Establishing secure communication between remote IoT devices using a Virtual Private Cloud (VPC) is an essential task for both businesses and hobbyists. As the world becomes increasingly reliant on smart devices and automation, safeguarding sensitive data and maintaining operational integrity is more important than ever. This comprehensive guide focuses on securely connecting remote IoT devices via VPC using Raspberry Pi, a flexible and cost-efficient platform favored by IoT enthusiasts and professionals alike.
In today's highly interconnected world, IoT devices are deployed in various locations, necessitating robust network security measures. Without proper protection, these devices are vulnerable to cyber threats, which can lead to data breaches and system failures. Understanding how to establish secure connections between IoT devices and a VPC is crucial for anyone working in this rapidly evolving field. This guide will walk you through the process, ensuring you gain the knowledge and tools needed to implement a secure IoT VPC configuration tailored to your specific requirements.
This article will provide a step-by-step approach to setting up and configuring a secure connection between remote IoT devices and a VPC using Raspberry Pi. By the end of this guide, you will have the skills and confidence to deploy a secure IoT infrastructure that meets your needs and protects your data.
Read also:Granblue Fantasy Relink Crossplay
Table of Contents
- Introduction
- Raspberry Pi Overview
- IoT VPC Basics
- Why Secure Connection Matters
- Setting Up Raspberry Pi
- VPC Configuration
- Connecting IoT Devices
- Security Best Practices
- Troubleshooting
- Conclusion
Understanding Raspberry Pi
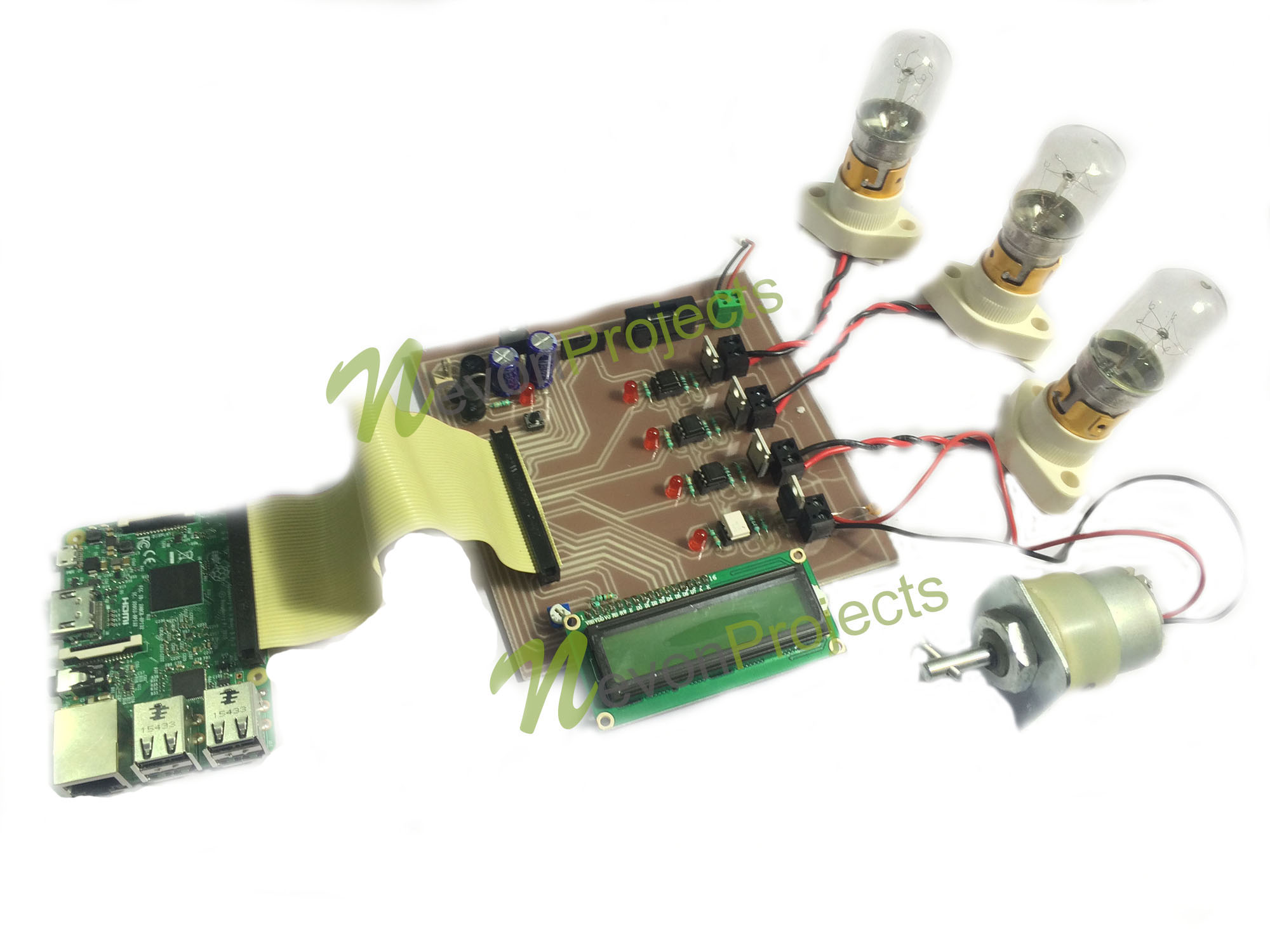
Raspberry Pi is a compact, affordable computer that has become a favorite among developers, hobbyists, and educators. It serves as an excellent platform for learning programming, experimenting with hardware, and building IoT projects. With a range of models offering varying specifications, the Raspberry Pi is versatile enough to cater to diverse use cases.
When it comes to securely connecting remote IoT devices via VPC, the Raspberry Pi can function as a gateway, facilitating communication between IoT devices and the cloud. Its small size, low power consumption, and extensive community support make it an ideal choice for IoT applications, enabling seamless integration and management of devices.
Key Features of Raspberry Pi
- Compact and lightweight design, perfect for portable and space-constrained environments.
- Support for multiple operating systems, offering flexibility in software development.
