In today's highly connected world, establishing remote connectivity for IoT devices behind a router using a Raspberry Pi has become an essential skill for both enthusiasts and professionals. The ability to control and monitor IoT devices from anywhere in the world opens up a universe of possibilities. However, setting up remote access for IoT devices behind a router requires a solid understanding of networking principles, robust security practices, and effective Raspberry Pi configurations.
As smart home automation and remote management solutions continue to gain popularity, the demand for reliable remote connectivity is on the rise. This comprehensive guide dives deep into the intricacies of setting up remote access for IoT devices using a Raspberry Pi, offering step-by-step instructions and expert advice to ensure success.
Whether you're a hobbyist aiming to control your home automation system remotely or a professional implementing advanced IoT solutions, this guide will equip you with the knowledge and tools necessary to achieve secure and efficient remote connectivity.
Read also:Paul Mishkin
Table of Contents
Introduction to Remote IoT Connectivity with Raspberry Pi
Understanding Networking Fundamentals for Remote Access
Configuring Your Raspberry Pi for IoT Deployment
Setting Up Port Forwarding on Your Router
Implementing Dynamic DNS (DDNS) for Consistent Access
Establishing Secure SSH Connections
Read also:Luke Wilson
Enhancing Security for Remote IoT Access
Resolving Common Challenges in Remote Connectivity
Exploring Real-World Applications of Remote IoT Connectivity
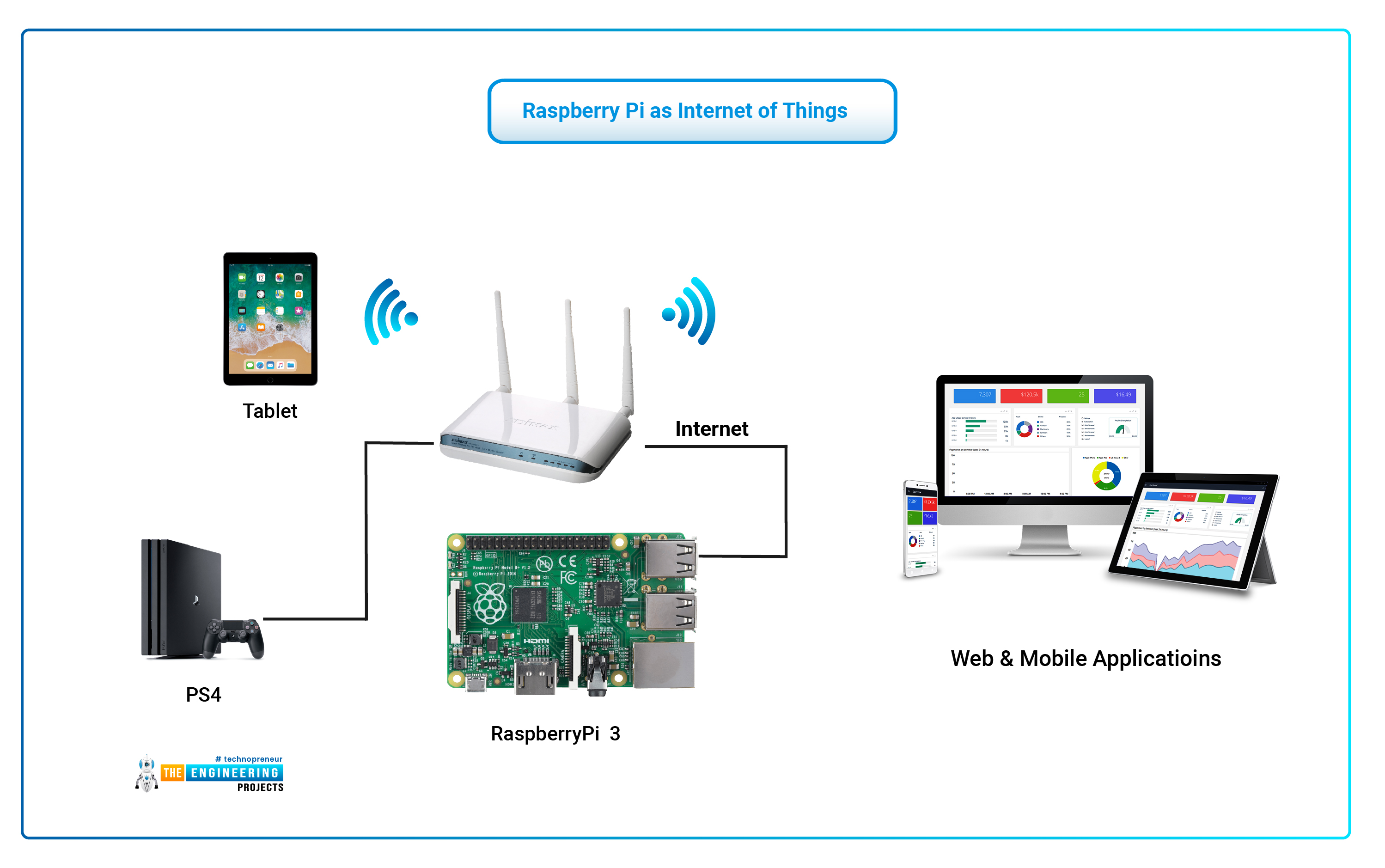
Introduction to Remote IoT Connectivity with Raspberry Pi
Why Remote Access is Essential
In an era where technology permeates every aspect of daily life, remote access to IoT devices has become indispensable. Whether it's monitoring and controlling smart home systems, managing industrial IoT deployments, or facilitating remote health monitoring, the ability to interact with devices from anywhere in the world is transforming how we interact with technology. By leveraging a Raspberry Pi as a central hub, users can create a robust and scalable infrastructure for remote connectivity that is both cost-effective and highly customizable.
