Navigating SSH key management in a remote IoT environment can be complex, yet it is essential for maintaining secure and efficient network operations. As IoT devices become more integrated into everyday systems, the importance of robust security measures cannot be overstated. Understanding and implementing effective SSH key management practices is vital for safeguarding sensitive information and ensuring seamless communication between devices.
With the rapid expansion of the Internet of Things (IoT), the demand for secure remote access to devices has surged. RemoteIoT SSH key management is pivotal in this process, ensuring that only authorized users and devices can access the network. Without proper SSH key management, organizations risk unauthorized access, data breaches, and operational disruptions that could compromise their entire network.
This article explores the complexities of RemoteIoT SSH key management, offering valuable insights, best practices, and actionable tips. By the end of this guide, you will gain a comprehensive understanding of how to manage SSH keys effectively and securely in a remote IoT environment.
Read also:Franco Columbu
Table of Contents
- Understanding SSH and Its Role in IoT Security
- Overview of RemoteIoT SSH Key Management
- Revolutionizing Authentication with Biometric SSH Keys
- Best Practices for Secure SSH Key Management
- Critical Security Considerations in SSH Key Management
- Leveraging Tools and Technologies for Efficient SSH Key Management
- Streamlining SSH Key Management with Automation
- Avoiding Common Pitfalls in SSH Key Management
- Meeting Industry Standards and Compliance Requirements
- Exploring Future Trends in RemoteIoT SSH Key Management
Understanding SSH and Its Role in IoT Security
Secure Shell (SSH) is a cryptographic network protocol designed to provide secure data communication over unsecured networks. It is widely utilized for remote device management, file transfer, and secure command execution. In the context of RemoteIoT, SSH serves as a critical security layer, ensuring that communication between IoT devices and servers remains encrypted and tamper-proof.
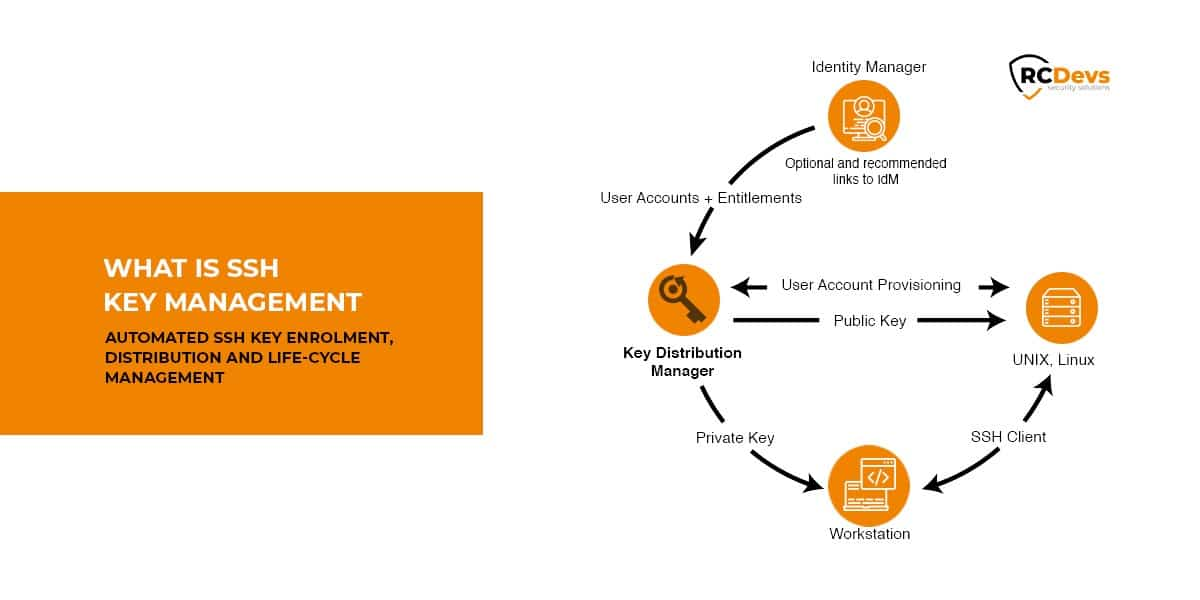
SSH key management involves the generation, distribution, and revocation of cryptographic keys used for authentication. Proper SSH key management is essential for maintaining the integrity of IoT networks, preventing unauthorized access, and ensuring compliance with industry standards.
