The Internet of Things (IoT) is revolutionizing the way we interact with technology, creating an interconnected ecosystem where devices communicate seamlessly. However, as connectivity grows, so does the importance of robust security measures. Secure Shell (SSH) plays a critical role in safeguarding IoT devices from unauthorized access and potential cyber threats, ensuring a secure and reliable network environment.
In this detailed SSH IoT tutorial, we will explore the intricacies of implementing SSH to secure IoT devices. Whether you're a hobbyist experimenting with smart gadgets or a professional managing large-scale IoT deployments, understanding SSH is essential for protecting your devices and maintaining the integrity and privacy of your data.
This guide will provide you with step-by-step instructions, expert advice, and best practices to help you effectively integrate SSH into your IoT projects. Let’s dive in and discover how SSH can transform the security of your IoT ecosystem.
Read also:Lola Shark Tale
Table of Contents
- What is SSH?
- Understanding IoT
- Why Choose SSH for IoT?
- The Evolution of SSH
- Configuring SSH for IoT
- Enhancing SSH Security
- Optimizing SSH Usage
- Troubleshooting Common SSH Issues
- Best Practices for SSH in IoT
- Conclusion
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol designed to secure communication between devices over an unsecured network. It establishes a secure channel for remote command execution and file transfer, ensuring that all data transmitted between a client and server is encrypted. This encryption guarantees confidentiality, integrity, and authentication, making SSH an indispensable tool for securing sensitive information.
In the context of IoT, SSH is particularly valuable as it allows administrators to manage and monitor devices remotely while maintaining the highest level of security. By implementing SSH, you can establish a secure connection to your IoT devices, ensuring that they remain protected from unauthorized access and potential cyber threats.
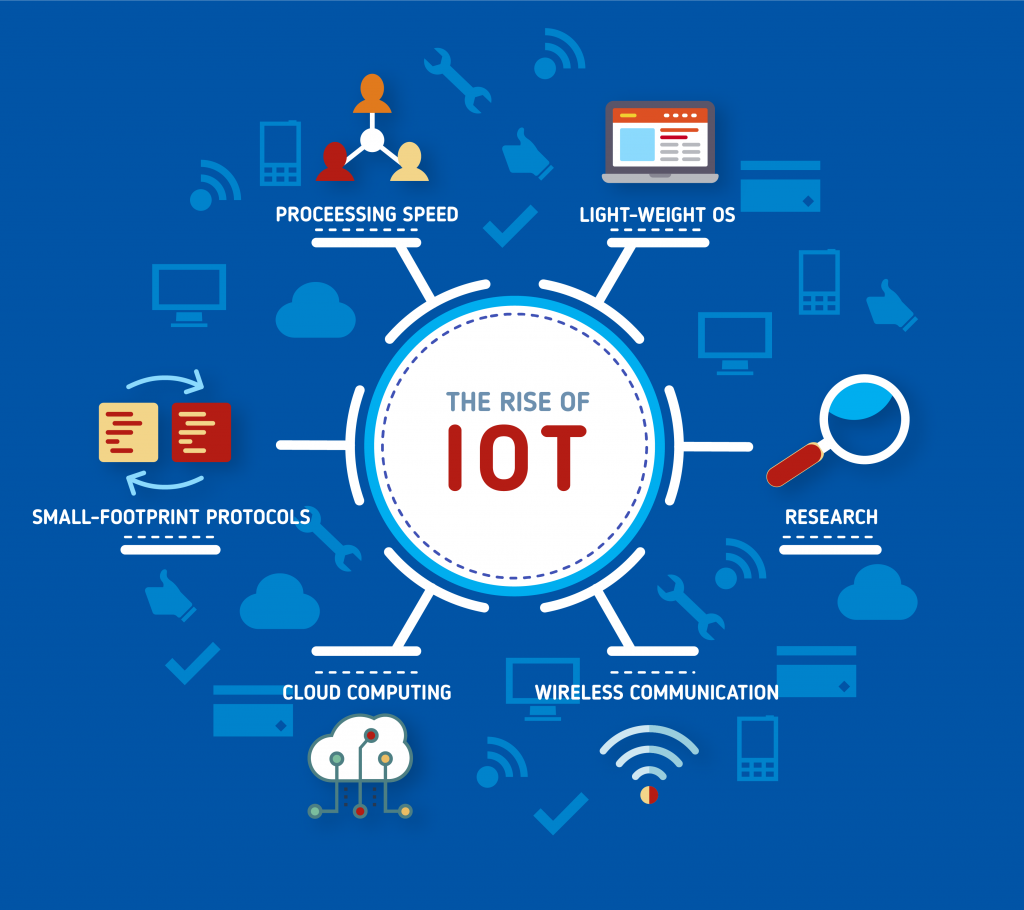
Understanding IoT
The Internet of Things (IoT) refers to the vast network of interconnected devices equipped with sensors, software, and connectivity capabilities. These devices range from everyday household appliances to sophisticated industrial machinery, all designed to enhance efficiency, convenience, and productivity in our daily lives. IoT devices collect and exchange data, enabling them to perform tasks autonomously and interact with their environment in real-time.
As the adoption of IoT continues to grow, so does the need for robust security measures. With SSH, IoT devices can be safeguarded against unauthorized access, ensuring that sensitive data remains secure and protected from potential breaches. By integrating SSH into your IoT infrastructure, you can significantly enhance the security and reliability of your connected devices.
Why Choose SSH for IoT?
