Utilizing a Raspberry Pi SSH tunnel proxy has emerged as a vital tool for users aiming to fortify network security, circumvent geographical limitations, and safeguard online privacy. This compact yet powerful device, paired with SSH tunneling, provides an exceptional means of secure communication. Whether you're a tech aficionado, a remote professional, or someone concerned about privacy, learning to establish and utilize a Raspberry Pi SSH tunnel proxy is indispensable.
In this detailed guide, we will delve into the world of Raspberry Pi SSH tunnel proxies, exploring their functionality, advantages, and the step-by-step process of setting them up. By the conclusion of this article, you will possess a comprehensive understanding of how to leverage this technology to secure your data and enhance your network's capabilities.
This guide caters to both beginners and advanced users, ensuring that everyone can grasp the concepts and implement them effectively. We will cover everything from the fundamentals of SSH tunneling to advanced configurations, empowering you to tailor the solution to your unique needs.
Read also:Brad Paisley Wife And Kids A Closer Look At The Country Stars Family Life
Table of Contents
- Exploring Raspberry Pi SSH Tunnel Proxy
- Understanding Raspberry Pi Fundamentals
- What Exactly is SSH Tunneling?
- Advantages of Leveraging Raspberry Pi SSH Tunnel Proxy
- Comprehensive Setup Guide
- Strengthening Security with SSH Tunnel Proxy
- Practical Applications of Raspberry Pi SSH Tunnel Proxy
- Addressing Common Issues and Troubleshooting
- Maximizing Your Raspberry Pi SSH Tunnel Proxy
- Summary and Next Steps
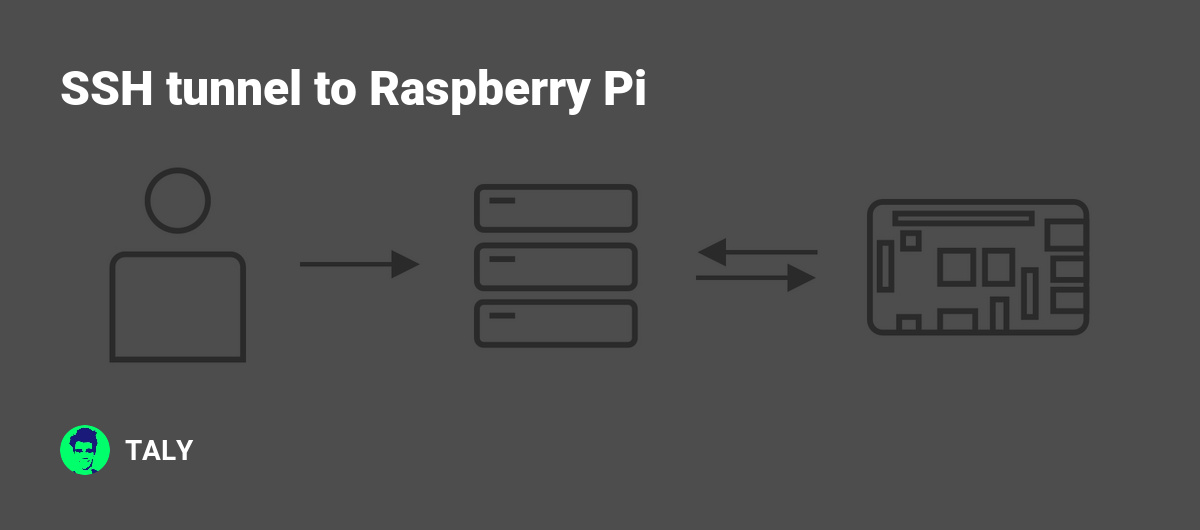
Exploring Raspberry Pi SSH Tunnel Proxy
A Raspberry Pi SSH tunnel proxy represents a dynamic fusion of hardware and software that empowers users to establish secure connections across untrusted networks. This configuration permits you to encrypt internet traffic, navigate through firewalls, and access restricted content while preserving privacy.
The integration of SSH tunneling with Raspberry Pi furnishes a cost-efficient and adaptable solution for individuals and organizations aiming to enhance network security. By channeling your traffic via an SSH tunnel, you can safeguard sensitive data and ensure the confidentiality of your online activities.
Regardless of whether you're working remotely, traveling, or simply seeking to secure your home network, Raspberry Pi SSH tunnel proxy delivers a robust solution that is both straightforward to set up and highly customizable.
