In today's highly interconnected world, remote IoT device access has emerged as a cornerstone of modern technology. From enhancing the functionality of smart homes to driving innovation in industrial automation, the ability to remotely manage and monitor IoT devices is revolutionizing industries and enriching the user experience. This comprehensive guide will explore the nuances of remote IoT device access, covering its advantages, challenges, and best practices, along with essential security measures to safeguard your network.
As technological advancements continue to reshape the landscape of innovation, the Internet of Things (IoT) stands out as one of the most transformative developments of our era. It seamlessly connects everyday objects to the internet, empowering them to exchange data and operate autonomously. At the heart of this ecosystem lies remote IoT device access, enabling users to control and interact with devices from virtually anywhere on the globe.
This article will provide an in-depth exploration of remote IoT device access, encompassing its diverse applications, potential challenges, and strategies for ensuring secure connectivity. Whether you are a tech enthusiast eager to learn more, a business owner seeking to optimize operations, or an IT professional aiming to enhance network security, this guide will equip you with the knowledge needed to fully leverage the capabilities of remote IoT device access.
Read also:Is Park Bo Gum Married
Table of Contents
- Understanding Remote IoT Device Access
- Advantages of Remote IoT Device Access
- Addressing Challenges in Remote IoT Device Access
- Enhancing Security for Remote IoT Access
- Key Protocols in Remote IoT Device Access
- Essential Tools and Platforms for Remote IoT Access
- Best Practices for Remote IoT Device Access
- Practical Applications of Remote IoT Device Access
- Emerging Trends in Remote IoT Device Access
- Conclusion
Understanding Remote IoT Device Access
Remote IoT device access refers to the capability of connecting, monitoring, and controlling IoT devices from a distant location. This functionality is achieved through the integration of cloud platforms, advanced networking protocols, and sophisticated software solutions. By facilitating remote access, businesses and individuals can significantly enhance operational efficiency, minimize costs, and streamline workflows.
At its foundation, remote IoT device access empowers users to interact with a variety of devices, such as sensors, actuators, and controllers, without the need for physical presence. This capability is particularly advantageous in industries like healthcare, manufacturing, and agriculture, where real-time monitoring and control are crucial for success.
Why Remote IoT Device Access is Crucial
As the adoption of IoT devices continues to grow at an unprecedented rate, the demand for effective remote access solutions has surged accordingly. According to a report by Statista, the global IoT market is projected to reach a staggering $1.6 trillion by 2025. This rapid expansion underscores the necessity of developing robust and secure remote IoT access solutions to meet the evolving needs of businesses and consumers.
Advantages of Remote IoT Device Access
Remote IoT device access offers a multitude of benefits that make it an indispensable tool for modern organizations. Below are some of the most prominent advantages:
- Boosted Efficiency: By enabling remote monitoring and control, businesses can significantly streamline their operations, reducing downtime and improving overall productivity.
- Cost Reduction: Remote access eliminates the need for frequent on-site visits, resulting in substantial cost savings for businesses.
- Scalability: IoT devices can be effortlessly added or removed from a network, allowing businesses to scale their operations as needed without compromising performance.
- Enhanced Security: When paired with appropriate security measures, remote IoT device access can effectively safeguard sensitive data and prevent unauthorized access.
Addressing Challenges in Remote IoT Device Access
Despite its numerous benefits, remote IoT device access also presents several challenges that must be carefully addressed. These challenges include:
1. Security Vulnerabilities
IoT devices are often susceptible to cyberattacks, making security a top priority for remote access solutions. Hackers can exploit vulnerabilities in device firmware, communication protocols, or network configurations to gain unauthorized access, potentially compromising sensitive information.
Read also:Wes Bentley
2. Connectivity Constraints
Reliable network connectivity is essential for the optimal performance of remote IoT device access systems. Factors such as limited bandwidth, signal interference, and network congestion can all negatively impact the reliability and efficiency of remote connections.
