As the world embraces remote work and smart technology, the need for secure access to Internet of Things (IoT) devices via SSH has become more critical than ever. Remote IoT SSH serves as a cornerstone for enabling users to efficiently manage and monitor IoT devices from virtually anywhere. Ensuring secure connections while maintaining optimal performance is essential for both businesses and individuals.
In today's digital landscape, where more organizations are integrating IoT solutions, the importance of effective remote management cannot be overstated. Remote IoT SSH not only enhances accessibility but also provides robust protection against potential cyber threats, safeguarding sensitive data.
This article explores the concept of remote IoT SSH in depth, examining its advantages, challenges, and best practices. Whether you're a tech enthusiast, a business owner, or an IT professional, understanding how to implement secure remote IoT SSH can significantly boost your operational efficiency and security.
Read also:Lachapel
Table of Contents:
- Understanding IoT SSH
- The Importance of Remote IoT SSH
- How to Set Up Remote IoT SSH
- Securing Remote IoT SSH Connections
- Top Tools for Remote IoT SSH
- Troubleshooting Common Challenges
- Maximizing Performance
- Comparing Remote IoT SSH Solutions
- The Future of Remote IoT SSH
- Conclusion
Understanding IoT SSH
IoT SSH, or Secure Shell for the Internet of Things, is a specialized protocol designed to enable secure communication between IoT devices and remote servers. It facilitates the management, monitoring, and control of IoT devices from any location, ensuring a secure channel that protects sensitive data from unauthorized access.
While traditional SSH protocols are widely used for secure remote access, IoT SSH is uniquely tailored to meet the specific needs of IoT devices, such as low power consumption and limited processing capabilities. By encrypting data transmissions, IoT SSH ensures that critical information remains protected, which is particularly important given the sensitive nature of data handled by IoT devices.
Key features of IoT SSH include:
- End-to-end encryption to safeguard data during transmission
- Robust authentication mechanisms to verify user identities
- Efficient resource utilization to accommodate IoT device limitations
- Scalability to support multiple devices simultaneously
Variations of IoT SSH Protocols
There are several variations of IoT SSH protocols, each designed to address specific use cases and device requirements. Some of the most popular variations include:
- SSH2: The latest version of SSH, offering enhanced security features and improved performance.
- Lightweight SSH: Optimized for devices with limited resources, ensuring efficient operation without compromising security.
- Custom SSH: Tailored solutions designed for specific industries or applications, providing specialized functionality.
The Importance of Remote IoT SSH
Remote IoT SSH is indispensable for modern businesses and individuals who rely on IoT devices for their operations. The ability to manage devices remotely not only saves time and resources but also ensures optimal performance and security. By reducing the need for physical site visits, remote IoT SSH offers significant cost savings while maintaining secure, encrypted connections.
Read also:Hank Kunneman Age
Key benefits of remote IoT SSH include:
- Enhanced security through encrypted connections that protect sensitive data
- Improved efficiency by enabling real-time remote management and monitoring
- Cost savings by minimizing the need for on-site visits and manual interventions
- Scalability to handle large-scale deployments and manage multiple devices simultaneously
Real-World Applications
Remote IoT SSH finds applications across various industries, revolutionizing how businesses and individuals interact with IoT devices. Some prominent examples include:
- Manufacturing: Monitoring and controlling machinery remotely to optimize production processes.
- Healthcare: Managing medical devices and securely handling patient data to improve healthcare delivery.
- Agriculture: Monitoring environmental conditions and automating processes to enhance crop yields.
- Smart Cities: Efficiently managing infrastructure and utilities to create sustainable urban environments.
