In today's interconnected world, the ability to connect to IoT devices remotely without incurring costs has become increasingly important. As smart devices continue to proliferate, managing them from anywhere has become essential for both personal and professional purposes. This article delves into methods for securely accessing IoT devices remotely for free, ensuring that your data remains protected while maximizing convenience.
With the growing adoption of IoT devices for home automation, industrial applications, and beyond, the demand for reliable remote access solutions has surged. However, many users are reluctant to invest in paid solutions when effective free alternatives exist. This guide will provide you with comprehensive insights and practical steps to achieve secure remote access to your IoT devices without compromising on security or affordability.
By the end of this article, you will have a thorough understanding of how to set up remote access for your IoT devices while maintaining robust security measures. Let's explore the possibilities and solutions in detail.
Read also:Access Iot Device Behind Nat
Table of Contents
- Introduction
- Understanding SSH
- Why SSH is Ideal for IoT Devices
- Free SSH Tools for IoT Devices
- Enhancing Security with Best Practices
- Essential Tools and Software
- Step-by-Step Guide to Setting Up SSH
- Troubleshooting Common Issues
- Exploring Alternatives to SSH
- The Future of IoT Remote Access
Understanding SSH
SSH, or Secure Shell, is a network protocol that enables users to establish secure connections to remote devices, even over unsecured networks. It ensures the confidentiality and integrity of all data exchanged between the client and the server through robust encryption. SSH is widely utilized in IT infrastructure and has become a trusted method for managing IoT devices remotely.
For IoT devices, SSH provides a secure and reliable way to access and manage systems from anywhere in the world. With SSH, you can execute commands, transfer files, and monitor device performance without exposing sensitive information to potential threats.
Why SSH is Ideal for IoT Devices
Unmatched Security
SSH is celebrated for its robust security features, making it an excellent choice for IoT devices. The protocol employs advanced encryption algorithms to safeguard data during transmission, significantly reducing the risk of unauthorized access and data breaches.
Cost-Effective Solution
One of the standout advantages of SSH is its cost-effectiveness. Many SSH clients and servers are open-source and available free of charge, providing an accessible solution for individuals and small businesses looking to manage their IoT devices without incurring expenses.
Wide Compatibility
SSH is compatible with a broad range of operating systems and devices, including Linux, macOS, and Windows. This versatility ensures that you can connect to your IoT devices regardless of the platform they operate on, enhancing convenience and flexibility.
Free SSH Tools for IoT Devices
Several free SSH tools and services are available to help you connect to your IoT devices remotely. Below are some of the most popular options:
Read also:Brad Paisley Wife And Kids A Closer Look At The Country Stars Family Life
- OpenSSH: A widely adopted open-source SSH client and server that provides secure remote access to IoT devices, making it a go-to choice for many users.
- Bitvise SSH Client: A free SSH client for Windows that offers advanced features such as SFTP file transfer and terminal emulation, making it ideal for more complex tasks.
- Putty: A lightweight and user-friendly SSH client for Windows, perfect for beginners who require a simple yet effective solution for remote access.
These tools cater to a variety of user needs, offering flexibility and functionality without any associated costs.
Enhancing Security with Best Practices
When accessing IoT devices remotely, adhering to security best practices is crucial to protect your data and devices. Here are some key tips to ensure a secure connection:
- Use strong, complex, and unique passwords for your SSH accounts to prevent unauthorized access.
- Enable two-factor authentication (2FA) to add an additional layer of security to your login process.
- Regularly update your SSH client and server software to address vulnerabilities and maintain optimal security.
- Limit SSH access to specific IP addresses to minimize the risk of unauthorized access attempts.
Implementing these practices will help fortify your IoT devices against potential threats, ensuring their security and integrity.
Essential Tools and Software
SSH Clients
SSH clients are software applications that facilitate secure connections to remote devices using the SSH protocol. Some of the most popular SSH clients include:
- OpenSSH
- Bitvise SSH Client
- Putty
SSH Servers
SSH servers are installed on the devices you wish to access remotely. They handle incoming connections and provide secure access to the device. Common SSH servers include:
- OpenSSH Server
- Dropbear SSH
Selecting the appropriate tools and software depends on your specific requirements and the devices you are managing. Each option offers unique features to suit different use cases.
