In today’s digital age, the ability to remotely access IoT devices is a cornerstone of modern technology. Whether you're overseeing smart home systems or monitoring industrial equipment, the capability to control and supervise devices from anywhere is indispensable. Secure Shell (SSH) provides a reliable method for achieving this, and with web-based tools, the process becomes even more streamlined. This article will guide you step-by-step on how to remotely access IoT devices using SSH web solutions while also offering free download options to simplify your setup.
In the modern era of interconnectedness, IoT devices are omnipresent. From smart thermostats to advanced industrial sensors, these devices produce valuable data that must be accessed and managed efficiently. However, ensuring secure remote access without sacrificing performance remains a significant challenge for many users. This is precisely where SSH plays a pivotal role. By integrating SSH with web-based tools, users can remotely manage their IoT devices with enhanced security and efficiency.
Through this article, we will delve into setting up remote access, explore the best tools available, and provide resources for free download options. Regardless of whether you're a beginner or an experienced user, this comprehensive guide will offer actionable insights to help you establish a robust remote access system for your IoT devices.
Read also:Naviyd Ely Raymond
Exploring IoT and the Role of Remote Access
Understanding IoT Devices
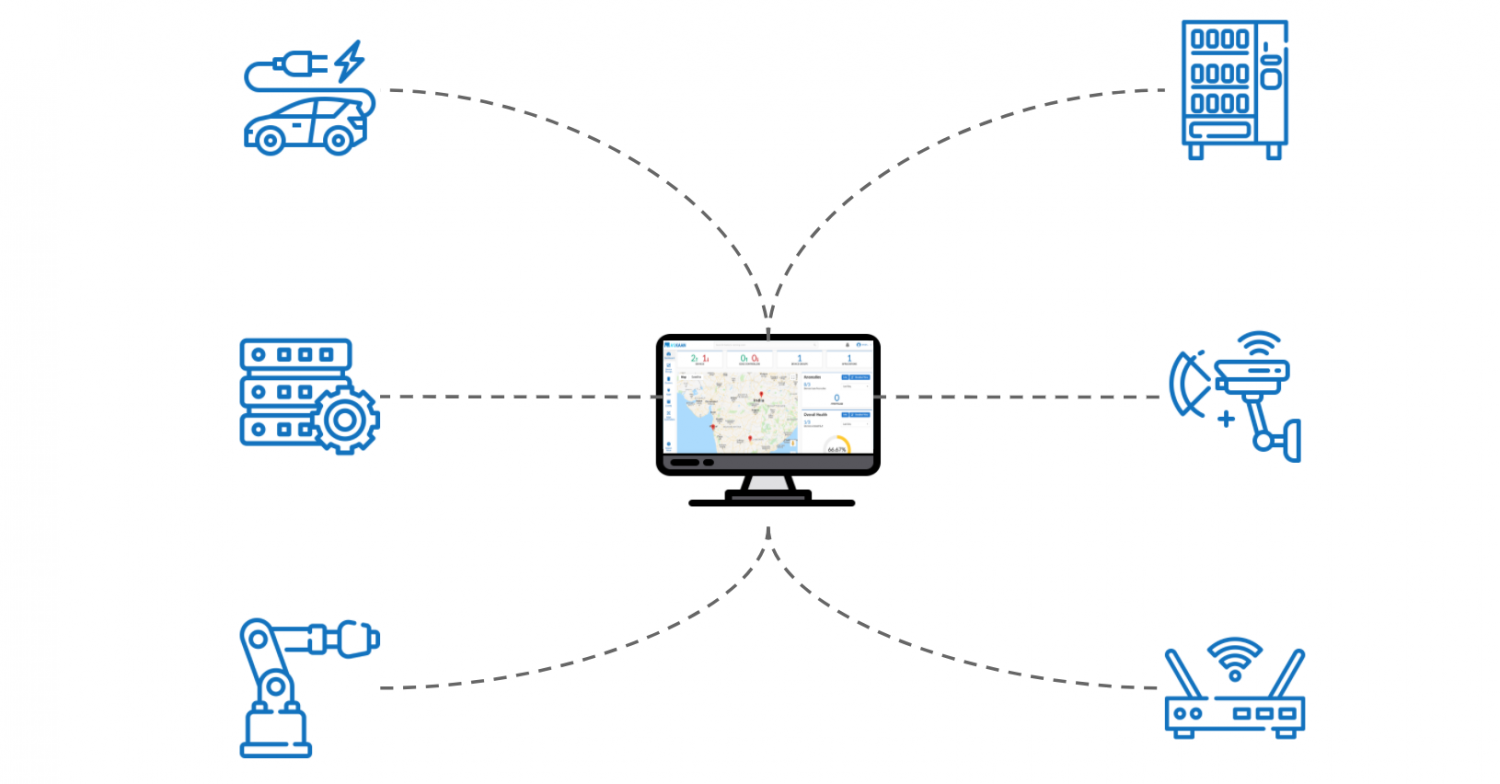
IoT devices encompass any physical objects equipped with sensors, software, and connectivity features that enable them to exchange data with other devices and systems over the internet. These devices span a wide range, from consumer products such as smart speakers and wearables to industrial equipment like robotics and manufacturing machinery. IoT devices not only enhance automation and efficiency across industries but also generate real-time data that can be leveraged for analysis and informed decision-making. However, ensuring the security of these devices when accessed remotely is of paramount importance.
- IoT devices significantly enhance automation and efficiency in various sectors.
- They provide real-time data for in-depth analysis and decision-making processes.
- Security concerns are critical when managing IoT devices remotely.
Why Remote Access is Essential
Remote access empowers users to control and monitor IoT devices from any location worldwide. This capability is crucial for multiple reasons:
- Convenience: Users can manage their devices without needing to be physically present.
- Efficiency: Real-time monitoring and updates help save valuable time and resources.
