As technology continues to evolve and an increasing number of devices become interconnected, the importance of robust security measures has never been more critical. One of the most effective solutions for safeguarding Internet of Things (IoT) devices is the implementation of a remote IoT firewall. This advanced technology offers unparalleled protection against cyber threats, ensuring that your network remains secure regardless of your location.
A remote IoT firewall is specifically engineered to protect smart devices from unauthorized access and malicious attacks. With the rapid expansion of IoT networks, both businesses and individuals must prioritize the development and enhancement of their cybersecurity infrastructure. This article will explore the top remote IoT firewalls available on the market, their features, and why they are essential for modern-day security.
Whether you're a small business owner, an IT professional, or a tech-savvy individual, understanding the importance of a remote IoT firewall can significantly enhance the safety and reliability of your network. In this comprehensive guide, we'll delve into the key aspects of remote IoT firewalls, empowering you to make informed decisions about your cybersecurity needs.
Read also:Lola Shark Tale
Table of Contents
- Introduction to Remote IoT Firewall
- Benefits of Using a Remote IoT Firewall
- Types of Remote IoT Firewalls
- Comparison of Top Remote IoT Firewalls
- How to Implement a Remote IoT Firewall
- Enhancing IoT Security with Remote Firewalls
- Common Challenges in IoT Security
- Emerging Trends in Remote IoT Firewalls
- Tips for Choosing the Best Remote IoT Firewall
- The Future of Remote IoT Firewalls
Understanding the Role of Remote IoT Firewalls
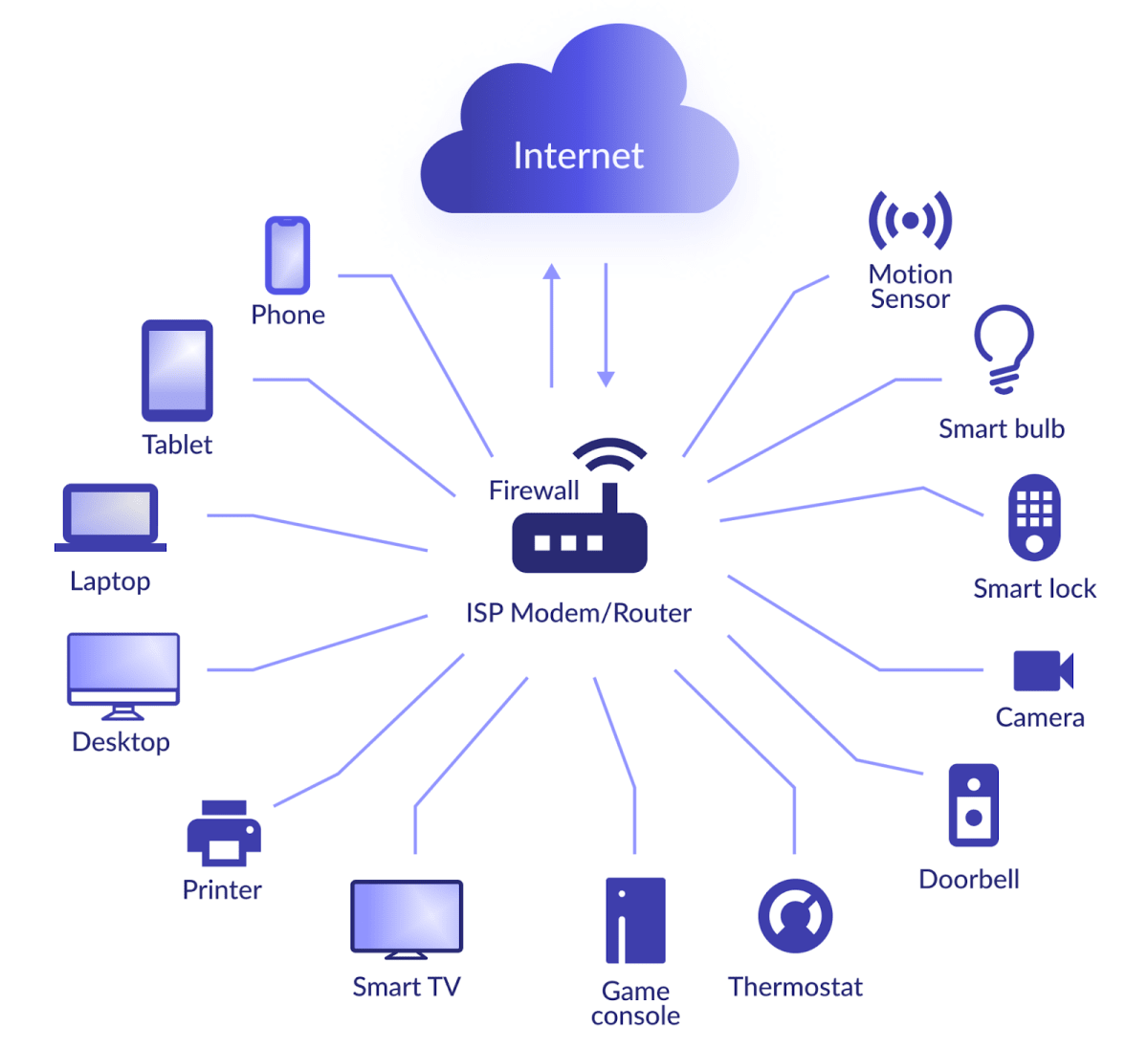
A remote IoT firewall is a specialized cybersecurity solution designed to protect IoT devices and networks from external threats. Unlike traditional firewalls, which focus on securing corporate networks, remote IoT firewalls are specifically tailored to address the unique vulnerabilities of IoT devices. These devices, ranging from smart thermostats to industrial sensors, often lack robust security protocols, making them prime targets for cybercriminals.