Understanding Raspberry Pi Fundamentals
Raspberry Pi is a diminutive yet affordable computer that has garnered immense popularity among hobbyists, educators, and professionals. This credit-card-sized device is capable of running a full-fledged operating system and can be configured to execute a wide array of tasks, ranging from media streaming to server hosting.
Key attributes of Raspberry Pi include:
- Compact design with minimal power consumption
- Support for multiple operating systems, including various Linux distributions
- Extremely customizable hardware and software settings
- Extensive community support and resources
For setting up an SSH tunnel proxy, Raspberry Pi serves as an excellent platform due to its affordability, ease of use, and compatibility with diverse networking tools.
Read also:Manish Dayal Opleiding
What Exactly is SSH Tunneling?
SSH (Secure Shell) tunneling is a technique used to encrypt data transmissions between two devices across an unsecured network. By establishing an SSH tunnel, you can securely transfer data, access remote servers, and bypass network restrictions.
The process involves creating an encrypted connection between your local machine and a remote server. Once the tunnel is established, all traffic passing through it is encrypted, rendering it difficult for unauthorized parties to intercept or decipher the data.
SSH tunneling is widely employed for:
- Securing remote server access
- Overcoming firewalls and censorship
- Protecting sensitive information during transmission
Advantages of Leveraging Raspberry Pi SSH Tunnel Proxy
Employing Raspberry Pi as an SSH tunnel proxy presents several benefits, including:
- Cost-Effective: Raspberry Pi is significantly less expensive compared to dedicated hardware solutions, making it an appealing option for budget-conscious users.
- Portability: Its compact size allows for easy transportation, enabling you to establish a secure connection wherever you go.
- Customizability: Thanks to its open-source nature, Raspberry Pi can be tailored to meet specific requirements, whether for personal or professional purposes.
- Enhanced Security: By encrypting your internet traffic, you can shield your data from potential threats and unauthorized access.
These advantages make Raspberry Pi SSH tunnel proxy an excellent choice for anyone aiming to bolster their network security and privacy.
Comprehensive Setup Guide
Hardware Prerequisites
Prior to setting up your Raspberry Pi SSH tunnel proxy, ensure you have the following hardware components:
- Raspberry Pi (any model equipped with Ethernet or Wi-Fi capabilities)
- MicroSD card (minimum 8GB, preferably 16GB or higher)
- Power adapter compatible with your Raspberry Pi model
- Ethernet cable (optional, depending on your network setup)
Software Installation Process
Once you have the necessary hardware, adhere to these steps to install the required software:
- Download the Raspberry Pi OS image from the official website.
- Utilize a tool like BalenaEtcher to flash the OS image onto your MicroSD card.
- Insert the MicroSD card into your Raspberry Pi and power it on.
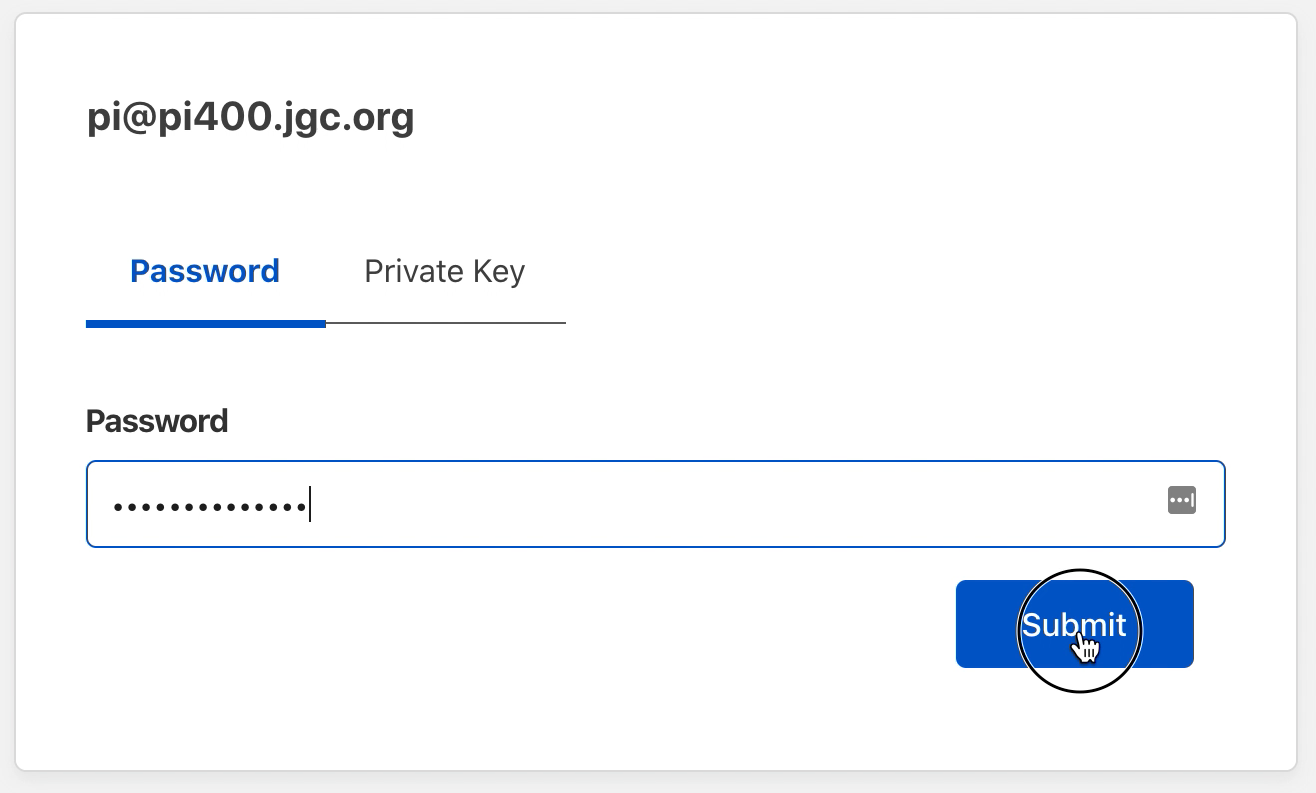
- Connect to your Raspberry Pi via SSH using a terminal or PuTTY.
