In today’s fast-paced world of interconnected devices, securely accessing and managing remote IoT devices has become a cornerstone of modern technology. As the Internet of Things (IoT) continues to expand its influence across industries, understanding how to efficiently log in to remote IoT devices is vital for maintaining operational efficiency and safeguarding data integrity.
IoT Core serves as the foundation for many IoT ecosystems, offering a powerful platform for device management, data collection, and advanced analytics. Whether you're a developer, system administrator, or technology enthusiast, gaining a thorough understanding of remote IoT device login processes is essential for ensuring seamless integration and secure communication between devices.
This article delves into the complexities of remote IoT device login for IoT Core, providing practical insights, expert advice, and actionable strategies. By the end of this guide, you'll have a comprehensive understanding of the topic, empowering you to optimize your IoT infrastructure's performance and security.
Read also:Irene Banerjee
Table of Contents
- Understanding Remote IoT Device Login
- Exploring IoT Core
- Key Security Considerations
- Authentication Methods for IoT Devices
- Step-by-Step Guide to Remote IoT Device Login
- Troubleshooting Common Challenges
- Best Practices for Managing Remote IoT Devices
- Emerging Trends in IoT Device Management
- Data Privacy and Compliance in IoT
- Conclusion
Understanding Remote IoT Device Login
The ability to log in to remote IoT devices is a transformative capability that allows users to manage and interact with devices from any location. This functionality is particularly valuable in scenarios where physical access to the device is impractical or impossible. With IoT Core as a central platform, organizations can streamline device management processes, enhance operational efficiency, and elevate overall system performance.
Remote IoT device login encompasses several critical components, including robust authentication protocols, secure communication channels, and intuitive device management interfaces. Familiarizing yourself with these elements is crucial for ensuring a smooth and secure login experience. Additionally, staying abreast of the latest advancements in IoT technology can help organizations address potential challenges and capitalize on emerging opportunities.
Exploring IoT Core
IoT Core acts as a pivotal platform for managing IoT devices, offering an array of features designed to simplify device integration and streamline data management. Some of the standout capabilities of IoT Core include:
- Device Provisioning: Simplifies the process of adding and configuring new devices, reducing setup time and complexity.
- Data Collection: Facilitates efficient collection and analysis of device data, enabling data-driven decision-making.
- Remote Monitoring: Provides real-time insights into device performance and status, empowering proactive maintenance.
- Security Features: Implements advanced security measures to safeguard devices and sensitive data.
Key Features of IoT Core
IoT Core's architecture is engineered to support large-scale deployments, making it an ideal solution for enterprises seeking to implement IoT solutions. Its scalability, reliability, and user-friendly interface make it a preferred choice across various industries.
Key Security Considerations
Security is paramount in remote IoT device login, as unauthorized access can lead to severe data breaches and operational disruptions. To mitigate these risks, organizations must adopt comprehensive security measures, such as:
- Encryption: Ensures secure communication between devices and the IoT Core platform, safeguarding sensitive data.
- Authentication: Verifies the identity of users and devices attempting to access the system, preventing unauthorized access.
- Access Control: Restricts access to sensitive data and functions based on predefined user roles and permissions, enhancing data protection.
Best Security Practices
In addition to implementing fundamental security measures, organizations should consider adopting cutting-edge technologies like machine learning-based threat detection and behavioral analytics to fortify their IoT security posture. These advanced tools can help identify and neutralize potential threats in real time.
Read also:Understanding The Concept Of Masa 49 And Its Cultural Significance
Authentication Methods for IoT Devices
Authentication is a cornerstone of secure remote IoT device login. Various authentication methods are available, each offering distinct advantages and limitations. Some of the most widely used authentication methods include:
- Username and Password: A straightforward and widely adopted method, though vulnerable to brute-force attacks if not properly implemented.
- Two-Factor Authentication (2FA): Adds an additional layer of security by requiring users to provide two forms of identification, enhancing protection against unauthorized access.