Why Remote IoT Firewalls Are Essential in Today's Digital Landscape
IoT devices are increasingly integrated into critical infrastructure, from healthcare systems to smart cities. This widespread adoption necessitates advanced security measures to prevent unauthorized access and data breaches. A remote IoT firewall serves as a digital barrier, monitoring and filtering incoming and outgoing traffic to ensure only legitimate connections are allowed. Furthermore, these firewalls provide real-time threat detection and response, reducing the risk of cyberattacks that could compromise sensitive data or disrupt essential services.
The Advantages of Implementing a Remote IoT Firewall
Implementing a remote IoT firewall offers numerous advantages for both businesses and individuals. Below are some of the key benefits:
- Enhanced Security: Provides robust protection for IoT devices against unauthorized access and cyber threats.
- Real-Time Monitoring: Offers continuous surveillance of network activity to detect and mitigate threats promptly.
- Scalability: Easily adapts to growing IoT networks, ensuring consistent protection as more devices are added.
- Centralized Management: Allows administrators to control and configure security settings from a single interface, streamlining operations.
These benefits underscore the importance of remote IoT firewalls in maintaining the integrity and reliability of IoT networks, making them an indispensable tool for modern cybersecurity.
Exploring the Different Types of Remote IoT Firewalls
Remote IoT firewalls come in various forms, each tailored to specific needs and environments. Understanding the different types can help you choose the most suitable solution for your requirements:
1. Cloud-Based Firewalls
Cloud-based remote IoT firewalls offer unparalleled flexibility and ease of deployment. Hosted on remote servers, they enable users to access and manage their firewall settings from anywhere with an internet connection. This makes them ideal for organizations with distributed teams or those seeking a cost-effective solution.
Read also:Does Jonny Lee Miller Have Tattoos
2. On-Premises Firewalls
On-premises firewalls are installed directly on local networks, providing greater control and customization options. They are particularly advantageous for organizations that prioritize data privacy and compliance with strict security regulations. These firewalls offer enhanced data sovereignty and are often preferred by enterprises handling sensitive information.
3. Hybrid Firewalls
Hybrid firewalls combine the advantages of both cloud-based and on-premises solutions, offering a balanced approach to IoT security. They enable organizations to leverage the scalability of cloud services while maintaining the security of on-premises infrastructure. This hybrid model is especially beneficial for businesses requiring flexibility and robust security.
Comparing the Top Remote IoT Firewalls in the Market
Several remote IoT firewalls stand out in the market due to their advanced features and robust security capabilities. Below is a detailed comparison of some of the best options:
1. Palo Alto Networks
Palo Alto Networks offers a comprehensive suite of remote IoT firewalls that provide advanced threat prevention and network segmentation. Their solutions are widely regarded for their ease of use and seamless integration with existing IT infrastructures. With cutting-edge features like automated threat intelligence, Palo Alto Networks is a top choice for organizations seeking comprehensive security.
2. Fortinet
Fortinet's remote IoT firewalls are renowned for their high performance and scalability. They offer a range of features, including AI-driven threat detection and automated response mechanisms, making them suitable for large-scale IoT deployments. Fortinet's commitment to innovation ensures that their firewalls remain at the forefront of cybersecurity technology.
3. Check Point
Check Point delivers state-of-the-art remote IoT firewalls that prioritize security without compromising speed. Their solutions are designed to protect against the latest cyber threats while ensuring seamless connectivity for IoT devices. With features like unified threat management and real-time threat intelligence, Check Point is a leading provider of IoT security solutions.
A Step-by-Step Guide to Implementing a Remote IoT Firewall
Implementing a remote IoT firewall involves several critical steps to ensure optimal performance and security:
- Assess Your Network: Identify all IoT devices and their connection points to determine the scope of your firewall implementation. This step is crucial for creating a tailored security strategy.
