In the modern era of interconnected devices, the ability to remotely manage IoT devices using SSH (Secure Shell) has become an essential tool for both individuals and businesses. This secure protocol offers unparalleled convenience and robust security for accessing and controlling devices from anywhere in the world. If you're looking to download free SSH IoT device access software, this guide will provide you with everything you need to know.
Whether you're a technology enthusiast, a network administrator, or someone simply aiming to streamline your device management process, understanding the tools available can significantly enhance your efficiency. This article will take you through the process of downloading and utilizing SSH IoT device access software effectively.
By the end of this guide, you will have a thorough understanding of the top options available, how to select the best software for your needs, and how to maintain the security of your devices while harnessing the power of SSH. Let's get started!
Read also:Hank Kunneman Age
Table of Contents
- Understanding SSH IoT Device Access
- The Importance of SSH for IoT Devices
- Top Free SSH IoT Device Software Options
- How to Select the Right SSH IoT Software
- Step-by-Step Installation Guide
- Enhancing Security for SSH IoT Device Management
- Best Practices for Managing SSH IoT Devices
- Addressing Common Issues and Troubleshooting
- Future Trends in SSH IoT Device Management
- Conclusion and Next Steps
Understanding SSH IoT Device Access
What is SSH?
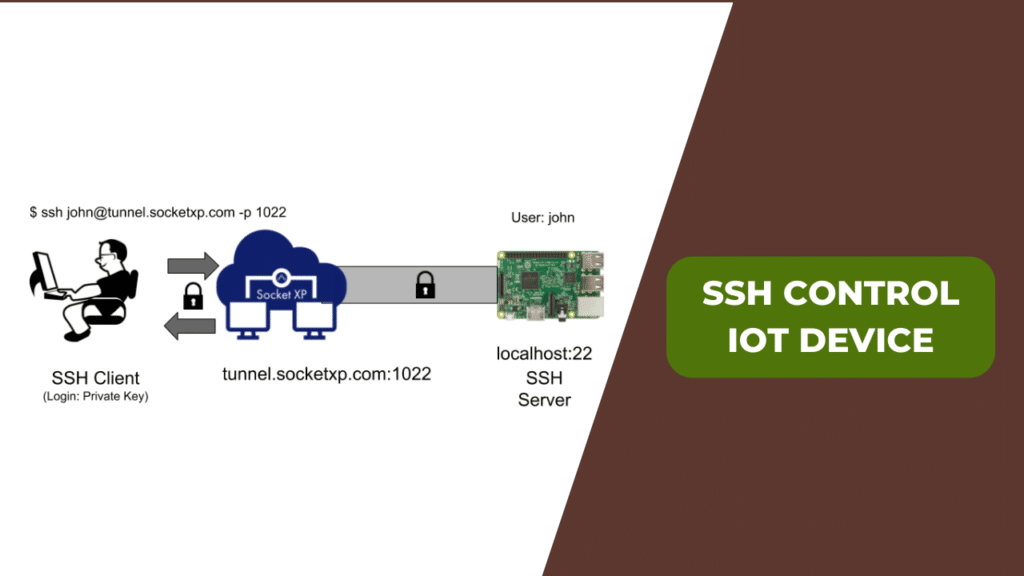
SSH, or Secure Shell, is a cryptographic network protocol designed to facilitate secure communication between devices. It enables users to access remote servers, manage IoT devices, and execute commands over potentially insecure networks. With SSH, users can connect to IoT devices from any location, ensuring both convenience and security.
Key Features of SSH
SSH is equipped with several features that make it ideal for managing IoT devices:
- Encryption: Ensures secure communication by encrypting all data transmitted between devices.
- Authentication: Implements robust mechanisms to verify that only authorized users can access devices.
- File Transfer: Supports protocols like SFTP for secure file transfer between devices.
- Compatibility: Works seamlessly with a wide range of devices and operating systems, making it versatile for various applications.
