In the age of interconnected technology, establishing secure peer-to-peer (P2P) connections between IoT devices on Android is crucial for both users and developers. As the Internet of Things (IoT) continues to expand, the importance of secure communication between devices grows exponentially. This guide aims to provide actionable insights, tools, and best practices to help you create a robust and secure P2P connection for IoT devices on Android platforms.
In a world where billions of IoT devices are actively in use, the demand for secure and efficient connectivity solutions has never been higher. Whether you're a developer integrating P2P technology into your applications or an end-user looking to protect your IoT devices, this article will walk you through essential steps and considerations to ensure your devices are secure and efficient.
By the conclusion of this guide, you will have a comprehensive understanding of how to securely connect remote IoT devices using P2P technology on Android, ensuring both privacy and optimal performance. Let’s delve into the possibilities and challenges of this rapidly evolving field.
Read also:Is Park Bo Gum Married
Table of Contents
- Understanding IoT and P2P Connectivity
- Why Security is Crucial in IoT P2P Connections
- Android as an Optimal Platform for IoT P2P
- Methods for Establishing Secure Connections in Remote IoT P2P
- Tools and Applications for Secure IoT P2P on Android
- Challenges and Solutions in IoT P2P Security
- Best Practices for Securely Connecting Remote IoT P2P on Android
- Data Privacy and Compliance in IoT P2P
- Emerging Trends in IoT P2P Security
- Conclusion and Call to Action
Understanding IoT and P2P Connectivity
The Internet of Things (IoT) represents a network of physical devices embedded with sensors, software, and connectivity that enables them to exchange data seamlessly. Peer-to-peer (P2P) connectivity allows these devices to communicate directly without relying on a central server, which not only reduces latency but also enhances efficiency. For Android users, leveraging P2P technology can significantly improve the performance and reliability of IoT applications.
Key Benefits of IoT P2P
- Minimized reliance on centralized servers, reducing potential single points of failure.
- Improved data transfer speed, ensuring faster communication between devices.
- Enhanced privacy and security, as data is transmitted directly between devices without intermediaries.
Despite these advantages, ensuring secure communication in such an environment requires a deep understanding of potential vulnerabilities and strategies to mitigate them effectively.
Why Security is Crucial in IoT P2P Connections
As IoT devices become increasingly integrated into our daily lives, the risks associated with insecure connections grow significantly. According to a report by Gartner, the number of IoT devices is expected to exceed 25 billion by 2025. This rapid expansion underscores the necessity for robust security measures to safeguard sensitive data and prevent unauthorized access.
Common Security Threats
- Data breaches, where sensitive information is exposed to unauthorized parties.
- Man-in-the-middle attacks, where attackers intercept and alter communications between devices.
- Malware infections, which can compromise the functionality and security of IoT devices.
Prioritizing security in IoT P2P connections is essential for developers and users alike, as it helps mitigate these risks and fosters a safer digital ecosystem.
Android as an Optimal Platform for IoT P2P
Android provides a versatile and scalable platform for developing IoT applications that utilize P2P connectivity. With its open-source architecture and a vast developer community, Android offers the tools necessary to create secure and efficient IoT solutions. The platform's flexibility allows developers to tailor their applications to meet specific user needs while maintaining high security standards.
Advantages of Using Android for IoT
- Wide compatibility across various devices, ensuring broad usability.
- Access to a comprehensive library of APIs, simplifying the development process.
- Strong community support, providing developers with resources and guidance.
These advantages make Android an excellent choice for developers aiming to implement secure IoT P2P connections.
Read also:Unveiling The World Of Beeg A Comprehensive Guide
Methods for Establishing Secure Connections in Remote IoT P2P
Creating secure connections for remote IoT P2P on Android involves implementing advanced encryption protocols, robust authentication mechanisms, and secure communication channels. Below are some of the most effective methods:
1. SSL/TLS Encryption
SSL/TLS encryption ensures that data transmitted between devices is securely encrypted, making it extremely challenging for attackers to intercept and decipher the information.