- Public Key Infrastructure (PKI): Utilizes digital certificates to verify the identity of devices and users, offering a highly secure authentication mechanism.
Selecting the Right Authentication Method
Choosing the appropriate authentication method depends on several factors, including security requirements, usability considerations, and resource availability. Organizations should carefully evaluate these factors to select an authentication solution that aligns with their specific needs and objectives.
Step-by-Step Guide to Remote IoT Device Login
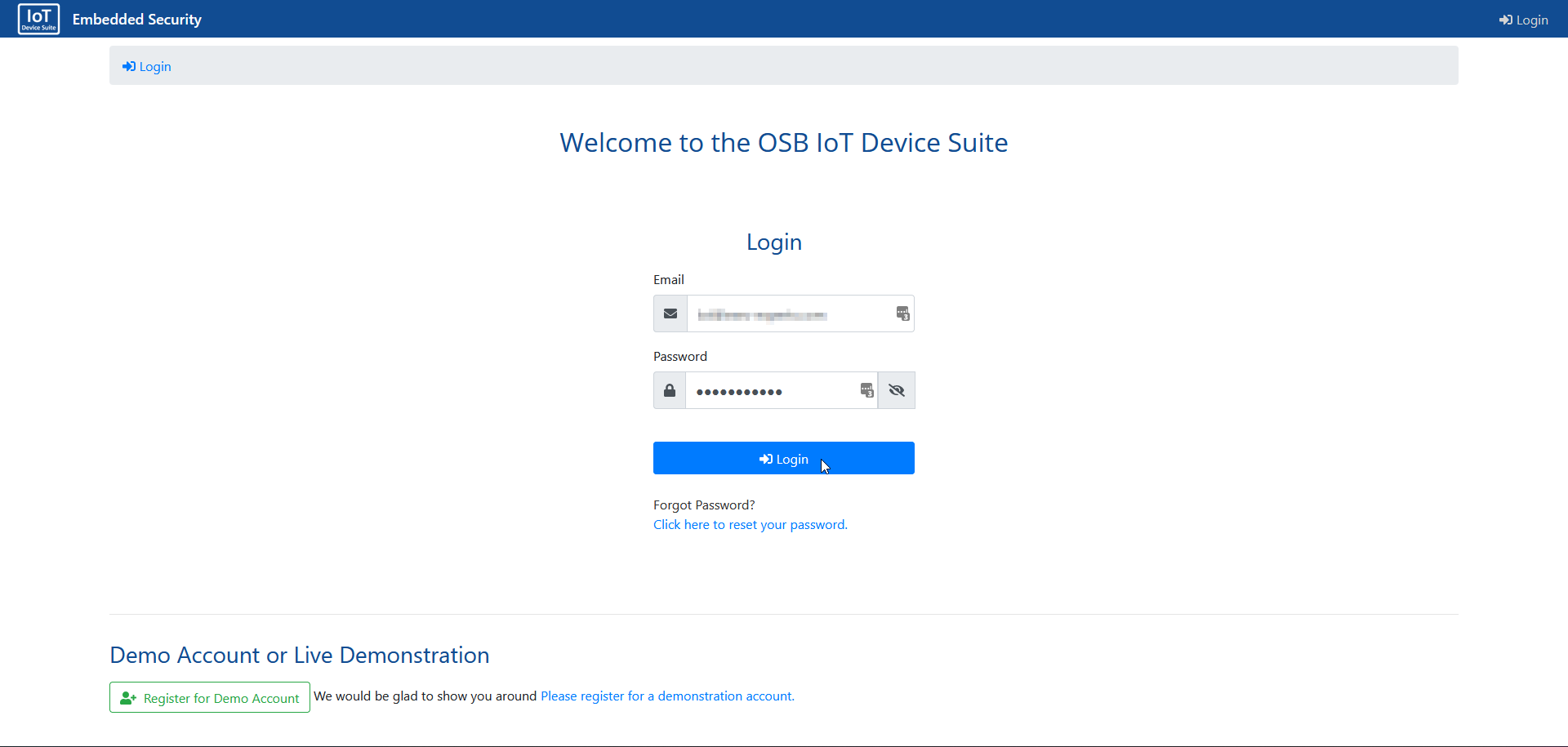
Logging into a remote IoT device using IoT Core involves several critical steps that require meticulous attention to detail. Below is a comprehensive guide to help you navigate the process:
- Install IoT Core: Begin by installing the IoT Core platform on your server or cloud environment, ensuring compatibility with your infrastructure.