- GPIO pins for interfacing with hardware components, enhancing its functionality.
- Built-in Wi-Fi and Bluetooth capabilities for wireless connectivity.
- Cost-effective and energy-efficient, making it a practical choice for long-term IoT projects.
Exploring IoT VPC Fundamentals
A Virtual Private Cloud (VPC) is a virtual network dedicated to your cloud environment, allowing you to launch resources in a logically isolated section of the cloud. In the context of IoT, VPC plays a critical role in ensuring secure and reliable communication between devices and the cloud. By leveraging VPC, organizations can control access to their IoT devices, manage traffic flow, and protect sensitive data.
VPC setups are particularly valuable for organizations deploying IoT devices in remote locations where security risks are higher. With VPC, you can isolate your IoT devices from the public internet, reducing the chances of unauthorized access and ensuring data privacy.
Advantages of Using VPC for IoT
- Enhanced security through network isolation, minimizing the risk of cyberattacks.
- Granular control over device access, allowing precise management of permissions.
- Scalability to accommodate growing IoT fleets, ensuring your infrastructure can evolve with your needs.
- Integration with cloud services for advanced data processing and analytics, enabling smarter decision-making.
The Importance of Secure Connections in IoT
In the rapidly expanding realm of IoT, security must be a top priority. With billions of connected devices exchanging data, the potential for cyberattacks is significant. Hackers can exploit vulnerabilities in IoT networks to gain unauthorized access, steal sensitive information, or disrupt operations. These risks highlight the critical need for secure connections in IoT environments.
Securing remote IoT VPC connections is essential to mitigate these risks. By implementing robust security measures, you can protect your devices, preserve data integrity, and ensure the reliability of your IoT infrastructure. A well-secured network not only safeguards your data but also enhances the overall efficiency and trustworthiness of your IoT ecosystem.
Read also:Park Bo Gum And Kim Yoo Jung Relationship
Preparing Your Raspberry Pi
Before you can establish secure connections between remote IoT devices and a VPC, you need to set up your Raspberry Pi. This involves installing the necessary software, configuring network settings, and preparing the device for IoT applications. Proper setup is crucial to ensure smooth communication and optimal performance.
Step-by-Step Raspberry Pi Setup
- Download the latest Raspberry Pi OS from the official website, ensuring you have the most up-to-date version.
