Managing IoT devices remotely has become a cornerstone of modern technology. With the growing demand for secure and efficient solutions, setting up a Raspberry Pi-based remote IoT platform without SSH keys offers an innovative approach for enthusiasts, developers, and businesses. This comprehensive guide will walk you through creating a seamless, secure, and cost-effective remote access system for your IoT projects.
In today's rapidly evolving technological landscape, the Internet of Things (IoT) continues to expand, driving the need for reliable and secure remote access solutions. Whether you're a beginner exploring IoT or a seasoned professional, learning how to configure your Raspberry Pi for remote access without SSH keys is a valuable skill. This article will provide step-by-step instructions, practical tips, and insights to help you implement this solution effectively.
As the interest in remote IoT platforms grows, exploring alternatives to traditional SSH key authentication becomes increasingly important. By learning how to set up a Raspberry Pi for remote access without relying on SSH keys, you can simplify your workflow, enhance security, and streamline your IoT projects. Let's delve into the details and discover how to implement this solution effortlessly.
Read also:Does Jonny Lee Miller Have Tattoos
Contents Overview
- Introduction to Remote IoT Platforms
- Overview of Raspberry Pi
- Understanding SSH Key-Free Access
- Setting Up a Remote IoT Platform
- Security Best Practices
- Optimizing Performance
- Troubleshooting Common Issues
- Alternative Solutions
- Use Cases and Applications
- Conclusion
The Role of Remote IoT Platforms in Modern Technology
Remote IoT platforms have transformed the way devices communicate and interact over the internet. These platforms enable users to monitor, control, and manage IoT devices from anywhere in the world, revolutionizing industries ranging from smart homes to industrial automation. Integrating Raspberry Pi into these platforms has further enhanced their capabilities, making them more accessible and versatile.
A remote IoT platform setup without SSH keys provides an innovative alternative to traditional key-based authentication methods. This approach simplifies remote access while maintaining robust security. By eliminating the need for SSH keys, users can reduce the risk of key-related vulnerabilities and streamline their workflow, ensuring a more efficient and secure IoT experience.
Why Raspberry Pi Stands Out in IoT Projects
- Cost-effective and versatile hardware tailored for IoT applications
- Extensive community support and comprehensive documentation for seamless troubleshooting
- Compatibility with a wide range of operating systems and programming languages
- Energy-efficient design perfect for long-term IoT deployments
Exploring the Capabilities of Raspberry Pi
Raspberry Pi is a compact, single-board computer designed for educational purposes and hobbyist projects. Despite its small size, it boasts impressive features that make it ideal for IoT applications. The latest models feature enhanced processing power, expanded memory, and advanced connectivity options, making them suitable for both simple and complex IoT setups.
Key Features of Raspberry Pi
- Quad-core processors for superior performance in demanding applications
- Multiple GPIO pins for seamless integration with sensors, actuators, and other peripherals
- Built-in Wi-Fi and Bluetooth capabilities for wireless connectivity
- Support for diverse operating systems, including Raspbian, Ubuntu, and others
The Advantages of SSH Key-Free Access
SSH (Secure Shell) is a widely used protocol for securely connecting to remote devices. Traditionally, SSH relies on key-based authentication to ensure secure access. However, setting up a remote IoT platform without SSH keys involves configuring alternative authentication methods, such as password-based or certificate-based authentication. This approach simplifies the setup process while maintaining a high level of security.
Benefits of SSH Key-Free Access
- Eliminates the need for managing and distributing SSH keys
- Reduces the risk of unauthorized access through stolen or compromised keys
- Streamlines the setup process, making it more accessible for beginners
A Step-by-Step Guide to Setting Up Your Remote IoT Platform
Configuring a remote IoT platform without SSH keys on a Raspberry Pi involves several essential steps. Follow this detailed guide to ensure a successful setup:
Step 1: Install the Operating System
Begin by installing the desired operating system on your Raspberry Pi. Raspbian is a popular choice due to its user-friendly interface and extensive support. Refer to the official Raspberry Pi documentation for detailed installation instructions.
Read also:Yang Yang Wife
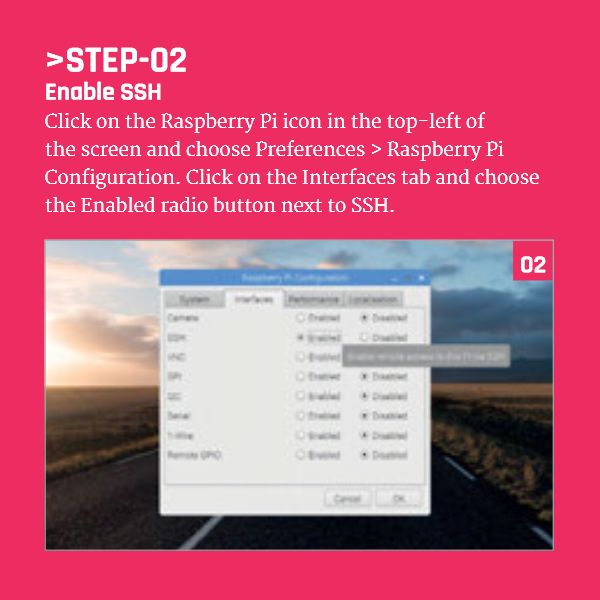
Step 2: Enable SSH
SSH must be enabled on your Raspberry Pi to allow remote access. This can be done through the Raspberry Pi Configuration tool or by creating an empty file named "ssh" on the boot partition. Ensure that SSH is properly configured before proceeding.