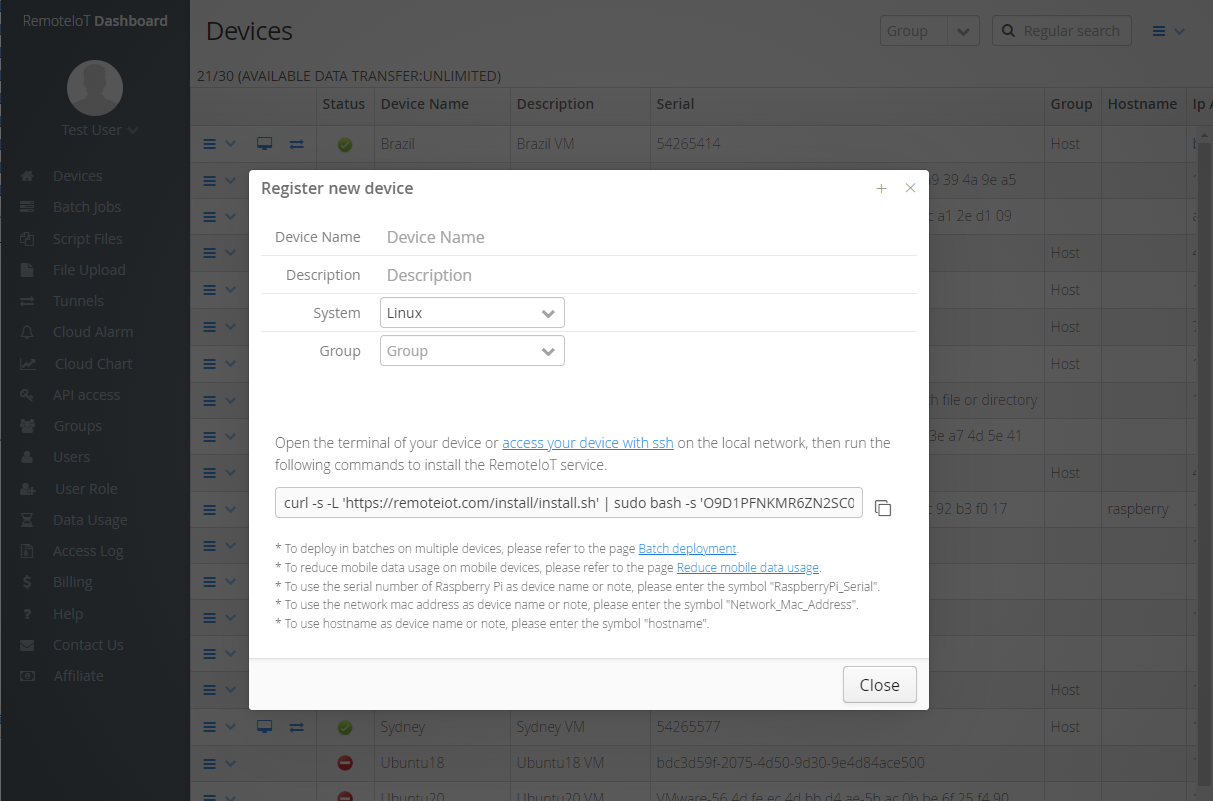
Step-by-Step Guide to Setting Up SSH
Setting up SSH for remote access to IoT devices involves a series of steps. Follow this guide to ensure a seamless setup process:
- Install an SSH server on your IoT device to enable remote access capabilities.
- Configure the SSH server settings, including the port number and authentication method, to align with your security preferences.
