In today’s interconnected world, securing remote access to your Raspberry Pi is more important than ever. As remote interactions with Raspberry Pi devices become increasingly common, ensuring robust security measures is vital to protect sensitive data and maintain system integrity. This guide will walk you through the essential steps to effectively secure your Raspberry Pi for remote access.
Whether you're a hobbyist, a developer, or a professional in an enterprise setting, the significance of securing remote access for your Raspberry Pi cannot be overstated. This article delves into various techniques and best practices designed to safeguard your Raspberry Pi from unauthorized access and potential cyber threats.
By adopting the strategies outlined here, you can ensure that your Raspberry Pi remains protected while still providing seamless remote access. Let’s explore the details and equip yourself with the knowledge needed to enhance the security of your device.
Read also:Naviyd Ely Raymond
Table of Contents
- Understanding Remote Access on Raspberry Pi
- Why Securing Remote Access is Crucial
- Top Security Practices for Remote Access
- Enhancing Security Through SSH Configuration
- Optimizing Firewall Settings for Raspberry Pi
- The Role of Two-Factor Authentication
- The Importance of Regular Updates
- Strengthening Network Security
- Monitoring Logs for Suspicious Activity
- Additional Tips for Enhanced Security
- Conclusion and Next Steps
Understanding Remote Access on Raspberry Pi
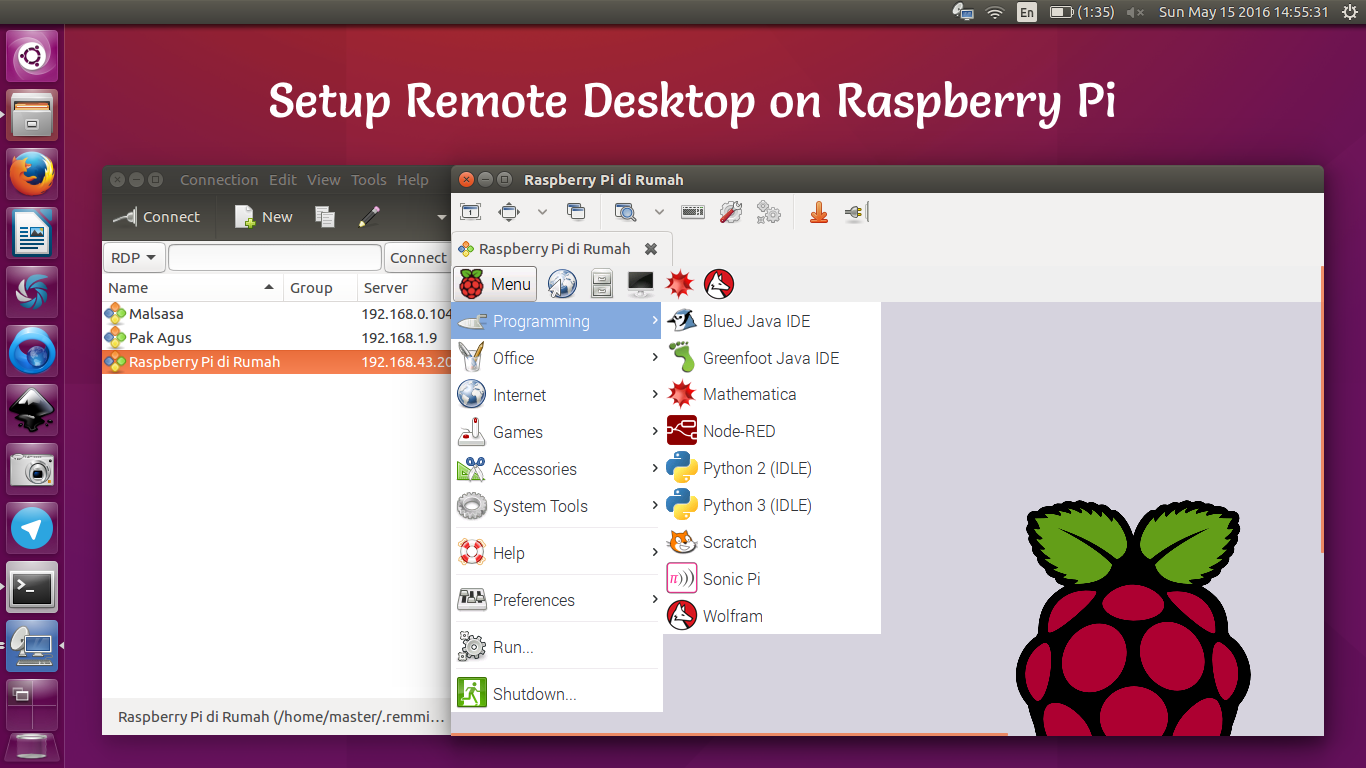
Remote access to a Raspberry Pi enables users to control and manage their devices from virtually anywhere in the world. This capability is particularly advantageous for developers, hobbyists, and professionals who require interaction with their Raspberry Pi without being physically present. However, enabling remote access also introduces potential security risks that must be addressed to maintain device safety.
