In today's highly interconnected world, ensuring secure communication between IoT devices and routers has become more important than ever. Configuring SSH for IoT devices plays a pivotal role in safeguarding your network and devices. Whether you're a tech enthusiast or a professional, understanding how to set up SSH for IoT devices will significantly enhance your cybersecurity skills and knowledge.
As the Internet of Things (IoT) continues to expand, the demand for secure communication channels has grown exponentially. SSH (Secure Shell) provides a robust, encrypted method for accessing and managing IoT devices via routers, effectively minimizing the risks of unauthorized access and data breaches. This protocol ensures that your devices remain secure while exchanging critical information.
This article delves into everything you need to know about setting up SSH for IoT devices and routers. From basic concepts to advanced configurations, you'll gain a comprehensive understanding of how to secure your IoT ecosystem effectively and efficiently.
Read also:Honeytoon Teach Me First Free Your Ultimate Guide To Learning Korean With Fun And Interactive Comics
Table of Contents
- Understanding SSH
- IoT Devices and Routers: An Overview
- Why SSH Is Crucial for IoT Security
Preparing Your Environment for SSH IoT Setup
- Step-by-Step Guide to SSH IoT Device Router Setup
- Resolving Common SSH IoT Issues
- Advanced Security Measures for SSH IoT
- Best Practices for SSH IoT Device Router Setup
Real-World Applications of SSH IoT
- Future Trends in SSH IoT Device Router Setup
- Conclusion
Understanding SSH
SSH, or Secure Shell, is a cryptographic network protocol designed to secure communication between two networked devices. It creates a secure channel over an unsecured network, ensuring that all data exchanged between devices remains private and tamper-proof. SSH is widely used across industries for remote server management, file transfers, and secure communication. For IoT devices, SSH serves as an indispensable tool for protecting sensitive information transmitted between devices and routers.
With its robust encryption and authentication mechanisms, SSH ensures that unauthorized parties cannot intercept or manipulate the data being transmitted. This makes it an ideal solution for securing IoT ecosystems, where devices often handle critical and sensitive information.
IoT Devices and Routers: An Overview
IoT devices are smart gadgets designed to collect, send, and receive data. These devices rely on routers to connect to the internet and communicate with other systems. A router acts as the central hub for managing network traffic, ensuring seamless connectivity and efficient communication between devices. However, as IoT ecosystems continue to grow, so do the potential security risks.
When setting up IoT devices, it's essential to implement robust security measures to protect against potential threats. Configuring SSH for IoT devices and routers ensures that all communication remains encrypted and secure, reducing the likelihood of unauthorized access or data breaches.
Why SSH Is Crucial for IoT Security
Security is paramount when managing IoT ecosystems. SSH plays a vital role in addressing several security concerns by:
- Encrypting all data transmissions to prevent eavesdropping and data interception.
- Authenticating devices and users to ensure only authorized parties can access the network.
- Providing a secure method for remotely managing IoT devices, allowing administrators to perform maintenance and updates without compromising security.
By implementing SSH, you can significantly reduce the risk of cyberattacks and data breaches, ensuring the integrity and reliability of your IoT network.
Read also:Irene Banerjee
Preparing Your Environment for SSH IoT Setup
Before configuring SSH for your IoT devices and router, it's crucial to ensure that your environment is properly prepared. Follow these steps to set the stage for a successful SSH setup:
1. Update your router's firmware to the latest version. This ensures optimal security and performance, protecting your network from known vulnerabilities.
2. Verify that your IoT devices support SSH and have the necessary software installed. If required, install or update the SSH client or server software on your devices.
3. Create a secure password or implement key-based authentication for SSH access. This adds an extra layer of security, making it more difficult for unauthorized users to gain access.
Step-by-Step Guide to SSH IoT Device Router Setup
Setting up SSH for your IoT devices and router involves several steps. Follow this comprehensive guide to configure SSH effectively:
Step 1: Accessing the Router
Begin by logging in to your router's admin panel using the default IP address (e.g., 192.168.1.1) and credentials. Once logged in, navigate to the security settings and enable SSH access. This step ensures that your router is ready to establish secure connections with your IoT devices.
