In today’s highly interconnected world, leveraging SSH remote access solutions for IoT has transformed the way individuals and businesses manage their connected devices. Whether you’re a DIY enthusiast crafting innovative projects or a professional overseeing large-scale IoT deployments, understanding and implementing SSH remote access is essential for ensuring secure and efficient device communication. This cutting-edge technology empowers users to control and monitor IoT devices remotely, anywhere in the world, without incurring exorbitant costs.
SSH (Secure Shell) is a robust cryptographic network protocol designed to facilitate secure communication over potentially insecure networks. By establishing a secure channel between a client and server, SSH ensures the integrity and confidentiality of all data exchanges. For IoT enthusiasts, utilizing free SSH remote access tools can significantly enhance productivity while drastically reducing the expenses typically associated with proprietary software or paid services.
As the Internet of Things continues to expand exponentially, the demand for secure and reliable remote access solutions has never been higher. This article will provide an in-depth exploration of SSH remote access for IoT, discussing its benefits, implementation strategies, and best practices. Whether you’re new to the concept or looking to refine your existing setup, this guide will equip you with the knowledge to make informed decisions and optimize your IoT environment.
Read also:Sprunki Parodybox Wiki Fandom
Table of Contents
- Introduction to SSH Remote Access IoT Free
- What is SSH and Why is it Essential for IoT?
- Key Benefits of SSH Remote Access for IoT
- Free Tools and Platforms for SSH Remote Access IoT
- Setting Up SSH Remote Access for IoT Devices
- Security Best Practices for SSH Remote Access IoT
- Troubleshooting Common SSH Issues
- Scalability Considerations for SSH Remote Access IoT
- Use Cases for SSH Remote Access IoT Free
- The Future of SSH Remote Access in IoT
- Conclusion and Call to Action
Introduction to SSH Remote Access IoT Free
SSH remote access IoT free solutions have redefined how we interact with connected devices in an increasingly digital world. At its core, SSH enables users to establish secure connections to remote devices via the internet, all while safeguarding data security. This technology has been widely embraced across various industries, from manufacturing and healthcare to transportation and beyond, thanks to its robust security features and ease of deployment.
Why SSH is Crucial in IoT
In the realm of IoT, devices often operate in environments where security is non-negotiable. Traditional communication protocols may expose sensitive data to unauthorized access, rendering them unsuitable for mission-critical applications. SSH addresses this challenge by encrypting all data exchanged between devices, ensuring both confidentiality and data integrity. This makes SSH an indispensable tool for securing IoT ecosystems.
Defining Features of SSH Remote Access IoT Free
- Data encryption during transmission to protect sensitive information.
- Advanced authentication mechanisms to verify the identity of users and devices.
- Compatibility with multiple devices and platforms, offering versatility for diverse IoT deployments.
- A cost-effective solution for both small-scale projects and large-scale enterprise implementations.
What is SSH and Why is it Essential for IoT?
SSH, or Secure Shell, is a network protocol designed to enable secure communication between devices over potentially unsecured networks. Initially developed in 1995 as a secure alternative to less reliable protocols like Telnet and rlogin, SSH has evolved into a versatile tool with applications ranging from remote command execution and file transfers to secure tunneling. Its adaptability and security features make it an ideal choice for IoT environments.
How SSH Operates
SSH establishes a secure connection between a client and a server through advanced encryption algorithms such as AES and RSA. This ensures that all data transmitted between the two parties remains confidential and tamper-proof. Furthermore, SSH employs authentication mechanisms like passwords, public key pairs, and two-factor authentication to verify user identities, adding an extra layer of security.
SSH and IoT: A Seamless Partnership
IoT devices are frequently deployed in remote locations where physical access is impractical or impossible. SSH remote access IoT free solutions empower users to manage and monitor these devices from virtually anywhere in the world. This capability is particularly advantageous for applications such as smart home automation, industrial monitoring, environmental sensing, and more.
Key Benefits of SSH Remote Access for IoT
Integrating SSH remote access into your IoT infrastructure offers a multitude of advantages, addressing both technical and financial considerations. Below are some of the standout benefits:
Read also:Robert Benevides
- Enhanced Security: SSH encrypts all communication, significantly reducing the risk of data breaches and unauthorized access.
- Cost-Effectiveness: Free SSH tools eliminate the need for expensive proprietary software or subscription-based services, making it an affordable option for all budgets.
- Flexibility: SSH supports a wide array of devices and operating systems, ensuring compatibility with diverse IoT deployments.
- Scalability: Whether you’re managing a small-scale project or a large-scale enterprise solution, SSH can adapt seamlessly to meet your needs.