How to Set Up Remote IoT SSH
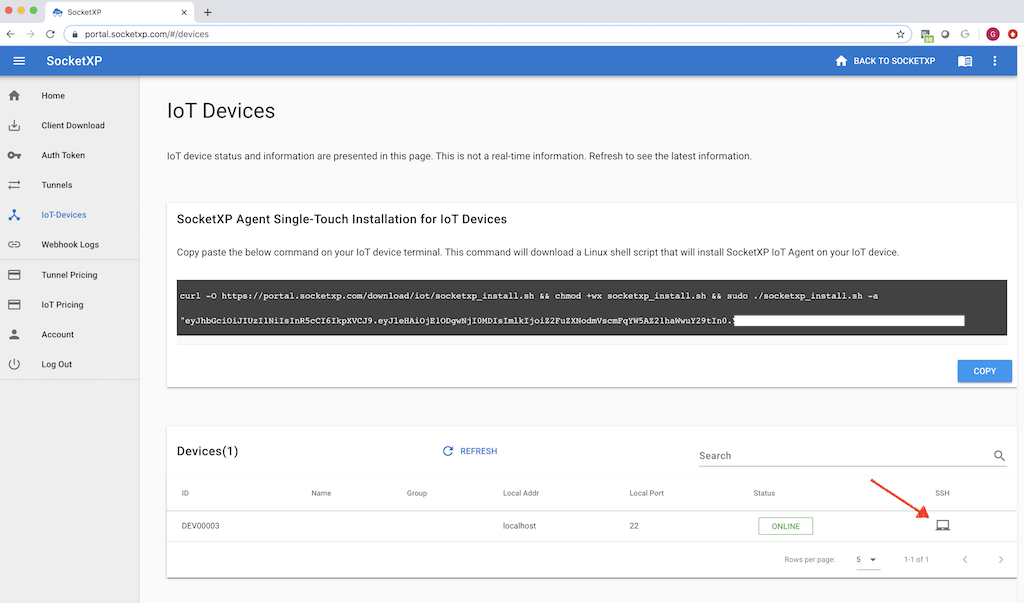
Setting up remote IoT SSH involves several key steps, including configuring the IoT device, establishing a secure connection, and testing the setup to ensure everything works seamlessly. Follow this step-by-step guide to get started:
- Install an SSH client on your device to facilitate secure communication.
- Configure the IoT device to support SSH connections, ensuring all necessary settings are properly adjusted.
- Set up a static IP address or dynamic DNS to enable remote access from external networks.
- Enable port forwarding on your router to allow external connections to reach your IoT device.
- Test the connection thoroughly to verify that everything is functioning as intended.
Following best practices during the setup process is crucial to ensuring maximum security and performance. Neglecting these steps can leave your system vulnerable to potential threats.
Tips for Successful Setup
To ensure a successful remote IoT SSH setup, consider the following recommendations:
- Use strong passwords or SSH keys for authentication to enhance security.
- Regularly update firmware and software to address security vulnerabilities and improve functionality.
- Monitor connections for suspicious activity to detect and respond to potential threats promptly.
- Implement firewall rules to restrict unauthorized access and protect your network.
Securing Remote IoT SSH Connections
Security is paramount when it comes to remote IoT SSH. Implementing best practices can significantly reduce the risk of cyberattacks and ensure the integrity of your data. Below are some key security measures to consider:
- Use end-to-end encryption for all communications to protect data during transmission.
- Implement two-factor authentication (2FA) for an additional layer of security.
- Regularly audit logs to identify and respond to potential threats in a timely manner.
- Limit access to authorized users only to minimize the risk of unauthorized access.
By prioritizing security, you can safeguard your IoT devices and the sensitive data they handle, ensuring peace of mind for both businesses and individuals.
Common Security Threats
Remote IoT SSH is not immune to security threats. Some common risks include:
- Brute-force attacks, where attackers attempt to guess passwords through repeated trials.
- Man-in-the-middle attacks, where attackers intercept communications between devices.
- Malware infections that compromise device functionality and data integrity.
- Unauthorized access due to weak passwords or misconfigured settings.
Understanding these threats empowers you to take proactive measures to mitigate them and protect your system.