2. Public Key Infrastructure (PKI)
PKI provides a framework for managing digital certificates and public-key encryption, significantly enhancing the security of IoT P2P connections by verifying the authenticity of devices.
3. Mutual Authentication
Mutual authentication ensures that both devices in a P2P connection verify each other's identity, reducing the risk of unauthorized access and enhancing overall security.
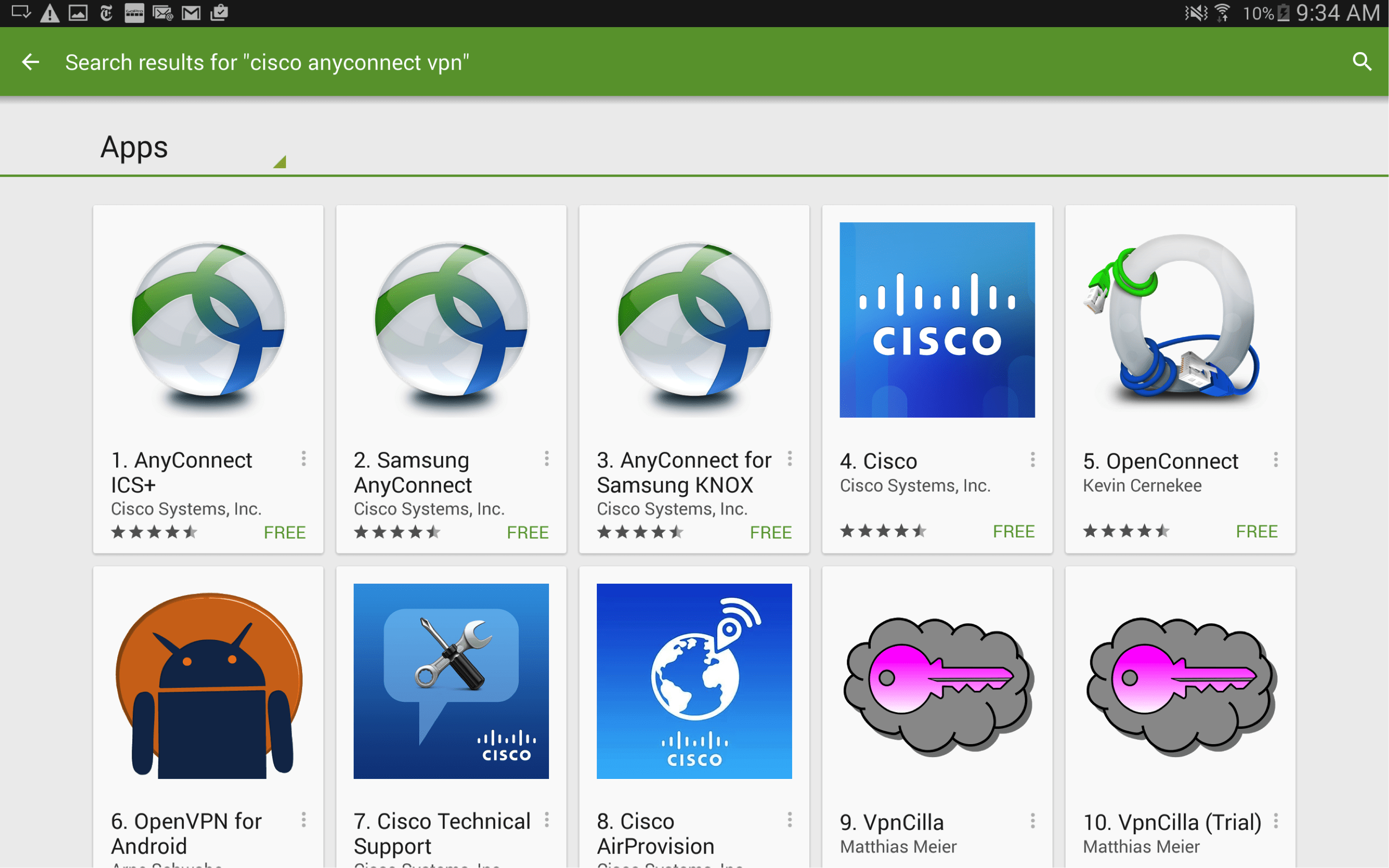
Tools and Applications for Secure IoT P2P on Android
Several tools and applications are available to facilitate secure IoT P2P connections on Android. These tools empower developers to implement robust security measures while optimizing performance.
