Managing IoT devices remotely while operating behind a firewall can be a challenge, but it is entirely feasible with the right strategies and tools. If you're working in an environment where network security is critical, understanding how to configure your system properly becomes essential. This guide will walk you through the process of using RemoteIoT behind a firewall on Windows, ensuring seamless communication without compromising security.
As the Internet of Things (IoT) continues to expand, the demand for secure and efficient remote management grows. Whether you're a network administrator or a tech enthusiast, this article will equip you with the knowledge needed to navigate through firewalls and ensure your IoT devices remain accessible and secure.
In this detailed guide, we will cover everything from setting up port forwarding to configuring firewalls, ensuring compatibility with Windows systems, and troubleshooting common issues. By the end, you'll have a comprehensive understanding of how to use RemoteIoT effectively while maintaining network integrity.
Read also:Scott Wapner Family
Table of Contents
- Introduction to RemoteIoT
- Understanding Firewalls
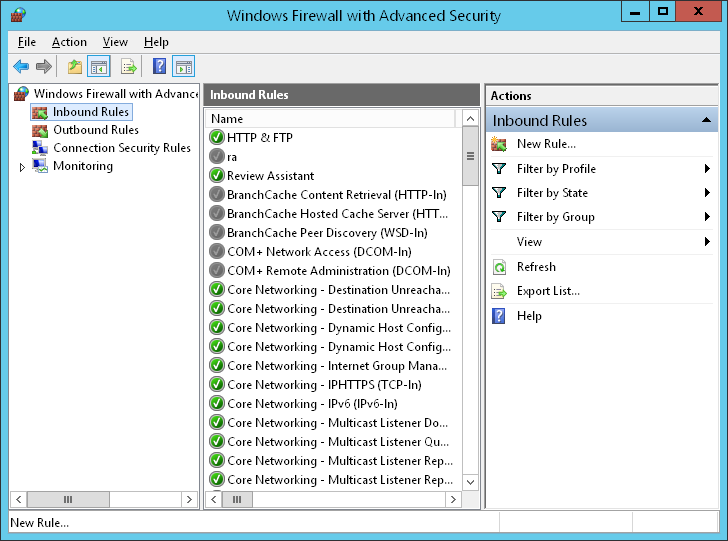
- Configuring Windows for RemoteIoT
- Setting Up Port Forwarding
- Securing Your RemoteIoT Connection
- Troubleshooting Common Issues
- Optimizing Performance
- Best Practices for RemoteIoT
- Frequently Asked Questions
- Conclusion and Next Steps
Getting Started with RemoteIoT
RemoteIoT is an advanced tool designed to facilitate remote access and management of IoT devices. It enables users to interact with their devices from anywhere globally, provided the necessary configurations are in place. The main challenge when using RemoteIoT behind a firewall lies in ensuring that the firewall does not obstruct essential communication channels.
One of the standout features of RemoteIoT is its adaptability to various network environments. By understanding how to configure it correctly, you can ensure that your IoT devices remain accessible without compromising your network's security.
Key Features of RemoteIoT
- Remote device management with intuitive controls.
- Secure data transmission using advanced encryption protocols.
- Compatibility with multiple platforms, including Windows, Mac, and Linux.
- Customizable settings tailored to different network environments.
An Overview of Firewalls
A firewall serves as a network security system that monitors and regulates incoming and outgoing network traffic based on predefined security rules. When using RemoteIoT behind a firewall, it's vital to grasp how firewalls function and how they can influence your IoT device's connectivity.
Types of Firewalls
- Packet-filtering firewalls: These analyze individual packets of data and decide whether to allow or block them based on specific criteria.
- Stateful inspection firewalls: These track active connections and ensure that only legitimate packets are allowed through.
- Application-layer firewalls: These provide deeper inspection by examining the content of the data being transmitted.
- Next-generation firewalls: These combine traditional firewall capabilities with advanced features like intrusion prevention and application awareness.
Understanding the type of firewall you're working with will enable you to make the necessary adjustments for RemoteIoT to function effectively.
Preparing Your Windows System for RemoteIoT
Before configuring your firewall, ensure that your Windows system is set up to support RemoteIoT. This involves enabling specific services and adjusting network settings to optimize performance.
