Securing communication in remote IoT environments is fundamental to protecting sensitive data and maintaining system efficiency. As the Internet of Things (IoT) expands, the demand for robust security measures, such as SSH key management, becomes increasingly critical. This article delves into the best practices for managing SSH keys in remote IoT settings, offering actionable strategies to fortify your system's security.
In today’s hyper-connected world, IoT devices are frequently deployed in distant locations. These devices rely on secure communication channels to transmit and receive data. SSH keys play a pivotal role in establishing these secure connections, yet managing them effectively can be complex. This guide addresses the intricacies of remote IoT SSH key management, providing practical solutions to overcome common challenges.
Whether you are a developer, IT professional, or business owner, understanding the significance of SSH key management is crucial for safeguarding your IoT infrastructure. By implementing the strategies outlined in this article, you can ensure your systems remain secure and operational, even in the most remote and demanding environments.
Read also:Robert Benevides
Table of Contents
- Overview of SSH Key Management
- The Role of SSH Keys in IoT Security
- Strategies for Effective Remote IoT SSH Key Management
- Addressing Challenges in Remote SSH Key Management
- Leveraging Tools for Streamlined SSH Key Management
- Critical Security Considerations for SSH Key Management
- The Role of Automation in SSH Key Management
- Navigating Compliance and Regulatory Requirements
- Exploring Future Trends in Remote IoT SSH Key Management
- Conclusion and Next Steps
Overview of SSH Key Management
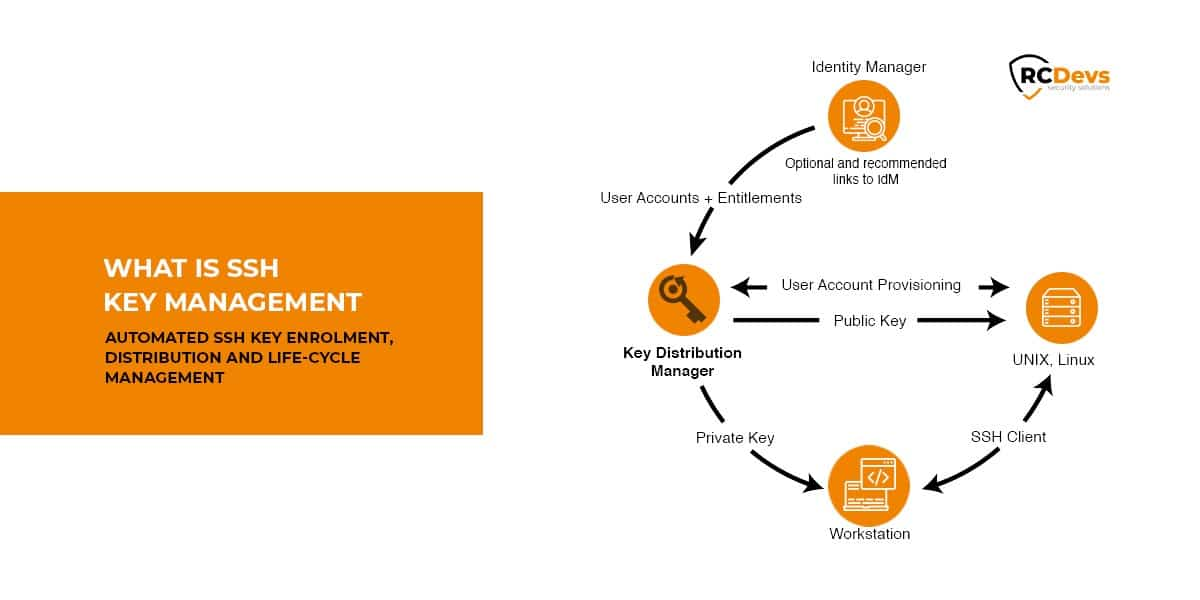
SSH (Secure Shell) is a cryptographic protocol designed to facilitate secure communication over potentially insecure networks. At the heart of this protocol lies SSH keys, which enable secure authentication without the need for passwords. In the context of IoT, SSH keys serve as the backbone for establishing secure connections between devices and servers, ensuring data confidentiality and integrity.