3. Complexity of Deployment
Setting up a secure and efficient remote IoT device access system can be a complex undertaking, requiring specialized knowledge and expertise. Businesses may need to invest in training programs, advanced tools, and robust infrastructure to ensure seamless implementation.
Enhancing Security for Remote IoT Access
Ensuring the security of remote IoT device access is paramount to protecting sensitive data and preventing unauthorized access. Below are some critical security considerations:
- Authentication: Implement strong authentication mechanisms, such as multi-factor authentication, to reliably verify user identities and enhance system security.
- Encryption: Utilize encryption protocols, such as TLS or SSL, to secure the transmission of data between devices and remote access systems, safeguarding against potential breaches.
- Firewalls and Intrusion Detection Systems: Deploy firewalls and intrusion detection systems to actively monitor and protect networks from potential threats, ensuring the integrity of the system.
- Regular Updates: Ensure that IoT devices and associated software are consistently updated with the latest security patches and firmware updates to address emerging vulnerabilities.
Key Protocols in Remote IoT Device Access
A variety of communication protocols are commonly employed in remote IoT device access systems. These protocols enable devices to exchange data securely and efficiently. Among the most widely used protocols are:
1. MQTT (Message Queuing Telemetry Transport)
MQTT is a lightweight messaging protocol specifically designed for use in low-bandwidth, high-latency networks. Its simplicity and efficiency have made it a popular choice for IoT applications where resource constraints are a concern.
2. CoAP (Constrained Application Protocol)
CoAP is a specialized web transfer protocol tailored for use with constrained devices and networks. It is particularly well-suited for IoT applications where resources are limited, offering reliable communication capabilities.
3. HTTP/HTTPS
HTTP and HTTPS are standard protocols used for web communication. Although not as lightweight as MQTT or CoAP, they are widely supported and can be effectively utilized for secure remote IoT device access, ensuring compatibility and reliability.
Essential Tools and Platforms for Remote IoT Access
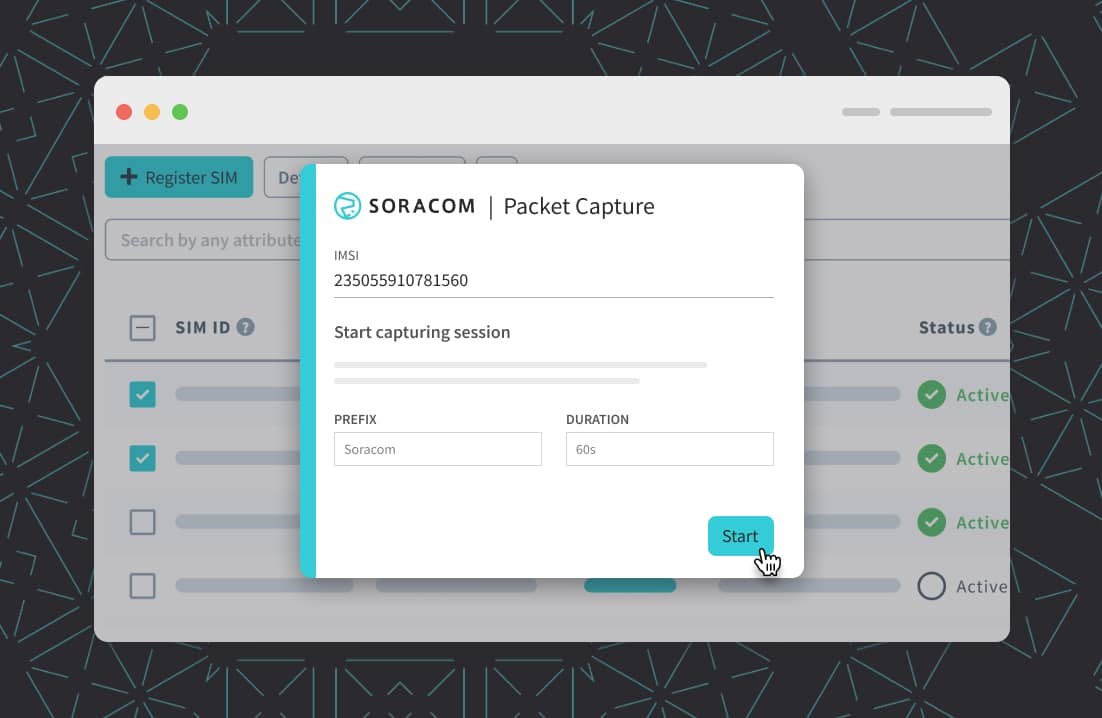
A range of tools and platforms are available to facilitate remote IoT device access, providing users with the resources needed to manage and monitor their IoT devices from anywhere in the world. Some of the most prominent options include:
- Amazon Web Services IoT Core: A cloud-based platform that enables secure and scalable IoT device management, offering a comprehensive suite of tools to streamline operations.