Configuration Instructions
With the hardware and software in place, proceed with the following configuration steps:
- Update your Raspberry Pi's software using the command:
sudo apt update && sudo apt upgrade. - Install OpenSSH server if it's not already installed:
sudo apt install openssh-server. - Set up port forwarding on your router to direct incoming SSH traffic to your Raspberry Pi.
- Configure the SSH tunnel by editing the SSH configuration file:
sudo nano /etc/ssh/sshd_config.
Strengthening Security with SSH Tunnel Proxy
To fortify the security of your Raspberry Pi SSH tunnel proxy, consider implementing the following best practices:
- Utilize strong, unique passwords for SSH access.
- Enable two-factor authentication for additional protection.
- Regularly update your Raspberry Pi's software to address vulnerabilities.
- Monitor your SSH logs for any suspicious activity.
By adhering to these security measures, you can mitigate the risk of unauthorized access and ensure the integrity of your data.
Practical Applications of Raspberry Pi SSH Tunnel Proxy
Raspberry Pi SSH tunnel proxy offers numerous real-world applications, such as:
- Remote Work: Securely access company resources while working remotely or traveling.
- Traveling: Bypass geo-restrictions and access blocked content in foreign countries.
- Home Network Security: Protect personal data from potential threats within your local network.
These use cases underscore the versatility and utility of Raspberry Pi SSH tunnel proxy across various scenarios.
Addressing Common Issues and Troubleshooting
While setting up your Raspberry Pi SSH tunnel proxy, you may encounter some common issues. Below are solutions to assist you in troubleshooting:
- Connection Issues: Verify that your router's port forwarding settings are correctly configured.
- Slow Performance: Optimize your Raspberry Pi's performance by disabling unnecessary services.
- SSH Access Problems: Confirm that your SSH server is operational and that your firewall rules permit SSH traffic.
By promptly addressing these issues, you can ensure a seamless and efficient setup process.
Maximizing Your Raspberry Pi SSH Tunnel Proxy
To fully harness the potential of your Raspberry Pi SSH tunnel proxy, consider the following optimization tips:
- Upgrade your Raspberry Pi's hardware for superior performance.
- Employ lightweight applications and services to minimize resource usage.
- Consistently monitor and maintain your setup to guarantee optimal functionality.
These optimizations will assist you in achieving faster speeds and enhanced reliability in your SSH tunnel proxy.
Summary and Next Steps
Raspberry Pi SSH tunnel proxy delivers a potent and versatile solution for augmenting your network security and privacy. By following the steps outlined in this guide, you can establish and configure your own SSH tunnel proxy, customized to your unique requirements.
We invite you to share your experiences and insights in the comments section below. Furthermore, explore our other articles for additional tips and tutorials on utilizing Raspberry Pi for various applications.
Stay secure, stay informed, and enjoy your tinkering journey!