Proper SSH key management is indispensable for maintaining the security of IoT systems. Neglecting this critical aspect can expose your network to potential threats, turning SSH keys into liabilities. This section explores the foundational principles of SSH key management and its importance within the IoT landscape.
Understanding SSH Keys
SSH keys operate as a pair, consisting of a public key and a private key. The public key is shared with the server, while the private key remains securely stored on the client side. During the authentication process, the server verifies the client’s identity using the public key, ensuring a secure and authenticated connection. This mechanism eliminates the need for passwords, enhancing both security and usability.
Why SSH Keys Outperform Passwords
- SSH keys provide superior security compared to traditional passwords, significantly reducing the risk of brute-force attacks.
- They eliminate the burden of remembering complex passwords, improving user experience and reducing human error.
- SSH keys can be easily revoked or replaced if compromised, minimizing the impact of security breaches and ensuring ongoing protection.
The Role of SSH Keys in IoT Security
IoT devices often operate in remote and unsecured environments, making them particularly vulnerable to security threats. SSH keys offer a reliable method for securing communication between these devices and centralized servers. By adhering to SSH key management best practices, organizations can safeguard their IoT infrastructure from unauthorized access and potential data breaches.
This section examines the unique challenges faced in IoT environments and highlights how SSH keys can effectively address them, ensuring robust security and operational efficiency.
Securing Remote IoT Devices
Remote IoT devices are inherently susceptible to security threats due to their isolated locations and limited physical security measures. SSH keys play a vital role in mitigating these risks by ensuring that only authenticated devices and users gain access to the network. This layer of protection is essential for maintaining the integrity of IoT systems.
Read also:Brad Paisley Wife And Kids A Closer Look At The Country Stars Family Life
Scalability in IoT Networks
As IoT networks continue to expand, the demand for scalable security solutions becomes increasingly significant. SSH keys provide an efficient and scalable method for managing authentication across vast networks of devices. This ensures consistent security without compromising system performance or resource utilization.
Strategies for Effective Remote IoT SSH Key Management
Implementing best practices for SSH key management is crucial for maintaining the security and efficiency of your IoT systems. This section outlines key strategies to enhance your remote IoT SSH key management processes, ensuring optimal protection and operational performance.
Regular Key Rotation
Periodic key rotation is a critical practice for maintaining robust security. By updating SSH keys on a regular basis, you can minimize the risk of unauthorized access and ensure that compromised keys are promptly replaced. This proactive approach significantly strengthens your system’s defense mechanisms.
Key Storage and Access Control
Proper storage and access control of SSH keys are essential for preventing unauthorized use. Keys should be securely stored in encrypted repositories, with access strictly limited to authorized personnel. This can be achieved through the implementation of advanced key management systems and stringent access control policies, ensuring the highest level of security.
Monitoring and Auditing
Continuous monitoring and auditing of SSH key usage are vital for identifying potential security threats. By tracking key usage patterns and analyzing activity logs, organizations can detect suspicious behavior and take corrective action before it leads to a security breach. This proactive monitoring ensures the integrity of your SSH key management system.
Addressing Challenges in Remote SSH Key Management
Managing SSH keys in remote IoT environments presents unique challenges that must be addressed to ensure effective security. This section explores these challenges and provides practical solutions for overcoming them, enhancing the overall security of your IoT infrastructure.
Key Distribution in Remote Locations
Distributing SSH keys to remote IoT devices can be a complex and resource-intensive process, especially in areas with limited or unreliable connectivity. To address this challenge, organizations can implement automated key distribution systems that ensure keys are securely delivered to devices without requiring manual intervention. This not only improves efficiency but also enhances security by minimizing human error.
