As the Internet of Things (IoT) continues to reshape industries globally, securely connecting IoT devices to Amazon Web Services (AWS) through SSH has emerged as an indispensable skill for developers and IT professionals. This comprehensive guide explores the intricacies of IoT SSH connections to AWS, ensuring devices are both secure and efficiently managed in the cloud.
In the era of rapidly expanding connected devices, establishing secure communication channels is no longer a choice but a necessity. IoT SSH integration with AWS provides a robust framework for encrypted communication, safeguarding sensitive data against potential cyber threats and ensuring compliance with modern security standards.
This article delves into the technical nuances of setting up IoT SSH connections to AWS, offering practical advice, step-by-step guidance, and best practices. Whether you're a beginner exploring IoT for the first time or an experienced developer seeking to refine your skills, this guide equips you with the knowledge needed to implement secure and scalable IoT systems.
Read also:Naviyd Ely Raymond
Table of Contents
- Understanding IoT SSH Connect AWS
- The Importance of IoT SSH Connect AWS
- Establishing IoT SSH Connections to AWS
- Enhancing Security for IoT SSH on AWS
- Addressing Common Challenges in IoT SSH Connect AWS
- Troubleshooting IoT SSH Connect AWS
- Optimizing IoT SSH Connect AWS Performance
- Scaling IoT SSH Connect AWS Solutions
- The Evolution of IoT SSH Connect AWS
- Conclusion: Leveraging IoT SSH Connect AWS for Success
Understanding IoT SSH Connect AWS
The Internet of Things (IoT) has redefined how technology integrates into our daily lives, enabling billions of interconnected devices to communicate seamlessly. At the heart of this revolution lies IoT SSH connect AWS, a critical solution that ensures secure and reliable communication between IoT devices and the cloud environment.
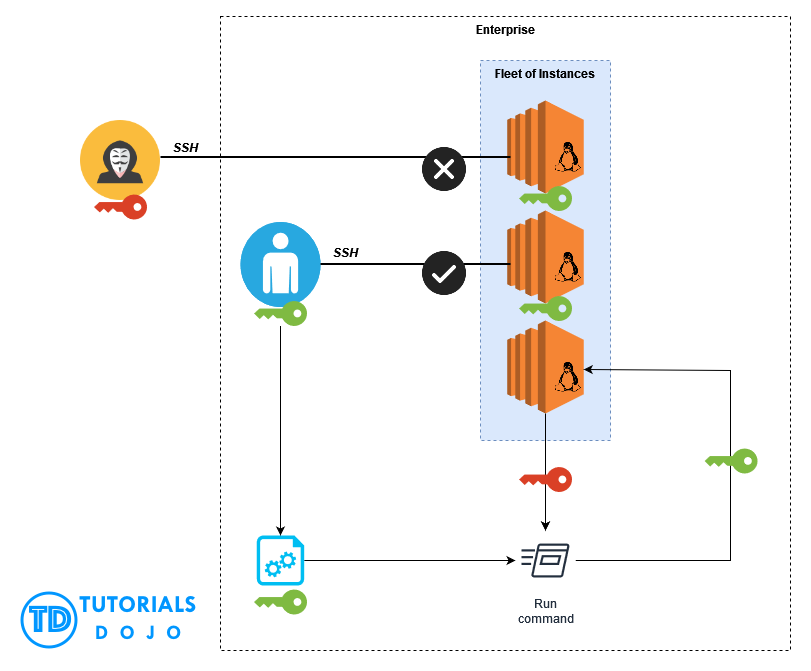
SSH (Secure Shell), a cryptographic network protocol, facilitates secure data transmission over unsecured networks. By integrating SSH with AWS, organizations gain the ability to manage IoT devices remotely while maintaining robust security protocols. AWS's scalable infrastructure empowers developers to build and deploy IoT applications effortlessly, enhancing both security and operational efficiency.
This integration not only fortifies data protection but also simplifies device management, making it an ideal choice for modern IoT deployments. Organizations can now scale their operations seamlessly, ensuring their IoT solutions grow in tandem with their business needs.
The Importance of IoT SSH Connect AWS
In today's hyper-connected world, securing IoT devices is no longer optional but a fundamental requirement. IoT SSH connect AWS offers numerous advantages that make it an essential component of modern IoT ecosystems:
- Enhanced Data Security: SSH encrypts all data transmissions between IoT devices and AWS, protecting sensitive information from unauthorized access and potential cyber threats.
- Effortless Remote Management: Developers can manage and update IoT devices remotely, streamlining maintenance processes and reducing operational overheads.
- Scalability and Flexibility: AWS's cloud infrastructure supports millions of devices, ensuring your IoT solution can expand as your business grows without compromising performance.
- Cost-Effective Solutions: Leveraging AWS's pay-as-you-go pricing model, organizations can optimize costs while maintaining high levels of performance and reliability.
These benefits position IoT SSH connect AWS as a cornerstone for secure and scalable IoT deployments, enabling businesses to thrive in an increasingly digital landscape.
Establishing IoT SSH Connections to AWS
Prerequisites for IoT SSH Connect AWS
Before initiating the setup process for IoT SSH connect AWS, ensure you have the following prerequisites in place:
Read also:Jason Momoa Height
- An active AWS account with appropriate administrative permissions.
- An IoT device equipped with SSH capabilities and configured for secure communication.
- A properly configured SSH client installed on your local machine.
