The integration of IoT remote SSH server technology has transformed the way we interact with devices and systems remotely. As the Internet of Things (IoT) continues to expand exponentially, the demand for secure and reliable remote access solutions has skyrocketed. An IoT remote SSH server empowers users to manage and control their devices from virtually any location, ensuring seamless connectivity while upholding stringent security protocols.
In today's hyper-connected world, where the number of connected devices is growing at an unprecedented rate, businesses and individuals require robust systems to monitor and manage their networks effectively. IoT remote SSH server solutions provide an exceptional means to achieve this objective. By utilizing Secure Shell (SSH) protocols, these systems establish encrypted communication channels, safeguarding sensitive data during transmission and offering peace of mind to users.
This article delves deep into the intricacies of IoT remote SSH servers, exploring their functionalities, benefits, and implementation strategies. Whether you're a network administrator, a developer, or a tech enthusiast, understanding the inner workings of IoT remote SSH servers is essential for optimizing your IoT infrastructure and ensuring its long-term success.
Read also:Pepper0 Family The Ultimate Guide To Their Impactful Journey And Achievements
Table of Contents
- Understanding IoT Remote SSH Servers
- What Is SSH and Why Is It Vital?
- Key Benefits of IoT Remote SSH Servers
- Advanced Security Features of IoT Remote SSH Servers
- Deploying an IoT Remote SSH Server
- Best Practices for Managing IoT Remote SSH Servers
- Addressing Common Challenges and Troubleshooting
- IoT Remote SSH Servers Across Industries
- Emerging Trends in IoT Remote SSH Technology
- Final Thoughts and Next Steps
Understanding IoT Remote SSH Servers
An IoT remote SSH server functions as a critical bridge, enabling secure communication and management between users and their IoT devices from remote locations. The rapid proliferation of IoT devices has intensified the need for efficient and secure methods of accessing and controlling these devices. Secure Shell (SSH), initially designed for secure network communication, has emerged as a cornerstone in IoT remote access solutions, offering unparalleled security and reliability.
SSH employs encryption to protect data in transit, ensuring that sensitive information remains shielded from unauthorized access. For IoT applications, where security is non-negotiable, an IoT remote SSH server provides a dependable way to manage devices without compromising safety. Understanding the foundational principles of SSH and its application within IoT environments is indispensable for anyone seeking to implement remote access capabilities effectively.
This section explores the basic concepts of SSH and explains why it is an essential component of modern IoT setups, setting the stage for a deeper dive into its capabilities and applications.
What Is SSH and Why Is It Vital?
Secure Shell (SSH) is a cryptographic network protocol designed to facilitate secure communication over unsecured networks. Since its inception in 1995, SSH has become a globally recognized standard for remote access and command execution. Its significance stems from its ability to provide secure authentication and encrypted data transfer, making it an indispensable tool in today's interconnected world.
For IoT remote SSH servers, the protocol ensures that commands sent to devices and data received from them are protected against interception and tampering. This feature is especially crucial in industries such as healthcare, finance, and manufacturing, where data security is of utmost importance. By safeguarding sensitive information, SSH plays a pivotal role in maintaining the integrity and confidentiality of IoT ecosystems.
SSH operates on port 22 by default and supports various authentication methods, including password-based and public key authentication. Public key authentication, in particular, enhances security by eliminating the need for passwords, thereby reducing the risk of brute-force attacks and unauthorized access.
Read also:Scott Wapner Wife
Key Benefits of IoT Remote SSH Servers
Implementing an IoT remote SSH server offers a multitude of advantages that cater to both individual users and large-scale organizations. Below, we explore some of the most significant benefits of adopting this technology:
- Enhanced Security: SSH encrypts all data transmitted between the client and server, providing a robust defense against eavesdropping, man-in-the-middle attacks, and other malicious activities.
- Reliability: SSH connections are highly stable and can be configured to reconnect automatically in the event of network disruptions, ensuring continuous access to critical systems and data.
- Scalability: IoT remote SSH servers are designed to handle multiple devices simultaneously, making them ideal for large-scale deployments across diverse industries.
- Cost-Effectiveness: By enabling remote management, businesses can significantly reduce the need for on-site maintenance, resulting in substantial cost savings and improved operational efficiency.