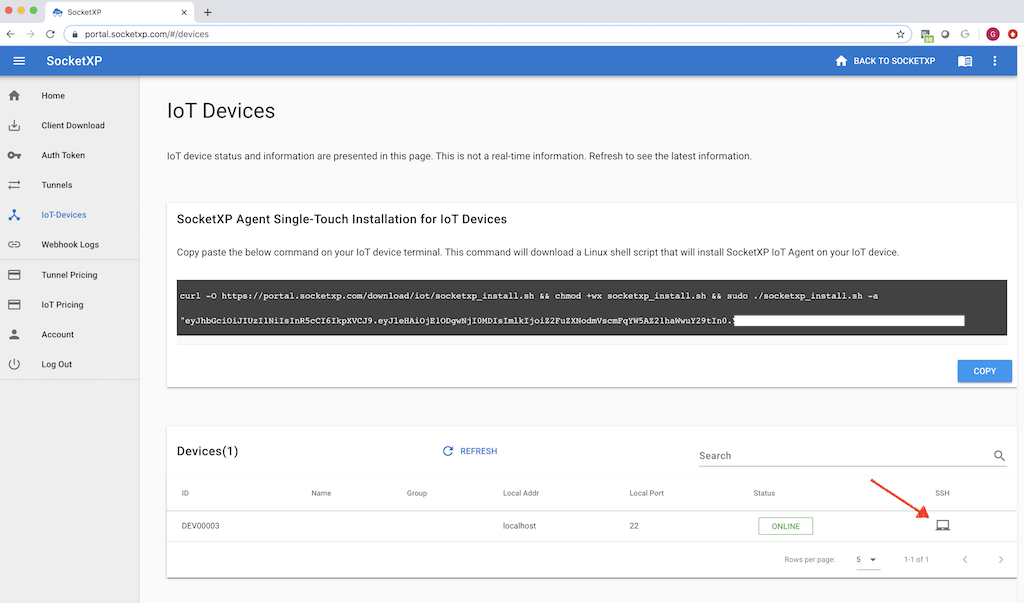
Free Tools and Platforms for SSH Remote Access IoT
Several open-source and free tools are available to facilitate SSH remote access in IoT projects. These tools provide a reliable foundation for building secure and efficient connectivity solutions without breaking the bank.
Popular SSH Clients
- Putty (for Windows)
- OpenSSH (for Linux and macOS)
- Termius (cross-platform compatibility)
SSH Servers for IoT Devices
- Dropbear
- BusyBox
- OpenSSH
Setting Up SSH Remote Access for IoT Devices
Configuring SSH remote access for IoT devices involves several key steps, including installing the necessary software, setting up authentication protocols, and securing the connection. Below is a comprehensive guide to help you navigate the process:
Step 1: Install SSH Server on IoT Device
The installation process varies depending on the operating system of your IoT device. For instance, on a Raspberry Pi running Raspbian, you can install an SSH server using the following command:
sudo apt-get install openssh-server
Step 2: Configure Authentication
Disable password-based authentication and enable public key authentication to enhance security. Generate a public-private key pair on your local machine and copy the public key to the IoT device using:
ssh-copy-id user@iot-device
Step 3: Secure the Connection
Implement firewall rules to restrict access to the SSH port (default is 22) and consider utilizing non-standard ports for added protection. Regularly update your SSH server to address any potential security vulnerabilities.
Security Best Practices for SSH Remote Access IoT
Although SSH provides robust security features, adhering to best practices is crucial to minimizing risks. Below are some recommendations to enhance your SSH setup:
- Utilize strong passwords or passphrase-protected private keys to fortify authentication.
- Enable two-factor authentication for an additional layer of security.
- Limit access to trusted IP addresses by configuring firewall rules.
- Regularly audit SSH logs to detect and respond to suspicious activity promptly.
Addressing Common Security Threats
Despite its strengths, SSH remote access IoT free solutions are not immune to security threats. Potential risks include brute-force attacks, man-in-the-middle attacks, and misconfigured servers. Staying informed about these threats and implementing preventive measures is essential for maintaining a secure environment.
Troubleshooting Common SSH Issues
Even with its reliability, SSH remote access IoT free solutions may occasionally encounter issues. Below are some common problems and their corresponding solutions:
Connection Refused
Ensure that the SSH server is operational and that firewall rules permit traffic on the SSH port. Double-check the IP address and port number used for the connection.
Authentication Failed
Verify the private key file’s permissions and confirm that the public key has been correctly copied to the IoT device. If using password-based authentication, recheck the username and password for accuracy.
Timeout Errors
Adjust the timeout settings on your SSH client or reduce the number of concurrent connections. Ensure a stable internet connection and assess network latency to resolve the issue.
Scalability Considerations for SSH Remote Access IoT
As your IoT deployment scales, ensuring scalability becomes paramount. SSH remote access IoT free solutions can effectively handle large-scale deployments with strategic planning and optimization:
Load Balancing
Implement load balancing techniques to distribute incoming SSH connections across multiple servers, thereby enhancing performance and reliability.
Centralized Management
Employ centralized management tools to simplify the configuration and monitoring of SSH servers across all devices. This approach not only streamlines maintenance but also reduces the likelihood of human error.
Use Cases for SSH Remote Access IoT Free
SSH remote access IoT free solutions find applications across various industries and domains, including:
- Smart Homes: Gain control over and monitor smart devices such as thermostats, cameras, and lighting systems remotely.
- Industrial Automation: Efficiently manage and troubleshoot industrial equipment in real-time, enhancing productivity and efficiency.
- Agriculture: Monitor critical parameters like soil moisture levels, temperature, and environmental conditions using IoT sensors.
- Healthcare: Securely access medical devices and patient data for remote diagnostics and personalized treatment plans.
The Future of SSH Remote Access in IoT
As IoT continues to evolve and expand, the role of SSH remote access will only grow in importance. Emerging technologies such as quantum encryption and blockchain have the potential to further enhance the security and reliability of SSH-based solutions. Additionally, advancements in artificial intelligence and machine learning could lead to smarter and more efficient management of IoT devices, paving the way for a more connected and secure future.
Conclusion and Call to Action
SSH remote access IoT free solutions offer a secure, cost-effective, and scalable method for managing connected devices. By following the guidelines outlined in this article, you can implement robust SSH configurations tailored to your specific needs. We invite you to explore the resources mentioned, share your experiences in the comments below, and delve into our other articles for further insights into IoT and related technologies. Stay ahead of the curve by staying informed about the latest trends in the industry and leveraging SSH to unlock the full potential of your IoT ecosystem.