However, achieving seamless remote connectivity requires careful planning and meticulous configuration. This section introduces the fundamental concepts and benefits of remote IoT connectivity using a Raspberry Pi, laying the groundwork for more detailed discussions in subsequent sections.
Understanding Networking Fundamentals for Remote Access
Key Networking Concepts You Need to Know
To effectively set up remote access for IoT devices, it's crucial to have a solid understanding of basic networking principles. These include:
- IP addresses and their classification (public vs. private)
- Subnet masks and their role in network segmentation
- Ports and their significance in facilitating communication
- Router functionality, including NAT (Network Address Translation)
These foundational concepts are the building blocks for configuring remote access to IoT devices behind a router, ensuring that data flows smoothly and securely between devices.
Configuring Your Raspberry Pi for IoT Deployment
Preparing Your Raspberry Pi for Optimal Performance
For your Raspberry Pi to serve as a reliable gateway for IoT devices, it must be properly configured. Follow these essential steps:
- Install the latest version of Raspberry Pi OS to ensure compatibility and security.
- Enable SSH (Secure Shell) to allow secure remote access to your Raspberry Pi.
- Assign a static IP address to your Raspberry Pi for consistent and stable connectivity.
- Install necessary software packages and libraries to support IoT communication protocols.
By completing these initial steps, you ensure that your Raspberry Pi is fully prepared to act as a secure and efficient gateway for your IoT devices.
Setting Up Port Forwarding on Your Router
A Step-by-Step Guide to Configuring Port Forwarding
Port forwarding is a critical component of enabling remote access to devices behind a router. Follow these guidelines to configure port forwarding effectively:
- Log in to your router's administration panel using its local IP address.
- Navigate to the port forwarding section and locate the appropriate settings.
- Create rules to forward specific ports to your Raspberry Pi's local IP address.
- Test the configuration thoroughly to confirm that incoming requests are correctly routed.
Properly configured port forwarding ensures that external requests are directed to the correct device within your network, enabling seamless remote access.
Implementing Dynamic DNS (DDNS) for Consistent Access
Why DDNS is Vital for Remote Connectivity
Dynamic DNS (DDNS) allows you to access your home network using a consistent domain name, even if your public IP address changes. This section explains:
- How DDNS simplifies remote access by providing a stable endpoint.
- Popular DDNS providers and their features, including free and paid options.
- Steps to configure DDNS on your router or Raspberry Pi for uninterrupted connectivity.
- Common issues that may arise and how to troubleshoot them effectively.
With DDNS in place, you can maintain reliable access to your IoT devices, regardless of your ISP's dynamic IP assignment policies.
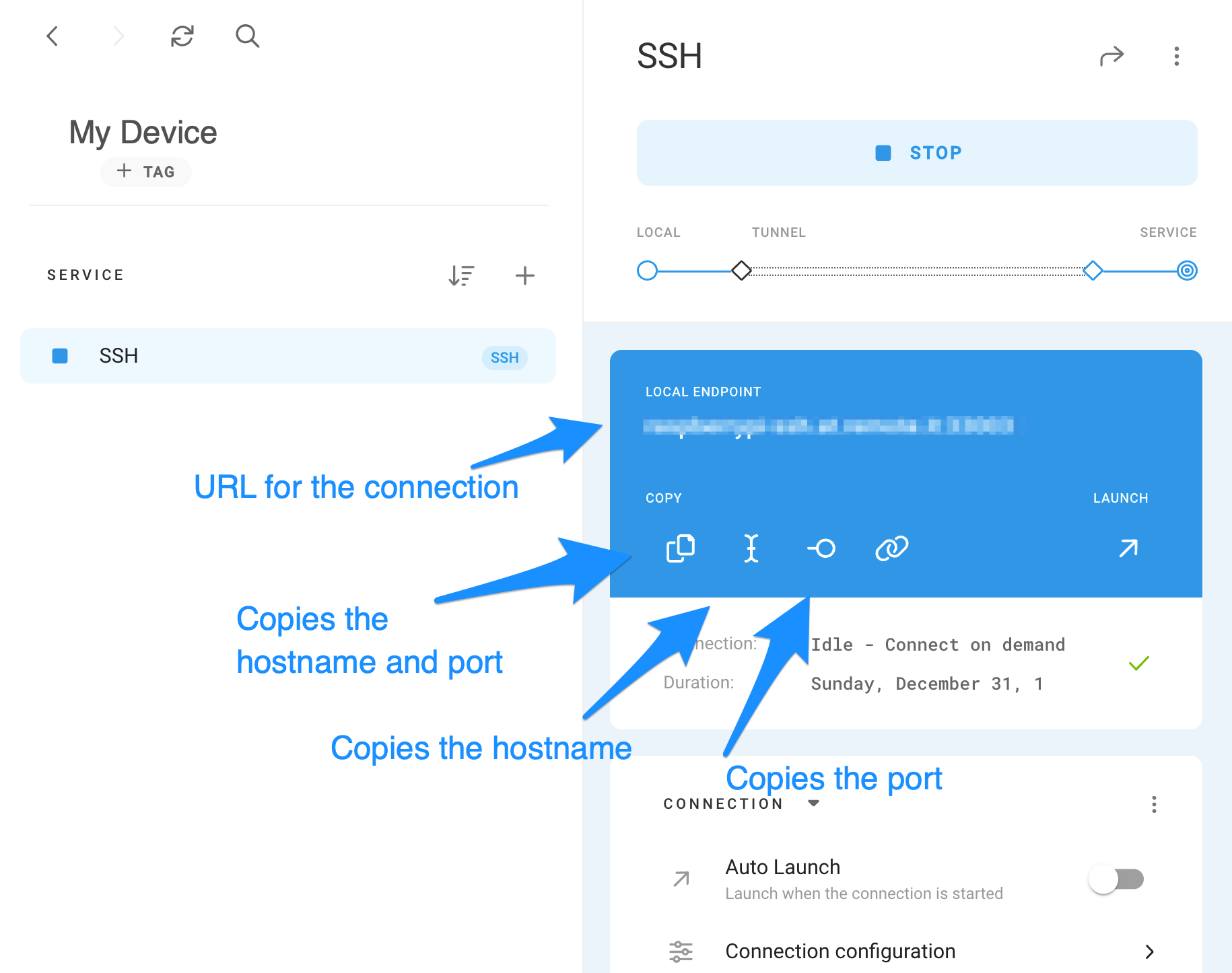
Establishing Secure SSH Connections
Maximizing Security with SSH
SSH (Secure Shell) is the gold standard for secure remote access due to its robust encryption and authentication mechanisms. This section covers:
- Configuring SSH on your Raspberry Pi to enable remote connections.
- Connecting to your Raspberry Pi securely from remote locations using SSH clients.
