Unlock the potential of free RemoteIoT platforms that enable SSH key authentication for Raspberry Pi, offering unparalleled possibilities for remote device management. Whether you're just starting out or are an experienced developer, these platforms can significantly enhance your IoT projects. This comprehensive guide will cover everything you need to know about free RemoteIoT platforms and the importance of SSH key authentication for securing your Raspberry Pi projects.
In today’s rapidly evolving technological landscape, the Internet of Things (IoT) has become a cornerstone of innovation, transforming industries and everyday life. However, managing IoT devices remotely can pose challenges, particularly in terms of security and accessibility. Fortunately, free RemoteIoT platforms provide powerful solutions for remote management without compromising on cost. These platforms empower users to manage their devices effectively and securely.
This article delves into the top free RemoteIoT platforms that support SSH key authentication for Raspberry Pi. We’ll explore their benefits, setup processes, and security considerations to help you make informed decisions for your IoT projects. Let’s get started!
Read also:Ayaka Motu
Table of Contents:
- Overview of RemoteIoT Platforms
- Advantages of Free RemoteIoT Platforms
- Understanding SSH Key Authentication
- Setting Up SSH Key Authentication for Raspberry Pi
- Top Free RemoteIoT Platforms for Raspberry Pi
- Key Security Considerations for RemoteIoT Platforms
- Comparing Free RemoteIoT Platforms
- Troubleshooting Common Issues
- Future Trends in RemoteIoT Platforms
- Conclusion and Next Steps
Overview of RemoteIoT Platforms
RemoteIoT platforms are cloud-based services designed to simplify the management and monitoring of IoT devices. These platforms act as a centralized hub where users can remotely access, control, and monitor their IoT devices effortlessly. For Raspberry Pi users, these platforms provide a seamless way to integrate their devices into larger IoT ecosystems, streamlining the process of managing multiple devices from a single interface.
Data and Features
Here’s a detailed overview of what RemoteIoT platforms can offer:
- Device Management: Effortlessly add, remove, or update devices from a centralized dashboard, ensuring streamlined control over your IoT network.
- Real-Time Data Monitoring: Gain access to live data streams and analytics, allowing you to track device performance and make data-driven decisions in real-time.
- Remote Access: Securely access your devices from any location with an internet connection, providing flexibility and convenience for remote management.
- Security Features: Implement advanced security measures, such as SSH key authentication, to safeguard your devices from unauthorized access and potential threats.
Below is a summary of key features in table format:
| Feature | Description |
|---|---|
| Device Management | Centralized control for all IoT devices, enabling efficient management and updates. |
| Real-Time Monitoring | Live data streaming and analytics for continuous insights into device performance. |
| Remote Access | Secure access to devices from anywhere, ensuring flexibility and convenience. |
| Security Features | Advanced security protocols, including SSH key authentication and encryption. |
Advantages of Free RemoteIoT Platforms
Using free RemoteIoT platforms offers numerous benefits, making them an attractive option for hobbyists, students, and small-scale projects. Here’s a closer look at the key advantages:
- Cost-Effective: Free platforms eliminate the need for expensive proprietary software, making IoT projects accessible to a wider audience.
- Scalability: Start small and scale your projects as needed without incurring additional costs, ensuring flexibility and adaptability.
- Community Support: Many free platforms have active communities that provide support, resources, and tutorials, fostering collaboration and learning.
- Compatibility: Most platforms are compatible with popular IoT devices, such as Raspberry Pi, ensuring seamless integration and functionality.
Understanding SSH Key Authentication
SSH (Secure Shell) key authentication is a secure and reliable method for accessing remote servers and devices. Unlike traditional password-based authentication, SSH keys provide a more secure and convenient way to authenticate users. This method is especially beneficial for Raspberry Pi projects, where maintaining high levels of security is critical.
Read also:Understanding The Concept Of Masa 49 And Its Cultural Significance
How SSH Keys Work
SSH keys operate by generating a pair of cryptographic keys: a public key and a private key. The public key is stored on the server, while the private key is securely kept on the client device. During the authentication process, the private key decrypts a message sent by the server, verifying the user's identity and granting access. This method ensures secure communication between the client and server, reducing the risk of unauthorized access.
