Are you facing challenges with your RemoteIoT platform SSH key not working? If you're struggling to establish a secure connection, you're not alone. Many users encounter difficulties when configuring SSH keys for remote access. This article provides a detailed, step-by-step guide to help you troubleshoot and resolve the problem effectively.
SSH (Secure Shell) is a cryptographic network protocol that ensures secure communication between a client and a server. In the context of the RemoteIoT platform, SSH keys are indispensable for enabling secure and seamless remote access. However, when these keys fail to function correctly, it can disrupt your workflow and cause frustration.
This article delves into the underlying causes of SSH key failures, offers practical solutions, and provides expert advice to ensure smooth operation. Whether you're a beginner or an experienced user, this guide equips you with the knowledge to address and resolve SSH key issues efficiently.
Read also:Wes Bentley
Table of Contents
- Understanding SSH and Its Role
- Common Challenges with RemoteIoT Platform SSH Keys
- Step-by-Step Troubleshooting Process
- Best Practices for Managing SSH Keys
- Enhancing Security for SSH Key Usage
- Advanced Techniques for SSH Configuration
- Frequently Asked Questions
- Real-World Case Studies
- Essential Tools and Resources
- Conclusion and Next Steps
Understanding SSH and Its Role
SSH (Secure Shell) is a protocol that encrypts data transmitted over a network, ensuring secure communication between devices. In the RemoteIoT platform, SSH keys act as a digital identity for authentication, replacing traditional password-based logins. This method significantly enhances security by minimizing the risk of unauthorized access.
The RemoteIoT platform SSH key plays a critical role in maintaining the integrity and confidentiality of your IoT devices. By utilizing SSH keys, you can establish secure connections without repeatedly entering passwords, streamlining your workflow and improving efficiency.
Having a foundational understanding of SSH and its integration with the RemoteIoT platform is essential for troubleshooting issues related to SSH key functionality. Let's explore the common problems users encounter and how to address them effectively.
Common Challenges with RemoteIoT Platform SSH Keys
Identifying SSH Key Failures
When the RemoteIoT platform SSH key fails to work, it can stem from several factors. Below are some of the most prevalent issues:
- Incorrect Key Permissions: SSH keys require specific file permissions to function correctly. Improper permissions can lead to authentication failures, preventing secure access to your devices.
- Corrupted Key Files: Damaged or incomplete SSH key files can prevent successful authentication, disrupting your ability to connect to the platform.
- Server Configuration Errors: Misconfigured SSH server settings can block key-based authentication, making it impossible to establish a secure connection.
- Network Issues: Connectivity problems or firewall restrictions can interfere with the SSH connection process, leading to frustrating delays or failed attempts.
Identifying the root cause of the problem is the first step toward resolving it. Let's proceed with a detailed troubleshooting guide to address these challenges systematically.
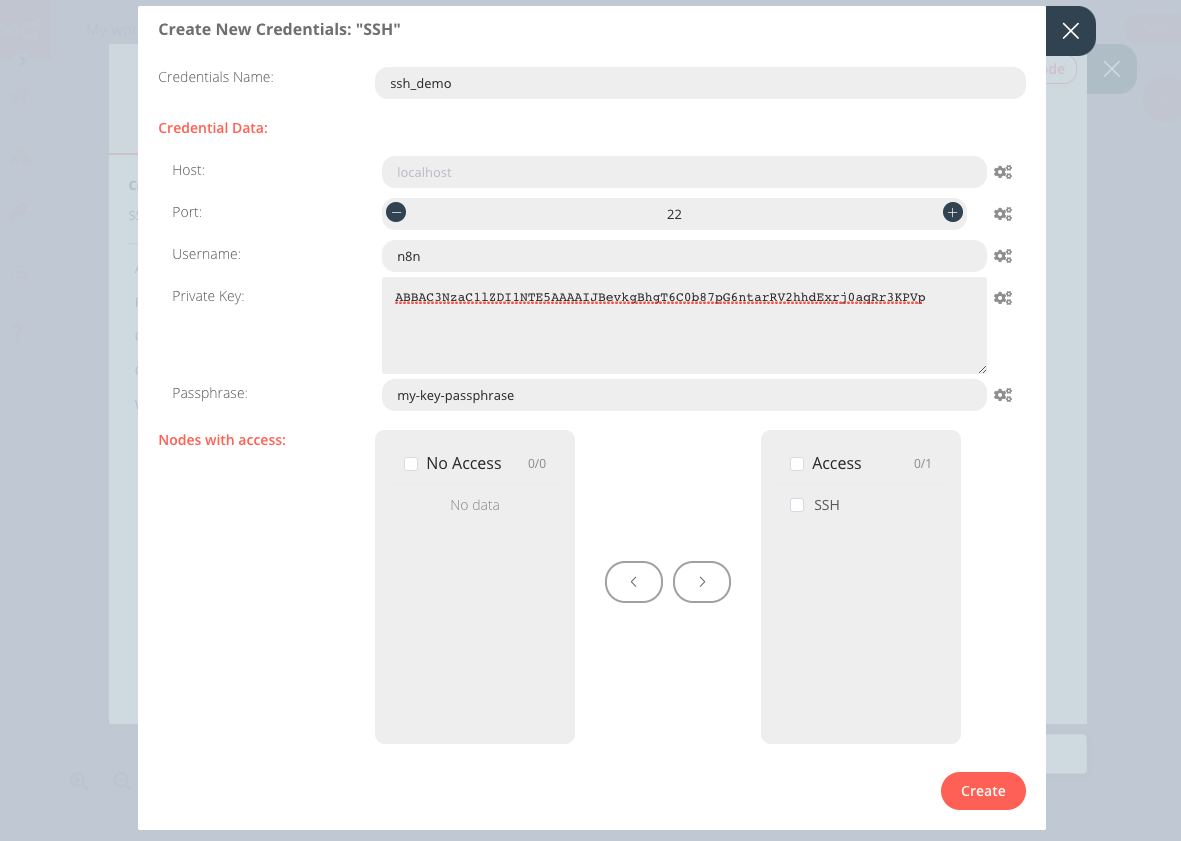
Step-by-Step Troubleshooting Process
Verifying Key Permissions
To ensure proper functionality, SSH key files must have the correct permissions. Follow these steps:
Read also:Mamitha Baiju Age
- Check the file permissions of your private key using the command:
ls -l ~/.ssh/id_rsa. - Ensure the permissions are set to 600 by running:
chmod 600 ~/.ssh/id_rsa.
Testing the SSH Connection
Before diving into advanced troubleshooting, manually test the SSH connection:
- Use the command:
ssh -v username@hostnameto enable verbose output, which helps identify potential issues. - Review error messages or warnings that indicate the source of the problem, allowing you to take corrective actions.
These steps will help you pinpoint the exact issue and guide you toward resolving it effectively.
Best Practices for Managing SSH Keys
Implementing best practices for SSH key management can prevent future issues and enhance security:
- Use Strong Passphrases: Protect your private keys with robust passphrases to add an extra layer of security, making unauthorized access more difficult.
- Limit Key Usage: Restrict SSH key access to specific users and devices to minimize risks and ensure that only authorized individuals can access sensitive systems.
- Regularly Rotate Keys: Periodically update SSH keys to maintain ongoing security and reduce the likelihood of compromised keys affecting your system.
By adopting these practices, you can resolve current issues and safeguard your RemoteIoT platform against future vulnerabilities.
Enhancing Security for SSH Key Usage
Disabling Password Authentication
To enhance security, disable password-based authentication and rely solely on SSH keys:
- Edit the SSH configuration file:
/etc/ssh/sshd_config. - Set the parameter
PasswordAuthentication noto enforce key-based authentication. - Restart the SSH service:
systemctl restart sshdto apply the changes and ensure the new settings take effect.
Using SSH Agents
SSH agents simplify key management by securely storing private keys and handling authentication automatically. Tools like ssh-agent and ssh-add streamline your workflow, reducing the need for repetitive authentication processes.
Advanced Techniques for SSH Configuration
Customizing SSH Key-Based Authentication
For advanced users, customizing SSH settings can optimize performance and security:
- Specify custom port numbers in the SSH configuration file to avoid common attack vectors, making it harder for malicious actors to target your system.
- Implement fail2ban or similar tools to block repeated unauthorized access attempts, adding an additional layer of protection against brute-force attacks.
These techniques require a deeper understanding of SSH protocols but offer significant benefits in terms of security and efficiency.
Frequently Asked Questions
Why Is My RemoteIoT Platform SSH Key Not Working?
This issue can arise due to incorrect key permissions, corrupted key files, or misconfigured server settings. Follow the troubleshooting steps outlined earlier to identify and resolve the problem systematically.
How Do I Generate a New SSH Key Pair?
Use the following command to generate a new SSH key pair:
ssh-keygen -t rsa -b 4096 -C "your_email@example.com"
Follow the prompts to create and save your new keys, ensuring they meet the required security standards.
Real-World Case Studies
Case Study 1: Incorrect Key Permissions
A user encountered the RemoteIoT platform SSH key not working issue due to improper file permissions. After resetting the permissions to 600, the problem was resolved immediately, restoring secure access to their devices.
Case Study 2: Server Configuration Errors
Another user faced difficulties due to misconfigured SSH server settings. By restoring the default configuration and enabling key-based authentication, the issue was successfully addressed, ensuring smooth and secure connections.
Essential Tools and Resources
Several tools and resources can assist in managing SSH keys effectively:
- OpenSSH: A widely used SSH implementation that provides robust security features and extensive documentation to support users at all levels.
- SSH Keychain: A utility for managing SSH keys across multiple devices, simplifying the process of maintaining secure access across various systems.
- SSH Config Generator: An online tool for creating custom SSH configuration files, enabling users to tailor their settings for optimal performance and security.
Referencing authoritative sources like the OpenSSH documentation and official RemoteIoT platform guides can provide additional insights and solutions, empowering you to address complex challenges effectively.
Conclusion and Next Steps
In conclusion, resolving the RemoteIoT platform SSH key not working issue requires a systematic and methodical approach to troubleshooting and resolution. By following the steps and best practices outlined in this guide, you can ensure smooth and secure operation of your SSH connections, enhancing both productivity and security.
We encourage you to share your experiences and solutions in the comments section below. Additionally, explore other articles on our site for more insights into IoT security and SSH management. Together, we can create a safer and more efficient digital environment for everyone.