The Importance of SSH for IoT Devices
Using SSH for IoT devices offers numerous advantages over alternative remote access methods. One of the most significant benefits is the assurance of secure communication through encryption, which is especially critical for IoT devices handling sensitive information. Additionally, SSH supports advanced authentication methods, such as public key authentication, reducing the risk of unauthorized access.
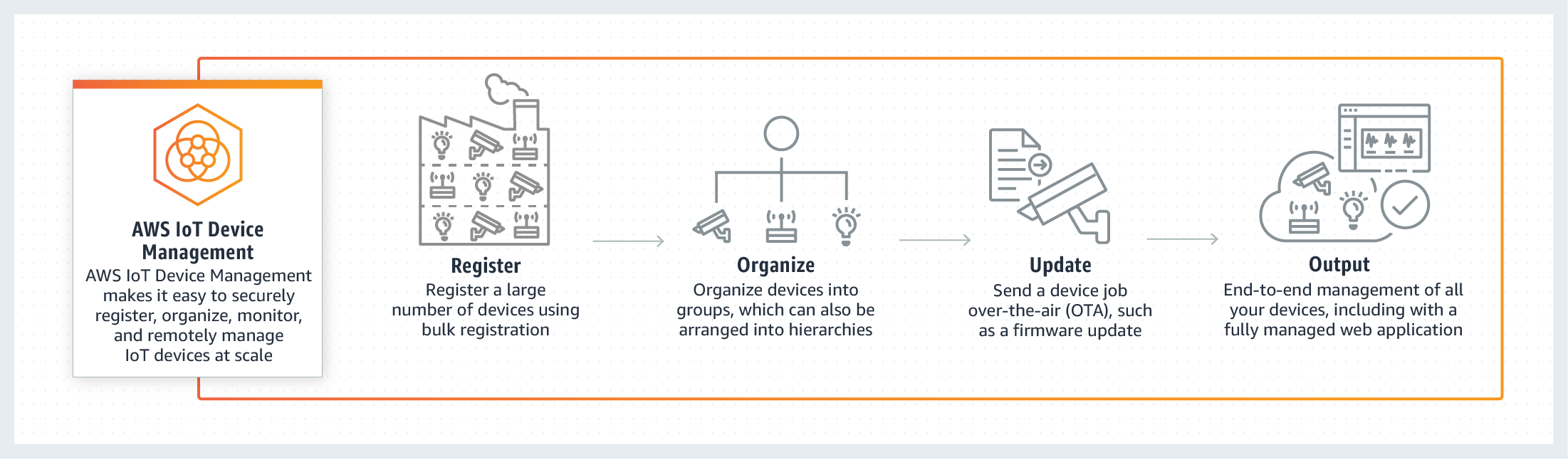
Another notable advantage of SSH is its adaptability. It can be utilized to manage a diverse array of IoT devices, ranging from smart home appliances to complex industrial sensors. Regardless of whether you're managing a single device or an entire network, SSH equips you with the tools necessary for efficient and secure management.
Top Free SSH IoT Device Software Options
Popular Free SSH Clients
There are several free SSH clients available that cater to IoT device management. Below are some of the most widely used options:
- PuTTY: A highly regarded SSH client for Windows, offering an intuitive interface and comprehensive features.
- OpenSSH: A free, open-source SSH client included with most Linux and macOS systems, providing reliable performance.
- Bitvise SSH Client: A feature-rich SSH client available in both free and paid versions, with the free version suitable for personal use.
Open Source Alternatives
In addition to the aforementioned options, there are several open-source alternatives that provide advanced capabilities for managing SSH IoT devices:
Read also:Franco Columbu
- MobaXterm: A powerful SSH client offering a range of features, including terminal emulation and file transfer capabilities.
- KiTTY: A lightweight and customizable SSH client based on PuTTY, ideal for users seeking simplicity and flexibility.
How to Select the Right SSH IoT Software
Selecting the appropriate SSH IoT software involves considering several factors, such as your specific requirements and the devices you intend to manage. Below are some essential considerations:
Compatibility
Ensure that the software you choose is compatible with the devices you're managing. Review the system requirements and confirm that the software supports the operating systems and protocols used by your devices.