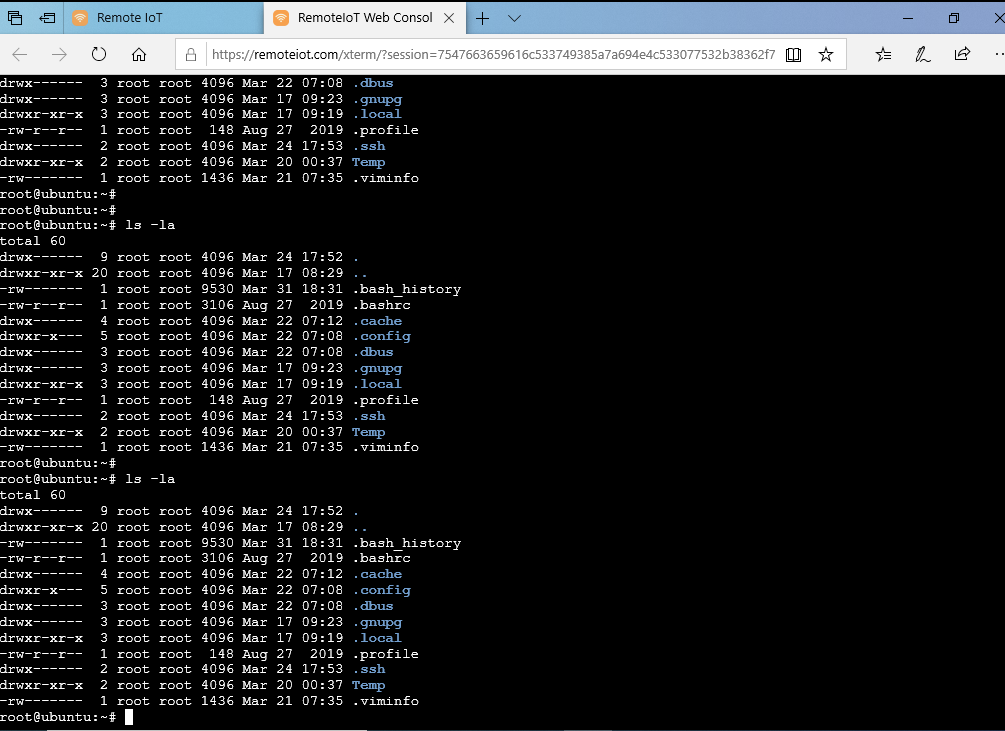
- Install an SSH client on your local machine to establish a connection to the IoT device.
- Connect to your IoT device using the SSH client by entering the device's IP address and login credentials.
- Test the connection to ensure that everything is functioning correctly and securely.
By following these steps, you can establish a secure and reliable connection to your IoT devices, empowering you to manage them effectively from anywhere.
Troubleshooting Common Issues
While setting up SSH for IoT devices, you may encounter some common issues. Below are a few troubleshooting tips to help you resolve them:
- Connection Refused: Verify that the SSH server is running and that the correct IP address and port number have been entered.
- Authentication Failed: Carefully check your login credentials and ensure that two-factor authentication is properly configured and functioning.
- Slow Connection: Optimize your network settings and consider upgrading to a faster internet connection to enhance performance.
Addressing these issues promptly will help you maintain a stable and secure connection to your IoT devices, ensuring uninterrupted access.
Exploring Alternatives to SSH
MQTT
MQTT (Message Queuing Telemetry Transport) is a lightweight messaging protocol designed specifically for IoT devices. It allows devices to communicate efficiently over low-bandwidth networks, making it an excellent alternative to SSH for certain applications where real-time data exchange is critical.
WebSockets
WebSockets provide a bi-directional communication channel over a single TCP connection, enabling real-time interactions. They are particularly well-suited for applications requiring instant updates and can be used to remotely access IoT devices through a web browser, offering a more interactive user experience.
While these alternatives offer unique advantages, SSH remains the most secure and widely adopted option for remote access due to its robust encryption and reliability.
The Future of IoT Remote Access
As the Internet of Things continues to evolve, so too will the methods for remote access. Technological advancements and the growing demand for secure connections will drive innovation in this field. Future solutions may include:
- Enhanced encryption protocols to further strengthen data protection.
- Integration with AI for automated security monitoring, enabling proactive threat detection and response.
- Improved user interfaces for easier management and more intuitive interactions with IoT devices.
Staying informed about these developments will empower you to make the most of your IoT devices while ensuring they remain secure and efficient.
Conclusion
Accessing IoT devices remotely for free is both feasible and practical with the right tools and knowledge. By leveraging SSH, you can establish a secure connection to your devices without incurring costs. It is essential to follow security best practices and stay updated on the latest advancements in IoT technology to maximize the potential of your devices.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for further insights into IoT and related topics.
Data Source: SSH.com, OpenSSH, MQTT.org