Remote IoT monitoring has revolutionized the way businesses and individuals manage devices and systems from afar. As the Internet of Things (IoT) continues to expand, the demand for secure and reliable remote access solutions has skyrocketed. This article delves into how to use SSH (Secure Shell) for remote IoT monitoring and introduces you to free SSH clients for Mac that can simplify your journey.
In today's fast-paced technological landscape, the ability to monitor and manage IoT devices remotely is no longer a luxury but a necessity. Whether you're a developer, IT professional, or hobbyist, understanding how to implement SSH for remote IoT monitoring is essential for maintaining secure and efficient operations. This guide will walk you through setting up SSH, recommend free SSH clients for Mac, and provide best practices to keep your system secure and efficient.
Contents Overview
- Exploring Remote IoT Monitoring
- Understanding SSH and Its Importance
- Why SSH Is Ideal for IoT Monitoring
- Top Free SSH Clients for Mac
- Step-by-Step Installation of SSH Clients on Mac
- Configuring SSH for Remote IoT Monitoring
- Ensuring Secure SSH Connections
- Addressing Common SSH Issues
- Advantages of Remote IoT Monitoring with SSH
- Conclusion and Next Steps
Exploring Remote IoT Monitoring
Remote IoT monitoring empowers users to access and manage IoT devices from any location with an internet connection. This capability is particularly vital for businesses that depend on IoT devices for critical operations, such as manufacturing, healthcare, and smart home systems. By utilizing SSH, users can establish secure connections to these devices, enabling tasks such as data collection, troubleshooting, and configuration updates.
Read also:Will Ferrel Teeth
SSH plays a pivotal role in securing remote access by encrypting all data transmissions. In the context of IoT, where devices often handle sensitive information, ensuring robust security measures is paramount. This section will provide a deeper understanding of remote IoT monitoring and highlight the critical role SSH plays in maintaining secure and reliable connections.
Understanding SSH and Its Importance
What Exactly Is SSH?
SSH, or Secure Shell, is a network protocol that facilitates secure communication between devices over potentially unsecured networks. It encrypts all data transmitted between devices, ensuring confidentiality and integrity of the information exchanged.
Key Features of SSH
- Encryption: SSH ensures all data transmitted between devices is encrypted, making it nearly impossible for attackers to intercept sensitive information.
- Authentication: SSH supports various authentication methods, including password-based and public-key authentication, ensuring only authorized users can access devices.
- Port Forwarding: SSH enables users to forward traffic from one port to another, providing secure access to services running on remote devices.
For remote IoT monitoring, SSH is an invaluable tool that guarantees secure and reliable connections, enhancing the overall efficiency of device management.
Why SSH Is Ideal for IoT Monitoring
In the realm of remote IoT monitoring, security is non-negotiable. Devices connected to the internet are susceptible to cyberattacks, necessitating robust security measures. SSH offers numerous advantages that make it a top choice for IoT monitoring:
- Enhanced Security: SSH encrypts all data transmissions, significantly reducing the risk of data breaches and unauthorized access.
- Reliability: SSH connections are stable and resilient, ensuring continuous access to IoT devices even during network disruptions.
- Scalability: SSH can handle multiple connections simultaneously, making it suitable for extensive IoT deployments.
By adopting SSH for IoT monitoring, users can ensure their devices remain secure and operational, regardless of the location from which they are accessed.
Top Free SSH Clients for Mac
Popular Options for Mac Users
Mac users have access to several free SSH clients, each with unique features and benefits. Below are some of the most popular options:
Read also:Paul Mishkin
- Terminal (Built-in): macOS includes a built-in SSH client accessible through the Terminal application. It's lightweight and ideal for experienced users familiar with command-line interfaces.
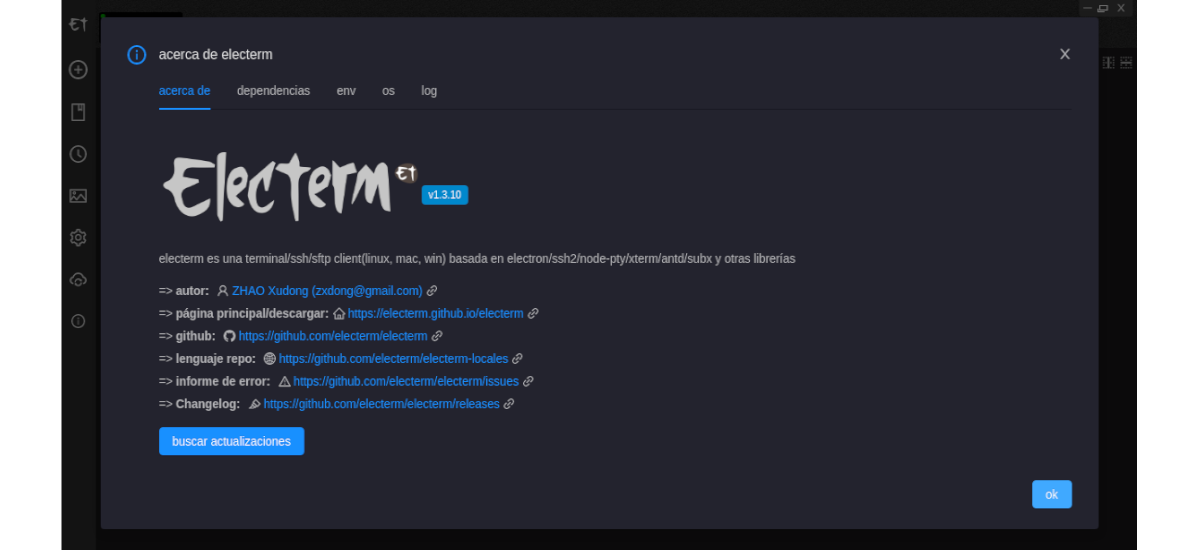
- Termius: A user-friendly SSH client with a graphical interface, Termius is perfect for beginners. It supports multiple connections and sessions, enhancing convenience.
