In today's highly interconnected world, establishing secure connections for remote IoT devices using P2P (Peer-to-Peer) protocols has become an indispensable skill. Whether you're a hobbyist or a professional developer, understanding how to configure a Raspberry Pi for secure remote access is essential. This guide will provide you with a step-by-step approach to securely connecting remote IoT devices using P2P protocols on Raspberry Pi, including downloading the necessary software and ensuring robust security measures.
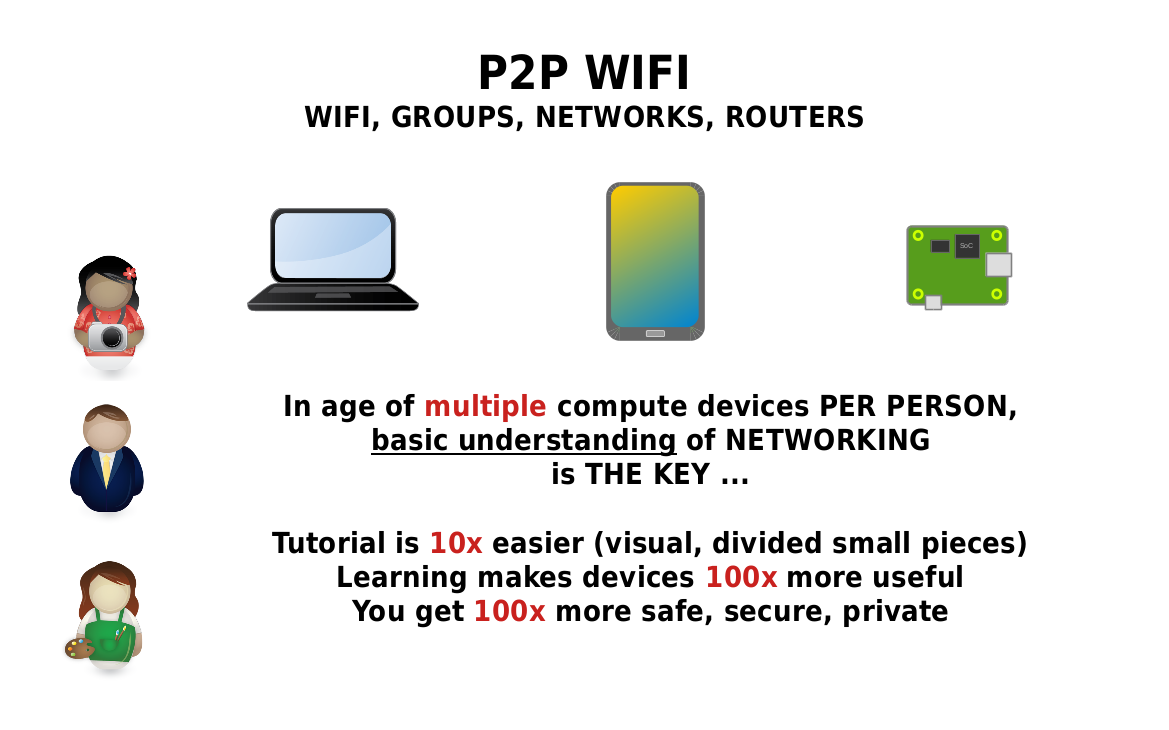
As the Internet of Things (IoT) continues to expand, the number of connected devices is increasing exponentially, making security a top priority. The Raspberry Pi, known for its affordability and versatility, has emerged as a preferred platform for IoT projects. However, ensuring secure connections is critical to safeguard sensitive data and maintain privacy. This guide will help you navigate the complexities of securing IoT devices while leveraging the capabilities of Raspberry Pi.
This article aims to provide a detailed and practical approach to setting up and maintaining secure remote IoT P2P connections on Raspberry Pi. By the end of this guide, you'll have the knowledge and tools to implement a secure setup that aligns with your specific needs.
