In today's interconnected world, the Internet of Things (IoT) has transformed the way we live and conduct business. IoT management platforms that incorporate SSH (Secure Shell) play a pivotal role in ensuring secure, reliable, and efficient communication between devices. With billions of devices connected globally, the secure and effective management of IoT networks has become a necessity rather than an option.
As the number of IoT devices continues to expand exponentially, the importance of robust IoT management platforms that leverage SSH cannot be overstated. These platforms provide advanced tools and features to safeguard networks, streamline operations, and enhance scalability. Whether you're managing a smart home or overseeing an enterprise-grade IoT infrastructure, understanding how SSH integrates into IoT management is essential for achieving success in the digital age.
This in-depth guide explores the significance of IoT management platforms, the critical role of SSH in securing IoT networks, and practical strategies for implementing these technologies. By the end of this article, you will have a comprehensive understanding of how to harness the power of IoT management platforms with SSH to protect and optimize your digital ecosystem.
Read also:What Happened To Carolin Bacic
Table of Contents
- Understanding IoT Management Platforms
- The Role of SSH in IoT Management
- Essential Features of IoT Management Platforms with SSH
- Advantages of Incorporating SSH in IoT Management
- Choosing the Right IoT Management Platform with SSH
- Securing IoT Networks with SSH
- Addressing Challenges in IoT Management with SSH
- Practical Applications of IoT Management Platforms with SSH
- The Future of IoT Management Platforms with SSH
- Conclusion
Understanding IoT Management Platforms
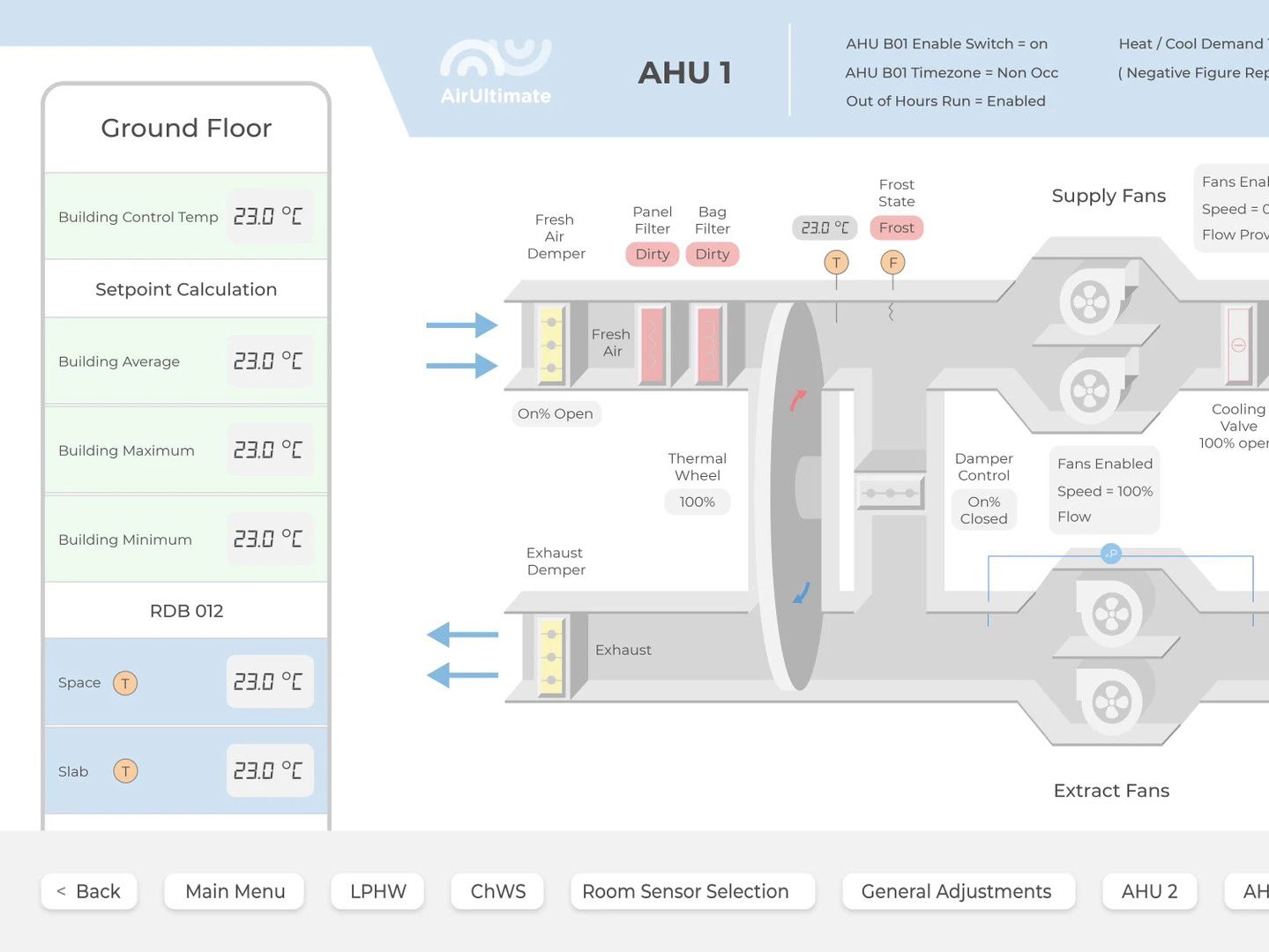
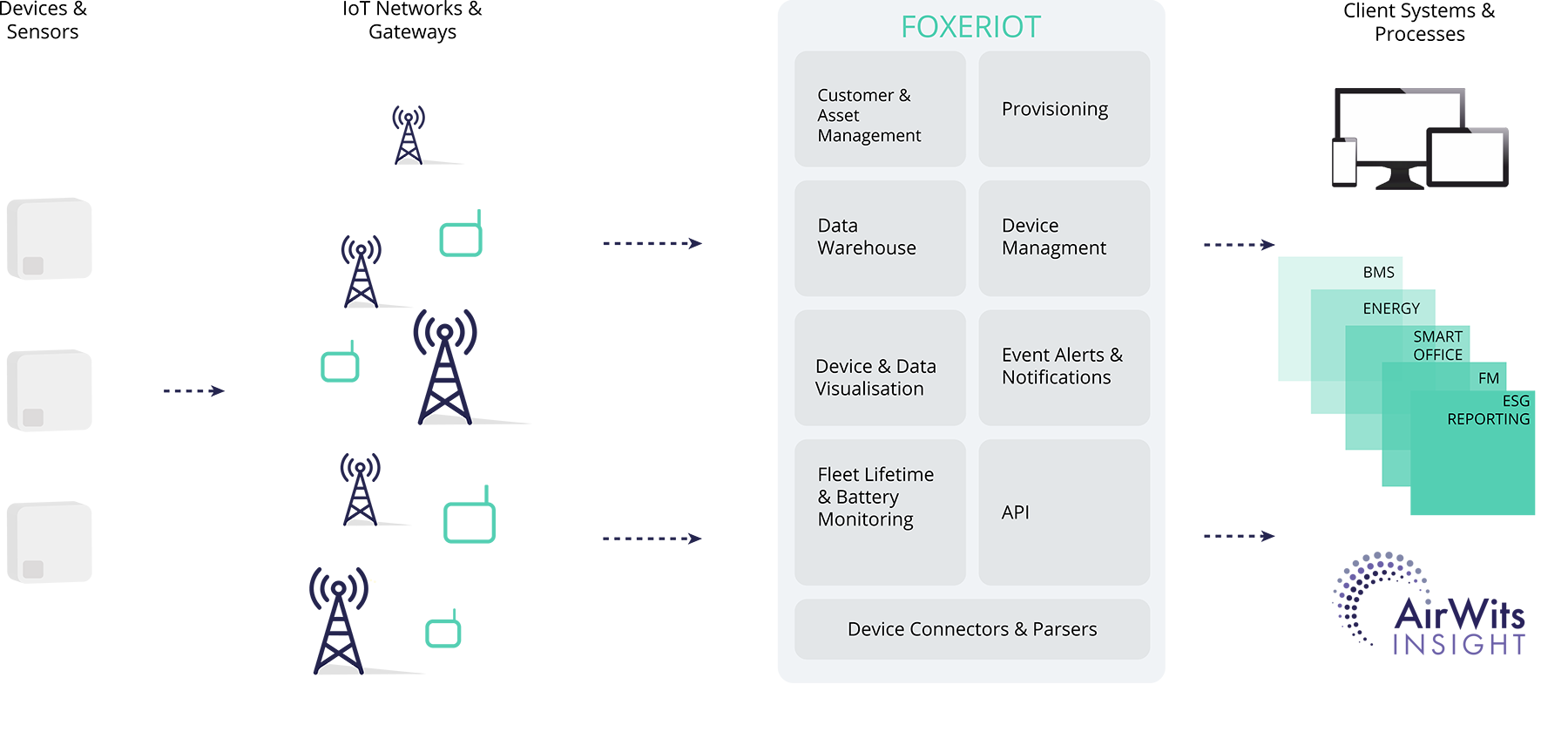
An IoT management platform serves as the central hub for monitoring, controlling, and optimizing IoT devices within a network. These platforms provide a suite of tools for device provisioning, data collection, firmware updates, and security management. By centralizing these functions, IoT management platforms simplify the complexities associated with managing large-scale IoT ecosystems.
