As technology evolves at a rapid pace, the demand for secure and efficient remote access solutions continues to rise. Navigating how to use RemoteIoT behind a firewall is a critical skill for businesses and individuals aiming to manage IoT devices securely from any location globally. This comprehensive guide explores best practices and strategies to ensure smooth connectivity while maintaining robust security measures.
RemoteIoT has revolutionized the Internet of Things (IoT) landscape, empowering users to monitor and control devices remotely. However, accessing these devices behind corporate or personal firewalls can pose significant challenges. This article provides actionable solutions and detailed instructions to help you overcome these hurdles effectively.
Whether you're a network administrator, an IoT enthusiast, or a small business owner, this guide will equip you with the knowledge and tools necessary to configure and manage RemoteIoT securely. Let’s get started!
Read also:Jeff Carriveau
Contents Overview
- Introduction to RemoteIoT
- Understanding Firewall Fundamentals
- The Importance of Using RemoteIoT Behind a Firewall
- Comprehensive Setup Guide
- Enhancing Security for RemoteIoT
- Addressing Common Issues
- Maximizing Performance
- Best Practices for Secure Connections
- Advanced Configuration Techniques
- Final Thoughts
Exploring RemoteIoT
RemoteIoT is a state-of-the-art platform designed to facilitate remote access to IoT devices, enabling users to interact with their devices from virtually anywhere with an internet connection. This platform offers a wide array of features, such as real-time monitoring, automated alerts, and advanced remote control capabilities, making it an indispensable tool for modern businesses and individuals alike.
Core Features of RemoteIoT
- Robust and secure device management
- Real-time data analytics for actionable insights
- Customizable dashboards tailored to user preferences
- Seamless integration with third-party applications
By leveraging the capabilities of RemoteIoT, businesses can significantly enhance operational efficiency and productivity. However, ensuring secure access to these devices, especially when they are situated behind firewalls, remains a key challenge that requires careful planning and execution.
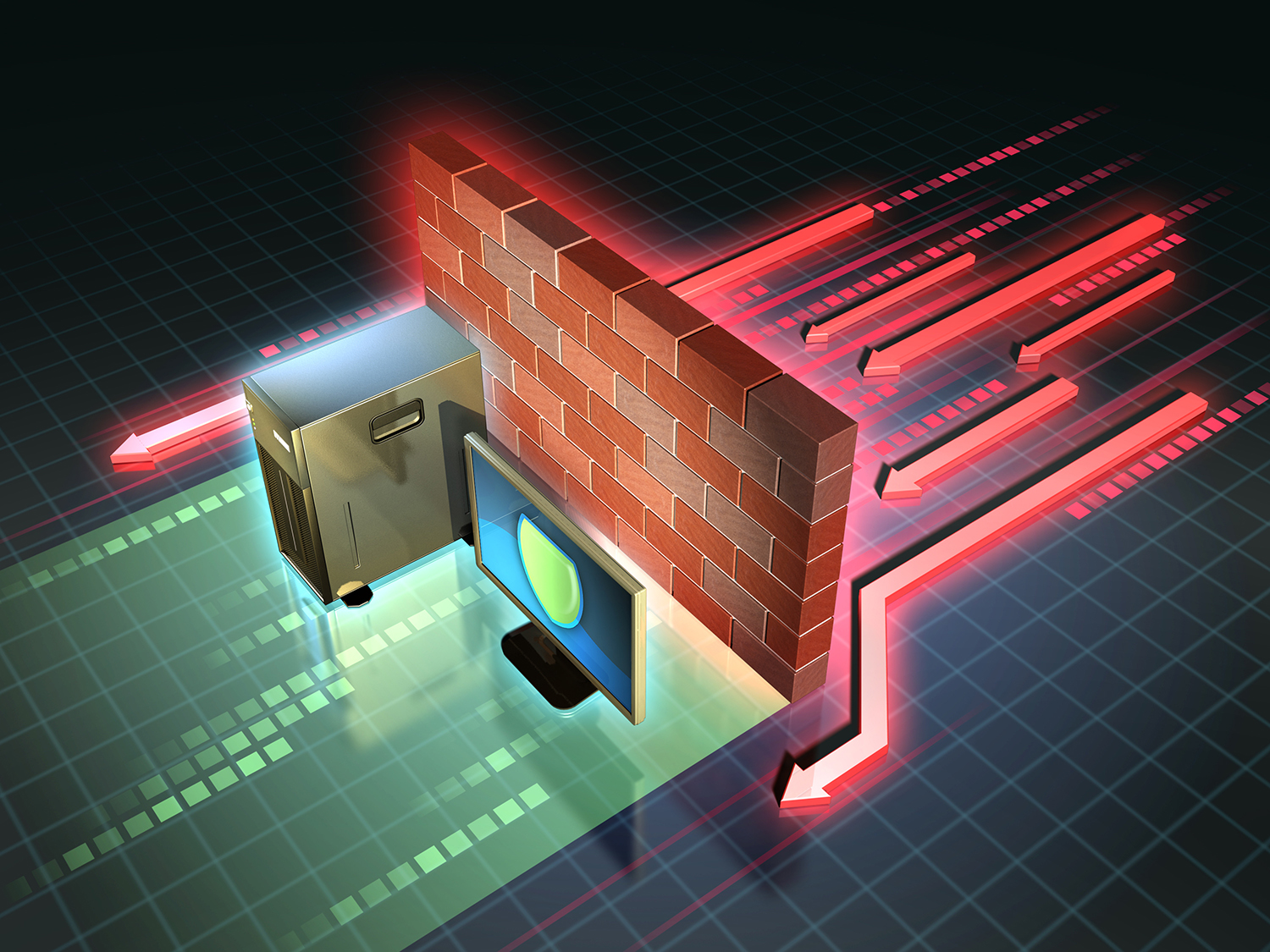
Understanding the Role of Firewalls
A firewall serves as a critical component of network security, monitoring and controlling both incoming and outgoing network traffic based on predefined security protocols. It acts as a protective barrier between internal, trusted networks and external, untrusted networks, such as the internet, thereby safeguarding sensitive data and resources.
Types of Firewalls and Their Functions
- Packet-filtering firewalls: Inspect individual packets of data to determine whether they should be allowed or blocked.
- Stateful inspection firewalls: Maintain context awareness by tracking active connections and applying rules dynamically.
- Application-level gateways: Operate at the application layer to provide deeper inspection and filtering capabilities.
- Next-generation firewalls: Combine traditional firewall features with advanced threat detection and protection mechanisms.
Gaining a thorough understanding of the type of firewall you are working with is essential for configuring RemoteIoT effectively. Each firewall type comes with its own unique set of rules and limitations, which must be carefully considered during the setup process.
The Case for Using RemoteIoT Behind a Firewall
Deploying RemoteIoT behind a firewall offers numerous benefits, including enhanced security, greater control over device access, and adherence to corporate policies. By configuring your firewall appropriately, you can ensure that only authorized personnel have access to your IoT devices, thereby minimizing the risk of unauthorized access and potential data breaches.
According to industry projections by Gartner, the global IoT market is expected to reach a staggering $1.1 trillion by 2030. As more organizations adopt IoT solutions, the importance of secure remote access becomes increasingly evident, making the integration of RemoteIoT behind firewalls a strategic necessity.
Read also:Brad Paisley Wife And Kids A Closer Look At The Country Stars Family Life
Comprehensive Setup Guide
Setting up RemoteIoT behind a firewall demands meticulous planning and execution. Follow the steps outlined below to ensure a seamless configuration process:
Step 1: Identify Your Firewall Type
Begin by determining the specific type of firewall you are using and consult the manufacturer’s documentation for detailed configuration instructions tailored to your setup.
Step 2: Configure Port Forwarding
Set up port forwarding on your router to enable incoming traffic to reach your RemoteIoT server. Common ports utilized by RemoteIoT include 80 (HTTP) and 443 (HTTPS), though these may vary depending on your specific requirements.
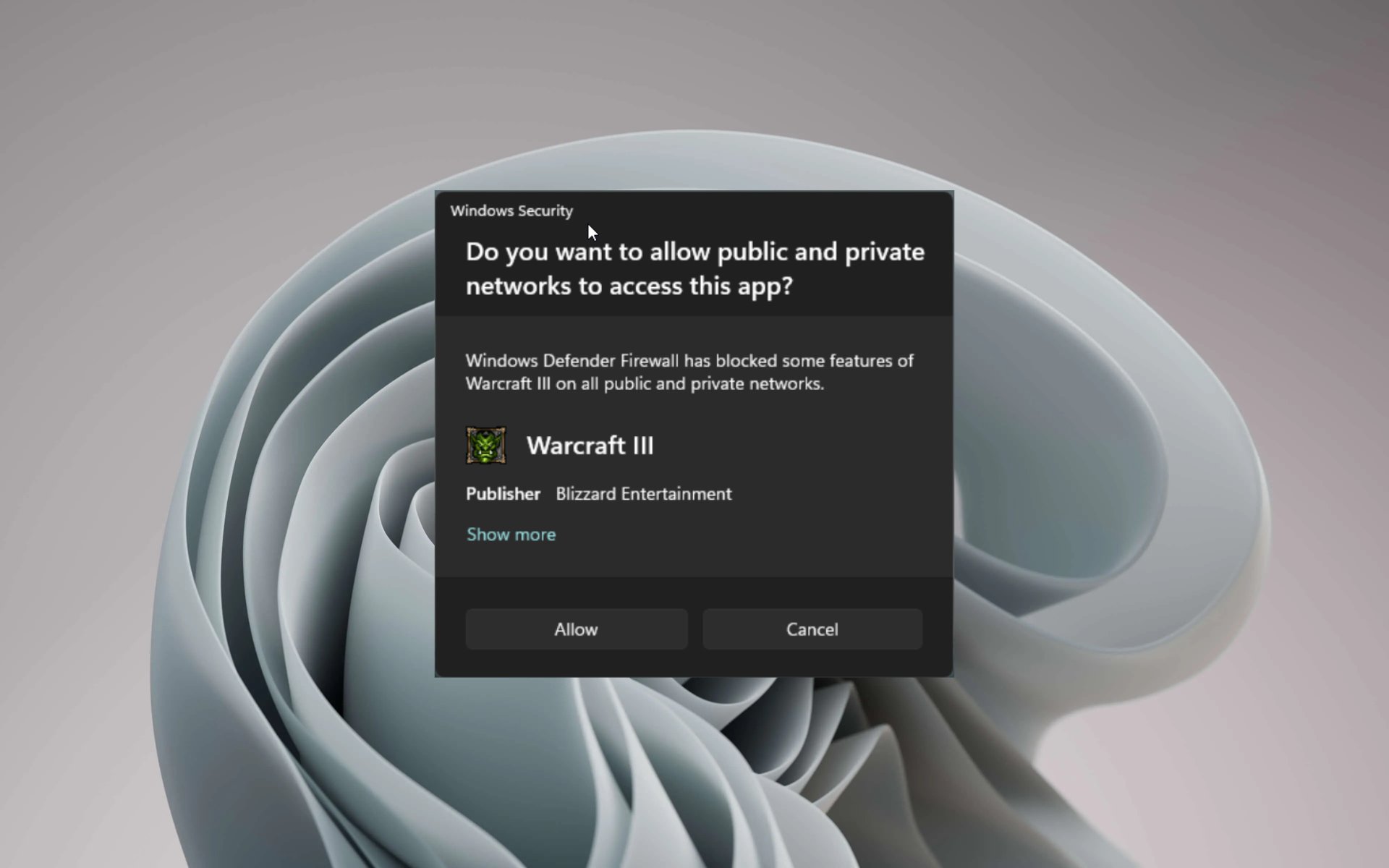
Step 3: Adjust Firewall Rules
Create customized rules within your firewall to permit traffic from trusted IP addresses or networks. This step ensures that only authorized users can gain access to your IoT devices, thereby enhancing overall security.
Step 4: Test Your Configuration
Once your firewall has been configured, thoroughly test the connection to confirm that RemoteIoT is accessible from outside your network. This step is crucial for identifying and resolving any potential issues before deployment.
Strengthening Security for RemoteIoT
Security should always remain a top priority when configuring RemoteIoT behind a firewall. Below are several strategies to enhance the security of your setup:
- Implement strong, unique passwords for all user accounts to prevent unauthorized access.
- Enable two-factor authentication (2FA) for an additional layer of protection.
- Regularly update your firewall and RemoteIoT software to address vulnerabilities and incorporate the latest security patches.
- Monitor access logs diligently to detect and respond to any suspicious activity promptly.
Resolving Common Issues
Even with meticulous planning, challenges may arise during the setup of RemoteIoT behind a firewall. Below are some frequently encountered problems along with their corresponding solutions:
Issue 1: Inability to Connect to RemoteIoT Server
Solution: Verify that port forwarding is correctly configured and that your firewall rules allow incoming traffic on the designated ports. Double-check all settings to ensure accuracy.
Issue 2: Slow Connection Speeds
Solution: Optimize your network settings and ensure that your internet connection meets the minimum requirements for RemoteIoT. Consider upgrading your infrastructure if necessary to improve performance.
Issue 3: Security Alerts
Solution: Examine your firewall logs closely and adjust rules as needed to prevent unauthorized access attempts. Regularly review logs to stay informed about potential threats.
Boosting Performance
To achieve optimal performance of RemoteIoT behind a firewall, consider adopting the following strategies:
- Deploy a dedicated server for RemoteIoT to minimize resource contention and enhance stability.
- Implement load balancing to distribute traffic evenly across multiple servers, ensuring consistent performance under varying workloads.
- Enable data compression to reduce bandwidth usage and accelerate data transmission.
By optimizing your setup, you can significantly improve the speed and reliability of your RemoteIoT connections, delivering a seamless user experience.
Best Practices for Secure Connections
Adhering to best practices is vital for maintaining secure connections to your IoT devices. Below are some recommendations to help you safeguard your devices and data:
- Regularly review and update your firewall rules to reflect evolving security requirements and address new threats.
- Restrict access to trusted IP addresses or networks to limit exposure to potential security risks.
- Encrypt all data transmissions using SSL/TLS to protect sensitive information during transit.
Implementing these practices will fortify your defenses and protect your devices and data from unauthorized access and malicious attacks.
Exploring Advanced Configurations
For users seeking to take their RemoteIoT setup to the next level, consider the following advanced configuration options:
Option 1: Virtual Private Network (VPN)
Set up a VPN to establish a secure tunnel between your device and the RemoteIoT server. This ensures that all data transmissions are encrypted and protected from interception, providing an additional layer of security.
Option 2: Reverse Proxy
Utilize a reverse proxy to manage incoming requests and distribute them to the appropriate servers. This not only improves performance but also enhances security by concealing the actual server IP address from external entities.
Final Thoughts
In summary, mastering the use of RemoteIoT behind a firewall is essential for anyone aiming to manage IoT devices securely. By following the steps and strategies outlined in this guide, you can configure your firewall to enable seamless access to your devices while maintaining the highest level of security.
We invite you to share your thoughts and experiences in the comments section below. If you found this article informative, please consider sharing it with your network. For more insightful content on IoT and network security, explore our other articles and stay informed about the latest trends and best practices.
Stay safe, stay connected, and embrace the power of secure IoT management with RemoteIoT!