- Use a reliable tool like Balena Etcher to flash the OS image onto an SD card, ensuring a stable and error-free installation.
- Insert the SD card into your Raspberry Pi and power it on, allowing the system to boot for the first time.
- Connect to Wi-Fi or Ethernet and update the system using the terminal, ensuring all packages and drivers are current.
- Install essential packages for IoT communication, such as MQTT or SSH, to enable secure and efficient data exchange.
Configuring Your VPC
With your Raspberry Pi ready, the next step is to configure the VPC. This involves setting up subnets, security groups, and routing rules to ensure secure communication between IoT devices and the cloud. Configuring your VPC correctly is vital for maintaining the security and reliability of your IoT infrastructure.
Using a cloud provider like AWS, you can create a VPC tailored to your IoT needs. This includes defining IP address ranges, enabling DNS resolution, and configuring network ACLs to control traffic flow and enhance security.
Configuring Security Groups
Security groups act as virtual firewalls for your VPC, controlling inbound and outbound traffic to your IoT devices. By setting up rules that allow only necessary traffic, you can significantly enhance the security of your IoT network. Carefully configuring security groups ensures that only authorized devices and users can access your network, reducing the risk of unauthorized access and data breaches.
Connecting Your IoT Devices
With your Raspberry Pi and VPC configured, it's time to connect your IoT devices. This process involves registering devices, setting up communication protocols, and ensuring secure data transfer. Proper device management is essential for maintaining the integrity and efficiency of your IoT network.
Popular IoT communication protocols include MQTT, CoAP, and HTTP. Depending on your specific use case, you can choose the protocol that best suits your needs. Additionally, implementing encryption and authentication mechanisms is crucial to safeguard your IoT data and prevent unauthorized access.
Tips for Efficient IoT Device Management
- Utilize device management platforms for centralized control, simplifying the monitoring and maintenance of your IoT fleet.
- Monitor device performance and health in real-time, enabling proactive identification and resolution of issues.
- Regularly update firmware to address security vulnerabilities and ensure your devices are equipped with the latest protections.
- Implement failover mechanisms to ensure continuity in case of network disruptions or device failures.
Enhancing Security with Best Practices
While establishing secure connections between remote IoT devices and VPC using Raspberry Pi is a significant step toward protecting your devices, it's essential to follow additional security best practices. These practices help fortify your IoT infrastructure against potential threats and ensure its long-term reliability and resilience.
Key security measures include using strong, unique passwords, enabling two-factor authentication, and regularly auditing your network for vulnerabilities. Staying vigilant and proactive in your security efforts is crucial to maintaining a secure IoT environment.
Data Encryption and Authentication
Data encryption is vital for protecting sensitive information transmitted between IoT devices and the cloud. By encrypting data both at rest and in transit, you can prevent unauthorized access and data breaches. Additionally, implementing robust authentication mechanisms ensures that only authorized devices and users can access your IoT network, adding an extra layer of security to your infrastructure.
Addressing Common Challenges
Even with careful planning and implementation, challenges may arise when setting up a secure IoT VPC connection. Common issues include network connectivity problems, device registration failures, and configuration errors. Understanding how to troubleshoot these challenges is essential for maintaining a reliable and secure IoT infrastructure.
Common Issues and Solutions
- Network Connectivity: Check your router settings to ensure proper IP assignment and resolve any network-related issues.
- Device Registration: Verify device credentials and re-register devices if necessary to ensure they are correctly integrated into your network.
- Configuration Errors: Review configuration files carefully and correct any syntax mistakes to ensure your setup functions as intended.
Final Thoughts
Securing remote IoT VPC connections using Raspberry Pi is a crucial step in building a robust and reliable IoT infrastructure. By following the steps outlined in this guide, you can ensure your devices are protected from cyber threats and operate efficiently, contributing to the success of your IoT projects.
We encourage you to share your experiences and insights in the comments section below. Additionally, feel free to explore other articles on our site for more information on IoT security and best practices. Together, let's work toward creating a safer and smarter connected world!
Data sources: AWS VPC Documentation, Raspberry Pi Official Documentation, Microsoft Security Best Practices.