Overview of RemoteIoT SSH Key Management
Why SSH Key Management is Critical
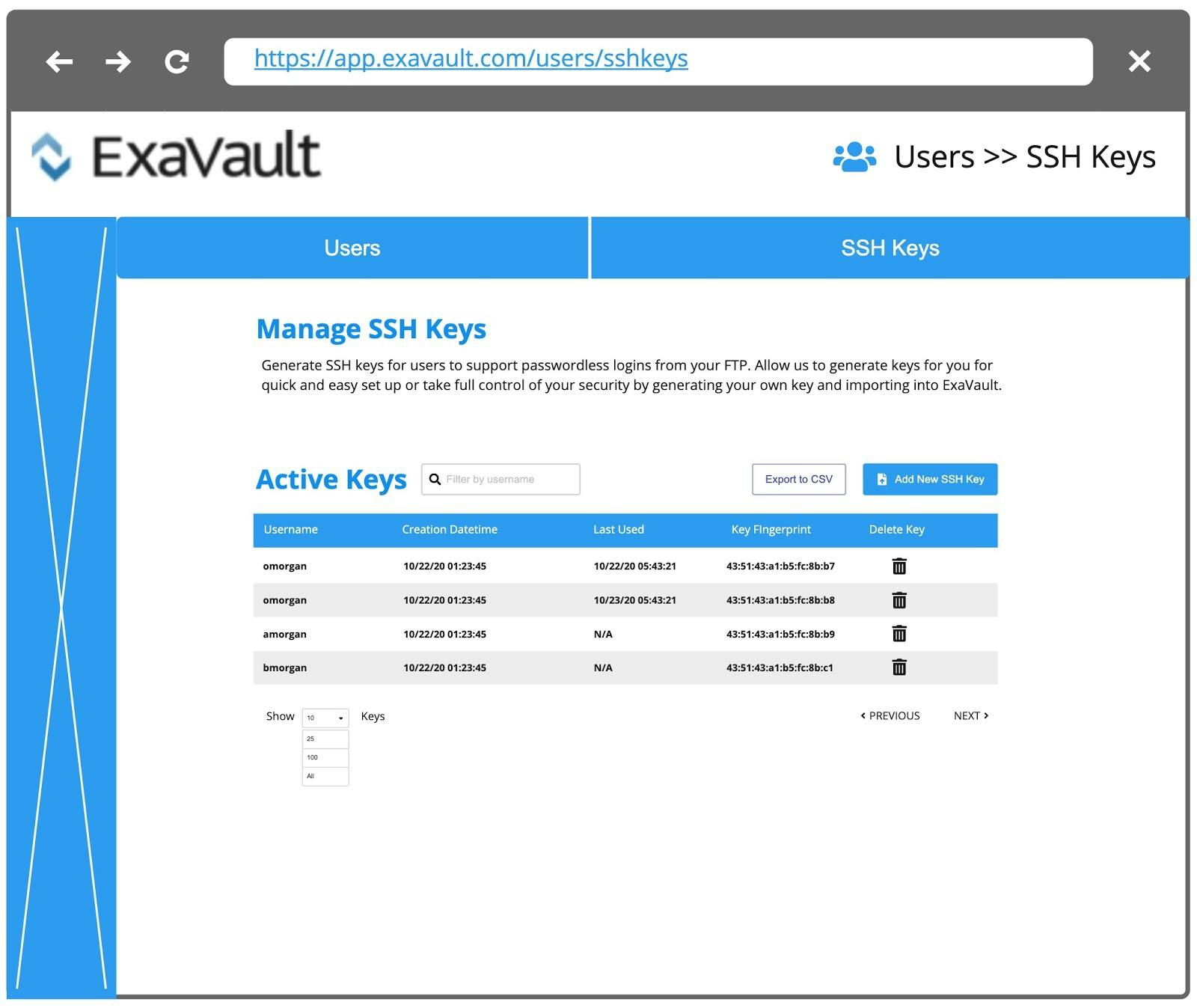
In a RemoteIoT environment, SSH key management plays a pivotal role in maintaining secure connections between devices and servers. Without effective management, organizations risk exposing sensitive data to unauthorized parties. SSH keys act as digital credentials, verifying the identity of users and devices attempting to access the network, thereby safeguarding the integrity of the system.
Key Components of SSH Key Management
- Key Generation: Creating strong, unique SSH keys tailored for each device and user to ensure maximum security.
- Key Distribution: Safely distributing keys to authorized entities while implementing stringent measures to prevent unauthorized access.