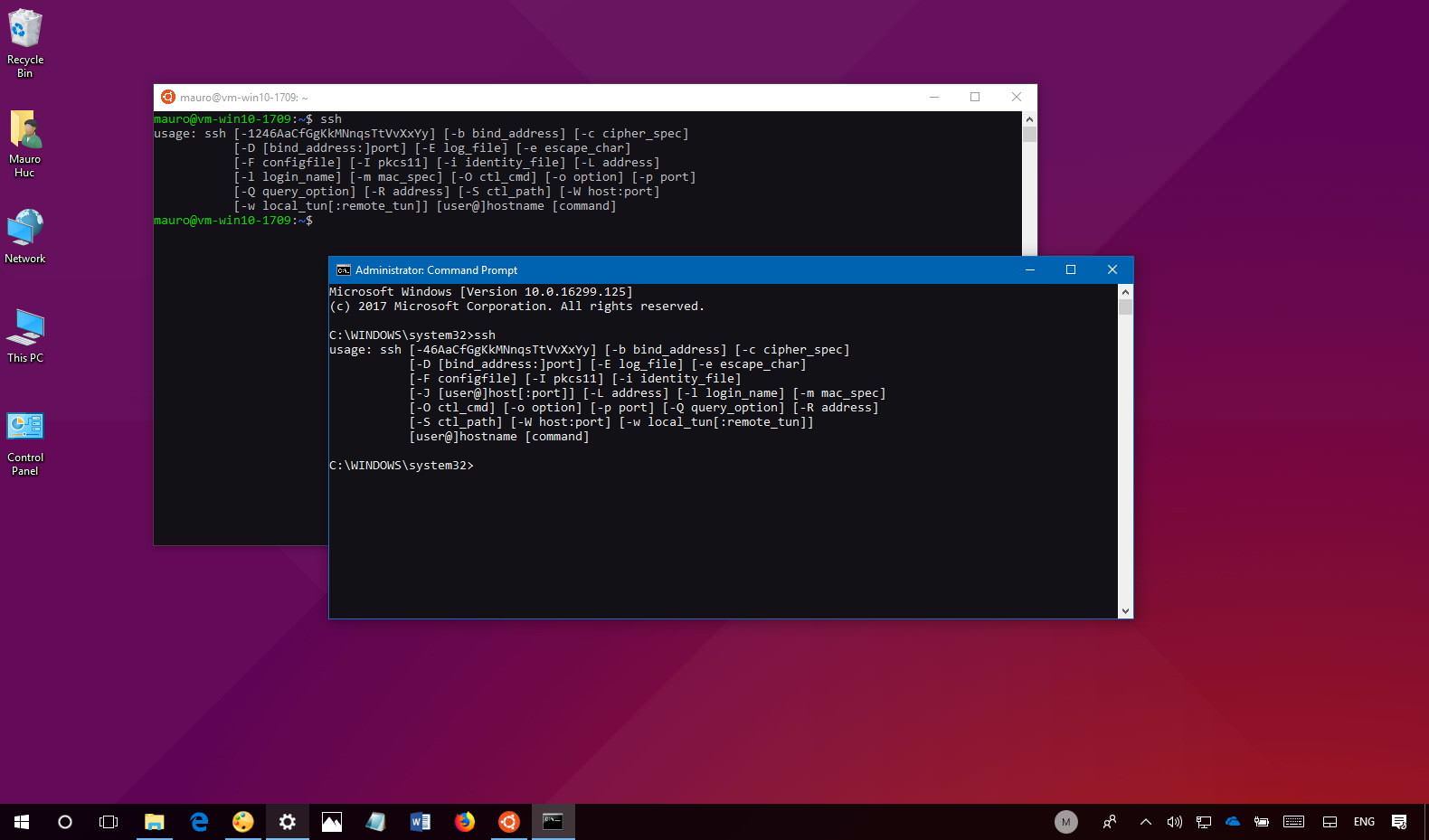
- PuTTY (for Mac): Originally designed for Windows, PuTTY is now available for Mac users and offers a comprehensive set of features for SSH connections.