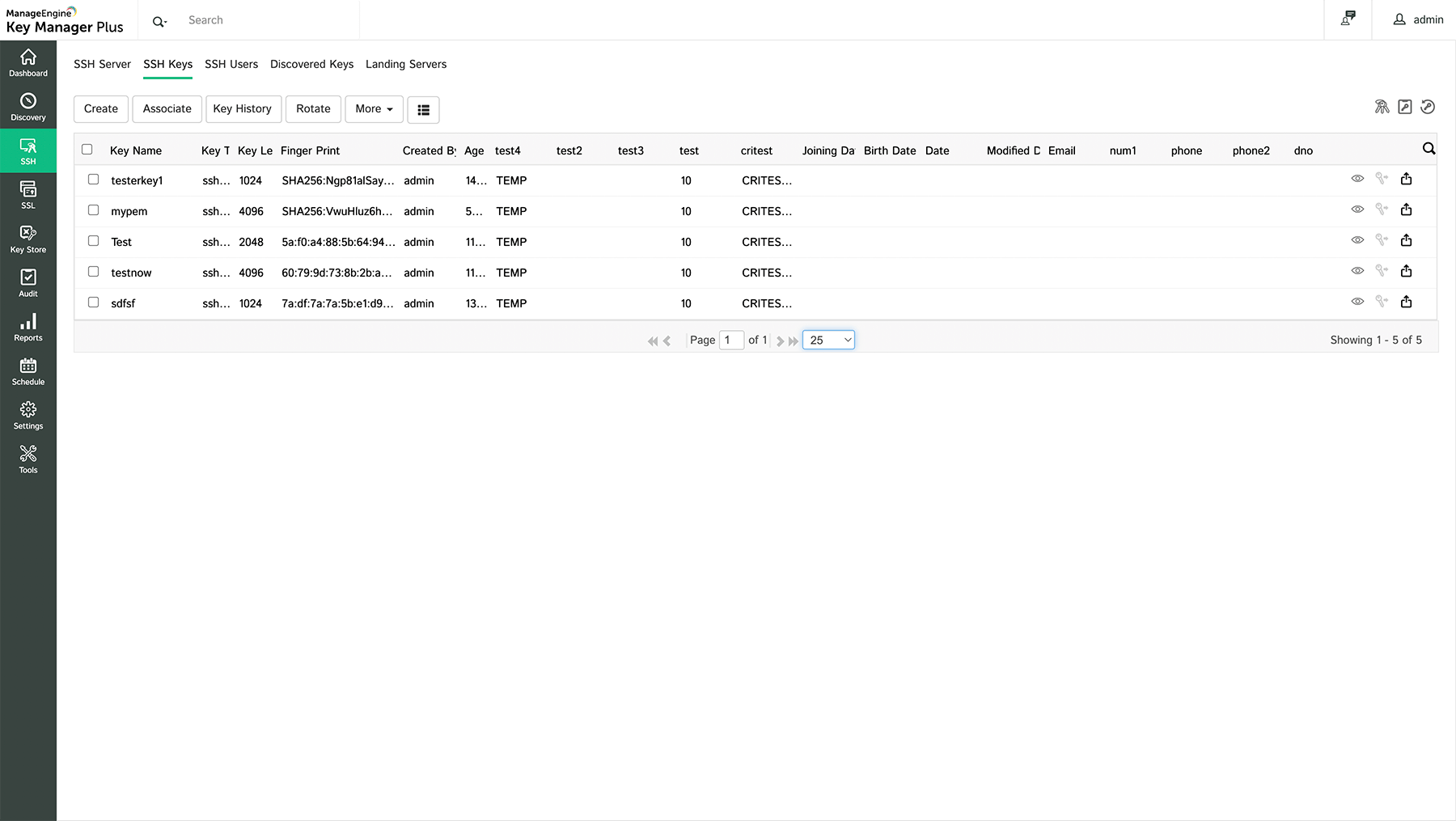
Managing Large Numbers of Keys
As IoT networks grow, the number of SSH keys required for secure communication increases exponentially. Managing these keys effectively demands robust systems and processes capable of handling large volumes without compromising security. Advanced key management platforms offer scalable solutions to meet this growing demand, ensuring consistent security across all devices.
Leveraging Tools for Streamlined SSH Key Management
A variety of tools and platforms are available to assist organizations in managing SSH keys more effectively. These tools provide features such as automated key rotation, secure storage, and comprehensive monitoring capabilities, significantly enhancing the efficiency and security of SSH key management processes.
