The Internet of Things (IoT) has reshaped how devices interact, and peer-to-peer (P2P) connections have emerged as a cornerstone of this transformation. The IoT P2P example demonstrates the ability of devices to communicate directly without relying on centralized servers, leading to enhanced efficiency, reduced latency, and improved scalability. This article delves into the concept of IoT P2P connections, their applications, and their impact on the future of connected systems.
As technology evolves, IoT devices have become increasingly sophisticated, enabling smarter homes, industries, and cities. P2P architecture offers a unique advantage by allowing devices to communicate directly, bypassing traditional server-based models. This approach not only enhances performance but also reduces the costs associated with maintaining centralized infrastructure, making it a game-changer for modern connectivity.
This comprehensive guide explores the intricacies of IoT P2P connections, offering practical examples, technical insights, and actionable advice for developers and enthusiasts. Whether you're a beginner or an experienced professional, this article will equip you with the knowledge needed to harness IoT P2P technology effectively.
Read also:Unveiling The World Of Beeg A Comprehensive Guide
Table of Contents
- What is IoT P2P?
- Benefits of IoT P2P
- Architecture of IoT P2P
- Real-World IoT P2P Examples
- Challenges in IoT P2P
- IoT P2P Protocols
- Security Considerations
- Future of IoT P2P
- How to Implement IoT P2P
- Conclusion
Understanding IoT P2P: A Decentralized Approach
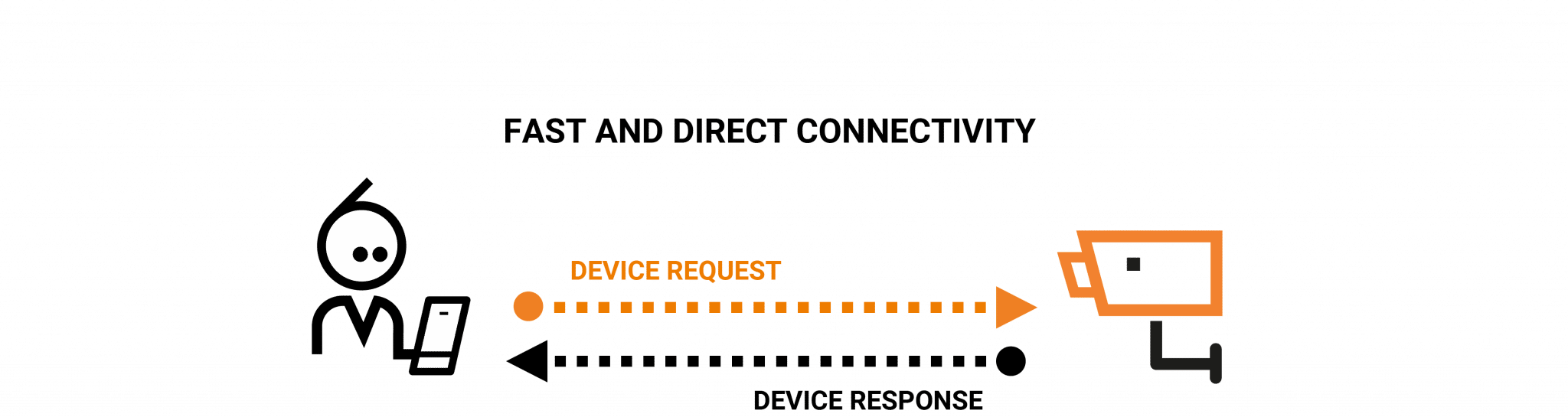
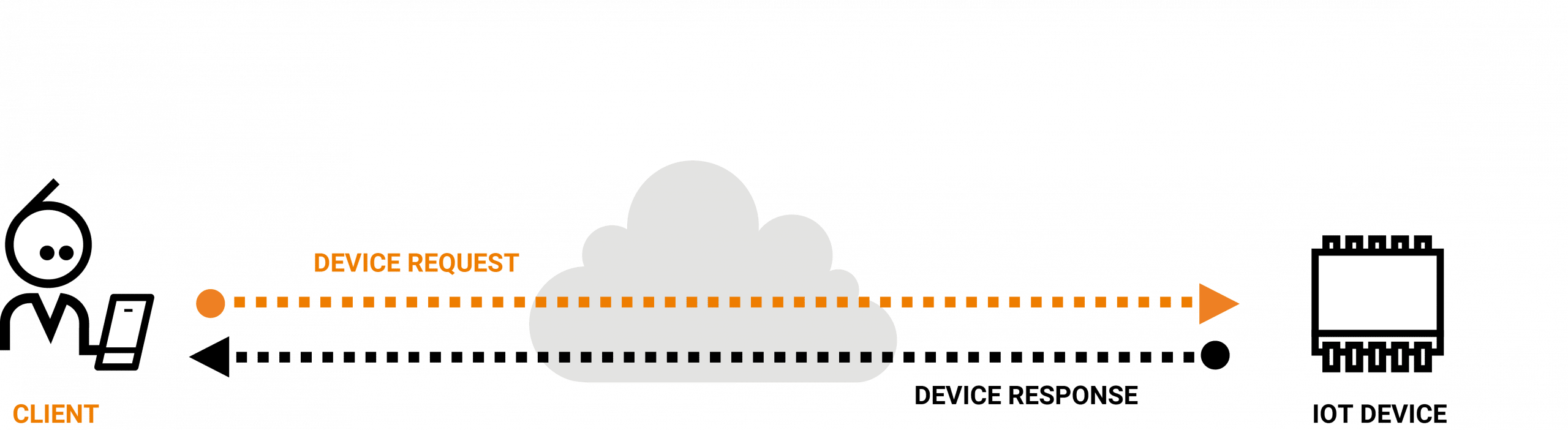
In the world of IoT, peer-to-peer (P2P) communication refers to a decentralized architecture where devices establish direct connections and exchange data without the need for intermediaries such as central servers. This approach is particularly advantageous in scenarios where real-time communication and low-latency interactions are essential. The IoT P2P example highlights how devices can autonomously collaborate, enhancing system efficiency and enabling seamless interactions.
P2P architecture has been utilized in various applications, such as file-sharing networks and VoIP systems, for years. However, its application in IoT introduces exciting possibilities and challenges. By eliminating the dependency on centralized servers, P2P systems can operate more efficiently, especially in environments with limited connectivity or high bandwidth requirements.
Key Features of IoT P2P
- Decentralized Communication: Devices communicate directly, reducing reliance on central hubs.
- Reduced Latency: Direct communication minimizes delays in data transmission.
- Improved Scalability: P2P systems can handle large numbers of devices without compromising performance.
- Cost-Effective Solutions: Eliminating centralized infrastructure reduces operational expenses.
The Advantages of IoT P2P Technology