These benefits underscore the importance of IoT remote SSH servers in modern IoT ecosystems, empowering users to manage their devices securely and efficiently.
Advanced Security Features of IoT Remote SSH Servers
Security forms the backbone of IoT remote SSH server functionality. To ensure comprehensive protection, these servers incorporate a range of advanced security features that address potential vulnerabilities and mitigate risks:
The key security features include:
- Encryption: SSH employs state-of-the-art encryption algorithms, such as AES and RSA, to secure data during transmission, ensuring that sensitive information remains protected at all times.
- Authentication: Multi-factor authentication and public key infrastructure (PKI) enhance access control, preventing unauthorized access and ensuring that only trusted users can interact with the system.
- Firewall Integration: IoT remote SSH servers can be seamlessly integrated with firewalls, enabling administrators to restrict access to trusted sources and further bolstering the system's security posture.
- Logging and Monitoring: Comprehensive logging capabilities allow administrators to track all activities on the server, facilitating forensic analysis and ensuring compliance with regulatory requirements.
By combining these features, IoT remote SSH servers create a secure and resilient environment for managing IoT devices, safeguarding against potential threats and ensuring the integrity of connected systems.
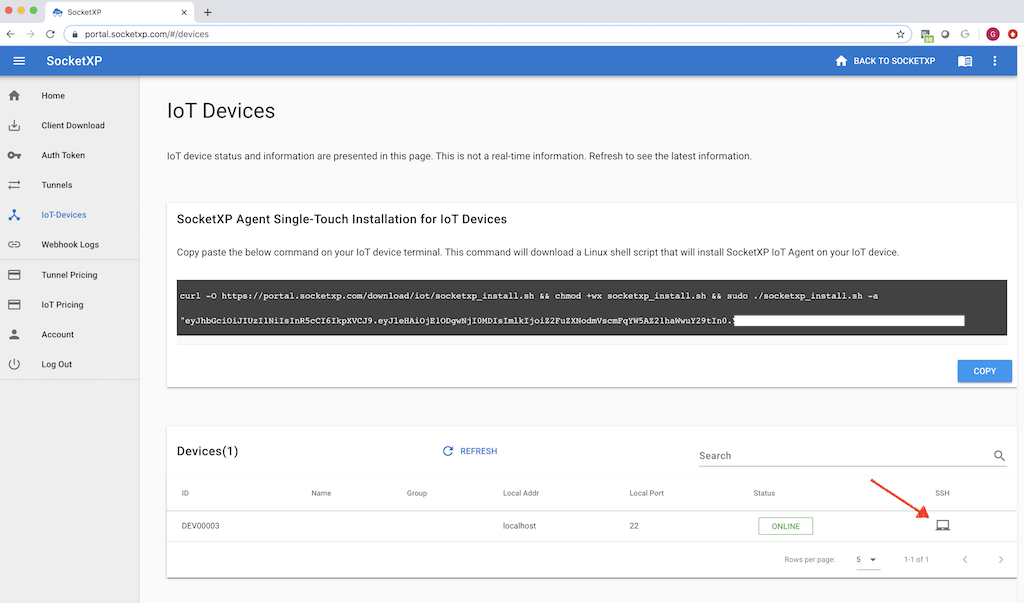
Deploying an IoT Remote SSH Server
Essential Hardware Requirements
Before embarking on the deployment of an IoT remote SSH server, it is crucial to ensure that your hardware meets the necessary specifications. The server must be capable of handling the expected workload, including managing multiple devices and processing encrypted data efficiently. Key considerations when selecting hardware include:
- Processor: Multi-core processors are recommended to enhance performance and ensure smooth operation under heavy workloads.
- Memory: Sufficient RAM is essential to support concurrent connections and maintain optimal server performance.
- Storage: Adequate disk space is necessary for storing logs, configuration files, and other critical data, ensuring that the server remains functional over time.
Choosing the right hardware is a critical step in ensuring the stability and efficiency of your IoT remote SSH server, laying the foundation for a successful deployment.
Configuring the Software
With the hardware in place, the next step involves configuring the software to align with your specific requirements. This process includes installing the SSH server software and setting up the necessary configurations. Popular SSH server implementations, such as OpenSSH and Dropbear, are widely supported and offer user-friendly interfaces for configuration.