- Register Devices: Register your IoT devices with IoT Core by providing essential device information, such as unique identifiers and configuration details.
- Configure Authentication: Set up robust authentication mechanisms to ensure secure access to devices, protecting against unauthorized access.
- Access Device: Use the IoT Core interface to connect to your remote IoT device and perform the necessary operations, leveraging the platform's powerful features.
Troubleshooting Common Challenges
Despite thorough preparation, issues may arise during the remote IoT device login process. Below are some common problems and their potential solutions:
- Connection Errors: Verify network connectivity and ensure proper configuration of communication protocols, addressing any network-related issues.
- Authentication Failures: Double-check user credentials and authentication settings to resolve access issues, ensuring accurate information is provided.
- Device Malfunctions: Investigate device logs and perform diagnostic tests to identify and address underlying issues, restoring device functionality.
Preventive Measures
Implementing regular maintenance and monitoring practices can help prevent many common issues associated with remote IoT device login. Additionally, staying updated with the latest software releases and security patches can significantly enhance system reliability and performance.
Best Practices for Managing Remote IoT Devices
To ensure optimal performance and security of remote IoT devices, organizations should adhere to the following best practices:
- Regular Updates: Keep IoT Core and all connected devices up-to-date with the latest software releases, addressing vulnerabilities and enhancing functionality.
- Monitoring and Logging: Implement comprehensive monitoring and logging solutions to track device activity and detect potential issues early, enabling proactive resolution.
- Access Control: Enforce strict access control policies to limit unauthorized access to sensitive data and functions, maintaining data integrity and security.
Emerging Trends in IoT Device Management
The field of IoT device management is continuously evolving, with new technologies and innovations emerging at a rapid pace. Some of the most promising trends include:
- Edge Computing: Enhances processing capabilities by performing computations closer to the data source, reducing latency and improving efficiency.
- Artificial Intelligence: Improves decision-making and automation through advanced analytics and machine learning algorithms, unlocking new possibilities for IoT applications.
- 5G Connectivity: Enables faster and more reliable communication between IoT devices, facilitating real-time data exchange and enhancing user experiences.
Impact on Remote IoT Device Login
These emerging trends are poised to revolutionize remote IoT device login processes, offering unprecedented opportunities for enhancing security, efficiency, and user engagement. By embracing these advancements, organizations can stay ahead of the curve in the ever-evolving IoT landscape.
Data Privacy and Compliance in IoT
Data privacy is a critical concern in the IoT ecosystem, with regulatory frameworks such as GDPR and CCPA imposing stringent requirements on data handling practices. Organizations must ensure compliance with these regulations by implementing appropriate data protection measures and maintaining transparency in their data processing activities. Prioritizing data privacy not only builds trust with users but also safeguards against legal and financial repercussions.
Conclusion
Mastery of remote IoT device login for IoT Core is indispensable for anyone involved in IoT device management. By comprehending the fundamental concepts, security considerations, and best practices outlined in this article, you can significantly enhance your IoT infrastructure's performance and security. We invite you to share your thoughts and experiences in the comments section below and explore other articles on our site for further insights into the dynamic world of IoT.
Thank you for reading, and we hope this guide serves as a valuable resource on your IoT journey!