IoT P2P technology offers numerous benefits that make it an attractive option for modern connected systems. One of the primary advantages is its ability to reduce latency, which is crucial for applications such as autonomous vehicles, smart grids, and industrial automation. Additionally, P2P systems are more resilient to network failures, as they do not depend on a single point of failure.
Another significant advantage of IoT P2P is its cost-effectiveness. By minimizing the need for centralized infrastructure, organizations can save on operational expenses while maintaining high levels of performance and reliability.
Advantages in Detail
- Lower Latency: Direct communication between devices ensures faster data transmission and real-time responsiveness.
- Improved Scalability: P2P systems can accommodate a growing number of devices without degrading performance, making them ideal for large-scale deployments.
- Enhanced Reliability: Decentralized architecture ensures system resilience, even in the event of network disruptions or failures.
The Building Blocks of IoT P2P Architecture
The architecture of IoT P2P systems is designed to facilitate direct communication between devices. This involves establishing secure connections, managing data exchanges, and ensuring interoperability across different platforms. Key components of IoT P2P architecture include discovery mechanisms, authentication protocols, and data exchange frameworks.
Discovery mechanisms enable devices to locate and identify one another within the network. Authentication protocols ensure secure connections by verifying the identity of devices. Data exchange frameworks define how information is transmitted and processed, ensuring seamless communication between peers.
Read also:Access Iot Device Behind Nat
Components of IoT P2P Architecture
- Node Identification: Each device in the network is assigned a unique identifier for secure communication.
- Peer Discovery: Devices use discovery protocols to find and connect with other devices in the network.
- Secure Communication Channels: Encryption and authentication protocols ensure that data exchanged between devices remains secure and protected from unauthorized access.
Real-World Applications of IoT P2P
IoT P2P technology is already being used in various real-world applications, demonstrating its potential to transform industries. For instance, in smart homes, IoT devices such as thermostats, lighting systems, and security cameras can communicate directly, enabling coordinated actions without the need for a central hub. Similarly, in industrial settings, machines can exchange data and optimize processes in real-time, improving efficiency and productivity.
Example 1: Smart Home Automation
In a smart home environment, IoT P2P connections allow devices to work together seamlessly. For example, when a motion sensor detects movement, it can trigger the lights to turn on without requiring a central server to process the request. This not only speeds up the response time but also reduces the load on the network, enhancing overall performance.