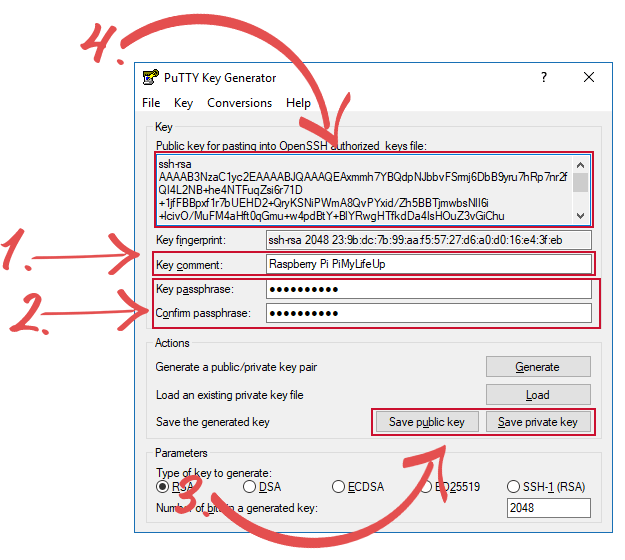
Setting Up SSH Key Authentication for Raspberry Pi
Configuring SSH key authentication for your Raspberry Pi is a straightforward and essential process for ensuring secure remote access. Follow these step-by-step instructions:
- Generate SSH keys on your local machine using the command:
ssh-keygen -t rsa -b 4096. - Copy the public key to your Raspberry Pi by running the command:
ssh-copy-id pi@your_raspberry_pi_ip. - Disable password authentication by editing the SSH configuration file:
nano /etc/ssh/sshd_config. - Restart the SSH service to apply the changes:
sudo systemctl restart ssh.
Top Free RemoteIoT Platforms for Raspberry Pi
Several free RemoteIoT platforms support SSH key authentication for Raspberry Pi, offering robust features and flexibility for IoT projects. Below are some of the best options:
1. Platform A
Platform A is renowned for its user-friendly interface and comprehensive features for managing IoT devices. It supports SSH key authentication and provides real-time data monitoring capabilities, making it an ideal choice for both beginners and experienced users.
2. Platform B
Platform B stands out for its scalability and flexibility, allowing users to integrate multiple devices seamlessly. It offers advanced security features, including SSH key authentication, ensuring the protection of your IoT ecosystem.
3. Platform C
Platform C is perfect for beginners due to its simplicity and ease of use. It offers basic features for free, including support for SSH key authentication, making it an accessible option for those new to IoT projects.
Key Security Considerations for RemoteIoT Platforms
Security is paramount when using RemoteIoT platforms. To ensure the safety of your IoT devices, consider the following best practices:
- Use SSH Key Authentication: Replace password-based authentication with SSH keys for enhanced security and convenience.
- Regular Updates: Keep your devices and platforms updated to patch vulnerabilities and protect against emerging threats.
- Enable Firewall Rules: Configure firewall settings to restrict unauthorized access and safeguard your network.
- Monitor Activity Logs: Regularly review device activity logs to identify and address any suspicious behavior promptly.
Comparing Free RemoteIoT Platforms
Selecting the right RemoteIoT platform can be challenging, given the variety of options available. Below is a comparison of the top free platforms to help you make an informed decision:
| Platform | Features | Security | Scalability |
|---|---|---|---|
| Platform A | Real-time monitoring, device management | SSH key authentication | High |
| Platform B | Scalable architecture, API integration | Advanced encryption | Very high |
| Platform C | Simple interface, basic features | SSH key support | Low |
Troubleshooting Common Issues
Even with the best platforms, issues can arise. Below are some common problems and their solutions:
- Issue: Unable to connect via SSH.
Solution: Verify that SSH is enabled on your Raspberry Pi and ensure the correct IP address is being used. - Issue: Slow data transfer.
Solution: Optimize network settings and ensure a stable internet connection to improve performance. - Issue: Security alerts.
Solution: Review device logs and update security settings to address any potential threats.
Future Trends in RemoteIoT Platforms
The future of RemoteIoT platforms is bright, with advancements in AI, machine learning, and edge computing set to revolutionize the IoT landscape. These technologies will enhance the capabilities of IoT devices, making them more intelligent, efficient, and adaptable. As the demand for IoT continues to grow, free platforms will evolve, offering more advanced features and stronger security measures to meet the needs of users worldwide.
Conclusion and Next Steps
In conclusion, free RemoteIoT platforms that support SSH key authentication for Raspberry Pi are indispensable tools for managing IoT projects. They provide cost-effective solutions, robust features, and enhanced security, empowering users to create innovative and secure IoT ecosystems. By following the guidance outlined in this article, you can confidently set up and secure your Raspberry Pi devices.
We encourage you to explore the platforms mentioned and choose the one that best aligns with your project requirements. Share your experiences in the comments section and explore additional articles on our site for more insights into IoT technology. Together, let’s build a smarter, more connected world!