Step 3: Configure Authentication
Instead of using SSH keys, configure your Raspberry Pi to use password-based authentication. Create a strong, unique password to prevent unauthorized access. Consider implementing additional security measures, such as two-factor authentication, for enhanced protection.
Step 4: Set Up Port Forwarding
If your Raspberry Pi is connected to a local network, you may need to configure port forwarding on your router to enable external access. Consult your router's documentation for specific instructions and ensure that the correct IP address and port number are specified.
Prioritizing Security in Your IoT Setup
While a remote IoT platform without SSH keys simplifies access, security should always remain a top priority. Implement the following best practices to safeguard your Raspberry Pi from potential threats:
1. Use Strong Passwords
Create complex passwords that include a mix of uppercase and lowercase letters, numbers, and special characters. Avoid using easily guessable information, such as birthdays or common words, to enhance security.
2. Enable Firewall Protection
Configure a firewall to restrict unauthorized access to your Raspberry Pi. Tools like UFW (Uncomplicated Firewall) or iptables can help you implement robust firewall rules tailored to your specific needs.
3. Regularly Update Software
Keep your operating system and applications up to date to ensure you have the latest security patches and improvements. Regular updates help protect your Raspberry Pi from emerging threats and vulnerabilities.
Maximizing the Performance of Your Remote IoT Platform
To ensure your remote IoT platform operates efficiently, consider the following optimization techniques:
1. Monitor Resource Usage
Utilize tools like htop or top to monitor CPU, memory, and disk usage on your Raspberry Pi. Identify and terminate unnecessary processes to free up resources and improve overall performance.
2. Fine-Tune Network Settings
Adjust network settings to enhance data transfer speeds and reduce latency. This may involve tweaking MTU values, enabling jumbo frames, or optimizing routing configurations for better performance.
3. Implement Caching Mechanisms
Use caching to store frequently accessed data, reducing the load on your Raspberry Pi and improving response times. Implementing caching mechanisms can significantly enhance the efficiency of your IoT platform.
Addressing Common Issues During Setup
Encountering challenges during the setup process is not uncommon. Below are some common problems and their solutions:
Problem 1: Unable to Connect via SSH
Solution: Verify that SSH is enabled and check your router's port forwarding settings. Ensure that the IP address and port number are correct and accessible from external networks.
Problem 2: Slow Performance
Solution: Analyze resource usage and optimize your Raspberry Pi's configuration. Consider upgrading hardware components, such as memory or storage, if necessary to improve performance.
Exploring Alternative Solutions
While a remote IoT platform without SSH keys is a practical solution, there are other methods worth exploring:
1. Cloud-Based Platforms
Services like AWS IoT Core and Microsoft Azure IoT Hub offer robust solutions for managing IoT devices. These platforms provide advanced features, including device management, analytics, and seamless integration with other services.
2. Third-Party Applications
Applications like BalenaCloud and Resin.io simplify the deployment and management of IoT devices. They offer user-friendly interfaces and extensive documentation, making them ideal for users of all skill levels.
Real-World Applications of Remote IoT Platforms
A remote IoT platform without SSH keys on a Raspberry Pi has numerous applications across various industries. Below are some examples:
1. Home Automation
Control smart home devices, such as lights, thermostats, and security systems, remotely using your Raspberry Pi. Create a centralized hub for managing all your smart home devices effortlessly.
2. Environmental Monitoring
Deploy sensors to monitor environmental factors like temperature, humidity, and air quality in real-time. Transmit the collected data to your Raspberry Pi for analysis and visualization, enabling informed decision-making.
3. Industrial Automation
Use Raspberry Pi to manage industrial processes, collecting data from machines and optimizing operations for increased efficiency. Implement predictive maintenance and automation to enhance productivity and reduce downtime.
Empowering Your IoT Projects with Secure, Efficient Remote Access
Setting up a remote IoT platform without SSH keys on a Raspberry Pi offers a practical and secure solution for managing IoT devices. By following the steps outlined in this guide, you can create a tailored system that meets your specific needs and simplifies your workflow.
We invite you to share your experiences and feedback in the comments section below. Your insights will help us improve and provide valuable information to other readers. For more articles on IoT and Raspberry Pi, explore our website and stay updated on the latest trends and technologies.
Remember, securing your IoT devices is essential. Always prioritize security measures to protect your data and ensure the integrity of your projects. Happy tinkering and innovation!