Steps to Configure Windows
- Enable Remote Desktop Protocol (RDP): This allows secure remote access to your Windows system, which is essential for managing IoT devices.
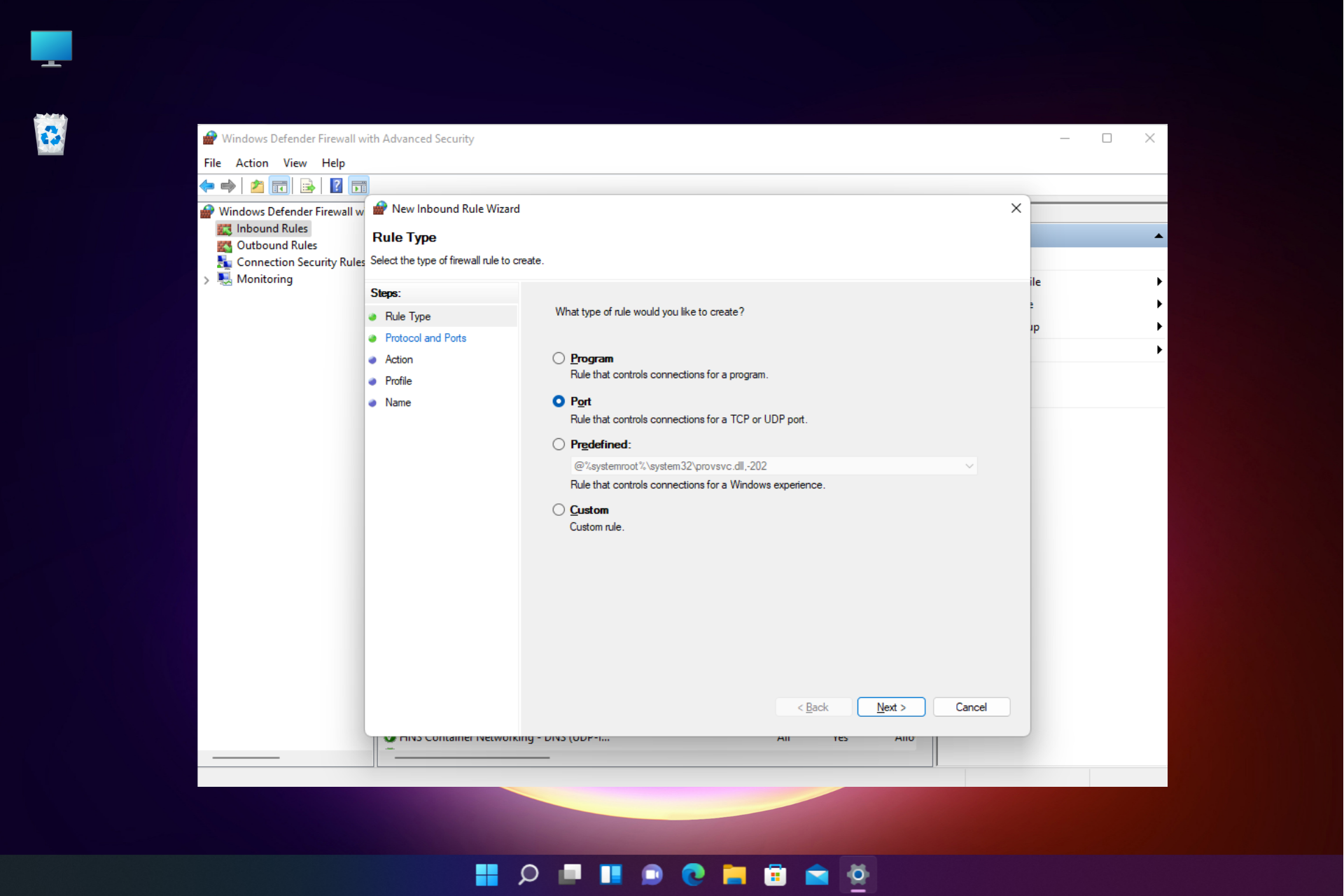
- Adjust Windows Defender Firewall settings: Configure the firewall to permit RemoteIoT traffic, ensuring that the necessary ports are open.
- Install necessary drivers and software: Ensure that your IoT devices have the required drivers and software installed for seamless operation.
By following these steps, you can prepare your Windows system to handle RemoteIoT operations efficiently and securely.