- Select the Right Solution: Choose a remote IoT firewall that aligns with your network's size, complexity, and security requirements. Consider factors such as scalability, ease of management, and compatibility with existing systems.
- Configure Settings: Customize firewall rules and policies to address specific threats and vulnerabilities. This step ensures that your firewall is optimized for your unique environment.
- Test and Monitor: Conduct thorough testing to ensure the firewall functions as intended and continuously monitor its performance for any anomalies. Regular updates and maintenance are essential for maintaining robust security.
By following these steps, you can establish a secure and efficient remote IoT firewall system that meets your organization's needs.
Strengthening IoT Security with Remote Firewalls
Remote IoT firewalls play a pivotal role in enhancing the overall security of IoT networks. By implementing these firewalls, organizations can:
- Prevent unauthorized access to sensitive data and devices, ensuring the privacy and integrity of critical information.
- Reduce the risk of malware infections and ransomware attacks, protecting networks from malicious actors.
- Ensure compliance with industry regulations and standards, avoiding potential legal and financial consequences.
- Improve network performance by blocking unnecessary traffic, optimizing resource utilization and reducing latency.
These measures contribute to a more secure and resilient IoT ecosystem, safeguarding both businesses and consumers from potential cyber threats.
Addressing the Common Challenges in IoT Security
Despite the benefits of remote IoT firewalls, several challenges can hinder their effectiveness:
1. Device Vulnerabilities
Many IoT devices lack basic security features, making them susceptible to attacks. Ensuring all devices meet minimum security standards is essential for maintaining a secure network. Regular firmware updates and security audits can help mitigate this issue.
2. Limited Resources
Smaller organizations may face resource constraints when implementing and managing remote IoT firewalls. Outsourcing to managed security service providers (MSSPs) can alleviate this challenge, providing access to expert support and advanced tools without the need for extensive in-house resources.
3. Rapidly Evolving Threats
Cyber threats are constantly evolving, requiring regular updates and improvements to firewall systems. Staying informed about the latest trends and technologies is vital for maintaining robust security. Organizations should invest in continuous training and education for their IT teams to keep pace with emerging threats.
The Evolution of Remote IoT Firewalls: Emerging Trends
The field of remote IoT firewalls is rapidly advancing, with several emerging trends shaping the future of IoT security:
1. Artificial Intelligence and Machine Learning
AI and machine learning are being integrated into remote IoT firewalls to enhance threat detection and response capabilities. These technologies enable firewalls to learn from past attacks and adapt to new threats in real-time, providing proactive protection against sophisticated cyber threats.
2. Zero Trust Architecture
Zero trust architecture is gaining popularity as a security model for IoT networks. It assumes that no device or user can be trusted by default, requiring continuous verification and authentication. This approach minimizes the risk of unauthorized access and ensures that only legitimate connections are allowed.
3. Edge Computing
Edge computing is being used to improve the efficiency and responsiveness of remote IoT firewalls. By processing data closer to the source, edge computing reduces latency and enhances security, enabling faster threat detection and response times.
Practical Tips for Choosing the Best Remote IoT Firewall
Selecting the right remote IoT firewall can be challenging, but the following tips can help simplify the process:
- Consider your specific security needs and budget when evaluating options. Prioritize solutions that offer the features and functionality required to protect your network effectively.
- Look for firewalls with advanced features such as AI-driven threat detection, centralized management, and real-time monitoring. These features can significantly enhance the effectiveness of your security strategy.
- Choose solutions that are compatible with your existing IT infrastructure and can scale with your network. This ensures that your firewall remains effective as your organization grows and evolves.
- Read customer reviews and case studies to assess the performance and reliability of potential firewalls. This can provide valuable insights into the strengths and limitations of each solution.
By following these tips, you can find a remote IoT firewall that meets your unique requirements and provides comprehensive protection for your IoT network.
The Future of Remote IoT Firewalls: Innovations and Advancements
The future of remote IoT firewalls looks promising, with ongoing advancements in technology driving innovation and improvement. As IoT networks continue to expand and evolve, so too will the capabilities of remote IoT firewalls. Expect to see increased integration of AI, machine learning, and edge computing, as well as more robust and adaptable security solutions.
Organizations and individuals must remain vigilant and proactive in their approach to IoT security, embracing these advancements to protect their networks and data from emerging threats. By staying informed and investing in cutting-edge technologies, you can ensure that your IoT infrastructure remains secure and resilient.
Conclusion
In conclusion, remote IoT firewalls are indispensable tools for safeguarding IoT networks against cyber threats. By understanding the benefits, types, and implementation strategies of these firewalls, you can make informed decisions about your cybersecurity needs. Remember to stay updated on the latest trends and technologies to ensure your network remains secure and resilient in an increasingly interconnected world.
We invite you to share your thoughts and experiences with remote IoT firewalls in the comments section below. Additionally, feel free to explore other articles on our site for more insights into cybersecurity and IoT solutions.