Popular SSH Key Management Tools
- HashiCorp Vault: A widely recognized tool for managing secrets, including SSH keys, with advanced security features and robust automation capabilities.
- OpenSSH: A trusted open-source implementation of SSH that includes comprehensive key management functionalities, making it an ideal choice for organizations seeking cost-effective solutions.
- Keywhiz: A specialized tool designed for managing secrets and keys, offering features such as automated key rotation, access control, and detailed auditing capabilities to enhance security and compliance.
Critical Security Considerations for SSH Key Management
Security remains a top priority when managing SSH keys in remote IoT environments. This section discusses key security considerations and best practices for ensuring the integrity and reliability of your SSH key management system.
Protecting Against Key Leakage
Preventing key leakage is paramount for maintaining the security of your SSH key management system. This can be achieved through the use of secure key storage solutions, robust encryption techniques, and strict access control policies. By implementing these measures, organizations can significantly reduce the risk of unauthorized key access and potential data breaches.
Implementing Multi-Factor Authentication
Multi-factor authentication (MFA) adds an additional layer of security to SSH key management by requiring users to provide multiple forms of verification beyond just the key. This significantly reduces the risk of unauthorized access and enhances overall system security, making it an essential component of any comprehensive SSH key management strategy.
The Role of Automation in SSH Key Management
Automation plays a critical role in simplifying and enhancing SSH key management processes. By automating tasks such as key rotation, distribution, and monitoring, organizations can improve efficiency, reduce the risk of human error, and strengthen security measures.
Benefits of Automation
- Increased Efficiency: Automation streamlines key management processes, enabling organizations to handle large numbers of keys more effectively and efficiently.
- Reduced Risk of Human Error: By minimizing manual intervention, automation reduces the likelihood of mistakes that could compromise security or system performance.
- Enhanced Security: Automated monitoring and alert systems enable organizations to detect and respond to potential threats in real-time, ensuring the highest level of security.
Navigating Compliance and Regulatory Requirements
Compliance with industry standards and regulations is essential for organizations managing SSH keys in IoT environments. This section explores key compliance requirements and their implications for SSH key management, helping organizations align their practices with regulatory mandates.
Regulations Affecting SSH Key Management
- General Data Protection Regulation (GDPR): Requires organizations to implement robust security measures to protect personal data, emphasizing the importance of secure SSH key management practices.
- Payment Card Industry Data Security Standard (PCI DSS): Mandates secure authentication methods for systems handling payment card information, underscoring the critical role of SSH keys in ensuring compliance.
Exploring Future Trends in Remote IoT SSH Key Management
As technology continues to evolve, so do the methods and tools for managing SSH keys in remote IoT environments. This section examines emerging trends and innovations in SSH key management that are likely to shape the future of IoT security, offering insights into cutting-edge solutions and strategies.
Quantum-Resistant Cryptography
With the advent of quantum computing, traditional cryptographic methods may become vulnerable to sophisticated attacks. Quantum-resistant cryptography offers a promising solution by providing secure algorithms that are resilient against quantum-based threats, ensuring the long-term security of SSH key management systems.
Blockchain for Key Management
Blockchain technology presents a decentralized and secure approach to managing SSH keys. By leveraging blockchain, organizations can ensure the integrity and transparency of their key management processes, reducing the risk of tampering and unauthorized access. This innovative solution has the potential to revolutionize SSH key management in IoT environments.
Conclusion and Next Steps
In summary, effective remote IoT SSH key management is fundamental to ensuring the security and efficiency of your IoT systems. By implementing the strategies and leveraging the tools outlined in this guide, you can enhance the security of your SSH key management processes and protect your network from potential threats. Proactive management and continuous improvement are key to maintaining robust security in an ever-evolving digital landscape.
We encourage you to take action by sharing this article with your colleagues and exploring the tools and resources mentioned here. For further insights, check out our additional articles on IoT security and best practices for managing remote systems. Together, we can build a safer and more secure IoT ecosystem for everyone.