- Generating and managing SSH keys to enhance security and streamline authentication.
- Best practices for configuring SSH, including disabling password authentication in favor of key-based access.
By leveraging SSH, you can ensure that all communication between your remote device and your IoT network remains secure and private.
Enhancing Security for Remote IoT Access
Protecting Your IoT Network from Threats
Security should always be a top priority when setting up remote access for IoT devices. Consider implementing the following measures:
- Use strong, unique passwords for all devices and accounts to deter brute-force attacks.
- Enable two-factor authentication (2FA) wherever possible to add an extra layer of protection.
- Regularly update software and firmware to patch vulnerabilities and enhance security.
- Monitor network activity for suspicious behavior and act promptly to mitigate potential threats.
These security practices help safeguard your IoT devices and prevent unauthorized access, ensuring the integrity of your remote connectivity setup.
Resolving Common Challenges in Remote Connectivity
Identifying and Addressing Issues Systematically
Even with careful planning, challenges may arise during the setup process. This section addresses common problems and provides solutions:
- Connection timeouts and network unreachable errors due to misconfigured settings.
- Port forwarding issues caused by incorrect rules or conflicting services.
- DDNS resolution failures due to outdated records or service outages.
- SSH authentication errors resulting from improper key configurations or firewall restrictions.
By systematically identifying and resolving these challenges, you can achieve stable and reliable remote connectivity for your IoT devices.
Exploring Real-World Applications of Remote IoT Connectivity
Innovative Use Cases for Remote IoT Solutions
Remote IoT connectivity enables a wide range of practical applications, including:
- Smart home automation systems for enhanced convenience and energy efficiency.
- Industrial IoT solutions for predictive maintenance and optimized operations.
- Remote health monitoring systems for real-time patient care and data analysis.
- Agricultural IoT deployments for precision crop management and resource optimization.
These applications demonstrate the versatility and transformative potential of remote IoT connectivity using a Raspberry Pi, offering solutions that span multiple industries and use cases.
Conclusion and Further Steps
Remote IoT connectivity using a Raspberry Pi represents a powerful approach to managing and monitoring IoT devices from anywhere in the world. By mastering networking fundamentals, configuring your Raspberry Pi effectively, and implementing robust security measures, you can create a reliable and secure remote access system tailored to your needs.
We encourage readers to experiment with the techniques outlined in this guide and explore additional resources to deepen their understanding. Share your experiences, ask questions, and engage with the growing community of IoT enthusiasts. Additionally, consider exploring advanced topics such as cloud-based IoT solutions and advanced networking configurations to further enhance your skills.
For more in-depth information, refer to the following authoritative sources:
Thank you for reading, and we look forward to your contributions to the thriving community of IoT innovators!