Read also:Rod Wave Weight
Table of Contents
- Introduction to Secure Remote IoT Connections
- Raspberry Pi: An Overview
- Understanding P2P Protocols
- Steps to Securely Connect Remote IoT Devices
- Software Setup and Download
- Enhancing Network Security
- Importance of Data Encryption
- Common Issues and Troubleshooting
- Best Practices for Secure IoT Connections
- Future Trends in IoT Security
Introduction to Secure Remote IoT Connections
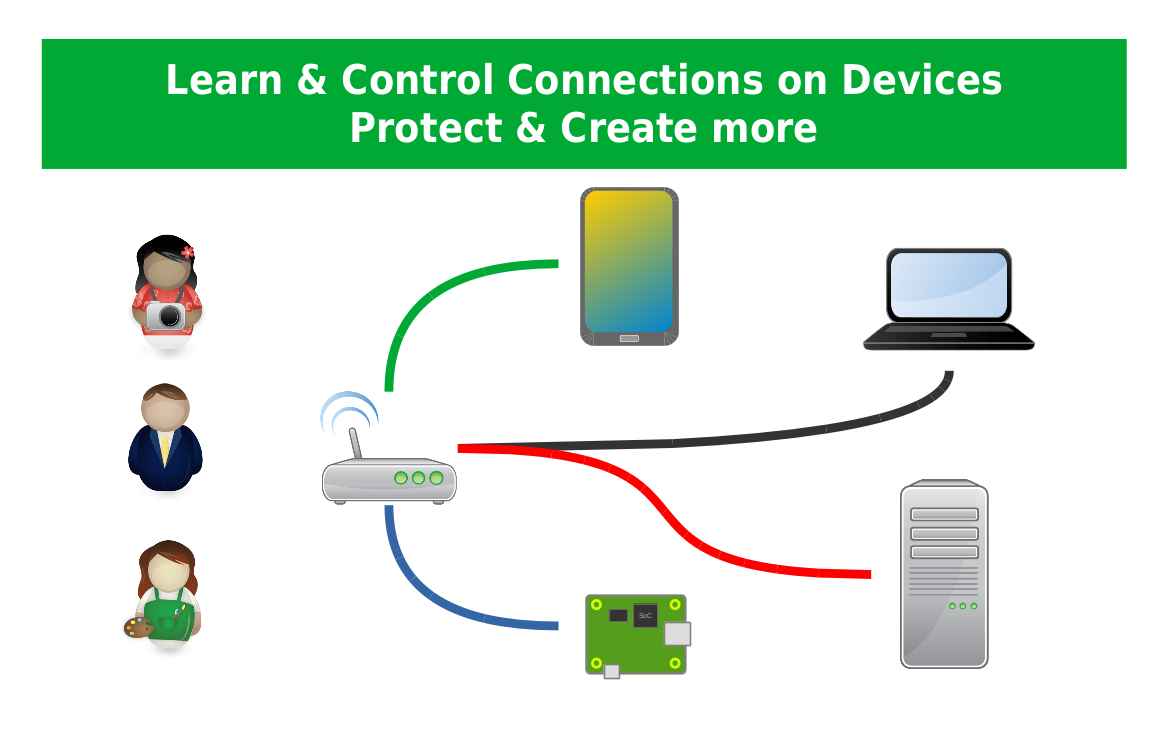
Remote IoT device connectivity has transformed the way we interact with technology, offering unparalleled convenience and efficiency. However, with this advancement comes the responsibility to prioritize security. Leveraging P2P protocols on a Raspberry Pi provides a powerful solution for establishing secure remote IoT connections. By utilizing the capabilities of Raspberry Pi, users can facilitate direct communication between devices without relying on centralized servers, enhancing both security and performance.
Why Secure Connections Are Essential
In the realm of IoT, devices often handle sensitive data, including personal information, location data, and even financial transactions. A security breach can lead to unauthorized access, data theft, and potential harm to users. Therefore, securing remote IoT connections is not merely a technical requirement but a moral obligation to protect users and their data.
Raspberry Pi: An Overview
The Raspberry Pi is a compact, cost-effective computer that has captured the attention of developers, hobbyists, and educators alike. Its versatility makes it an ideal platform for IoT projects. With the ability to run various operating systems and support a wide array of peripherals, the Raspberry Pi is perfectly suited for setting up secure remote IoT connections.
Key Features of Raspberry Pi
- Compact and energy-efficient design, making it ideal for portable and embedded applications.