By default, Raspberry Pi comes equipped with basic security settings that may not be sufficient for safeguarding remote access. It is imperative to implement advanced security measures to protect your device from unauthorized access and potential cyberattacks.
Why Remote Access is Essential
Remote access offers unparalleled flexibility and convenience, empowering users to accomplish a wide range of tasks, including:
- Managing files and applications remotely with ease.
- Monitoring system performance and health from a distance.
- Deploying updates and configurations without the need for physical presence.
Why Securing Remote Access is Crucial
Securing remote access for your Raspberry Pi is essential to protect sensitive data and prevent unauthorized access. In an era where cybercriminals are constantly scanning for vulnerabilities in internet-connected devices, an unsecured Raspberry Pi can quickly become a prime target for malicious attacks.
Common Security Threats
Some prevalent security threats associated with remote access to Raspberry Pi include:
- Brute force attacks targeting SSH credentials.
- Malware infections that compromise device functionality.
- Data breaches that expose sensitive information.
- Unauthorized access leading to potential misuse of the device.
By implementing comprehensive security measures, you can significantly mitigate these risks and ensure the safety of your Raspberry Pi.
Read also:Ayaka Motu
Top Security Practices for Remote Access
Here are some of the most effective security practices to fortify your Raspberry Pi’s remote access capabilities:
- Utilize strong, unique passwords that are difficult to guess.
- Disable unnecessary services that could serve as entry points for attackers.
- Limit user access and permissions to minimize potential damage.
- Regularly back up important data to prevent loss in case of a breach.
Adopting these practices lays the groundwork for a secure remote access environment for your Raspberry Pi.
Enhancing Security Through SSH Configuration
Secure Shell (SSH) serves as the primary method for remote access to Raspberry Pi. Properly configuring SSH is critical to securing your device. Below are some strategies for enhancing SSH security:
- Change the default SSH port to a non-standard number to deter automated attacks.
- Disable password-based authentication to eliminate brute force attack risks.
- Use SSH keys for authentication, ensuring only authorized users can access the device.
Steps to Configure SSH
To configure SSH on your Raspberry Pi, follow these steps:
- Enable SSH through the Raspberry Pi Configuration tool.
- Edit the SSH configuration file to apply desired security settings.
- Test the connection to ensure everything functions as intended.
Optimizing Firewall Settings for Raspberry Pi
A firewall acts as a protective barrier between your Raspberry Pi and potential threats on the internet. Configuring firewall settings is a fundamental step in securing remote access.
Configuring UFW Firewall
Uncomplicated Firewall (UFW) is a user-friendly tool for managing firewall settings on Raspberry Pi. Here’s how you can configure UFW:
- Install UFW on your Raspberry Pi to gain access to its features.
- Allow only the necessary ports required for remote access.
- Deny all other incoming connections to reduce the risk of unauthorized access.
By restricting access to specific ports, you can effectively minimize the attack surface for potential threats.
The Role of Two-Factor Authentication
Two-factor authentication (2FA) adds an additional layer of security to your Raspberry Pi’s remote access. By requiring a second form of verification, such as a one-time code, you can drastically reduce the likelihood of unauthorized access.
Setting Up 2FA with Google Authenticator
Google Authenticator is a widely used tool for implementing 2FA on Raspberry Pi. Here’s how you can set it up:
- Install the Google Authenticator PAM module on your Raspberry Pi.
- Configure SSH to integrate Google Authenticator for authentication purposes.
- Test the setup to ensure 2FA functions correctly.