Security Features
Opt for software that provides robust security features, including encryption and authentication. Additionally, evaluate whether the software supports advanced features like two-factor authentication (2FA) or public key authentication to enhance security.
User Interface
A user-friendly interface can significantly simplify the management of SSH IoT devices. Consider whether the software offers a graphical user interface (GUI) or requires command-line usage. Beginners may find a GUI more intuitive, while advanced users might prefer the flexibility of the command line.
Step-by-Step Installation Guide
Installing PuTTY
Follow these steps to install PuTTY, one of the most popular SSH clients:
- Download the PuTTY installer from the official website.
- Run the installer and follow the on-screen instructions to complete the setup.
- Once installed, open PuTTY and input the IP address or hostname of the IoT device you wish to connect to.
- Specify the port number (default is 22 for SSH) and click "Open" to establish the connection.
Installing OpenSSH
For Linux and macOS users, OpenSSH is often pre-installed. If it's not, you can install it using your system's package manager. For instance, on Ubuntu, you can install OpenSSH by executing the following command:
sudo apt-get install openssh-client
Enhancing Security for SSH IoT Device Management
Securing the management of SSH IoT devices is crucial to safeguarding your network and data. Below are some security tips to bear in mind:
Use Strong Passwords
Ensure all SSH accounts utilize strong, unique passwords. Avoid predictable or reused passwords to minimize the risk of unauthorized access.
Enable Public Key Authentication
Public key authentication adds an extra layer of security by requiring users to possess a private key to access the device. This mitigates the likelihood of brute-force attacks and unauthorized access.
Regularly Update Software
Maintain up-to-date SSH software and devices with the latest security patches and updates. This protects against known vulnerabilities and ensures the continued security of your devices.
Best Practices for Managing SSH IoT Devices
Implementing best practices for managing SSH IoT devices can enhance both efficiency and security. Below are some key practices to consider:
Document Your Devices
Create a comprehensive inventory of all your IoT devices, including their IP addresses, usernames, and other pertinent details. This will facilitate easier management and troubleshooting when necessary.
Limit Access
Restrict access to SSH IoT devices to only those who require it. Utilize role-based access control (RBAC) to ensure users have the appropriate level of access based on their responsibilities.
Monitor Activity
Consistently monitor SSH activity to identify any suspicious behavior. Employ tools such as log analysis software to review login attempts and detect potential security threats.
Addressing Common Issues and Troubleshooting
Despite thorough preparation, challenges may arise when managing SSH IoT devices. Below are some common problems and methods to troubleshoot them:
Connection Issues
If you're unable to connect to an IoT device using SSH, consider the following:
- Verify that the device is powered on and properly connected to the network.
- Ensure the IP address or hostname is accurate.
- Confirm that the SSH service is operational on the device.
Authentication Errors
In the event of authentication errors, ensure your credentials are correct and that public key authentication is properly configured. Additionally, check whether the device's firewall or security settings are obstructing your connection.
Future Trends in SSH IoT Device Management
The field of SSH IoT device management continues to evolve, with emerging technologies and trends shaping its future. Some notable trends to watch include:
Quantum-Safe Encryption
As quantum computing becomes more prevalent, the demand for quantum-safe encryption will increase. SSH protocols must adapt to remain secure against potential quantum attacks.
AI-Powered Security
Artificial intelligence (AI) and machine learning (ML) are increasingly integrated into IoT networks to enhance security. AI-powered tools can detect and respond to threats in real-time, improving the overall security of SSH IoT devices.
Conclusion and Next Steps
In summary, downloading and utilizing SSH IoT device access software can significantly improve your ability to manage remote devices securely and efficiently. By adhering to the guidelines and best practices outlined in this article, you can ensure the security of your devices while maximizing the benefits of SSH.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore other articles on our website for further tips and insights on managing IoT devices. Together, we can create a safer and more interconnected world!
Data Source: SSH Official Website, OpenSSH Project