Top Tools for Remote IoT SSH
Several tools are available to facilitate remote IoT SSH, each offering unique features and capabilities to meet diverse needs. Some of the top tools in the market include:
- OpenSSH: A widely used open-source SSH client and server, offering robust security and flexibility.
- Putty: A popular SSH client for Windows users, known for its simplicity and ease of use.
- Bitvise SSH Client: A feature-rich SSH client with advanced security features and user-friendly interface.
- SSH.NET: A .NET library for integrating SSH functionality into applications, ideal for developers.
Selecting the right tool depends on your specific requirements, technical expertise, and budget constraints.
Comparison of Tools
When evaluating tools for remote IoT SSH, consider the following factors to make an informed decision:
- Security features: Assess the level of security provided by each tool to protect your data.
- Ease of use: Choose a tool that aligns with your technical expertise and offers a user-friendly interface.
- Compatibility: Ensure the tool supports the platforms and devices you intend to use.
- Support and documentation: Opt for tools with comprehensive support and documentation to address any issues that may arise.
By carefully evaluating these factors, you can select the most suitable tool for your remote IoT SSH needs.
Troubleshooting Common Challenges
Despite careful planning, issues can still arise when setting up remote IoT SSH. Below are some common problems and their solutions:
- Connection Refused: Ensure the SSH server is running and the correct port is open to allow connections.
- Authentication Failed: Verify that the username and password/SSH key are accurate and correctly configured.
- Timeout Errors: Check network connectivity and firewall settings to resolve connection issues.
- Performance Issues: Optimize resource usage by disabling unnecessary services and processes.
Addressing these issues promptly can help maintain a stable and secure connection, ensuring uninterrupted access to your IoT devices.
Maximizing Performance
Optimizing the performance of remote IoT SSH is essential for ensuring smooth and efficient operations. Below are some strategies to enhance performance:
- Use data compression to reduce the size of transmitted data, improving transfer speeds.
- Limit the number of concurrent connections to prevent overloading the system and ensure stability.
- Disable unused services to free up resources and improve overall system performance.
- Regularly monitor performance metrics and make adjustments as needed to maintain optimal functionality.
Implementing these strategies can help you achieve a balance between performance and security, ensuring a seamless user experience.
Comparing Remote IoT SSH Solutions
Several remote IoT SSH solutions are available in the market, each catering to different needs and budgets. Below is a comparison of some popular solutions:
| Solution | Price | Features | Security |
|---|---|---|---|
| OpenSSH | Free | Basic SSH functionality with robust security features | High |
| Putty | Free | Simple interface, session management, and ease of use | Medium |
| Bitvise SSH Client | Paid | Advanced security features, SFTP support, and user-friendly interface | High |
| SSH.NET | Free | Library for integrating SSH functionality into applications, ideal for developers | High |
Selecting the right solution depends on your specific requirements, budget, and technical expertise. Carefully evaluating these factors can help you make an informed decision.
The Future of Remote IoT SSH
As technology continues to advance, the future of remote IoT SSH looks promising. Innovations in encryption, authentication, and resource optimization will further enhance the security and efficiency of remote IoT SSH. Additionally, the growing adoption of IoT devices across various industries will drive further innovation in this field.
Some potential future developments include:
- Quantum-resistant encryption to protect against emerging cyber threats.
- AI-driven threat detection and response systems to enhance security.
- Seamless integration with cloud platforms for enhanced scalability and flexibility.
- Enhanced usability and accessibility features to cater to a broader user base.
By staying informed about these advancements, you can prepare for the future of remote IoT SSH and leverage its full potential.
Conclusion
Remote IoT SSH is a powerful tool for securely and efficiently managing and monitoring IoT devices. By understanding its benefits, challenges, and best practices, you can harness its full potential to improve your operations. Whether you're a business owner, an IT professional, or a tech enthusiast, remote IoT SSH offers valuable capabilities that can enhance your productivity and security.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and related technologies.