Step-by-Step Guide to IoT SSH Connect AWS
To establish a secure IoT SSH connection to AWS, follow these detailed steps:
- Create an IAM user within AWS, assigning the necessary permissions for IoT management and secure communication.
- Set up an EC2 instance or configure IoT Core in AWS to act as the server endpoint for your IoT devices.
- Generate SSH keys for secure authentication, ensuring they are stored securely and accessible only to authorized personnel.
- Install and configure an SSH client on your IoT device, ensuring all settings align with AWS security standards.
- Test the connection thoroughly to verify secure communication and address any potential issues proactively.
By adhering to these steps, you can establish a secure and reliable IoT SSH connect AWS environment tailored to your specific needs.
Enhancing Security for IoT SSH on AWS
Ensuring the security of your IoT SSH connect AWS setup requires adherence to industry best practices. Consider implementing the following measures:
- Use Strong and Unique Passwords: Avoid default credentials and adopt complex, unique passwords to minimize the risk of unauthorized access.
- Enable Multi-Factor Authentication (MFA): Add an extra layer of security by requiring multiple forms of verification for all critical operations.
- Regularly Update Software and Firmware: Keep all devices, servers, and applications updated with the latest security patches and firmware updates.
- Monitor Logs and Alerts: Regularly review system logs for suspicious activity and configure real-time alerts to address potential threats promptly.
By integrating these practices into your IoT SSH connect AWS strategy, you can significantly enhance the security and reliability of your IoT ecosystem.
Addressing Common Challenges in IoT SSH Connect AWS
While IoT SSH connect AWS offers numerous benefits, it can present challenges that may hinder its effectiveness. Common issues include:
- Connection Failures: Often caused by misconfigured SSH settings, network disruptions, or firewall restrictions.
- Authentication Errors: Typically due to incorrect SSH keys, expired credentials, or insufficient IAM permissions.
- Performance Bottlenecks: Resulting from insufficient server resources, suboptimal configurations, or high traffic loads.
Identifying the root causes of these issues is the first step toward resolving them effectively and ensuring seamless operation.
Troubleshooting IoT SSH Connect AWS
Diagnosing Connection Issues
When troubleshooting IoT SSH connect AWS, consider the following systematic approach:
- Review SSH configurations for potential errors or misalignments with AWS security standards.
- Verify network settings, ensuring proper connectivity and addressing any firewall or DNS-related issues.
- Test the connection using alternative devices or networks to isolate the problem and identify its source.
Resolving Authentication Problems
Authentication issues can often be resolved by:
- Regenerating SSH keys and reapplying them, ensuring they align with the latest security protocols.
- Reviewing and updating IAM permissions to ensure appropriate access levels for all users and devices.
- Clearing cached credentials and restarting the connection process to eliminate potential conflicts.
By methodically addressing these challenges, you can restore functionality and enhance the reliability of your IoT SSH connect AWS setup.
Optimizing IoT SSH Connect AWS Performance
Optimizing IoT SSH connect AWS involves implementing strategic measures to enhance efficiency and reliability. Consider the following approaches:
- Load Balancing: Distribute incoming traffic evenly across multiple servers to prevent bottlenecks and ensure consistent performance.
- Caching Mechanisms: Implement caching solutions to reduce latency, improve response times, and enhance user experience.
- Resource Allocation: Allocate sufficient resources, including CPU, memory, and storage, to handle peak loads and maintain optimal performance levels.
By adopting these strategies, you can significantly enhance the efficiency and reliability of your IoT SSH connect AWS system, ensuring it meets the demands of modern IoT ecosystems.
Scaling IoT SSH Connect AWS Solutions
Horizontal Scaling
Horizontal scaling involves adding more servers to handle increased traffic and demands. AWS's auto-scaling feature automates this process, ensuring your IoT SSH connect AWS setup can adapt seamlessly to growing requirements.
Vertical Scaling
Vertical scaling focuses on upgrading existing servers with more powerful hardware, such as enhanced processors or increased memory capacity. This approach is ideal for applications requiring higher processing power or advanced computational capabilities.
By combining horizontal and vertical scaling strategies, you can create a scalable IoT SSH connect AWS architecture capable of supporting millions of connected devices while maintaining high performance levels.
The Evolution of IoT SSH Connect AWS
The future of IoT SSH connect AWS looks promising, driven by advancements in technology and emerging trends. Key developments include:
- Quantum-Safe Encryption: Protecting sensitive data against future quantum computing threats and ensuring long-term security.
- Edge Computing Integration: Enhancing performance by processing data closer to the source, reducing latency and improving real-time decision-making capabilities.
- AI-Driven Security Solutions: Leveraging artificial intelligence and machine learning to detect and mitigate potential threats in real-time, ensuring proactive security measures.
As technology continues to evolve, IoT SSH connect AWS will remain a pivotal component of secure and efficient IoT ecosystems, enabling businesses to thrive in an increasingly connected world.
Conclusion: Leveraging IoT SSH Connect AWS for Success
In conclusion, IoT SSH connect AWS offers a secure, scalable, and efficient solution for managing IoT devices in the cloud. By following the guidelines outlined in this article, you can establish a robust IoT SSH connect AWS setup tailored to your organization's unique needs and objectives.
We invite you to share your thoughts, experiences, and insights in the comments section below. For more in-depth information on IoT and cloud computing, explore our other articles and resources. Together, let's build a secure, connected, and innovative future!
Data Source: AWS IoT Core, SSH Protocol Documentation.