying and mitigating potential threats.
- Device profiling to identify and manage IoT devices on the network, ensuring comprehensive visibility and control.
- Behavioral analytics for detecting anomalies in IoT device activity, enabling proactive threat detection and response.
Addressing Common Challenges in IoT Firewall Integration
Connecting IoT devices behind firewalls can occasionally lead to connectivity issues. Below are some prevalent problems and their solutions:
- Connection timeouts: Review firewall rules to ensure necessary ports are open and that traffic is permitted without restrictions.
- Authentication failures: Verify the accuracy of authentication credentials and ensure devices are properly configured to meet security requirements.
- Performance degradation: Optimize network settings and consider implementing Quality of Service (QoS) policies to enhance performance and reliability.
Monitoring IoT Device Activity
Continuous monitoring of IoT device activity is essential for identifying and resolving connectivity issues. Utilize network monitoring tools to track device performance, detect anomalies, and troubleshoot problems in real time. Proactive monitoring ensures the smooth operation of IoT devices and enhances overall network security.
Conclusion and Future Considerations
Connecting IoT devices behind firewalls necessitates a comprehensive approach that balances security with functionality. By adhering to the best practices outlined in this article, you can ensure that your IoT devices remain secure while maintaining seamless communication with external systems. This balance is crucial for maximizing the benefits of IoT technology while minimizing associated risks.
To further strengthen your IoT security strategy, consider adopting advanced technologies such as AI-driven threat detection and machine learning-based anomaly detection. These tools provide deeper insights into network activity, enabling you to stay ahead of emerging threats and protect your organization’s digital assets effectively.
We invite you to share your thoughts and experiences in the comments section below. Additionally, explore other articles on our site for additional insights into IoT security and related topics. Together, we can build a safer and more connected digital future!