Comparison Table
| Client Name | Features | Pros | Cons |
|---|---|---|---|
| Terminal | Built-in, command-line interface | No installation required, lightweight | Less intuitive for beginners |
| Termius | Graphical interface, supports multiple sessions | Easy to use, cross-platform support | Paid version required for advanced features |
| PuTTY | Robust feature set, customizable | Free, widely used | Requires installation |
Step-by-Step Installation of SSH Clients on Mac
Installing an SSH client on your Mac is a simple process. Below are detailed instructions for each popular option:
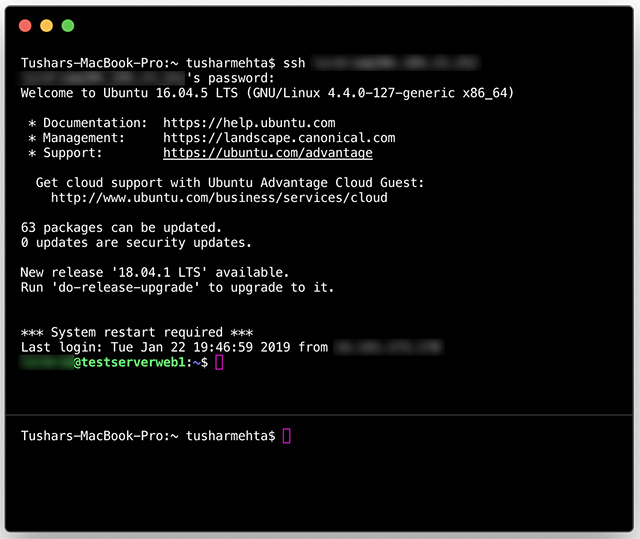
Using Terminal
- Open the Terminal application on your Mac.
- Type the command
ssh username@hostnameand press Enter. - Enter your password when prompted to establish the connection.
Installing Termius
- Download Termius from the official website or App Store.
- Launch the application and create a new connection by entering the hostname, username, and port number.
- Click the "Connect" button to establish the connection to the remote device.
Installing PuTTY
- Download PuTTY for Mac from the official website.
- Open the application and configure the session by entering the hostname and port number.
- Save the session for future use and click "Open" to establish the connection.
Configuring SSH for Remote IoT Monitoring
After installing an SSH client, the next step is to configure SSH for remote IoT monitoring. Here's a detailed breakdown of the process:
Step 1: Enable SSH on the IoT Device
Most IoT devices come with SSH disabled by default. Access the device's settings menu and enable the SSH service to allow remote connections.
Step 2: Configure Firewall Settings
Ensure your firewall permits incoming SSH connections on the default port (22). For added security, consider changing the default port.
Step 3: Test the Connection
Use your SSH client to test the connection to the IoT device. A successful connection indicates that you're ready to begin monitoring your devices remotely.
Ensuring Secure SSH Connections
To safeguard your SSH connections, adhere to the following best practices:
- Use strong, unique passwords for all SSH accounts to deter unauthorized access.
- Implement public-key authentication for an additional layer of security.
- Regularly update your SSH client and server software to address any security vulnerabilities.
- Monitor SSH logs for suspicious activity and take swift action if any irregularities are detected.
Addressing Common SSH Issues
Despite its reliability, SSH connections can occasionally encounter problems. Below are some common issues and their solutions:
Connection Refused
This error usually arises when the SSH service is not active on the remote device. Verify that SSH is enabled and that the firewall allows incoming connections on the appropriate port.
Authentication Failed
If you encounter an authentication failed error, recheck your username and password. If you're using public-key authentication, ensure the correct key is being utilized.
Timeout Errors
Timeout errors may result from network issues or incorrect hostname/IP address. Confirm the connection details and ensure your network is stable.
Advantages of Remote IoT Monitoring with SSH
Using SSH for remote IoT monitoring provides numerous benefits, including:
- Enhanced Security: SSH encrypts data and implements authentication, ensuring your information remains secure.
- Increased Efficiency: With remote access, you can manage multiple devices from a single location, saving valuable time and resources.
- Cost Savings: By minimizing the need for on-site visits, remote monitoring can significantly reduce operational expenses.
Conclusion and Next Steps
In summary, remote IoT monitoring using SSH is a powerful and secure solution for managing devices efficiently. By following the steps outlined in this article, you can set up SSH on your Mac and start monitoring your IoT devices from anywhere in the world.
We encourage you to explore the various SSH clients available for Mac and choose the one that aligns best with your needs. Always adhere to best practices for secure SSH connections to protect your devices and data effectively.
We invite you to share your thoughts and experiences in the comments section below. If you found this article helpful, please consider sharing it with your network. For more in-depth guides and tips on IoT and remote monitoring, explore our other articles on the site.