- Microsoft Azure IoT Hub: A fully managed service that allows users to seamlessly connect, monitor, and manage IoT devices at scale, enhancing operational efficiency and security.
- IBM Watson IoT Platform: A robust platform that provides advanced analytics, device management, and integration capabilities, empowering businesses to unlock the full potential of their IoT infrastructure.
Best Practices for Remote IoT Device Access
To ensure the successful implementation of remote IoT device access, it is vital to adhere to established best practices. Below are some key recommendations:
1. Comprehensive Planning and Design
Prior to implementing a remote IoT device access system, it is essential to meticulously plan and design the architecture. This process should focus on ensuring scalability, security, and reliability, laying a solid foundation for long-term success.
2. Adoption of Standardized Protocols
Employing standardized communication protocols is crucial for ensuring compatibility and interoperability between devices and systems. This approach promotes seamless integration and enhances the overall effectiveness of the system.
3. Continuous Monitoring and Maintenance
Regularly monitoring and maintaining your remote IoT device access system is essential for identifying and addressing potential issues before they escalate into critical problems. This proactive approach helps to ensure the ongoing stability and security of the system.
Practical Applications of Remote IoT Device Access
Remote IoT device access finds application across a wide array of industries, offering innovative solutions to diverse challenges. Some of the most notable applications include:
1. Smart Homes
Remote IoT device access empowers homeowners to effortlessly control smart home devices such as thermostats, lighting systems, and security cameras from anywhere in the world, enhancing convenience and security.
2. Industrial Automation
In the manufacturing sector, remote IoT device access allows engineers to monitor and control machinery and production processes in real-time, optimizing efficiency, reducing downtime, and improving overall productivity.
3. Healthcare
Remote IoT device access is transforming the healthcare industry by enabling remote patient monitoring, telemedicine, and real-time data analysis, enhancing patient care and outcomes.
Emerging Trends in Remote IoT Device Access
As technology continues to evolve, several trends are poised to shape the future of remote IoT device access. These trends include:
- Edge Computing: By processing data closer to the source, edge computing can significantly reduce latency and enhance the performance of remote IoT device access systems, offering faster and more reliable connections.
- Artificial Intelligence: AI-powered analytics can revolutionize remote IoT device access by delivering deeper insights, enabling predictive maintenance, and enhancing the overall capabilities of the system.
- 5G Networks: The deployment of 5G networks promises to transform remote IoT device access by providing unprecedented speeds and lower latency, paving the way for more advanced applications and use cases.
Conclusion
Remote IoT device access has become an integral component of modern technology, empowering users to monitor and control IoT devices from virtually anywhere in the world. This guide has explored the advantages, challenges, and best practices associated with remote IoT device access, as well as its diverse applications and future trends.
To fully harness the potential of remote IoT device access, it is imperative to prioritize security, adopt standardized protocols, and adhere to established best practices. By doing so, businesses and individuals can unlock the full potential of IoT technology, driving innovation and achieving success in their respective fields.
We invite you to share your thoughts and experiences with remote IoT device access in the comments section below. Additionally, feel free to explore other articles on our website for further insights into the fascinating world of IoT and technology.