Step 2: Installing SSH Server
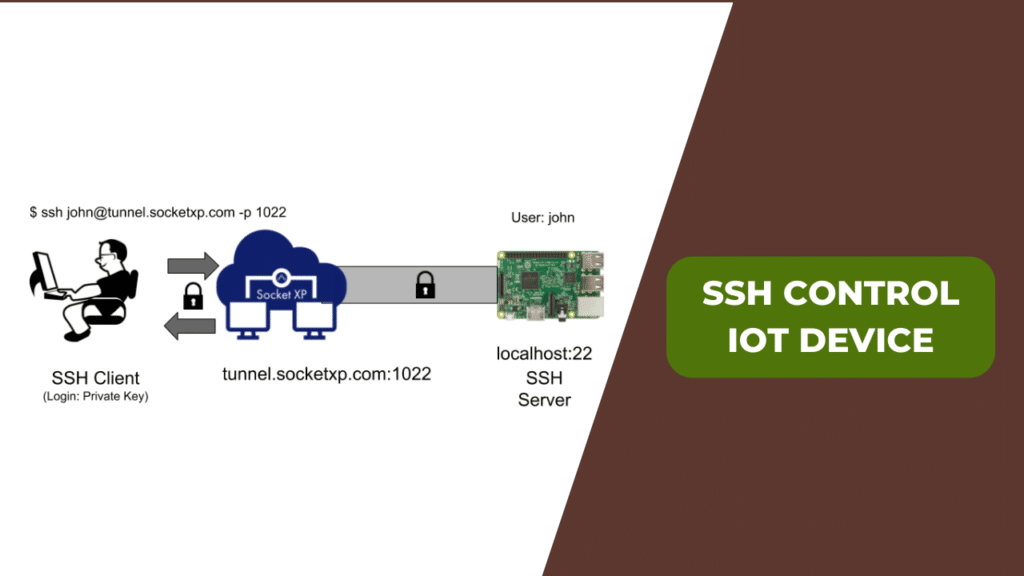
Next, install an SSH server on your IoT device. For Linux-based devices, OpenSSH is a popular choice, while Windows devices may require third-party software like PuTTY. Ensure that the SSH server is properly installed and configured to meet your specific needs.
Step 3: Configuring SSH
Edit the SSH configuration file, typically located at /etc/ssh/sshd_config, to customize settings such as the port number, authentication methods, and access permissions. This step allows you to fine-tune the SSH setup to align with your security requirements and operational preferences.
Step 4: Testing the Connection
Finally, use an SSH client to test the connection between your IoT device and router. Ensure that communication is secure and functioning correctly. This step confirms that your SSH setup is complete and operational.
Resolving Common SSH IoT Issues
During the SSH IoT device router setup process, you may encounter challenges. Here are some common issues and their solutions:
- Connection Refused: Verify that the SSH service is running on both the router and IoT device. Check the service status and restart it if necessary.
- Authentication Failed: Double-check your username, password, and key-based authentication settings. Ensure that all credentials are correct and properly configured.
