Monitoring a Raspberry Pi behind a firewall on Windows 10 might seem daunting, but with the right tools and techniques, it becomes a straightforward process. Whether you're managing a home server, setting up IoT devices, or monitoring network activity, this guide will help you navigate the complexities of securely connecting to your Raspberry Pi.
Firewalls play a crucial role in maintaining network security, but they can also create challenges when trying to access devices like the Raspberry Pi remotely. This article will guide you through the process of using your Raspberry Pi behind a firewall while ensuring both safety and efficiency. By the end, you'll have practical tips and actionable steps to implement.
Our goal is to provide you with detailed instructions and expert advice, ensuring that you can set up and monitor your Raspberry Pi without compromising your system's security. Let's delve into the specifics of how to achieve this seamlessly on Windows 10.
Read also:Understanding The Concept Of Masa 49 And Its Cultural Significance
Table of Contents
- Getting to Know Raspberry Pi
- Understanding the Windows 10 Firewall
- Steps to Monitor Raspberry Pi Behind a Firewall
- Configuring the Windows Firewall
- Using SSH for Secure Remote Access
- Securing Your Connection
- Troubleshooting Common Issues
- Advanced Techniques for Enhanced Security
- Essential Tools and Software
- Conclusion and Next Steps
Getting to Know Raspberry Pi
The Raspberry Pi is a compact, cost-effective computer that has transformed the way people interact with technology. Its versatility makes it an ideal choice for educational purposes, home automation projects, and even professional applications. Understanding its capabilities is the foundation for effectively utilizing it behind a firewall.
Why Should You Use Raspberry Pi Behind a Firewall? In today's digital age, security is paramount. Firewalls act as a protective barrier between your internal network and external threats, safeguarding sensitive data and preventing unauthorized access. However, this protection can sometimes complicate remote access to devices like the Raspberry Pi. By mastering the configuration of your Raspberry Pi and Windows 10 firewall settings, you can maintain robust security while still enjoying seamless remote access. This section will explore the fundamentals of Raspberry Pi and highlight the advantages of using it behind a firewall.
Understanding the Windows 10 Firewall
Windows 10 features a powerful firewall that plays a critical role in protecting your computer from unauthorized access. This firewall blocks both incoming and outgoing connections, which is essential when managing devices such as the Raspberry Pi.
Key Features of the Windows Firewall
- Inbound and Outbound Rules: Control which connections are allowed or blocked.
- Network Location Awareness: Automatically adjust firewall settings based on your network environment.
- Advanced Security Settings: Customize rules for specific applications and ports.
Understanding these features is vital for configuring your firewall to permit secure access to your Raspberry Pi. We'll explore how to fine-tune these settings without jeopardizing your system's security.
Steps to Monitor Raspberry Pi Behind a Firewall
Monitoring your Raspberry Pi behind a firewall involves a series of well-defined steps. Below is a comprehensive guide to help you set up and manage your device securely.
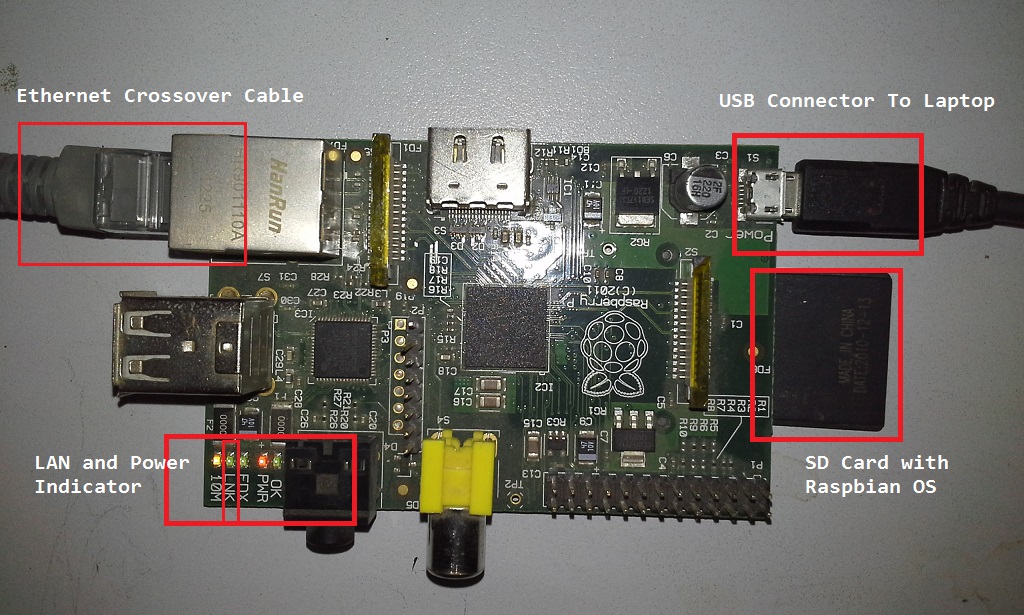
Step 1: Connect Raspberry Pi to Your Local Network
Ensure your Raspberry Pi is connected to the same local network as your Windows 10 computer. This can be achieved via Ethernet or Wi-Fi. Confirm the IP address assigned to your Raspberry Pi by examining its network settings.
