In the era of global connectivity, establishing secure remote IoT peer-to-peer (P2P) connections has become a cornerstone for managing devices effectively across vast distances. As technology continues to evolve, the demand for efficient, secure, and budget-friendly P2P solutions has surged. Whether you’re an amateur enthusiast or a seasoned professional, understanding how to set up secure IoT connections on platforms like Raspberry Pi is vital for preserving both privacy and functionality.
Integrating remote IoT devices with P2P technology brings a multitude of benefits, such as minimizing server reliance, boosting security, and ensuring smooth device communication. This comprehensive guide will delve into the most effective methods for setting up secure IoT P2P connections on Raspberry Pi. The goal is to create a robust and reliable setup that doesn’t strain your budget.
By the conclusion of this article, you will have acquired practical knowledge on downloading and configuring secure IoT P2P connections on Raspberry Pi. Additionally, you’ll gain insights into optimizing performance and ensuring data security. Let’s embark on this journey to unlock the full potential of IoT connectivity while prioritizing security and cost-effectiveness.
Read also:Mamitha Baiju Age
Table of Contents
- Introduction to Secure IoT Connections
- Understanding Raspberry Pi Basics
- Why Secure IoT Connections Are Crucial
- Overview of P2P Technology
- Free Solutions for Remote IoT Connectivity
- Step-by-Step Setup Guide for Raspberry Pi
- Security Best Practices for IoT Devices
- Optimizing Performance on Raspberry Pi
- Troubleshooting Common Issues
- Future Trends in Secure IoT P2P
Introduction to Secure IoT Connections
The Internet of Things (IoT) has revolutionized the way we interact with devices, fostering seamless communication between machines and humans. However, as the number of interconnected devices grows, the significance of secure connections becomes increasingly critical. Secure remote IoT P2P solutions provide a dependable framework for safeguarding data integrity and privacy.
What Is IoT?
IoT refers to a network of physical objects equipped with sensors, software, and connectivity capabilities, enabling them to exchange data with other devices and systems over the internet. This interconnected ecosystem powers a wide range of applications, from smart homes to sophisticated industrial automation systems.
Why Security Is Paramount
Without adequate security measures, IoT devices can become vulnerable to cyberattacks, leading to data breaches and unauthorized access. Implementing secure IoT P2P solutions ensures that your devices remain protected while maintaining peak functionality.
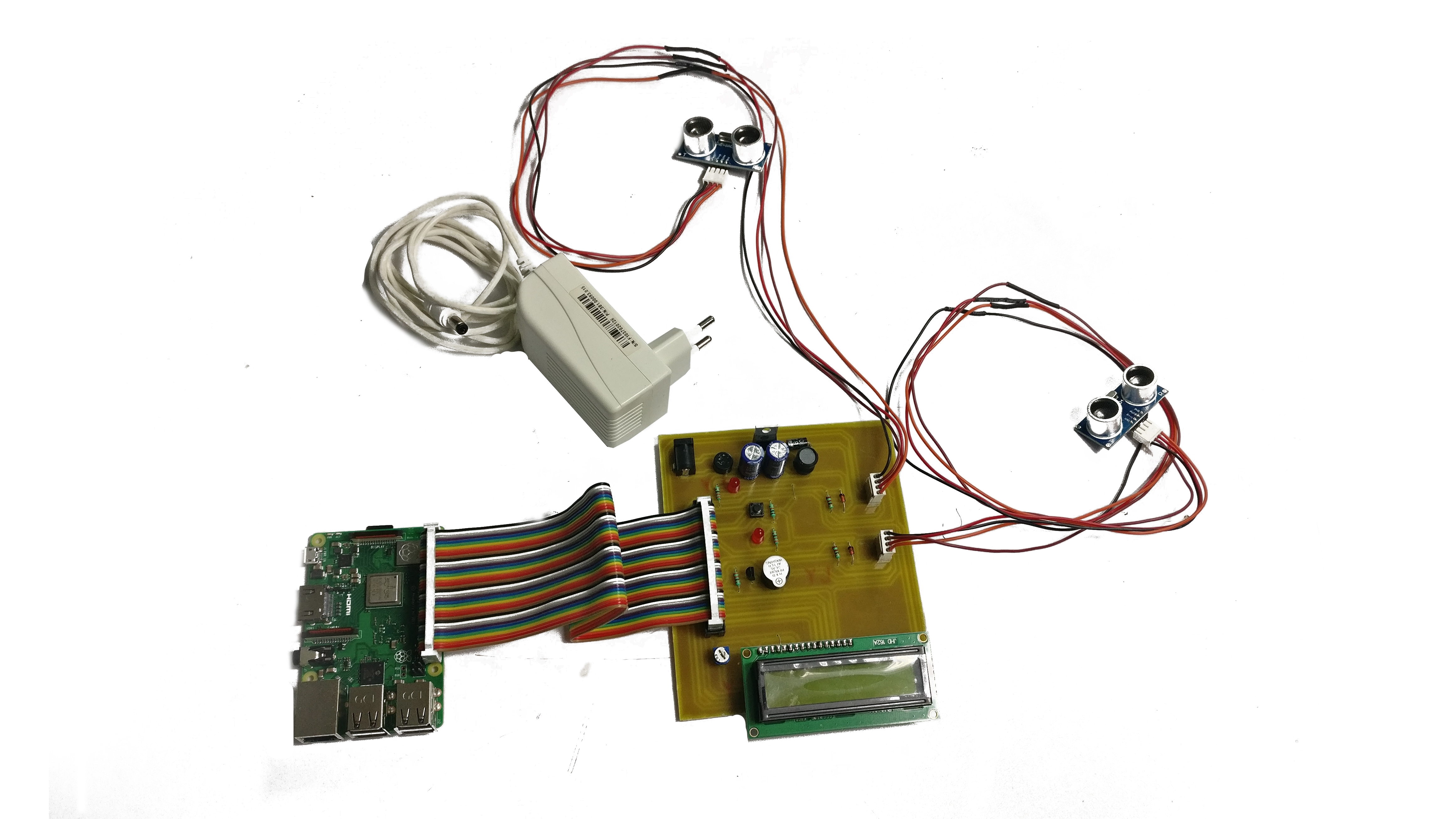
Understanding Raspberry Pi Basics