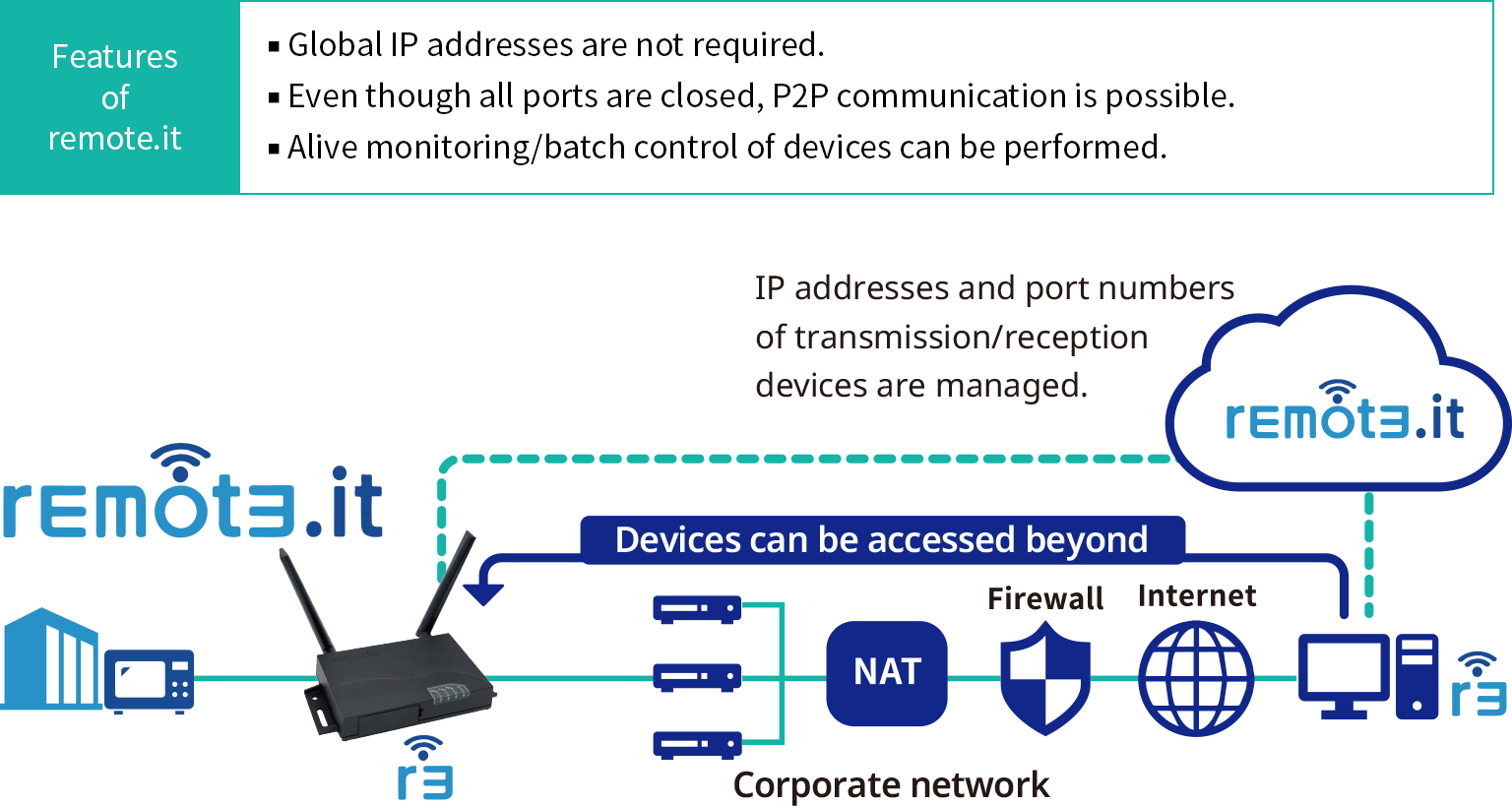
- Network Issues: Confirm that both devices are connected to the same network and that no firewalls are blocking the SSH port. Adjust network settings as needed to resolve connectivity problems.
Advanced Security Measures for SSH IoT
To further enhance the security of your SSH IoT device router setup, consider implementing the following advanced measures:
- Disable password-based authentication and switch to key-based authentication for increased security.
- Change the default SSH port to a non-standard port number to reduce the risk of automated attacks.
- Limit access to specific IP addresses using firewall rules, restricting who can connect to your devices.
Best Practices for SSH IoT Device Router Setup
Adopting best practices ensures a secure and efficient SSH IoT device router setup. Follow these guidelines to maximize security and performance:
- Regularly update your router and IoT device firmware to protect against newly discovered vulnerabilities.
- Monitor network activity for suspicious behavior, allowing you to quickly identify and respond to potential threats.
- Document your SSH configuration for future reference, making it easier to troubleshoot issues and maintain consistency across your network.