These platforms are specifically designed to address the unique challenges posed by IoT networks, such as device heterogeneity, scalability, and security. The integration of SSH ensures secure communication channels between devices and the central server, enhancing the reliability and resilience of the network.
Core Components of IoT Management Platforms:
- Device Management: Provisioning, monitoring, and controlling IoT devices with precision.
- Data Analytics: Collecting and analyzing data from IoT devices to derive actionable insights.
- Security Features: Implementing robust security measures to protect IoT networks from cyber threats.
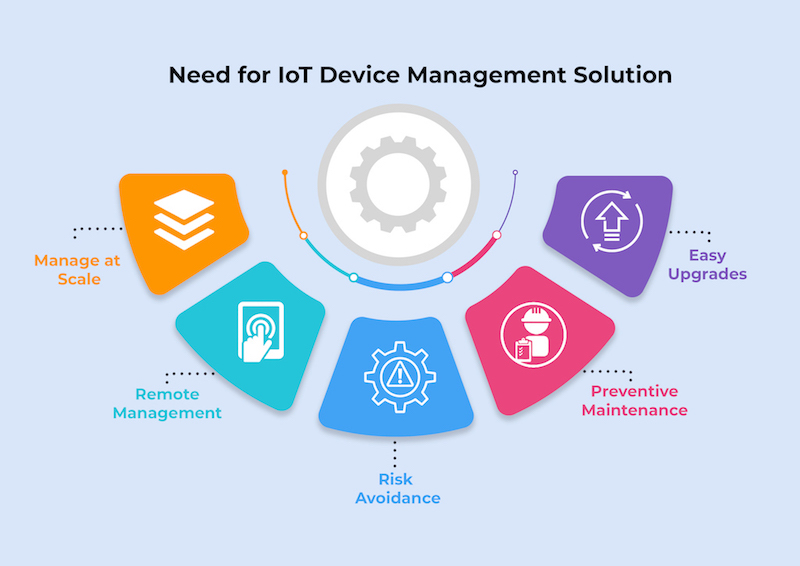
Why IoT Management Platforms Are Crucial
IoT networks can quickly become overwhelming without proper management. An IoT management platform ensures that devices remain connected, secure, and functional, even as the network expands. This is particularly vital in industries such as healthcare, manufacturing, and smart cities, where the reliability of IoT performance directly impacts operational success and safety.