Read also:Brad Paisley Wife And Kids A Closer Look At The Country Stars Family Life
Step 2: Configure Port Forwarding on Your Router
If you intend to access your Raspberry Pi from outside your local network, configuring port forwarding on your router is necessary. This process enables external devices to connect securely to your Raspberry Pi.
Step 3: Test the Connection
After completing the configuration, test the connection to verify that everything functions correctly. Tools such as PuTTY or Windows Terminal can be used to establish the connection.
Configuring the Windows Firewall
The Windows Firewall is instrumental in managing access to your Raspberry Pi. Here's how you can configure it:
Allow Specific Ports
By default, the Windows Firewall blocks most incoming connections. To enable access to your Raspberry Pi, create inbound rules for specific ports, such as port 22 for SSH.
Set Up Outbound Rules
Ensure that outbound connections are permitted for any software or applications you plan to use with your Raspberry Pi. Refer to Microsoft's official documentation for detailed instructions on configuring the Windows Firewall.
Using SSH for Secure Remote Access
Secure Shell (SSH) is one of the most widely used methods for accessing Raspberry Pi remotely. It provides a secure channel for communication between your Windows 10 computer and the Raspberry Pi.
Enabling SSH on Raspberry Pi
Activate SSH on your Raspberry Pi by using the Raspberry Pi Configuration tool or by creating an empty file named "ssh" on the boot partition. This step ensures that your Raspberry Pi is ready to accept remote connections.
Connecting via SSH on Windows 10
Utilize tools like PuTTY or the built-in SSH client in Windows Terminal to connect to your Raspberry Pi. Ensure that the correct IP address and port number are specified during the connection process.
Securing Your Connection
Security should always be a top priority when accessing devices behind a firewall. Below are some best practices to ensure your connection remains secure:
- Use strong, unique passwords to prevent unauthorized access.
- Implement two-factor authentication (2FA) for an added layer of protection.
- Regularly update your Raspberry Pi's firmware and software to address any potential vulnerabilities.
Consider employing a Virtual Private Network (VPN) to further enhance the security of your connection.
Troubleshooting Common Issues
Even with careful setup, issues may arise. Below are some common problems and their solutions:
Connection Timeout
If you're encountering connection timeouts, review your firewall settings to confirm that the appropriate ports are open. Verify the IP address and ensure that the Raspberry Pi is correctly connected to the network.
Authentication Errors
Authentication errors typically occur due to incorrect passwords or misconfigured SSH settings. Carefully check your credentials and ensure that SSH is properly enabled on your Raspberry Pi.
Advanced Techniques for Enhanced Security
For users seeking more advanced configurations, there are additional techniques to refine your setup:
Setting Up a Static IP Address
Assigning a static IP address to your Raspberry Pi ensures consistent connectivity and simplifies remote access. This process involves configuring your network settings to allocate a fixed IP address to your device.
Using Port Knocking
Port knocking introduces an extra layer of security by requiring a specific sequence of connection attempts before granting access. This method can significantly enhance the security of your setup.
These advanced techniques demand a deeper understanding of networking and security principles but offer substantial improvements in robustness and reliability.
Essential Tools and Software
Several tools and software can streamline the management of your Raspberry Pi:
- PuTTY: A widely-used SSH client for Windows that facilitates secure connections.
- Windows Terminal: A modern terminal application with built-in SSH support, offering a seamless user experience.
- WinSCP: A file transfer program that supports SFTP and SCP, enabling secure file transfers between your devices.
Consult the official documentation of these tools for comprehensive usage instructions.
Conclusion and Next Steps
In this article, we've examined how to use Raspberry Pi behind a firewall on Windows 10. From comprehending firewalls and configuring settings to securing connections and troubleshooting issues, you now possess the knowledge to manage your Raspberry Pi effectively.
Call to Action: We encourage you to experiment with these techniques and share your experiences in the comments section below. Additionally, explore our other articles for further insights into Raspberry Pi and networking.
Always remember, security is critical when managing devices behind a firewall. Stay informed and keep your systems updated to ensure optimal performance and protection.