Real-World Applications of SSH IoT
SSH IoT device router setup has practical applications in various industries, including:
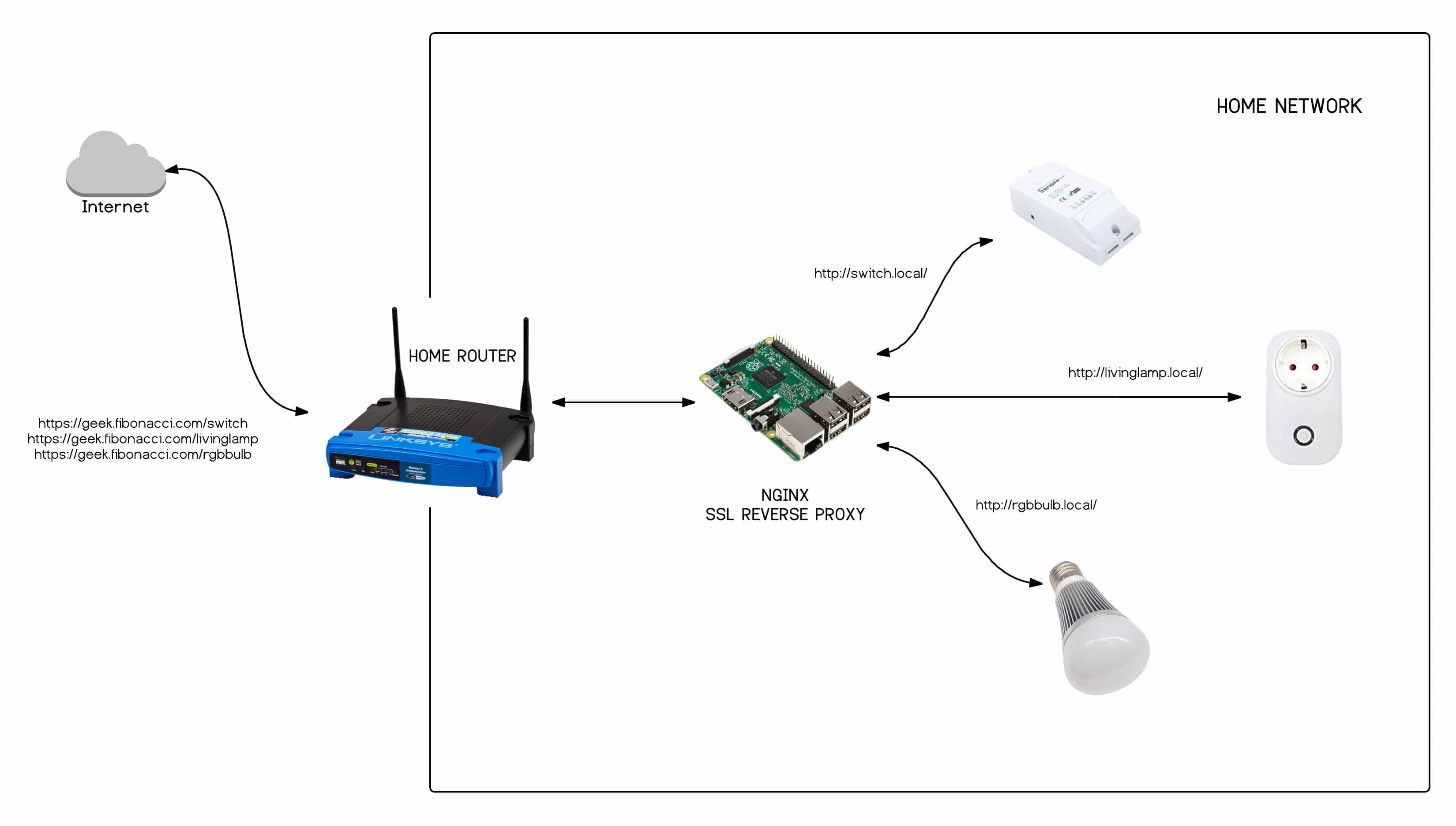
- Smart Homes: Secure communication between smart appliances and home routers, ensuring that all devices remain protected and functional.
- Industrial Automation: Protect data transmissions in manufacturing environments, safeguarding critical processes and equipment.
- Healthcare: Ensure the privacy and integrity of medical devices and patient information, maintaining compliance with industry regulations.
Future Trends in SSH IoT Device Router Setup
As technology continues to evolve, SSH IoT device router setup will adapt to address emerging security challenges. Future trends include:
- Integration with blockchain technology to enhance security and provide tamper-proof transaction records.
- AI-driven threat detection and response systems, enabling proactive identification and mitigation of potential threats.
- Quantum-resistant encryption methods, ensuring long-term security in the face of advancements in quantum computing.
Conclusion
Configuring SSH for IoT devices and routers is a critical step in securing your IoT ecosystem. By following the steps outlined in this guide, you can ensure that your devices and network remain protected from potential threats. Whether you're managing a smart home, industrial automation system, or healthcare network, SSH provides the foundation for secure and reliable communication.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore other articles on our site to deepen your understanding of cybersecurity and IoT technologies. Together, we can create a safer and more secure digital future.