The Role of SSH in IoT Management
SSH, or Secure Shell, is a cryptographic protocol that secures network communications. In the context of IoT management platforms, SSH plays a pivotal role in protecting sensitive data and ensuring secure interactions between devices. By encrypting data transmitted between devices and the central server, SSH minimizes the risk of cyberattacks, data breaches, and unauthorized access.
As IoT devices become increasingly integral to critical infrastructure, the need for robust security measures is more pressing than ever. SSH provides a secure channel for remote management, firmware updates, and data transfer, making it an indispensable component of IoT management platforms.
Read also:Kai Ryssdal Wife
How SSH Enhances IoT Security
- Encryption: Safeguards data in transit from interception and tampering.
- Authentication: Verifies the identity of users and devices to prevent unauthorized access.
- Integrity: Ensures the authenticity of transmitted data to prevent corruption and manipulation.
Essential Features of IoT Management Platforms with SSH
IoT management platforms that integrate SSH offer a range of advanced features designed to enhance security, scalability, and operational efficiency. These features empower organizations to manage their IoT networks effectively and securely, even as the complexity of the network grows.
Some of the most critical features include:
- Centralized Device Management: Streamline the monitoring and control of all connected devices from a unified dashboard.
- Secure Communication: Utilize SSH to encrypt all data transmissions between devices and the server, ensuring confidentiality and integrity.
- Remote Access: Enable secure remote management of IoT devices using SSH protocols, enhancing flexibility and convenience.
- Automated Updates: Schedule and deploy firmware updates securely across the network, minimizing downtime and vulnerabilities.
- Comprehensive Reporting: Generate detailed reports on device performance, network health, and security incidents for informed decision-making.
Advanced Security Features
In addition to SSH, modern IoT management platforms incorporate a variety of cutting-edge security features to protect against emerging threats. These include:
- Multi-Factor Authentication (MFA): Add an extra layer of security by requiring multiple forms of verification before granting access.
- Intrusion Detection Systems (IDS): Monitor network traffic for suspicious activity and potential threats in real time.
- Firewall Integration: Protect IoT networks from unauthorized access with integrated firewall capabilities, enhancing overall security.
Advantages of Incorporating SSH in IoT Management
The integration of SSH into IoT management platforms offers numerous benefits for organizations aiming to enhance the security and efficiency of their IoT networks. These advantages include:
- Enhanced Security: SSH ensures that all data transmissions are encrypted, significantly reducing the risk of cyberattacks and data breaches.
- Improved Scalability: SSH enables secure communication even as the number of connected devices grows, making it ideal for large-scale IoT deployments.
- Streamlined Operations: By simplifying remote management and automation, SSH reduces the time and effort required to maintain IoT networks, improving overall efficiency.
Organizations that adopt SSH in their IoT management strategies are better equipped to navigate the complexities of modern IoT ecosystems while maintaining stringent security standards.
Real-World Impact of SSH in IoT
Case studies from various industries highlight the tangible benefits of using SSH in IoT management. For instance, a healthcare provider implemented an IoT management platform with SSH to secure its medical devices, leading to improved patient outcomes and reduced downtime. Similarly, a manufacturing company leveraged SSH to streamline its production processes, resulting in increased efficiency and significant cost savings.
Choosing the Right IoT Management Platform with SSH
Selecting the appropriate IoT management platform with SSH can be challenging, given the multitude of options available. To make an informed decision, consider the following key factors:
- Scalability: Ensure the platform can accommodate your current and future IoT needs without compromising performance.
- Security Features: Look for platforms that offer robust security measures, including SSH and other advanced protocols, to safeguard your network.
- User Interface: Choose a platform with an intuitive and user-friendly interface to facilitate seamless navigation and management.