- Key Revocation: Removing access for compromised or outdated keys to maintain network security and prevent potential breaches.
Revolutionizing Authentication with Biometric SSH Keys
Biometric SSH keys represent a significant leap forward in authentication technology. By integrating biometric data, such as fingerprints or facial recognition, with traditional SSH keys, organizations can enhance security while improving user convenience. This approach reduces reliance on passwords, minimizing the risk of credential theft and strengthening overall network security.
Best Practices for Secure SSH Key Management
Implementing Strong Key Policies
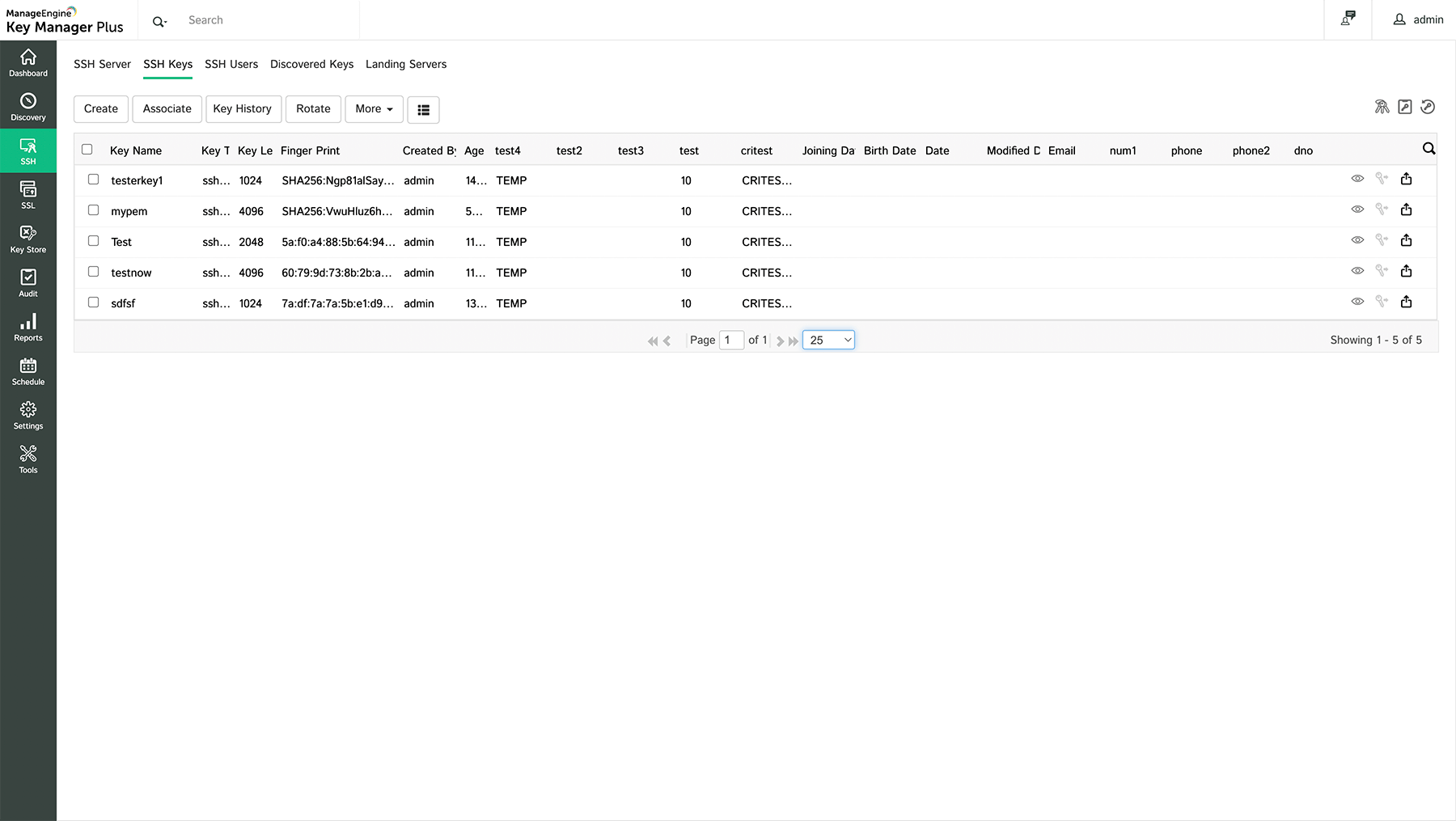
Establishing strong key policies is foundational to effective SSH key management. Organizations should define clear guidelines for key generation, storage, and rotation. Regular audits of SSH keys ensure that only active and authorized keys remain in use, reducing the risk of unauthorized access and maintaining network integrity.
Regular Key Rotation
Key rotation involves periodically replacing existing SSH keys with new ones. This practice minimizes the risk of key compromise and ensures that outdated keys are promptly removed from the system. Automating key rotation processes can streamline this task while reducing administrative overhead and enhancing security.
Read also:Telegram Teen Zoo
Critical Security Considerations in SSH Key Management
Protecting Against Key Theft
SSH keys are valuable assets that require robust protection. Organizations should implement measures such as encrypted key storage, access controls, and multi-factor authentication to safeguard SSH keys from unauthorized access. Regularly monitoring key usage can help detect and respond to potential security breaches, ensuring the network remains secure at all times.
Compliance with Industry Standards
Adhering to industry standards and regulations, such as NIST guidelines or ISO 27001, ensures that SSH key management practices meet the highest security standards. Compliance not only protects organizations from legal liabilities but also enhances trust with stakeholders by demonstrating a commitment to security excellence.
Leveraging Tools and Technologies for Efficient SSH Key Management
Several tools and technologies are available to facilitate SSH key management in a RemoteIoT environment. These include:
- SSH Key Management Systems (SKMS): Comprehensive solutions for managing SSH keys across large-scale networks, offering centralized control and automation capabilities.
- Identity and Access Management (IAM) Solutions: Platforms that integrate SSH key management with broader identity management strategies, ensuring seamless and secure access across the network.
- Automation Tools: Software designed to automate key generation, distribution, and revocation processes, reducing manual effort and minimizing the risk of human error.
Streamlining SSH Key Management with Automation
Automation plays a crucial role in streamlining SSH key management tasks. By automating key generation, distribution, and revocation, organizations can reduce manual errors, improve efficiency, and enhance security. Automation tools also enable real-time monitoring and alerting, allowing administrators to quickly respond to potential threats and maintain the integrity of the network.
Avoiding Common Pitfalls in SSH Key Management
Using Weak Keys
Using weak or default SSH keys increases the risk of unauthorized access. Organizations should always generate strong, unique keys for each device and user. Regularly updating key generation algorithms ensures that keys remain resistant to emerging threats, providing robust protection against potential breaches.
Ignoring Key Expiry
Failure to set expiration dates for SSH keys can lead to outdated keys remaining active in the system. Organizations should establish clear policies for key expiry and automate the removal of expired keys to maintain optimal security. This practice ensures that the network remains protected and that only active, authorized keys are in use.
Meeting Industry Standards and Compliance Requirements
Compliance with industry standards is essential for ensuring secure SSH key management practices. Organizations should familiarize themselves with relevant standards, such as:
- NIST SP 800-53: Provides comprehensive guidelines for managing cryptographic keys in federal information systems, ensuring robust security measures are in place.
- ISO/IEC 27001: Specifies requirements for an information security management system (ISMS), offering a structured approach to managing sensitive company information.
- CIS Controls: Offers practical recommendations for securing IT systems, including SSH key management, helping organizations implement best practices and reduce risk.
Exploring Future Trends in RemoteIoT SSH Key Management
The field of RemoteIoT SSH key management is rapidly evolving, driven by advancements in technology and increasing security demands. Emerging trends include:
- Quantum-Resistant Cryptography: Developing cryptographic algorithms resistant to quantum computing attacks, ensuring long-term security as technology advances.
- Artificial Intelligence and Machine Learning: Leveraging AI and ML for predictive threat detection and automated key management, enhancing the ability to respond to emerging threats in real time.
- Zero Trust Architecture: Implementing a zero-trust model to verify every access attempt, regardless of origin, ensuring that only authorized users and devices gain access to the network.
Conclusion
In conclusion, mastering RemoteIoT SSH key management is essential for securing IoT networks and protecting sensitive data. By understanding the importance of SSH keys, implementing best practices, and leveraging advanced tools and technologies, organizations can significantly enhance their security posture. It is crucial to regularly review and update SSH key management strategies to address emerging threats and comply with industry standards, ensuring a secure and resilient network.
We invite you to share your thoughts and experiences with RemoteIoT SSH key management in the comments section below. Additionally, explore our other articles for more insights into IoT security and best practices. Together, let's build a safer and more secure digital future!