- Scalability: It enables the effortless management of numerous devices spread across different locations.
SSH: A Secure Protocol for Remote Access
What SSH Entails
SSH, or Secure Shell, is a network protocol designed to facilitate secure communication between devices over unsecured networks. It encrypts all data transmitted between the client and server, ensuring both confidentiality and integrity. Its robust encryption and authentication mechanisms make SSH an ideal choice for securing IoT devices against unauthorized access and potential cyber threats.
Key Features of SSH:
- Encryption ensures secure data transfer.
- Authentication verifies the identity of users and devices.
- Support for various commands and applications enhances versatility.
Why SSH is Ideal for IoT Devices
SSH offers a secure and reliable solution for managing IoT devices remotely. Its advanced encryption and authentication protocols prevent unauthorized access, support secure file transfers, and are compatible with a wide array of operating systems and platforms.
- Prevents unauthorized access to IoT devices.
- Facilitates secure file transfers and command execution.
- Compatible with numerous operating systems and platforms.
Web-Based SSH Tools for IoT Devices
Advantages of Web-Based SSH
Web-based SSH tools eliminate the necessity of installing additional software on local machines. By accessing SSH through a browser, users can manage their IoT devices from any device with internet connectivity, offering unmatched convenience and flexibility.
Read also:Rod Wave Weight
- No need for software installation.
- Accessible from any device equipped with a browser.
- Simplified user interface for easier device management.
Popular Web-Based SSH Tools
Several tools are available for remotely accessing IoT devices via SSH web interfaces. Below are some of the most popular options:
- WebSSH: A lightweight tool that allows direct connection to SSH servers through a browser.
- GateOne: An advanced web-based terminal emulator that supports SSH, Telnet, and other protocols.
- Termius: A versatile SSH client available as both a web app and mobile app, providing cross-platform accessibility.
Free Download Options for SSH Tools
Where to Locate Free SSH Tools
Many SSH tools offer free versions or open-source alternatives that can be downloaded and used at no cost. Below are some reliable sources for finding free SSH tools:
- GitHub: A platform for open-source projects, offering free SSH tools such as WebSSH and GateOne.
- Official Websites: Visit the official websites of tools like Termius and PuTTY for free download options.
- Software Repositories: Platforms like SourceForge and Softpedia provide free SSH tools for download.