- Supports multiple operating systems, including Linux-based distributions, offering flexibility for diverse projects.
- Equipped with GPIO pins for interfacing with external hardware components, expanding its functionality.
- Highly customizable and expandable, allowing users to tailor the device to their specific needs.
Understanding P2P Protocols
P2P (Peer-to-Peer) protocols enable devices to communicate directly without the need for a central server. This decentralized approach offers numerous advantages, such as reduced latency, improved scalability, and enhanced security. By employing P2P protocols, IoT devices can establish secure connections with minimal overhead, ensuring efficient and reliable communication.
Types of P2P Protocols
- BitTorrent: A widely-used protocol for file sharing that leverages distributed networks for efficient data transfer.
- Skype: A communication platform that utilizes P2P technology to facilitate voice and video calls.
- IPFS (InterPlanetary File System): A distributed protocol designed for storing and sharing data across a peer-to-peer network.
Steps to Securely Connect Remote IoT Devices
Establishing secure remote IoT connections involves a series of critical steps, from configuring the Raspberry Pi to implementing advanced encryption protocols. Each step is essential in creating a robust and secure setup tailored to your specific requirements.
Step 1: Initial Setup of Raspberry Pi
To begin, install the appropriate operating system on your Raspberry Pi. Raspbian, a Debian-based distribution, is a popular choice for IoT projects due to its stability and support for various applications. Ensure that your Raspberry Pi is updated with the latest security patches to mitigate potential vulnerabilities.
Read also:Who Is Morgan Freeman S Son
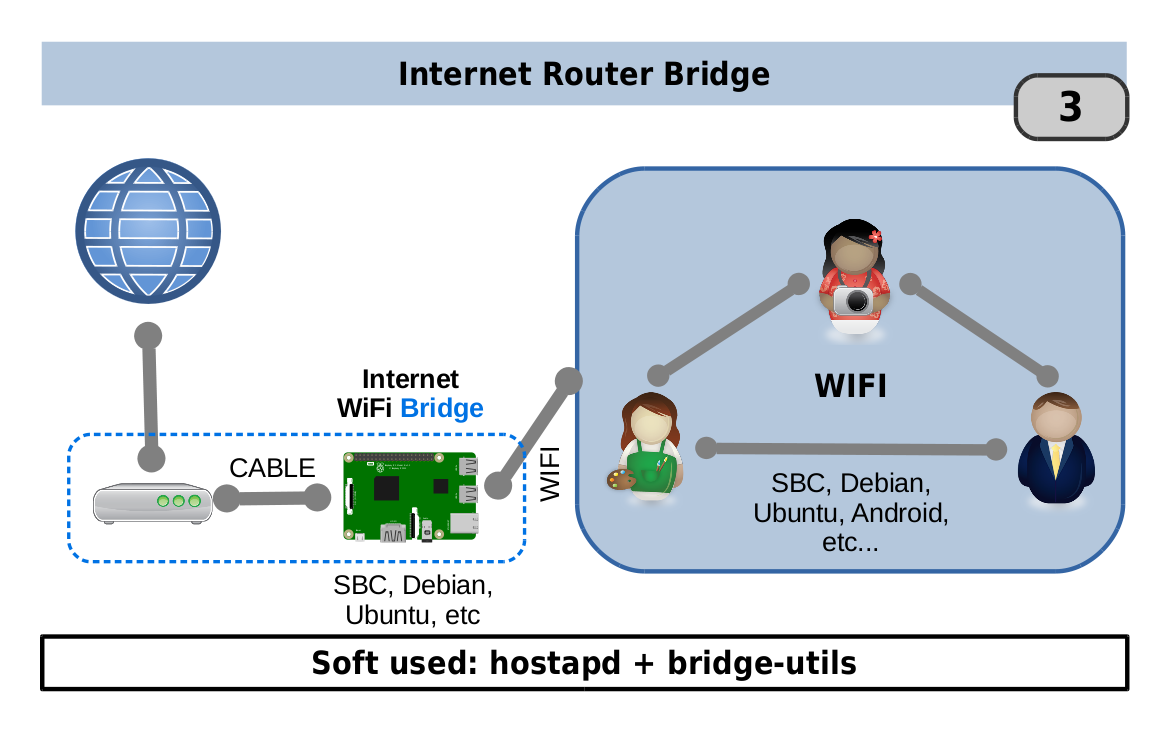
Step 2: Configure Network Settings
Set up your Raspberry Pi to connect seamlessly to your local network. Assign a static IP address to ensure consistent connectivity, and configure your router to enable port forwarding for P2P communication. Proper network configuration is vital for maintaining stable and secure connections.