Read also:Diesel Dave Net Worth
Configuring Port Forwarding for RemoteIoT
Port forwarding is a critical technique that directs incoming traffic to a specific device on your network. When using RemoteIoT behind a firewall, setting up port forwarding is essential to ensure that your IoT devices can communicate with external networks.
Steps to Set Up Port Forwarding
- Log in to your router's administrative interface: Access your router's settings using its IP address and login credentials.
- Locate the port forwarding section: Navigate to the port forwarding settings and create a new rule.
- Specify the port number and device IP address: Assign the appropriate port number and the IP address of your IoT device to enable communication.
Port forwarding not only enhances the accessibility of your IoT devices but also maintains a secure network environment.
Enhancing Security for RemoteIoT
Security should always be a top priority when managing IoT devices. Using RemoteIoT behind a firewall requires additional measures to ensure that your connection remains secure and protected from potential threats.
Security Measures
- Use strong passwords and encryption protocols: Implement robust authentication methods to safeguard your devices from unauthorized access.
- Regularly update firmware and software: Keep your systems up to date with the latest security patches and improvements.
- Implement two-factor authentication: Add an extra layer of security by requiring users to provide two forms of identification before accessing your devices.
By incorporating these security measures, you can protect your IoT devices from potential cyber threats and unauthorized access.
Resolving Common Issues with RemoteIoT
Even with meticulous configuration, issues may arise when using RemoteIoT behind a firewall. Understanding common problems and their solutions can help you address them quickly and efficiently.
Common Issues and Solutions
- Connection timeouts: Verify that your firewall rules are correctly configured and ensure that the necessary ports are open.
- Device inaccessibility: Check that your IoT device is properly configured and connected to the network. Restart the device if necessary.
- Security alerts: Review your security settings and ensure that they are current and aligned with best practices.
Addressing these issues promptly will help maintain the reliability and functionality of your RemoteIoT setup.
Maximizing Performance with RemoteIoT
To achieve optimal performance with RemoteIoT, it's essential to fine-tune your network settings and ensure that your devices are running efficiently. This involves monitoring and adjusting various aspects of your setup.
Performance Optimization Tips
- Monitor network traffic: Identify bottlenecks and areas for improvement by analyzing your network's performance.
- Use compression techniques: Reduce data transfer times by compressing files and data streams where possible.
- Regularly test your setup: Conduct routine tests to ensure that your RemoteIoT system operates smoothly and efficiently.
By following these tips, you can enhance the performance of your RemoteIoT system and ensure seamless operations.
Adopting Best Practices for RemoteIoT
Following best practices is crucial for maintaining a secure and efficient RemoteIoT setup. These practices will help you avoid common pitfalls and ensure long-term success in managing your IoT devices.
Best Practices
- Regularly review and update your firewall rules: Stay proactive by keeping your firewall configurations current and aligned with your network's needs.
- Keep your software and firmware up to date: Regular updates ensure that your systems are equipped with the latest security features and improvements.
- Document your configurations: Maintain detailed records of your settings and configurations for future reference and troubleshooting.
By adhering to these best practices, you can build a robust RemoteIoT system that meets your requirements and ensures long-term success.
Frequently Asked Questions
Q: Is RemoteIoT compatible with Mac systems?
A: Yes, while this guide focuses on Windows, RemoteIoT can also be configured to work on Mac systems with appropriate adjustments.
Q: How frequently should I update my firewall rules?
A: It's advisable to review and update your firewall rules regularly, especially after making significant changes to your network setup or adding new devices.
Q: What are some common security risks associated with RemoteIoT?
A: Common risks include unauthorized access, data breaches, and malware infections. Implementing strong security measures, such as encryption and two-factor authentication, can significantly mitigate these risks.
Conclusion and Next Steps
Using RemoteIoT behind a firewall on Windows is an achievable task with the right knowledge and tools. By following the steps outlined in this guide, you can ensure that your IoT devices remain accessible and secure. Remember to regularly update your configurations and adhere to best practices to maintain optimal performance.
We encourage you to share your experiences and insights in the comments section below. Additionally, explore other articles on our site for more valuable information on IoT and network management.
Stay informed and take the next step in mastering RemoteIoT today!
Data Source: Cisco Firewalls, Microsoft Windows