Installation and Setup Process
Once you've selected and downloaded the SSH tool of your choice, follow these steps for a successful setup:
- Download the tool from a reputable source.
- Install the software on your local machine or deploy it on a server.
- Configure the tool to connect to your IoT devices using their IP addresses or domain names.
- Test the connection to confirm secure and reliable access.
Security Best Practices for Remote Access
The Importance of Security
When remotely accessing IoT devices, security must be a top priority. Unauthorized access can lead to severe consequences such as data breaches, device malfunctions, and operational disruptions.
- Encrypt all communications to safeguard sensitive data.
- Regularly update devices and software to address vulnerabilities.
- Implement strong authentication methods, such as multi-factor authentication (MFA), for added security.
Securing SSH Connections
To ensure the security of your SSH connections, adhere to the following best practices:
- Use strong and unique passwords for all devices.
- Disable password-based authentication and rely on SSH keys instead.
- Restrict access to trusted IP addresses or networks to minimize risks.
Addressing Common Challenges and Solutions
Resolving Connection Issues
A frequent challenge when remotely accessing IoT devices is encountering connection problems. These issues may arise due to network complications, misconfigured settings, or firewall restrictions.
- Ensure stable internet access by checking your network connectivity.
- Verify that your SSH settings are correctly configured.
- Adjust firewall settings to permit SSH traffic.
Optimizing Performance
Enhancing the performance of your SSH connections is essential for efficient remote management. Here are some strategies to improve performance:
- Utilize compression to reduce data transfer sizes.
- Optimize your SSH configuration for faster and more reliable connections.
- Regularly monitor your devices to identify and resolve potential bottlenecks.
Case Studies and Real-World Applications
Industrial IoT Deployment
In industrial settings, remote access to IoT devices via SSH has transformed how equipment is managed and maintained. Companies can now monitor and control machines from a centralized location, reducing downtime and improving overall efficiency.
- Real-time monitoring of production lines ensures smooth operations.
- Remote troubleshooting and maintenance minimize disruptions.
- Data collection enables predictive maintenance for proactive problem-solving.
Smart Home Automation
For enthusiasts of smart homes, SSH offers a secure method to manage IoT devices like smart lights, thermostats, and security systems. Users can control these devices remotely, ensuring convenience and peace of mind.
- Control smart home devices effortlessly through a mobile app.
- Automate routines and schedules to enhance energy efficiency.
- Receive alerts and notifications for improved home security.
Future Trends in IoT Remote Access
Emerging Technologies
The landscape of IoT remote access continues to evolve with the advent of new technologies and solutions. Some of the most promising trends include:
- 5G Networks: Offering faster and more dependable connections for IoT devices.
- Edge Computing: Processing data closer to the source to reduce latency and improve performance.
- AI and Machine Learning: Enhancing automation and decision-making capabilities for IoT systems.
Security Implications
As IoT devices become increasingly integrated into daily life, the necessity for robust security measures will only intensify. Future advancements in encryption, authentication, and threat detection will play a critical role in ensuring the safety and reliability of these devices.
Conclusion
Remotely accessing IoT devices through SSH web tools is a powerful method for securely and efficiently managing and monitoring your devices. By adhering to the guidelines outlined in this article, you can establish a dependable remote access system tailored to your needs. Always prioritize security and stay informed about the latest trends and technologies in the IoT field.
Take Action: Download and install a free SSH tool today to begin managing your IoT devices remotely. Share your experiences in the comments section below and explore additional articles on our site for further insights into IoT and technology.
Table of Contents
- Exploring IoT and the Role of Remote Access
- SSH: A Secure Protocol for Remote Access
- Web-Based SSH Tools for IoT Devices
- Free Download Options for SSH Tools
- Security Best Practices for Remote Access
- Addressing Common Challenges and Solutions
- Case Studies and Real-World Applications
- Future Trends in IoT Remote Access
![How to Access IoT Devices Remotely with SSH [6 Easy Steps]](https://www.trio.so/blog/wp-content/uploads/2024/10/Benefits-of-Using-SSH-for-Remote-IoT-Access.webp)