Raspberry Pi is a highly versatile single-board computer widely utilized for a variety of applications, ranging from home automation to advanced robotics. Its affordability and adaptability make it an excellent platform for establishing secure IoT P2P connections.
Key Features of Raspberry Pi
- Compact size with minimal power consumption
- Compatibility with multiple operating systems
- Extensive community support and resources
- Integration with a wide array of hardware peripherals
Why Secure IoT Connections Are Crucial
As the number of IoT devices continues to expand, so does the likelihood of security breaches. Secure remote IoT P2P solutions address these concerns by integrating robust encryption protocols and authentication mechanisms.
Risks Associated with Insecure Connections
Insecure IoT connections can lead to several serious issues, including:
Read also:Manish Dayal Opleiding
- Data theft and invasion of privacy
- Unauthorized access to devices
- Network disruptions and system downtime
Advantages of Secure Connections
Implementing secure connections offers numerous benefits, such as:
- Enhanced protection of sensitive data
- Improved reliability of devices
- Reduced vulnerability to cyberattacks
Overview of P2P Technology
Peer-to-peer (P2P) technology facilitates direct communication between devices without the need for centralized servers. This decentralized approach enhances efficiency and reduces latency, making it particularly suitable for IoT applications.
How P2P Functions
P2P networks operate by enabling devices to function as both clients and servers, allowing them to share resources and data directly. This eliminates the need for intermediaries, thereby improving overall system performance.
Benefits of P2P in IoT
- High scalability and flexibility
- Cost efficiency
- Enhanced resilience against network failures
Free Solutions for Remote IoT Connectivity
Several free solutions are available for setting up secure IoT P2P connections on Raspberry Pi. These tools offer robust features without requiring any financial investment.
Popular Tools
- MQTT: A lightweight messaging protocol ideal for IoT applications
- WebRTC: A P2P communication framework supporting real-time data exchange
- ZeroTier: A virtual network layer enabling secure and seamless device connectivity
Selecting the Right Solution
Choosing the appropriate tool depends on your specific needs, such as device compatibility, data transfer speed, and security features. Evaluating these factors will help you determine the best option for your project.
Step-by-Step Setup Guide for Raspberry Pi
Establishing secure IoT P2P connections on Raspberry Pi involves several key steps. Follow this comprehensive guide to ensure a successful implementation.