Example 2: Industrial IoT
In industrial applications, IoT P2P technology enables machines to share operational data and adjust their settings dynamically. This leads to improved efficiency, reduced downtime, and enhanced safety. For instance, a manufacturing robot can communicate directly with a quality control system to ensure that products meet the required standards, streamlining the production process.
Overcoming Challenges in IoT P2P
While IoT P2P offers numerous benefits, it also presents several challenges that need to be addressed. One of the primary concerns is security, as decentralized systems can be more vulnerable to attacks if proper safeguards are not implemented. Additionally, managing large-scale P2P networks can be complex, requiring advanced algorithms and protocols to ensure smooth operation.
Another challenge is interoperability, as devices from different manufacturers may use incompatible communication standards. This can hinder the seamless integration of devices within a P2P network. To overcome these challenges, industry standards and best practices need to be established and widely adopted.
Addressing Security Challenges
- Implementing Strong Encryption: Protecting data with robust encryption ensures secure communication between devices.
- Using Secure Authentication Protocols: Verifying the identity of devices within the network prevents unauthorized access and ensures system integrity.
- Regularly Updating Firmware and Software: Keeping devices up to date with the latest security patches helps mitigate vulnerabilities and protect against emerging threats.
Protocols Supporting IoT P2P Communication
Various protocols have been developed to support IoT P2P communication, each with its own strengths and limitations. Some of the most commonly used protocols include MQTT (Message Queuing Telemetry Transport), CoAP (Constrained Application Protocol), and WebSocket.
MQTT is a lightweight protocol designed for low-bandwidth, high-latency networks, making it ideal for IoT applications. CoAP, on the other hand, is specifically designed for resource-constrained devices, enabling efficient communication in environments with limited processing power. WebSocket provides full-duplex communication channels, allowing for real-time data exchange between devices.
Selecting the Right Protocol
Choosing the appropriate protocol depends on the specific requirements of the application. Factors such as network bandwidth, device capabilities, and security needs should be considered when selecting a protocol for IoT P2P communication. Careful evaluation of these factors ensures optimal performance and reliability.
Ensuring Security in IoT P2P Systems
Security is a critical concern in IoT P2P systems, as these networks often handle sensitive data and control critical infrastructure. To ensure the security of IoT P2P connections, several measures can be implemented:
- End-to-End Encryption: Encrypting data during transmission protects it from unauthorized access and ensures confidentiality.
- Device Authentication: Verifying the identity of devices within the network prevents unauthorized access and ensures system integrity.
- Regular Security Audits: Conducting periodic audits helps identify vulnerabilities and address them before they can be exploited by malicious actors.
The Bright Future of IoT P2P
The future of IoT P2P is promising, with advancements in technology paving the way for new possibilities. As more devices become interconnected, the demand for efficient, secure, and scalable communication systems will continue to grow. IoT P2P technology is well-positioned to meet these demands, offering solutions that are both innovative and practical.
Emerging trends such as edge computing and blockchain technology are expected to further enhance the capabilities of IoT P2P systems. Edge computing enables data processing closer to the source, reducing latency and improving performance. Blockchain technology provides a decentralized ledger for secure and transparent transactions, enhancing the trustworthiness of IoT P2P networks.
Steps to Implement IoT P2P Technology
Implementing IoT P2P technology requires careful planning and execution. The following steps can help you get started:
- Define Your Use Case: Identify the specific application for which IoT P2P technology will be used. Clearly outlining your objectives ensures that the implementation aligns with your goals.
- Select the Right Protocol: Choose a protocol that aligns with the requirements of your application, considering factors such as network bandwidth, device capabilities, and security needs.
- Design the Architecture: Develop a robust architecture that ensures secure and efficient communication between devices. This includes defining discovery mechanisms, authentication protocols, and data exchange frameworks.
- Implement Security Measures: Incorporate security features such as encryption and authentication to protect your network from potential threats.
- Test and Optimize: Conduct thorough testing to identify and address any issues before deploying the system. Optimization ensures that the system performs optimally in real-world scenarios.
Conclusion: Embracing the Potential of IoT P2P
The IoT P2P example demonstrates the transformative potential of peer-to-peer communication in reshaping how devices interact and collaborate. By leveraging IoT P2P technology, organizations can create smarter, more efficient systems that meet the demands of modern applications. As the IoT landscape continues to evolve, P2P architecture will play an increasingly important role in shaping the future of connected systems.
We encourage readers to explore the possibilities of IoT P2P technology and consider how it can be applied to their specific needs. Feel free to leave a comment or share this article with others who may find it useful. For more insights into IoT and related technologies, explore our other articles on the site.