Popular Tools
- Android Things: A platform designed specifically for IoT development, offering enhanced security features.
- MQTT for Android: A lightweight messaging protocol ideal for IoT applications requiring secure and efficient communication.
- WebRTC: A technology enabling real-time communication, which can be leveraged for secure IoT P2P connections.
By utilizing these tools, developers can create secure and efficient IoT applications that meet the demands of modern users.
Challenges and Solutions in IoT P2P Security
While IoT P2P connectivity offers numerous advantages, several challenges must be addressed to ensure secure communication. These challenges include:
1. Limited Resources
IoT devices often have limited processing power and memory, making it difficult to implement complex security protocols. Lightweight encryption algorithms and optimized software can help overcome these limitations.
2. Scalability
As the number of connected devices increases, ensuring scalability without compromising security becomes a significant challenge. Implementing distributed ledger technologies like blockchain can enhance both scalability and security.
Best Practices for Securely Connecting Remote IoT P2P on Android
Adopting best practices is essential for ensuring secure IoT P2P connections on Android. Below are some key recommendations:
1. Regularly Update Software
Keeping your Android device and IoT applications up to date with the latest security patches is critical for protecting against emerging vulnerabilities.
2. Use Strong Passwords
Implementing strong, unique passwords for all devices and accounts significantly enhances security and reduces the risk of unauthorized access.
3. Enable Two-Factor Authentication
Two-factor authentication adds an extra layer of security by requiring users to provide two forms of identification before accessing their devices or accounts, making it harder for attackers to gain unauthorized access.
Data Privacy and Compliance in IoT P2P
Data privacy is a critical consideration in IoT P2P connectivity. Compliance with regulations such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) is essential for protecting user data and avoiding legal issues.
Key Compliance Measures
- Data minimization: Collect only the data necessary for the application's functionality.
- Transparent data collection practices: Clearly communicate data collection methods and purposes to users.
- Secure data storage: Implement robust encryption and security measures to protect stored data from breaches.
By adhering to these measures, developers and organizations can ensure their IoT P2P solutions meet the highest standards of data privacy and compliance.
Emerging Trends in IoT P2P Security
The future of IoT P2P security is shaped by emerging technologies and evolving security paradigms. Some of the most promising trends include:
1. Artificial Intelligence (AI) and Machine Learning (ML)
AI and ML can be leveraged to detect and respond to security threats in real time, enhancing the overall security of IoT P2P networks by identifying anomalies and potential vulnerabilities.
2. Quantum Cryptography
Quantum cryptography offers the potential for ultra-secure communication, making it nearly impossible for attackers to intercept or decipher data, even with advanced computational capabilities.
3. Edge Computing
Edge computing reduces latency and enhances security by processing data closer to the source, minimizing the risk of data breaches and ensuring faster response times.
Conclusion and Call to Action
In conclusion, establishing secure connections for remote IoT devices through P2P networks on Android requires a comprehensive approach that addresses both technical and organizational challenges. By following the best practices outlined in this guide and staying informed about emerging trends, you can ensure that your IoT P2P solutions remain secure, efficient, and aligned with user expectations.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore our other articles for more insights into IoT and cybersecurity. Together, we can build a safer and more connected digital world for everyone.