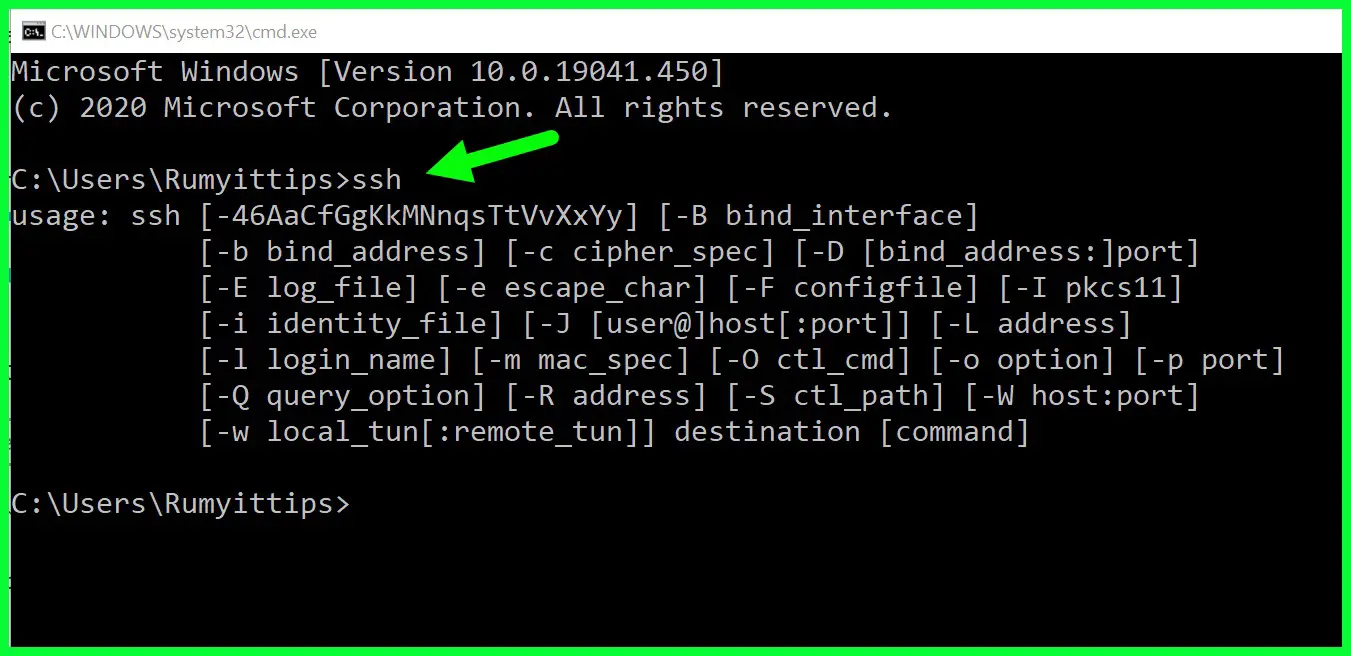
Step 1: Install Raspberry Pi OS
Begin by installing the latest version of Raspberry Pi OS on your device. This operating system serves as the foundation for running IoT applications and configuring P2P connections.
Step 2: Configure Network Settings
Ensure your Raspberry Pi is connected to a stable network. Properly configure network settings to enable seamless communication between devices.
Step 3: Install Required Software
Download and install the necessary software for your chosen P2P solution. Refer to the official documentation for detailed installation instructions.
Step 4: Secure Your Connection
Implement encryption protocols and authentication mechanisms to fortify your IoT P2P connection. Regularly update your software to address potential vulnerabilities.
Security Best Practices for IoT Devices
Adopting best practices for IoT security ensures your devices remain protected against potential threats. Follow these guidelines to enhance your system's security.
Regular Updates
Keep your software and firmware up to date to benefit from the latest security patches and enhancements.
Strong Authentication
Utilize strong passwords and multi-factor authentication to prevent unauthorized access to your devices.
Network Segmentation
Segment your network to isolate IoT devices from critical systems, thereby minimizing the impact of potential breaches.
Optimizing Performance on Raspberry Pi
Optimizing performance on Raspberry Pi is essential for maintaining efficient IoT P2P connections. Follow these tips to maximize your device's capabilities.
Resource Management
Monitor resource usage and allocate resources efficiently to prevent bottlenecks and ensure smooth operation.
Software Optimization
Adjust your software settings to improve performance and reduce latency in data transfer.
Troubleshooting Common Issues
Encountering issues during setup is a common occurrence. Use this troubleshooting guide to resolve common problems swiftly.
Connection Problems
Verify network settings and ensure all devices are properly connected. Restart your Raspberry Pi if necessary.
Software Errors
Refer to the official documentation or community forums for solutions to software-related issues. Reinstalling the software may also resolve persistent problems.
Future Trends in Secure IoT P2P
The future of secure IoT P2P technology is promising, driven by advancements in encryption, artificial intelligence, and edge computing.
Emerging Technologies
Innovations such as blockchain and quantum encryption are expected to play pivotal roles in enhancing IoT security in the years to come.
Industry Adoption
As more industries embrace IoT solutions, the demand for secure P2P connections will continue to grow, spurring further development and refinement of existing technologies.
Conclusion
Secure remote IoT P2P solutions provide a powerful and cost-effective means of managing IoT devices across distances. By following the steps outlined in this guide, you can establish a secure and efficient IoT P2P connection on Raspberry Pi, ensuring your devices remain protected and functional.
We invite you to share your thoughts and experiences in the comments section below. Additionally, explore our other articles for more insights into IoT and related technologies. Together, let’s build a safer and more interconnected world!