Software Setup and Download
After completing the initial setup of your Raspberry Pi, the next step is to download and install the necessary software for secure remote IoT connections. This includes P2P communication software, encryption tools, and monitoring applications that enhance the security and functionality of your setup.
Recommended Software
- WireGuard: A modern and efficient VPN solution designed for simplicity and security, making it ideal for IoT projects.
- OpenVPN: A widely-used open-source VPN protocol that provides robust security features for remote connections.
- mosquitto: An MQTT broker that facilitates IoT communication by enabling lightweight messaging between devices.
Enhancing Network Security
Network security plays a pivotal role in securing remote IoT connections. Implementing firewalls, intrusion detection systems, and regular security audits can significantly enhance the security of your network, protecting it from potential threats and vulnerabilities.
Firewall Configuration
Set up a firewall on your Raspberry Pi to block unauthorized access and protect sensitive data. Tools like UFW (Uncomplicated Firewall) simplify the configuration process, allowing users to define rules and policies with ease.
Importance of Data Encryption
Data encryption is a fundamental aspect of protecting sensitive information transmitted between IoT devices. By encrypting data, you ensure that even if intercepted, it remains unreadable to unauthorized parties, safeguarding your network and devices.
Encryption Protocols
- TLS (Transport Layer Security): A widely-used protocol that provides secure communication over the internet.
- SSL (Secure Sockets Layer): A predecessor to TLS, still utilized in some applications for secure data transmission.
- AES (Advanced Encryption Standard): A symmetric encryption algorithm known for its speed and security, making it suitable for IoT applications.
Common Issues and Troubleshooting
Even with meticulous planning, challenges may arise when setting up secure remote IoT connections. Common issues include connectivity problems, software conflicts, and configuration errors. Below are some troubleshooting tips to help resolve these challenges:
Troubleshooting Tips
- Check Network Settings: Verify that your Raspberry Pi is correctly configured to connect to the local network and that port forwarding is enabled for P2P communication.
- Verify Software Versions: Ensure that all installed software is up to date and compatible with your Raspberry Pi's operating system.
- Review Logs: Examine system logs for error messages and take appropriate corrective actions to resolve identified issues.
Best Practices for Secure IoT Connections
Adopting best practices is essential for maintaining secure IoT connections. Regularly updating software, using strong passwords, and monitoring network activity are crucial steps in detecting and mitigating potential threats.
Key Best Practices
- Implement Multi-Factor Authentication: Add an extra layer of security by requiring multiple forms of verification for accessing IoT devices.
- Regularly Back Up Important Data: Protect your data by creating regular backups to prevent loss in the event of a security breach or hardware failure.
- Stay Informed: Keep abreast of the latest security threats and vulnerabilities to ensure your setup remains secure and up to date.
Future Trends in IoT Security
The field of IoT security is evolving rapidly, with new technologies and protocols emerging to address existing challenges. Innovations such as quantum encryption, blockchain-based security, and AI-driven threat detection are shaping the future of IoT security, offering enhanced protection and efficiency.
Emerging Technologies
- Quantum Encryption: A cutting-edge technology that leverages the principles of quantum mechanics to provide unparalleled security for data transmission.
- Blockchain: A decentralized and tamper-proof system for storing and verifying data, offering transparency and security for IoT applications.
- AI-Driven Security: Utilizes machine learning algorithms to detect and respond to threats in real-time, enhancing the security of IoT networks.
Conclusion
Securing remote IoT connections using P2P protocols on a Raspberry Pi is a critical task that demands careful planning and execution. By following the steps outlined in this guide, you can establish a secure and efficient setup that meets your specific needs. Remember to stay informed about the latest security trends and best practices to ensure the ongoing protection of your IoT devices.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT security and related topics.
References: