Remote management of IoT devices using SSH on AWS is an essential strategy for businesses aiming to achieve efficient device management and secure connectivity. As IoT continues to grow exponentially, the demand for scalable and secure remote access solutions becomes increasingly critical. AWS provides a robust platform enabling organizations to utilize SSH (Secure Shell) for secure and efficient IoT device management, ensuring both operational effectiveness and data protection.
In an era where billions of IoT devices are interconnected worldwide, maintaining secure communication channels while minimizing latency and maximizing reliability is paramount. AWS delivers a comprehensive ecosystem that integrates IoT Core, EC2 instances, and various other services to facilitate secure remote access through SSH. This not only simplifies the management of IoT devices but also significantly improves operational efficiency and security.
This article explores the nuances of IoT remote access via SSH on AWS, discussing its advantages, potential challenges, and best practices. Whether you're a developer, IT professional, or business owner, understanding and implementing this solution effectively can greatly enhance the performance and security of your IoT infrastructure.
Read also:Jason Momoa Height
Table of Contents
- Introduction to IoT Remote Access via SSH on AWS
- Understanding AWS IoT Architecture
- Basics of SSH: Why It Matters in IoT
- Using AWS EC2 Instances for IoT Remote Access
- Security Best Practices for IoT Remote Access
- Scaling IoT Solutions on AWS
- Cost Considerations and Optimization
- Common Challenges and Solutions
- Real-World Applications of IoT Remote Access
- Conclusion: Taking Your IoT Infrastructure to the Next Level
Introduction to IoT Remote Access via SSH on AWS
The Internet of Things (IoT) has transformed the way we interact with technology, enabling billions of devices to connect and communicate effortlessly. However, managing these devices remotely presents significant challenges, particularly in ensuring secure and efficient access. This is precisely where IoT remote access via SSH on AWS proves invaluable.
AWS provides a powerful platform that integrates IoT Core, EC2 instances, and other services to facilitate secure remote access. By leveraging SSH, organizations can manage their IoT devices from any location globally while maintaining the highest level of security. This approach not only simplifies device management but also enhances operational efficiency, making it a cornerstone for modern IoT infrastructure.
Why Choose AWS for IoT Remote Access?
AWS offers numerous advantages for IoT remote access, including:
- Scalability: Easily expand your IoT infrastructure to meet increasing demands without compromising performance.
- Security: Implement cutting-edge security measures to safeguard your devices and data against unauthorized access.
- Reliability: Ensure consistent and uninterrupted connectivity with AWS's extensive global infrastructure.
- Integration: Seamlessly integrate with other AWS services to enhance functionality and streamline operations.
Understanding AWS IoT Architecture
AWS IoT architecture is meticulously designed to cater to the specific requirements of IoT applications, including secure remote access. The architecture comprises several key components that work together to enable seamless device management.
Key Components of AWS IoT Architecture
- AWS IoT Core: A managed cloud service that facilitates secure interaction between connected devices, cloud applications, and other devices.
- AWS EC2 Instances: Virtual servers that provide the necessary compute power for IoT applications, including remote access via SSH.
- AWS Lambda: A serverless computing service that allows you to execute code in response to events, such as device connections or data updates.
- AWS IoT Device Management: A service that simplifies the onboarding, organization, monitoring, and remote management of IoT devices at scale.
Basics of SSH: Why It Matters in IoT
Secure Shell (SSH) is a cryptographic network protocol that ensures secure communication between devices over unsecured networks. In the context of IoT, SSH plays a pivotal role in guaranteeing the security and integrity of remote access operations.
Advantages of Using SSH for IoT Remote Access
- Encryption: Protects sensitive data transmitted between devices and servers, ensuring confidentiality.
- Authentication: Ensures that only authorized users can access and manage IoT devices, reducing the risk of unauthorized access.
- Integrity: Verifies the authenticity of transmitted data, preventing tampering and ensuring data reliability.
Using AWS EC2 Instances for IoT Remote Access
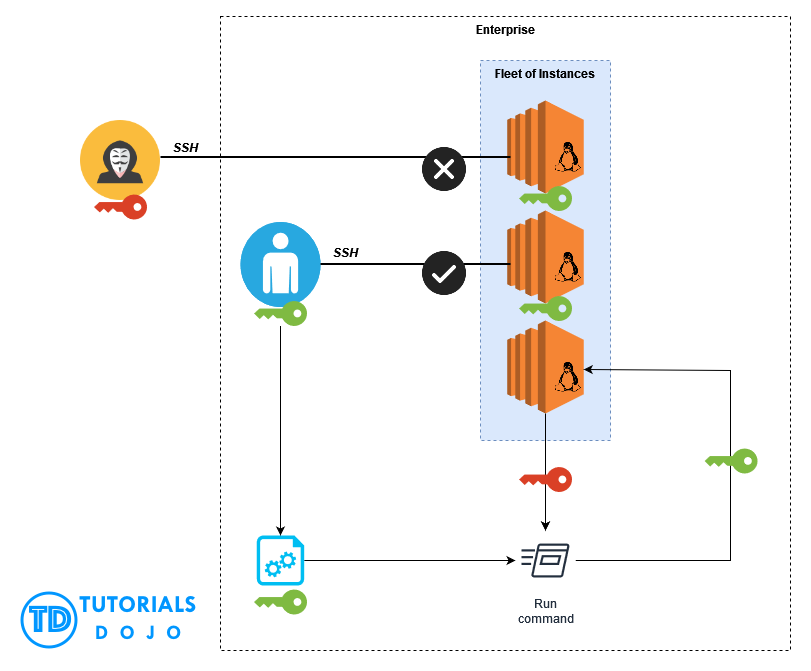
AWS EC2 instances form the backbone of IoT remote access solutions, providing the compute power necessary for secure device management. By utilizing EC2 instances, organizations can establish secure SSH connections to their IoT devices, enabling efficient remote management and monitoring.
Read also:Telegram Teen Zoo
Setting Up an EC2 Instance for IoT Remote Access
To set up an EC2 instance for IoT remote access, follow these detailed steps:
- Launch an EC2 Instance: Begin by launching an EC2 instance with the appropriate Amazon Machine Image (AMI) and instance type based on your workload requirements.
- Configure Security Groups: Adjust security settings to allow SSH access exclusively from authorized IP addresses, enhancing security.
- Install and Configure SSH Server Software: Install and configure SSH server software on the instance to enable secure remote connections.
- Connect Using an SSH Client: Use an SSH client to connect to the instance and begin managing IoT devices remotely.
Security Best Practices for IoT Remote Access
Securing IoT remote access is crucial to protecting your devices and data from unauthorized access. By adhering to best practices, you can minimize risks and maintain the highest level of security.
Key Security Best Practices
- Strong Passwords: Use complex, unique passwords for SSH access to prevent brute-force attacks.
- Two-Factor Authentication (2FA): Enable 2FA for an additional layer of security, making it harder for unauthorized users to gain access.
- IP Address Restrictions: Limit SSH access to specific IP addresses or ranges to reduce the attack surface.
- Regular Updates: Regularly update and patch your devices and software to address vulnerabilities and maintain security.
Scaling IoT Solutions on AWS
As your IoT infrastructure expands, the need for scalable solutions becomes increasingly important. AWS provides the tools and resources necessary to scale your IoT solutions effectively, ensuring optimal performance and reliability.
Strategies for Scaling IoT Solutions
- AWS Auto Scaling: Dynamically adjust resources based on demand to maintain performance and efficiency.
- Load Balancing: Distribute traffic across multiple instances to prevent bottlenecks and ensure consistent performance.
- AWS CloudWatch: Utilize AWS CloudWatch for comprehensive monitoring and alerting to stay informed about system health and performance.
Cost Considerations and Optimization
Managing costs is a critical aspect of implementing IoT remote access solutions on AWS. By understanding cost considerations and optimizing resource usage, you can reduce expenses while maintaining high performance.
Tips for Cost Optimization
- AWS Cost Explorer: Use AWS Cost Explorer to analyze and manage your expenses, identifying areas for cost reduction.
- Instance Selection: Choose the right instance type and size for your workload to avoid over-provisioning and unnecessary costs.
- Resource Management: Regularly review and terminate unused instances and resources to prevent unnecessary charges and optimize spending.
Common Challenges and Solutions
Implementing IoT remote access via SSH on AWS comes with its own set of challenges. Understanding these challenges and their solutions can help you overcome obstacles and ensure a successful deployment.
Addressing Common Challenges
- Latency: Opt for AWS regions closer to your devices to minimize latency and improve responsiveness.
- Bandwidth: Optimize data transfer to reduce bandwidth usage, ensuring efficient communication and cost-effectiveness.
- Security: Implement robust security measures to protect your devices and data, safeguarding against potential threats.
Real-World Applications of IoT Remote Access
IoT remote access via SSH on AWS has a wide range of real-world applications across various industries. From smart homes to industrial automation, this solution enables organizations to manage their IoT devices efficiently and securely.
Examples of Real-World Applications
- Remote Monitoring of Industrial Equipment: Monitor and manage industrial equipment in real-time, ensuring optimal performance and reducing downtime.
- Smart Home Automation and Control: Control smart home devices remotely, enhancing convenience and energy efficiency.
- Environmental Monitoring and Data Collection: Collect and analyze environmental data for scientific research, urban planning, and resource management.
Conclusion: Taking Your IoT Infrastructure to the Next Level
In summary, IoT remote access via SSH on AWS provides a powerful solution for managing IoT devices securely and efficiently. By leveraging AWS's robust platform and adhering to best practices, organizations can elevate their IoT infrastructure, ensuring optimal performance and security.
We invite you to share your thoughts and experiences in the comments below. Additionally, feel free to explore other articles on our site for further insights into IoT and AWS solutions. Together, let's build a smarter, more connected world.
Sources:
- AWS Documentation: https://docs.aws.amazon.com
- IoT Security Best Practices: https://www.nist.gov