Configuration steps typically encompass:
- User Accounts and Permissions: Establishing user accounts with appropriate permissions to ensure secure access and prevent unauthorized activities.
- Firewall Rules: Configuring firewall rules to allow SSH traffic while restricting access to unauthorized sources, enhancing the server's overall security.
- Public Key Authentication: Enabling public key authentication to provide a secure and password-less method of access, reducing the risk of brute-force attacks and enhancing convenience for authorized users.
Proper software configuration is vital for maximizing the server's functionality and ensuring that it operates securely and efficiently.
Best Practices for Managing IoT Remote SSH Servers
To ensure optimal performance and security, adhering to best practices is essential. Below are some recommended strategies for managing IoT remote SSH servers effectively:
- Regular Updates: Keeping the server software and firmware up to date is crucial for protecting against vulnerabilities and ensuring compatibility with the latest security protocols.
- Access Control: Limiting access to authorized personnel only and implementing strong authentication mechanisms are critical steps in maintaining the server's security and preventing unauthorized access.
- Monitoring: Continuously monitoring server activities enables administrators to detect and respond to potential threats promptly, minimizing the risk of data breaches and ensuring the system's integrity.
Implementing these best practices helps ensure that your IoT remote SSH server operates at peak performance while maintaining a secure and reliable environment for managing IoT devices.
Addressing Common Challenges and Troubleshooting
Even with their robust design, IoT remote SSH servers can encounter issues that may affect their performance. Common problems include connection timeouts, authentication failures, and configuration errors. Addressing these challenges requires a systematic and methodical approach:
- Connection Issues: Verify network settings and ensure that the server is reachable from the client by checking IP addresses, ports, and network connectivity.
- Authentication Failures: Review user credentials and ensure that public keys are correctly configured, addressing any discrepancies that may arise during the authentication process.
- Configuration Errors: Carefully review configuration files for syntax errors and misconfigurations, ensuring that all settings align with the server's requirements and operational standards.
Proactively addressing these issues ensures uninterrupted service and minimizes downtime, enabling users to maintain seamless connectivity with their IoT devices.
IoT Remote SSH Servers Across Industries
IoT remote SSH servers are widely utilized across various industries, each leveraging the technology to address specific needs and challenges:
- Healthcare: Securely managing medical devices and monitoring patient data remotely, ensuring compliance with stringent healthcare regulations and protecting sensitive health information.
- Manufacturing: Enabling remote access to industrial control systems for maintenance and troubleshooting, improving operational efficiency and reducing downtime in manufacturing environments.
- Finance: Protecting sensitive financial transactions and ensuring compliance with regulatory standards, safeguarding against cyber threats and maintaining the integrity of financial systems.
These diverse applications highlight the versatility and importance of IoT remote SSH servers in modern business operations, underscoring their role in driving innovation and enhancing security across industries.
Emerging Trends in IoT Remote SSH Technology
As technology continues to advance, the landscape of IoT remote SSH servers is evolving rapidly, driven by emerging trends and innovations. Some of the most promising developments include:
- Quantum-Resistant Encryption: Researchers are actively developing encryption methods that are secure against quantum computing threats, ensuring long-term protection for sensitive data.
- AI-Driven Security: Artificial intelligence is being integrated into security systems to enhance threat detection and response capabilities, enabling real-time monitoring and automated threat mitigation.
- Edge Computing Integration: Combining SSH with edge computing technologies is revolutionizing IoT networks, improving latency and efficiency while reducing reliance on centralized cloud infrastructure.
These trends point towards a future where IoT remote SSH servers play an even more critical role in securing and managing connected devices, driving innovation and enabling new possibilities in the IoT ecosystem.
Final Thoughts and Next Steps
In conclusion, IoT remote SSH servers represent a powerful and indispensable solution for secure and efficient remote device management. By leveraging SSH's robust security features and scalability, organizations can effectively manage their IoT ecosystems while safeguarding sensitive data and ensuring compliance with regulatory requirements.
We encourage readers to implement the best practices outlined in this article and explore the diverse applications of IoT remote SSH servers within their respective industries. Feel free to share your thoughts, comments, or questions below, and don't hesitate to share this article with others who may benefit from it. Together, we can build a safer, more connected, and more innovative future!