- Support and Documentation: Opt for platforms that provide comprehensive support and detailed documentation to maximize the value of your investment.
By carefully evaluating these factors, you can identify an IoT management platform that aligns with your specific requirements and supports your long-term objectives.
Evaluating Vendor Reputation
When selecting an IoT management platform, it is crucial to research the vendor's reputation and track record. Look for platforms offered by reputable vendors with a proven history of delivering reliable and secure solutions. Reading customer reviews and case studies can provide valuable insights into the platform's performance, usability, and customer satisfaction.
Securing IoT Networks with SSH
Integrating SSH into your IoT management strategy is a critical step in fortifying your network against potential threats. To maximize the security benefits of SSH, adhere to the following best practices:
- Use Strong Passwords: Ensure all SSH credentials are complex and unique to prevent unauthorized access.
- Enable Key-Based Authentication: Replace password-based authentication with more secure key-based methods to enhance security.
- Regularly Update SSH Software: Keep your SSH software up to date to protect against known vulnerabilities and emerging threats.
By following these guidelines, you can significantly enhance the security of your IoT network and reduce the risk of cyberattacks.
Common SSH Misconfigurations to Avoid
While SSH is a powerful tool for securing IoT networks, improper configuration can undermine its effectiveness. Common misconfigurations to avoid include:
- Using Default Credentials: Never use default usernames and passwords for SSH access, as they are easily exploited by attackers.
- Disabling Firewall Rules: Ensure firewall rules are properly configured to allow only necessary SSH traffic, preventing unauthorized access.
- Ignoring Security Updates: Regularly apply security patches and updates to address vulnerabilities and stay ahead of emerging threats.
Addressing Challenges in IoT Management with SSH
Despite its many advantages, implementing SSH in IoT management platforms can present several challenges. These challenges include:
- Complexity: Managing SSH keys and configurations across large IoT networks can be intricate and time-consuming, requiring specialized expertise.
- Compatibility: Ensuring compatibility between different devices and platforms can be a significant hurdle, especially in heterogeneous IoT ecosystems.
- Resource Constraints: Resource-constrained devices may struggle to support the computational overhead of SSH, necessitating optimization.
To overcome these challenges, organizations should invest in robust IoT management platforms that offer advanced tools and features to simplify SSH implementation and management.
Solutions to Common Challenges
Several strategies can help address the challenges associated with SSH in IoT management. These include:
- Automated Key Management: Use automated tools to simplify the management of SSH keys and configurations, reducing the burden on IT staff.
- Standardization: Adopt industry standards and best practices to ensure compatibility and interoperability across devices and platforms.
- Resource Optimization: Optimize SSH settings to minimize the impact on resource-constrained devices, ensuring seamless operation.
Practical Applications of IoT Management Platforms with SSH
IoT management platforms with SSH are being utilized in a variety of industries to enhance security, efficiency, and performance. Some notable examples include:
- Healthcare: Securely managing medical devices and patient data to improve healthcare outcomes and ensure compliance with regulations.
- Manufacturing: Streamlining production processes and reducing downtime through real-time monitoring and control of IoT devices.
- Smart Cities: Enabling the secure and efficient operation of smart infrastructure, such as traffic management systems, public lighting, and environmental monitoring.
These applications demonstrate the versatility and value of IoT management platforms with SSH across diverse industries, driving innovation and operational excellence.
Success Stories
Many organizations have achieved remarkable success by leveraging IoT management platforms with SSH. For example, a smart city initiative in Europe used SSH to secure its IoT network, resulting in improved public safety, reduced operational costs, and enhanced quality of life for residents. Similarly, a global manufacturing company implemented SSH in its IoT management strategy, leading to increased productivity, improved security, and a competitive edge in the market.
The Future of IoT Management Platforms with SSH
As IoT continues to evolve, the role of SSH in IoT management platforms is expected to become even more significant. Emerging technologies such as 5G, edge