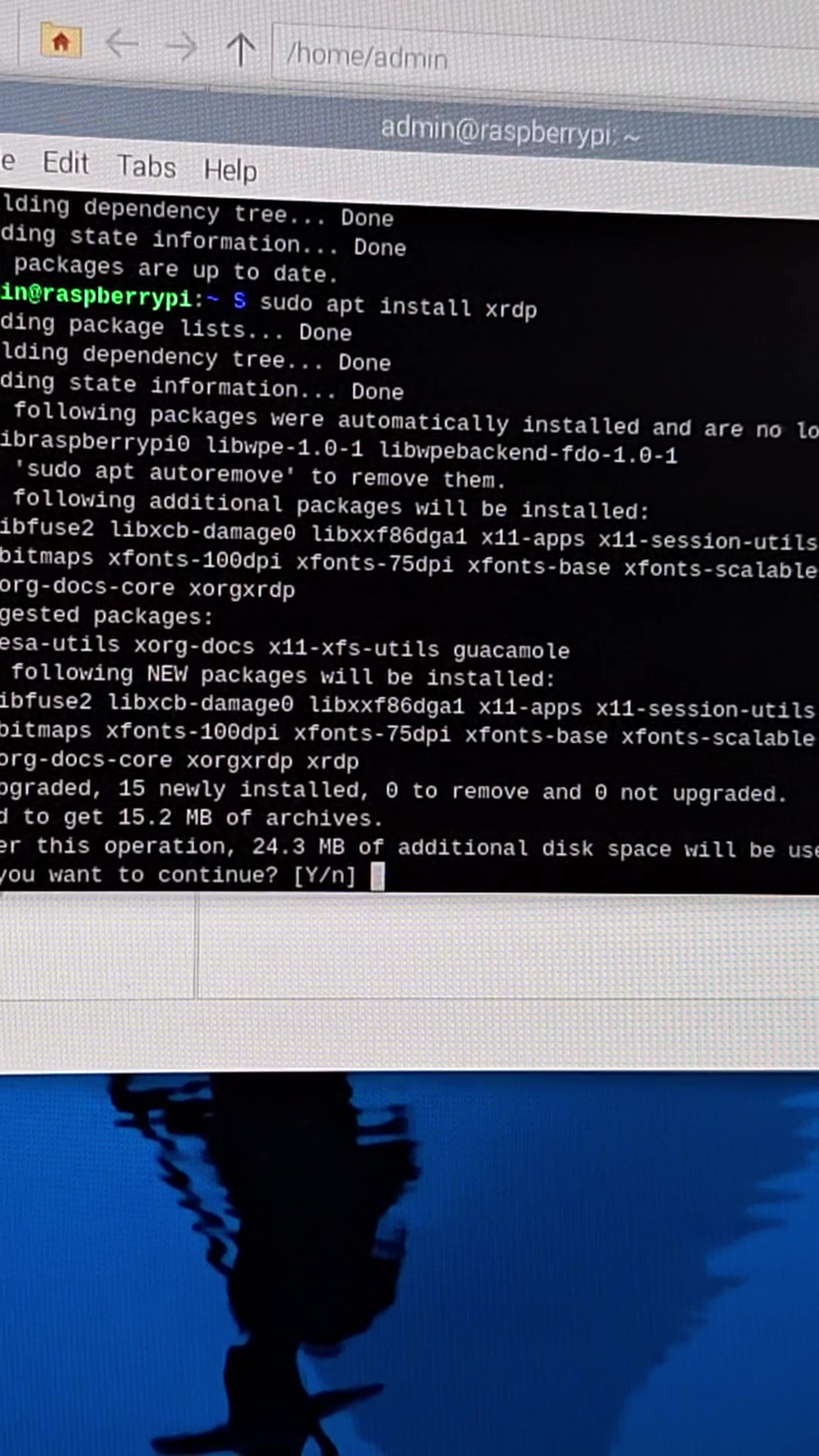
The Importance of Regular Updates
Keeping your Raspberry Pi updated is crucial for maintaining its security. Regular updates ensure that any known vulnerabilities are promptly addressed, reducing the risk of exploitation.
How to Update Raspberry Pi
To update your Raspberry Pi, follow these steps:
- Run the "sudo apt update" command to retrieve the latest package lists.
- Execute the "sudo apt full-upgrade" command to install all available updates.
- Reboot your Raspberry Pi to apply the changes and ensure everything runs smoothly.
Regular maintenance also involves monitoring system logs and conducting routine checks for any suspicious activities.
Strengthening Network Security
Network security plays a pivotal role in securing remote access for your Raspberry Pi. By implementing network-level security measures, you can further enhance the protection of your device.
Best Practices for Network Security
Here are some best practices for securing your network:
- Use a Virtual Private Network (VPN) to ensure secure communication between devices.
- Enable encryption for all network traffic to safeguard data in transit.
- Regularly change network passwords to prevent unauthorized access.
These practices contribute to creating a secure network environment for your Raspberry Pi.
Monitoring Logs for Suspicious Activity
Monitoring system logs is an effective way to detect and respond to potential security threats. By regularly reviewing logs, you can identify unusual activities and take appropriate actions to mitigate risks.
Tools for Log Monitoring
Several tools are available for log monitoring, including:
- Logwatch: A tool that provides detailed reports on system activity.
- Fail2Ban: A program that bans IP addresses showing malicious signs.
- rsyslog: A robust logging system for centralized log management.
These tools offer valuable insights into system activities, aiding in the maintenance of your Raspberry Pi’s security.
Additional Tips for Enhanced Security
Here are some additional tips to further bolster the security of your Raspberry Pi’s remote access:
- Utilize a strong and unique SSH key pair to authenticate users securely.
- Limit the number of login attempts to prevent brute force attacks.
- Regularly review and update security policies to adapt to evolving threats.
By adhering to these tips, you can ensure that your Raspberry Pi remains secure and protected against potential threats.
Conclusion and Next Steps
In conclusion, securing remote access for your Raspberry Pi is essential for protecting your device and preserving its integrity. By implementing the strategies outlined in this guide, you can significantly enhance the security of your Raspberry Pi’s remote access setup.
We encourage you to take immediate action by applying these security measures to your Raspberry Pi. Feel free to leave a comment below if you have any questions or suggestions. Additionally, don’t hesitate to share this article with others who may benefit from it. For more informative content, explore our other articles on cybersecurity and technology.
Data Sources: