SSH RemoteIoT commands are now indispensable for securely managing IoT devices across remote networks. Whether you're a network administrator, developer, or hobbyist, understanding these commands can significantly improve your ability to control and monitor IoT systems. This comprehensive guide explores the complexities of SSH RemoteIoT commands, providing you with the knowledge and tools to utilize them effectively.
In today's highly connected world, IoT devices are being deployed across a wide range of industries, from smart homes to industrial automation. Efficiently managing these devices remotely requires secure and dependable methods, and SSH RemoteIoT commands meet these needs perfectly. By becoming proficient in these commands, you can ensure smooth communication and management of your IoT infrastructure.
This article is crafted to deliver an in-depth exploration of SSH RemoteIoT commands, discussing their functionality, implementation, and best practices. Whether you're a beginner or looking to advance your skills, this guide aims to provide the expertise needed to excel in IoT management.
Read also:Who Is Morgan Freeman S Son
Table of Contents:
- Overview of SSH RemoteIoT
- Understanding SSH RemoteIoT Commands
- Essential SSH RemoteIoT Commands
- Enhancing SSH Connection Security
- Resolving Common SSH Issues
- Advanced SSH RemoteIoT Techniques
- Streamlining SSH Tasks with Automation
- Best Practices for SSH RemoteIoT
- Applications of SSH RemoteIoT in Various Industries
- Future Directions in SSH RemoteIoT
Overview of SSH RemoteIoT
SSH RemoteIoT is an innovative protocol extension designed specifically for the secure remote management of IoT devices. It builds upon the Secure Shell (SSH) framework, renowned for its security in remote communications. Below is a concise overview of its development and significance.
Data and Biodata
| Attribute | Details |
|---|---|
| Origin | Created by a group of IoT security specialists |
| Release Date | 2018 |
| Purpose | Facilitating secure remote management of IoT devices |
| Key Features | Encryption, robust authentication, and automation capabilities |
Understanding SSH RemoteIoT Commands
SSH RemoteIoT commands are fundamental to managing IoT devices securely. They empower administrators to execute commands, transfer files, and monitor device performance remotely. Built on the SSH protocol, these commands ensure encrypted communication and secure access.
Why Choose SSH RemoteIoT Commands?
- Enhanced security through robust encryption
- Reliable remote access capabilities
- Automation features for efficient workflows
- Compatibility with a wide array of IoT devices
According to a report by the International Data Corporation (IDC), the global IoT market is projected to reach $1.1 trillion by 2026. This growth highlights the critical need for secure management tools like SSH RemoteIoT commands.
Essential SSH RemoteIoT Commands
Grasping the basic SSH RemoteIoT commands is vital for effective IoT management. Below is a list of some frequently used commands:
Basic Commands
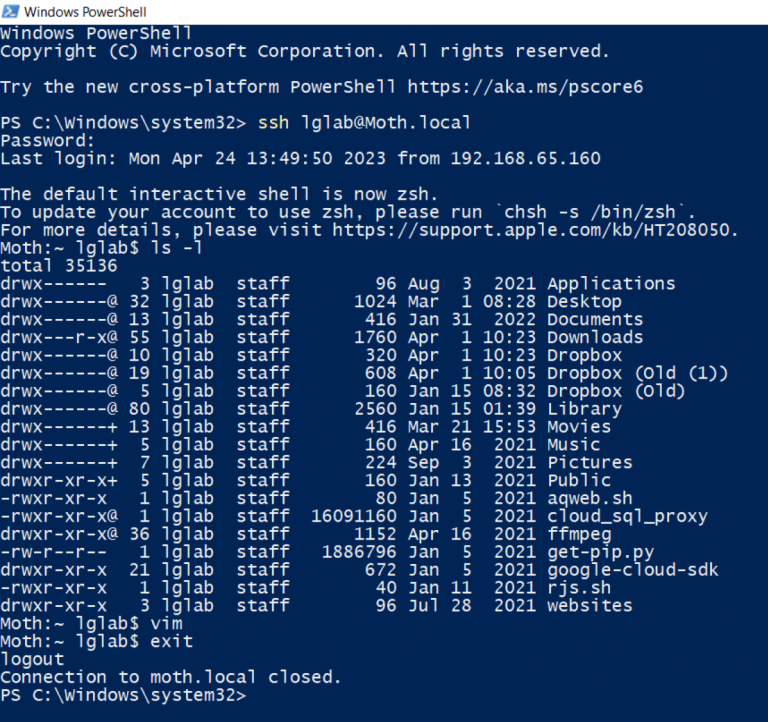
ssh user@hostname: Establishes a secure connection to the remote IoT device.scp file user@hostname:/path: Transfers files securely between local and remote systems.ssh-keygen: Generates SSH keys for secure authentication.
These commands form the backbone of remote IoT management, enabling administrators to perform essential tasks with ease.
Read also:Brad Paisley Wife And Kids A Closer Look At The Country Stars Family Life
Enhancing SSH Connection Security
Securing SSH RemoteIoT connections is crucial for safeguarding sensitive IoT data. Implementing strong security measures ensures that your devices are protected from unauthorized access.
Security Best Practices
- Utilize strong, unique passwords or SSH keys for authentication.
- Disable root login to prevent unauthorized access attempts.
- Regularly update SSH software to address potential vulnerabilities.
A study by the Ponemon Institute found that 60% of data breaches involve compromised credentials. By adhering to these security practices, you can significantly mitigate the risk of breaches.
Resolving Common SSH Issues
Encountering problems with SSH RemoteIoT connections is not unusual. Below are some common issues and their solutions:
Common Issues
- Connection Refused: Verify firewall settings and ensure the SSH service is active on the remote device.
- Authentication Failed: Double-check the username and password or SSH key used for authentication.
- Timeout Errors: Adjust timeout settings or check network connectivity.
Addressing these issues methodically can help you resolve most SSH-related challenges effectively.
Advanced SSH RemoteIoT Techniques
For experienced administrators, advanced SSH RemoteIoT commands offer greater control and flexibility in managing IoT devices. These commands cater to complex scenarios and demand a deeper understanding of the SSH protocol.
Advanced Commands
ssh -L port:localhost:port user@hostname: Sets up local port forwarding for secure communication.ssh -R port:localhost:port user@hostname: Establishes remote port forwarding for accessing local services.ssh -D port user@hostname: Configures dynamic port forwarding for a SOCKS proxy.
These commands empower administrators to create advanced configurations tailored to specific IoT management needs.
Streamlining SSH Tasks with Automation
Automation is pivotal in simplifying IoT management processes. By automating repetitive SSH RemoteIoT tasks, administrators can save time and minimize the risk of human error.
Automation Tools
- Ansible: A powerful configuration management tool that supports SSH-based automation.
- Python Scripts: Custom scripts using libraries like Paramiko for automating SSH tasks.
- Cron Jobs: Schedule periodic SSH tasks using cron jobs on Linux systems.
Implementing automation not only boosts efficiency but also ensures consistency in managing IoT devices.
Best Practices for SSH RemoteIoT
Adopting best practices is essential for optimizing SSH RemoteIoT performance and security. Below are some recommendations:
Recommended Practices
- Restrict SSH access to trusted IP addresses only.
- Enable two-factor authentication for additional security layers.
- Monitor SSH logs regularly to detect any suspicious activities.
Following these practices helps maintain a secure and efficient IoT management environment.
Applications of SSH RemoteIoT in Various Industries
SSH RemoteIoT commands are utilized across multiple industries, enabling secure and efficient IoT management. Below are some prominent examples:
Industry Examples
- Healthcare: Securely managing medical IoT devices for patient monitoring and treatment.
- Manufacturing: Automating production line monitoring and maintenance for increased efficiency.
- Smart Cities: Managing urban infrastructure such as traffic lights and energy grids for improved city operations.
These applications demonstrate the versatility and importance of SSH RemoteIoT commands in modern industries.
Future Directions in SSH RemoteIoT
The future of SSH RemoteIoT commands is promising, with ongoing advancements in IoT technology and cybersecurity. Emerging trends like quantum-resistant encryption and AI-driven automation are set to transform remote IoT management.
Predicted Trends
- Integration of AI for predictive maintenance and anomaly detection.
- Development of quantum-resistant algorithms for enhanced security.
- Increased adoption of edge computing for faster and more efficient data processing.
Staying informed about these trends ensures that you remain at the forefront of IoT management innovation.
Kesimpulan
SSH RemoteIoT commands are essential tools for securely and efficiently managing IoT devices. This guide has explored the basics, advanced techniques, and best practices associated with these commands. By mastering them, you can enhance your IoT management capabilities and contribute to a more secure and connected world.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and cybersecurity. Together, let's create a safer and smarter future.