Using SSH for IoT offers numerous advantages, making it an ideal choice for securing connected devices. Below are some key benefits of implementing SSH in your IoT projects:
- Encryption: SSH encrypts all communication between devices, ensuring that data transmitted over the network remains confidential and protected from interception.
- Authentication: SSH provides robust authentication mechanisms, ensuring that only authorized users can access IoT devices and reducing the risk of unauthorized access.
- Remote Management: SSH enables administrators to manage IoT devices remotely, streamlining maintenance and troubleshooting processes while minimizing the need for physical intervention.
- Scalability: SSH is highly scalable, making it suitable for managing large IoT networks with numerous devices and complex configurations.
The Evolution of SSH
Secure Shell (SSH) was first developed by Tatu Ylönen in 1995 in response to a password-sniffing attack on the Helsinki University of Technology network. Initially created as a replacement for unsecured protocols like Telnet and rlogin, SSH quickly gained popularity due to its advanced security features and reliability.
Read also:Understanding The Concept Of Masa 49 And Its Cultural Significance
Over the years, SSH has evolved into a widely adopted standard for secure communication. Below is a timeline highlighting key milestones in the development of SSH:
| Year | Milestone |
|---|---|
| 1995 | Development of SSH by Tatu Ylönen |
| 1997 | Release of SSH-1 protocol |
| 2006 | Standardization of SSH-2 by the Internet Engineering Task Force (IETF) |
| 2018 | Introduction of OpenSSH 7.7 with enhanced security features |
Configuring SSH for IoT
Step-by-Step Guide to Installing SSH
Configuring SSH for IoT involves several steps, including installing the SSH server, customizing settings, and testing the connection. Follow this detailed guide to set up SSH on your IoT devices:
- Install SSH Server: Begin by installing OpenSSH on your IoT device using the command:
sudo apt-get install openssh-server. - Configure SSH Settings: Edit the SSH configuration file with the command:
sudo nano /etc/ssh/sshd_config. Customize settings such as the port number, authentication methods, and access permissions to suit your specific requirements. - Restart SSH Service: After making changes to the configuration file, restart the SSH service using the command:
sudo service ssh restart. - Test the Connection: Use an SSH client to connect to your IoT device and verify that the setup is functioning correctly. This step ensures that your SSH configuration is properly implemented.
Enhancing SSH Security
Implementing Advanced Security Measures
To maximize the security of your SSH connections, consider implementing the following strategies:
- Disable Password Authentication: Transition to public key authentication instead of relying on passwords. This approach significantly reduces the risk of brute-force attacks and unauthorized access.
- Change Default Port: Modify the default SSH port (22) to a custom port number to deter automated attacks and enhance security.
- Limit User Access: Restrict SSH access to specific users or IP addresses to minimize the risk of unauthorized access attempts.
- Enable Two-Factor Authentication: Add an additional layer of security by requiring a second form of authentication, such as a one-time password or biometric verification.
Optimizing SSH Usage
Maximizing Efficiency and Performance
Here are some tips to help you optimize your SSH experience and improve the efficiency of your IoT projects:
- Use SSH Aliases: Create shortcuts for frequently accessed devices to streamline workflows and save time.
- Enable Compression: Enable data compression during transmission to enhance transfer speeds, especially over slow or unreliable networks.
- Monitor Logs: Regularly review SSH logs to identify potential security threats and address them promptly.
- Update Software: Keep your SSH server and client software updated with the latest security patches to protect against emerging vulnerabilities.
Troubleshooting Common SSH Issues
Solving SSH Problems Efficiently
Encountering issues with SSH is not uncommon, but most problems can be resolved with the right approach. Below are some common issues and their solutions:
- Connection Refused: Ensure that the SSH service is running and that the correct port number is specified. Verify that firewalls are not blocking the connection.
- Authentication Failed: Double-check that the correct username and key are being used for authentication. Ensure that the key file is properly formatted and accessible.
- Timeout Errors: Investigate network connectivity issues and confirm that firewalls or routers are not interfering with the SSH connection.
- Permission Denied: Review file and directory permissions for the SSH configuration files to ensure they are correctly set and accessible only to authorized users.
Best Practices for SSH in IoT
Implementing Robust Security Protocols
Adhering to best practices is crucial for maintaining the security of your IoT devices. Consider the following recommendations to enhance the security of your SSH implementation:
- Regular Audits: Conduct periodic audits of SSH configurations and access logs to identify vulnerabilities and address them proactively.
- Network Segmentation: Isolate IoT devices on a dedicated network segment to minimize potential attack surfaces and protect sensitive data.
- Use Strong Keys: Generate strong SSH keys with sufficient bit lengths to ensure robust encryption and prevent unauthorized access.
- Disable Root Login: Restrict root access to prevent unauthorized administrative control of devices and reduce the risk of system-wide compromises.
Conclusion
In conclusion, SSH is a powerful and versatile tool for securing IoT devices, offering encryption, authentication, and remote management capabilities. By following the steps outlined in this comprehensive SSH IoT tutorial, you can effectively implement SSH in your IoT projects, ensuring the security and integrity of your connected devices.
We invite you to share your thoughts, experiences, and insights in the comments section below. Additionally, explore our other resources for more information on IoT security and best practices. Together, let’s create a safer and more connected world through secure and reliable IoT solutions.
References:
- OpenSSH Official Documentation: https://www.openssh.com/
- Internet Engineering Task Force (IETF): https://www.ietf.org/
- IoT Security Foundation: https://iotsecurityfoundation.org/